0% found this document useful (0 votes)
71 views6 pagesSQL Injection Cheat Sheet
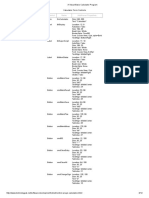
This SQL injection cheat sheet provides various syntax examples for executing SQL injection attacks across different database systems, including string concatenation, substring extraction, and comments. It also covers techniques for querying database versions, listing contents, triggering errors, and performing DNS lookups for data exfiltration. The document serves as a practical guide for understanding and utilizing SQL injection methods effectively.
Uploaded by
fidaxop276Copyright
© © All Rights Reserved
We take content rights seriously. If you suspect this is your content, claim it here.
Available Formats
Download as PDF, TXT or read online on Scribd
0% found this document useful (0 votes)
71 views6 pagesSQL Injection Cheat Sheet
This SQL injection cheat sheet provides various syntax examples for executing SQL injection attacks across different database systems, including string concatenation, substring extraction, and comments. It also covers techniques for querying database versions, listing contents, triggering errors, and performing DNS lookups for data exfiltration. The document serves as a practical guide for understanding and utilizing SQL injection methods effectively.
Uploaded by
fidaxop276Copyright
© © All Rights Reserved
We take content rights seriously. If you suspect this is your content, claim it here.
Available Formats
Download as PDF, TXT or read online on Scribd
/ 6