Computer Networks
for
Computer Science & Information
Technology
By
www.thegateacademy.com
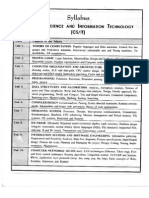
�Syllabus
Computer Networks
Syllabus for Computer Networks
ISO/OSI stack, LAN technologies (Ethernet, Token ring), Flow and error control techniques,
Routing algorithms, Congestion control, TCP/UDP and sockets, IP(v4), Application layer
protocols (ICMP, DNS, SMTP, POP, FTP, HTTP); Basic concepts of hubs, switches, gateways, and
routers.
Analysis of GATE Papers
(Computer Network)
Year
Percentage of marks
2013
7.00
2012
9.00
2011
3.00
2010
8.00
2009
3.33
Overall Percentage
6.513 %
2008
6.00
2007
9.33
2006
7.33
2005
6.00
2004
7.33
2003
5.33
THE GATE ACADEMY PVT.LTD. H.O.: #74, KeshavaKrupa (third Floor), 30th Cross, 10th Main, Jayanagar 4th Block, Bangalore-11
: 080-65700750, info@thegateacademy.com Copyright reserved. Web: www.thegateacademy.com
�Contents
Computer Networks
CONTENTS
Chapters
Page No
#1 Introduction
1 32
Computer Network
Goals/ Advantages of Networking
13
Components of Network
Criteria of a Network
Classification of a Network
Types of Network Connection
Network Topology
46
Transmission Modes
67
Data and Data Communication
The Model
7 20
Networks Connecting Devices
20 24
Assignment 1
25 28
Assignment 2
29
Answer Keys
30
Explanations
30 32
#2 Physical Layers (Data rate, Digital transmission)
33 47
Introduction
33
Transmission Impairment
33 34
Digital transmission
34 38
Transmission Mode
38 39
Multiplexing
39 40
Transmission Media
40 41
Assignment 1
42 44
Assignment 2
44 45
Answer Keys
46
Explanations
46 47
th
th
th
THE GATE ACADEMY PVT.LTD. H.O.: #74, Keshava Krupa (third Floor), 30 Cross, 10 Main, Jayanagar 4 Block, Bangalore-11
: 080-65700750, info@thegateacamy.com Copyright reserved. Web: www.thegateacademy.com
Page i
�Contents
Computer Networks
#3
Medium Access Sublayer (LAN Technologies: Ethernet, Token
Ring)
48 64
Introduction
48
Multiple Access Protocols
48 52
Ethernet Cabling
53
The 802.3 MAC sublayer protocol
54
IEEE standard 802.4-Token Bus
54 55
IEEE standard 802.5-Token Ring
55 58
Assignment 1
59 60
Assignment 2
60 61
Answer Keys
62
Explanations
62 64
#4
The Data Link Layer (Flow and error control techniques)
65 - 99
Data link Layer Design Issues
65 68
Error Detection and Error Correction
69 78
Flow Control and Error Control
78 91
High-level Data Link Control (HDLC) Protocol
91 93
Assignment 1
94 95
Assignment 2
95 96
Answer Keys
97
Explanations
97 99
#5
Routing & Congestion Control
100 114
Routing
100 101
Routing Algorithms:
101 107
Assignment 1
108 110
Assignment 2
110 111
Answer Keys
112
Explanations
112 114
th
th
th
THE GATE ACADEMY PVT.LTD. H.O.: #74, Keshava Krupa (third Floor), 30 Cross, 10 Main, Jayanagar 4 Block, Bangalore-11
: 080-65700750, info@thegateacamy.com Copyright reserved. Web: www.thegateacademy.com
Page ii
�Contents
Computer Networks
#6
TCP/IP, UDP And Sockets, IP(V4)
115 145
Over View of TCP/IP
115 117
Network Layer
117 121
Addressing on Internet
122 126
Subnetting
127 131
Other Protocol in the Network Layer
131 133
Transport Layer
133 137
Assignment 1
138 139
Assignment 2
140 141
Answer Keys
142
Explanations
142 145
#7
Application Layer
146 157
The Domian Name Service (DNS)
146 147
File Transfer Protocol (FTP)
148 149
Trivial File Transfer Protocol (TFTP)
149
Simple Mail Transfer Protocol (SMTP)
149 150
Uniform Resource Locator (URL)
150
Multipose Internet Mail Extensions (MIME)
150
Post Office Protocol (POP)
151
Hypertext Transfer Protocol (HTTP)
151
Assignment 1
152 153
Assignment 2
154
Answer Keys
155
Explanations
155 157
#8
Network Security
158 175
Symmetric key or Private key algorithms
158 160
Asymmetric key Algorithm (or) Public key Algorithm
160 161
Digital Signatures
161 162
Firewalls
162 168
th
th
th
THE GATE ACADEMY PVT.LTD. H.O.: #74, Keshava Krupa (third Floor), 30 Cross, 10 Main, Jayanagar 4 Block, Bangalore-11
: 080-65700750, info@thegateacamy.com Copyright reserved. Web: www.thegateacademy.com
Page iii
�Contents
Computer Networks
Assignment 1
169 170
Assignment 2
171 172
Answer Keys
173
Explanations
173 175
#9
Module Test
176 - 191
Test Questions
176 184
Answer Keys
185
Explanations
185 191
Reference Books
192
th
th
th
THE GATE ACADEMY PVT.LTD. H.O.: #74, Keshava Krupa (third Floor), 30 Cross, 10 Main, Jayanagar 4 Block, Bangalore-11
: 080-65700750, info@thegateacamy.com Copyright reserved. Web: www.thegateacademy.com
Page iv
�Chapter 1
Computer Networks
CHAPTER 1
Introduction
Computer Network
A computer network is created when several computers and terminal device are connected
together by data communication system.
A network is basically a communication system for computers.
Just as the telephone system allows two people to talk, networks allow computers to
communicate. Figure 1.1 illustrate a simple computer network where computer A and B can
communicate and share resources through computer C.
Fig. 1.1 Computer A and B can access files on C, and
can use the printer connected to C.
Goals / Advantages of Networking
(1)
Program and file sharing
Software resources can also be used more effectively over a network. With stand-alone
computers (i.e. not connected to network), the software used on the computer must be
present on each computers hard disk. It is also difficult and time consuming to install and
th
th
th
THE GATE ACADEMY PVT.LTD. H.O.: #74, Keshava Krupa (third Floor), 30 Cross, 10 Main, Jayanagar 4 Block, Bangalore-11
: 080-65700750, info@thegateacamy.com Copyright reserved. Web: www.thegateacademy.com
Page 1
�Chapter 1
Computer Networks
configure the software individually on every computer. With a network one can centrally
install and configure the software, which can be accessed at the entire connected
computer.
(2)
Network Resource sharing
Network resources include printers, plotters, Fax modems, scanners, floppy disks, CDROMS and storage devices (i.e. Hard disks) which can be shared by terminals connected to
network. For example the sharing of a resource such as a storage device.
(3)
Database sharing
A database program is an ideal application for a network. A network feature called record
locking lets multiple users simultaneously access a file without corrupting the data.
Record locking insures that no two users edit the same record at the same time.
(4)
Economical Expansion of the PC Base
Networks provide an economical way to expand the number of computers in an
organization.
(5)
Ability to use network software
A class of software called Groupware is designed specifically for networks. It lets users
interact and coordinate their activities.
Note: Not all software will use a network even if one is installed. You should check the
software documentation to see what features, if any, the software provides in a network
environment.
(6)
Ability to use electronic mail
Electronic mail lets users easily communicate with one another Messages are dropped in
mailboxes for the recipients to read at a convenient time.
(7)
Creation of workgroups
Groups are important in networks. They can consist of users who work in a department or
who are assigned to special project. With Netware, one can assign users to groups and
then give each group access to special directories and resources not accessible by other
users. This saves the trouble of assigning access to each individual user.
(8)
Centralized Management
Because Netware users dedicated servers can be grouped in one location, along with the
shared resource attached to them, for easier management.
Hardware upgrades, software backups, system maintenance and system protection are
much easier to handle when these devices are in one location.
(9)
Security
A network provides more secure environment for a companys important information.
Security starts with the login procedure to ensure that a user accesses the network using
his or her own account. This account is tailored (i.e. made according to the user
requirements) to give the user access only to authorized areas of the server and the
network. Login restrictions can force a user a log in at one specific station and only during
specific time frame or period.
(10) Access to more than one operating system
Netware provides connections for many different operating systems, including DOS, OS/2,
UNIX, and Apple Talk. Users of these systems can access files on the Netware server.
th
th
th
THE GATE ACADEMY PVT.LTD. H.O.: #74, Keshava Krupa (third Floor), 30 Cross, 10 Main, Jayanagar 4 Block, Bangalore-11
: 080-65700750, info@thegateacamy.com Copyright reserved. Web: www.thegateacademy.com
Page 2
�Chapter 1
Computer Networks
(11) Enhancement of the corporate structure
Networks can change the structure of an organization and the way it is managed. Users
who work in a specific department and for a specific manager no longer need to be in the
same physical area. Their offices can be located in areas where their expertise is most
needed. The network ties them to their department managers and systems. This
arrangement is useful for special project in which individuals from different departments,
such as research, production and marketing, need to work closely with each other.
Components of Network
Computer networks have the following fundamental components:
1.
2.
3.
4.
5.
Server
Workstations
Network Interface Cards
Cabling system
Shared Resources and Peripherals.
Criteria of a Network
A network must able to meet a certain number of criteria. The most important of these are
follows
(i) Performance: performance can be measured in many ways, including transmit time and
response time. The performance of a network depends upon these following factors:
(i) Number of users
(ii) Types of transmission medium
(iii) Capacity of connected hardware
(iv) Efficiency of the software
(ii) Reliability: In addition to accuracy of delivery. Network reliability is measured by the
frequency of failure, the time it takes for a link to recover from a failure.
(iii) Security: Network security issues include protecting data from the unauthorized access.
Classification of network
It contains two or more computer along with a transmission path to share information and
resource of communication system. By the networking we can make interconnection of two or
more network device
Depending upon the graphical area, we can divide the computer network in 3 parts.
(i) LAN (Local Area Network)
(ii) MAN (Metropolitan Area Network)
(iii) WAN (Wide Area Network)
(i) LAN: It spans over a diameter of 2 km, typically data transfer rate for LAN is 10-100 Mbps,
it is used by a signal organization. It propagates high transmission over unexpensive
media. Example co-axial cable, twisted pair cable.
(ii) MAN: It spans over 10 100km diameter. Data rate for MAN is 10 Mbps. Some special
equipments are required for transmission.
(iii) WAN: It spans across the country or nation. Data transfer rate for WAN is 1.5 mbps. It is
used by multiple organizations
th
th
th
THE GATE ACADEMY PVT.LTD. H.O.: #74, Keshava Krupa (third Floor), 30 Cross, 10 Main, Jayanagar 4 Block, Bangalore-11
: 080-65700750, info@thegateacamy.com Copyright reserved. Web: www.thegateacademy.com
Page 3
�Chapter 1
Computer Networks
Types of Network Connection
In a network two or more device are connected together through link. Link is a path for
communication that transfer data from one device to another.
There are two possible type of connection.
(i) Point to point
(ii) Multi-point
(i)
Point to point: In this case one device is connected to another device.
Link
Work station
Work station
Fig 1.2 Point to Point connection
(ii)
Multi-point: Here two or more device are connected to each other. In a multipoint
connection the capacity of the channel is shared either spatially or temporarily.
Work station
Work station
Main
frame
Work station
Fig 1.3 Multi-point connection
Network Topology
There are two types of topology
1. Physical topology
2. Logical topology
1.
Physical topology: Physical topology represent the physical structure of computer
network. It tells how different computers are connected across its communication
path. There are six basic topology possible.
(i) Mess
(ii) Star
(iii) Ring
(iv) Hybrid
(v) Bus
(vi) Cellular
(i)
Mess Topology: In mesh topology every device has a dedicated point to point link to
every other device. A fully connected mesh network has n(n 1)/2 physical channel
to link n device. To accommodate that many links, every device on the network must
have (n-1) input/output ports.
Advantages
(i) Eliminate traffic problems
(ii) A mesh topology is robust
(iii) It is more secure and private
(iv) Fault identification and fault isolation is easy
th
th
th
THE GATE ACADEMY PVT.LTD. H.O.: #74, Keshava Krupa (third Floor), 30 Cross, 10 Main, Jayanagar 4 Block, Bangalore-11
: 080-65700750, info@thegateacamy.com Copyright reserved. Web: www.thegateacademy.com
Page 4