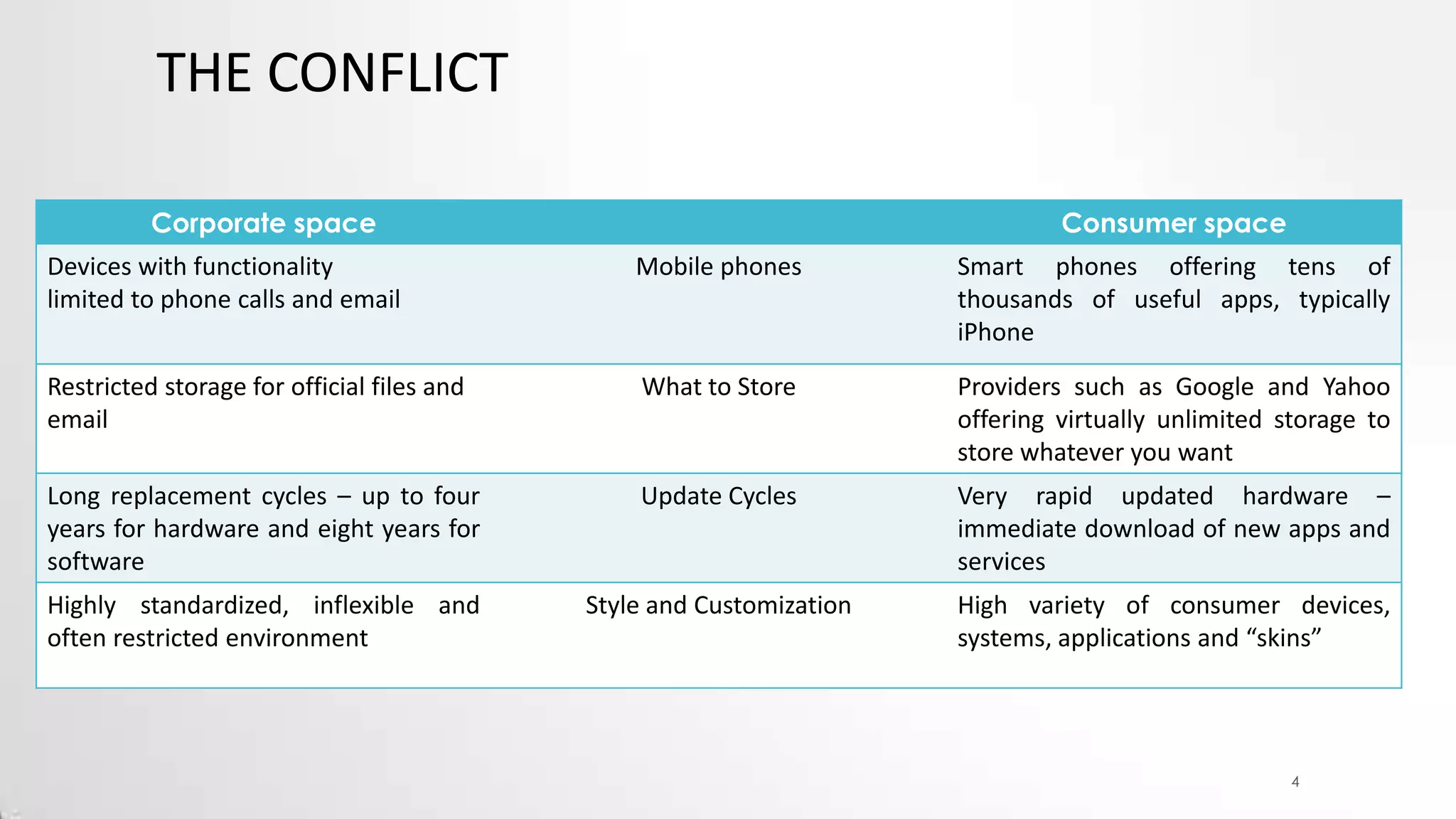
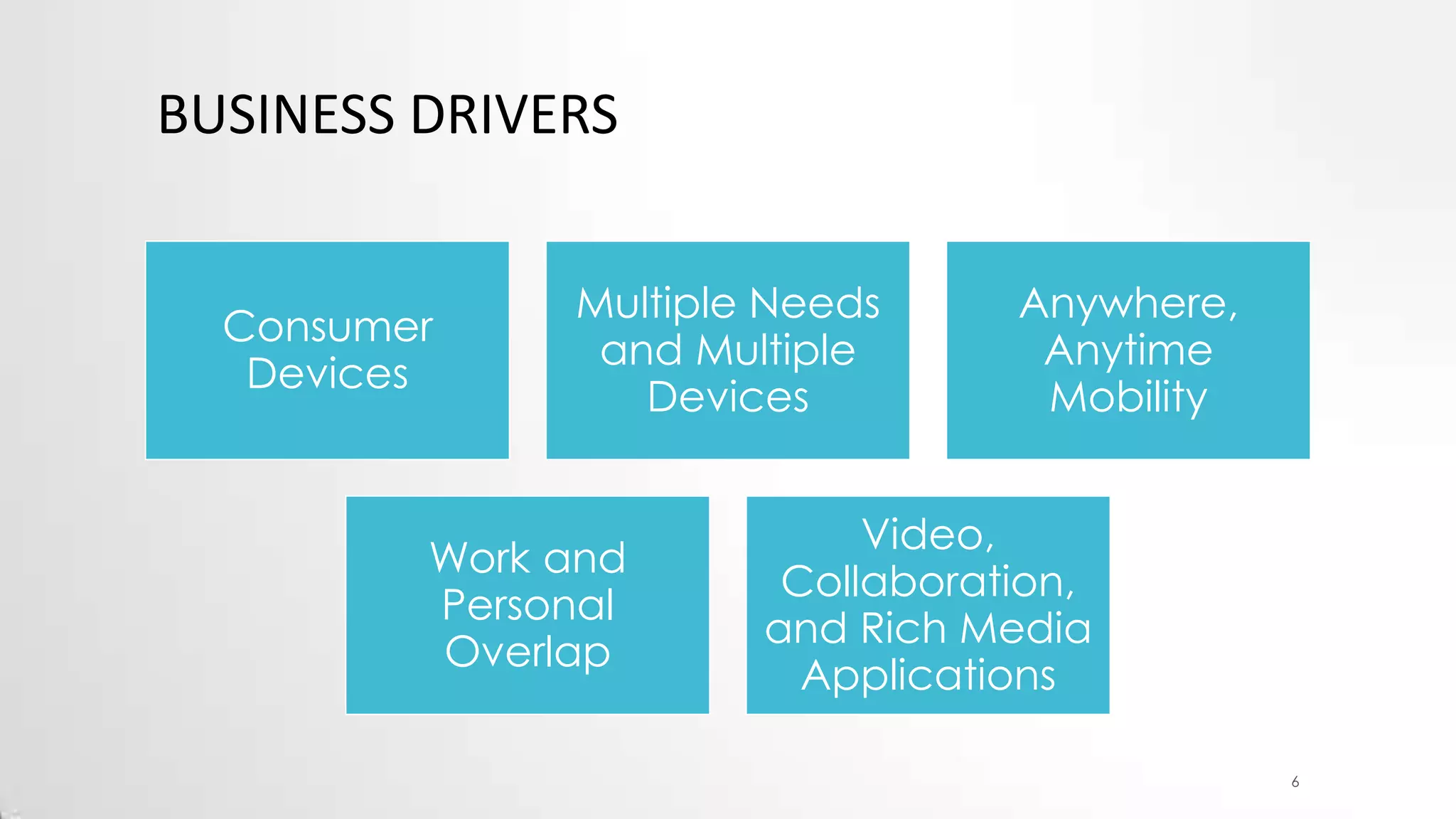
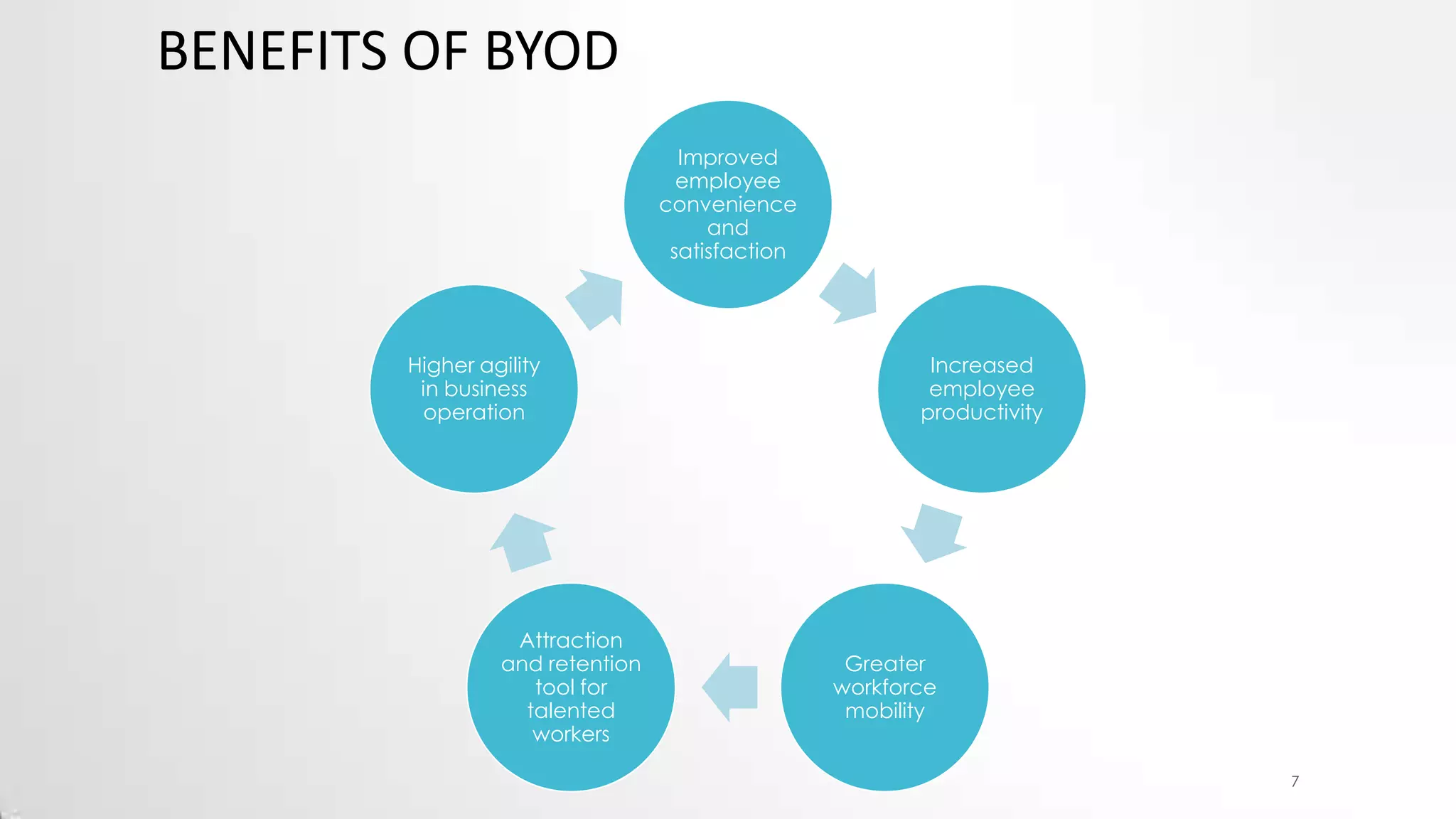
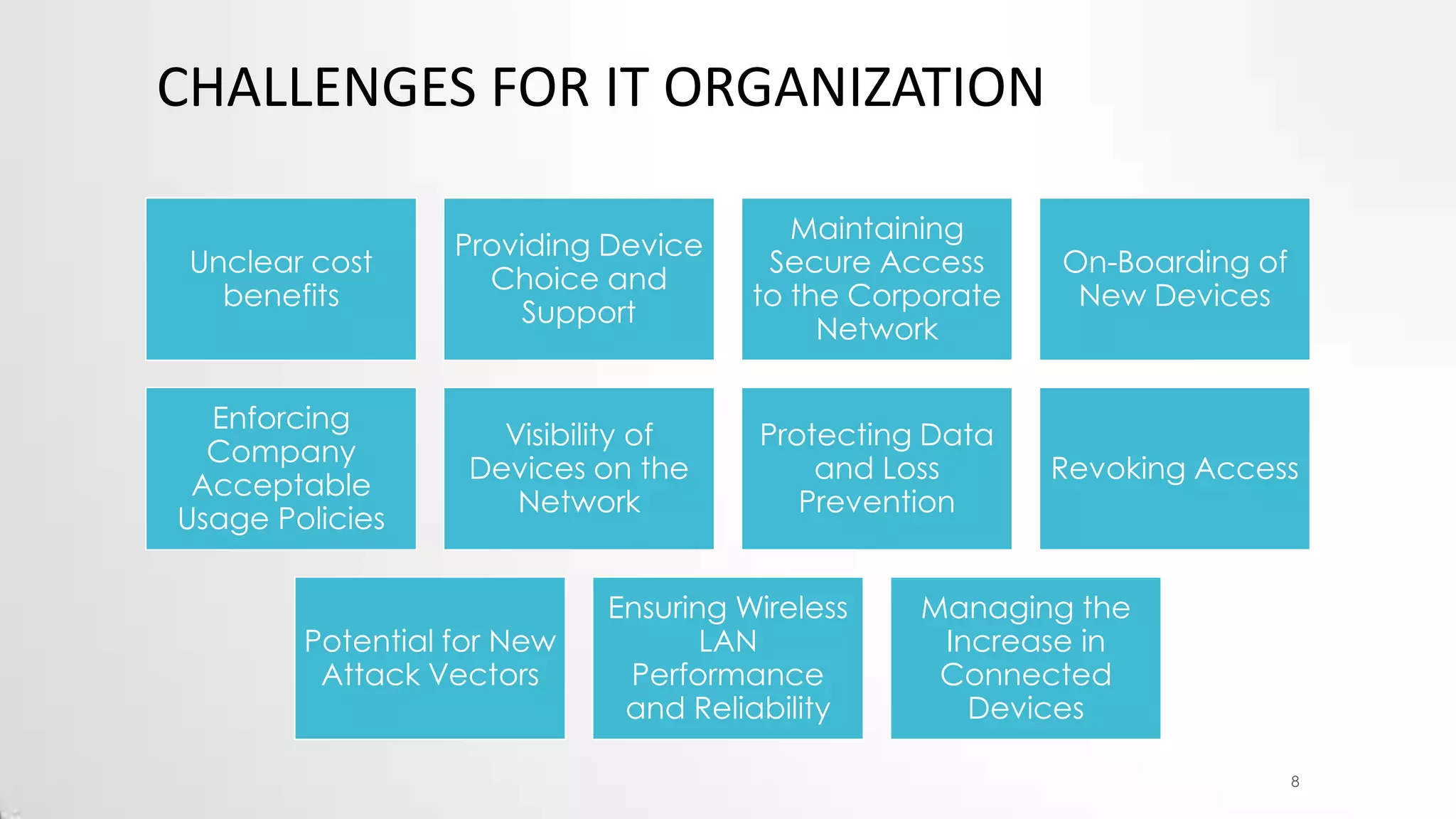
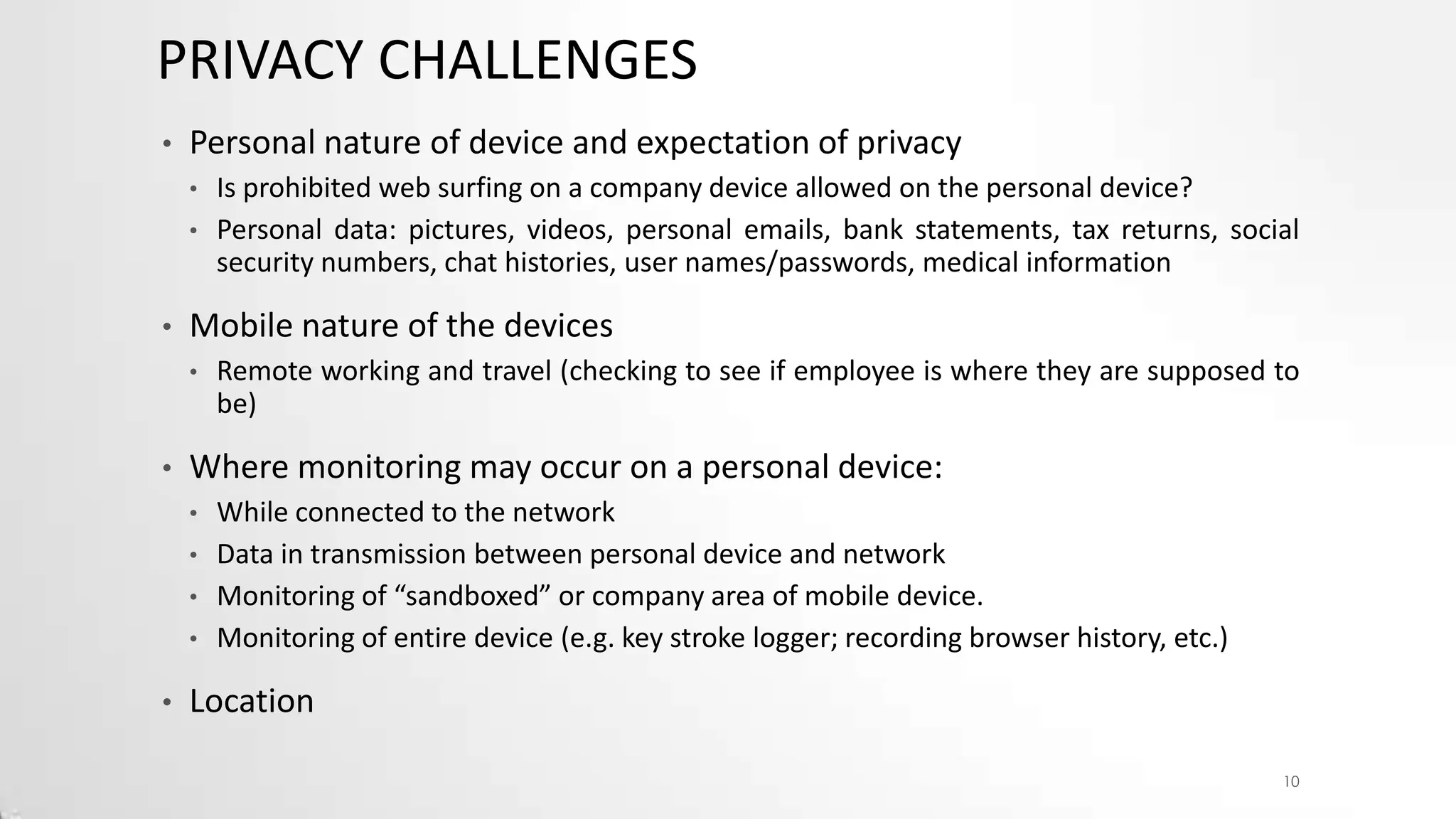
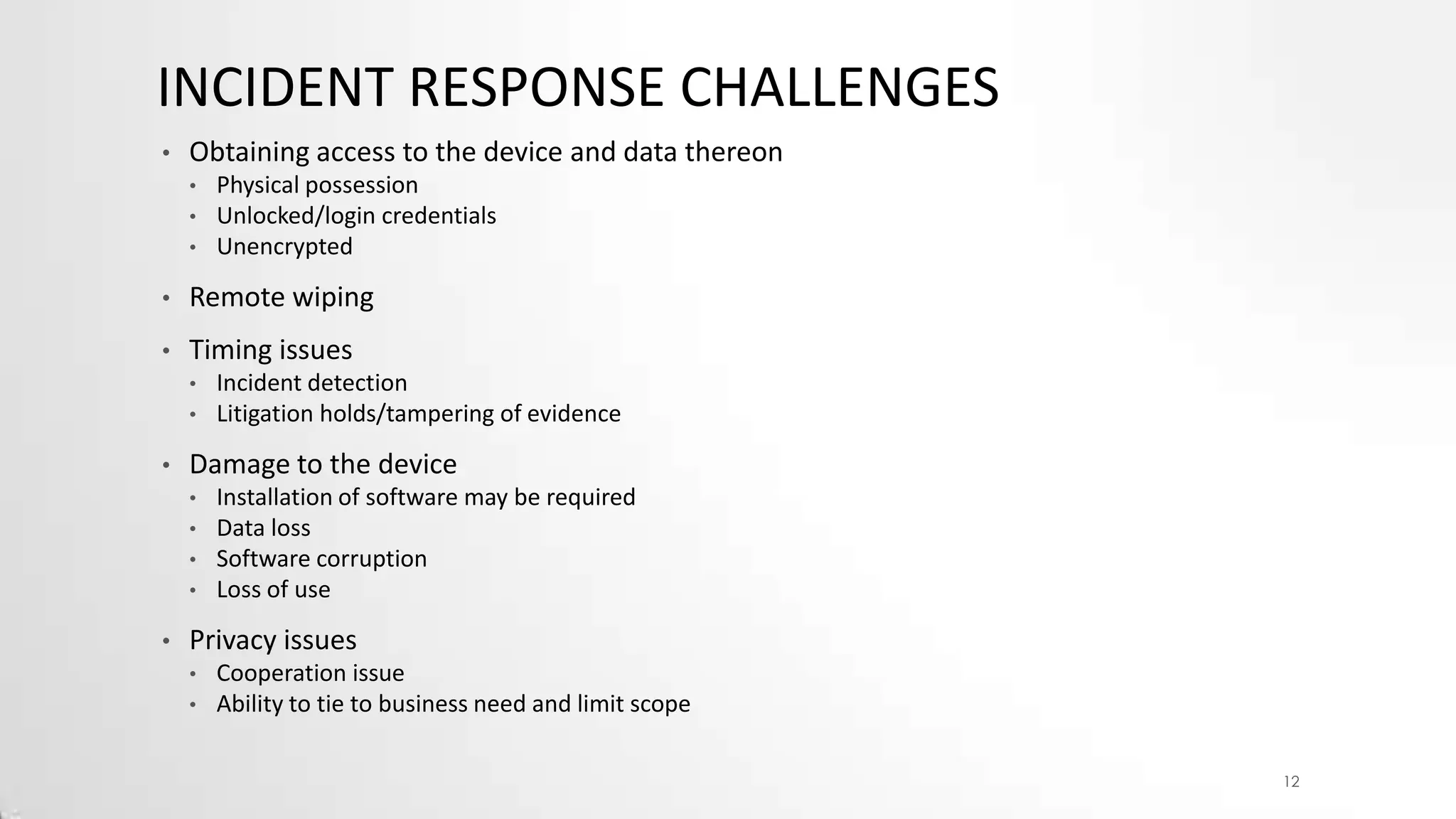
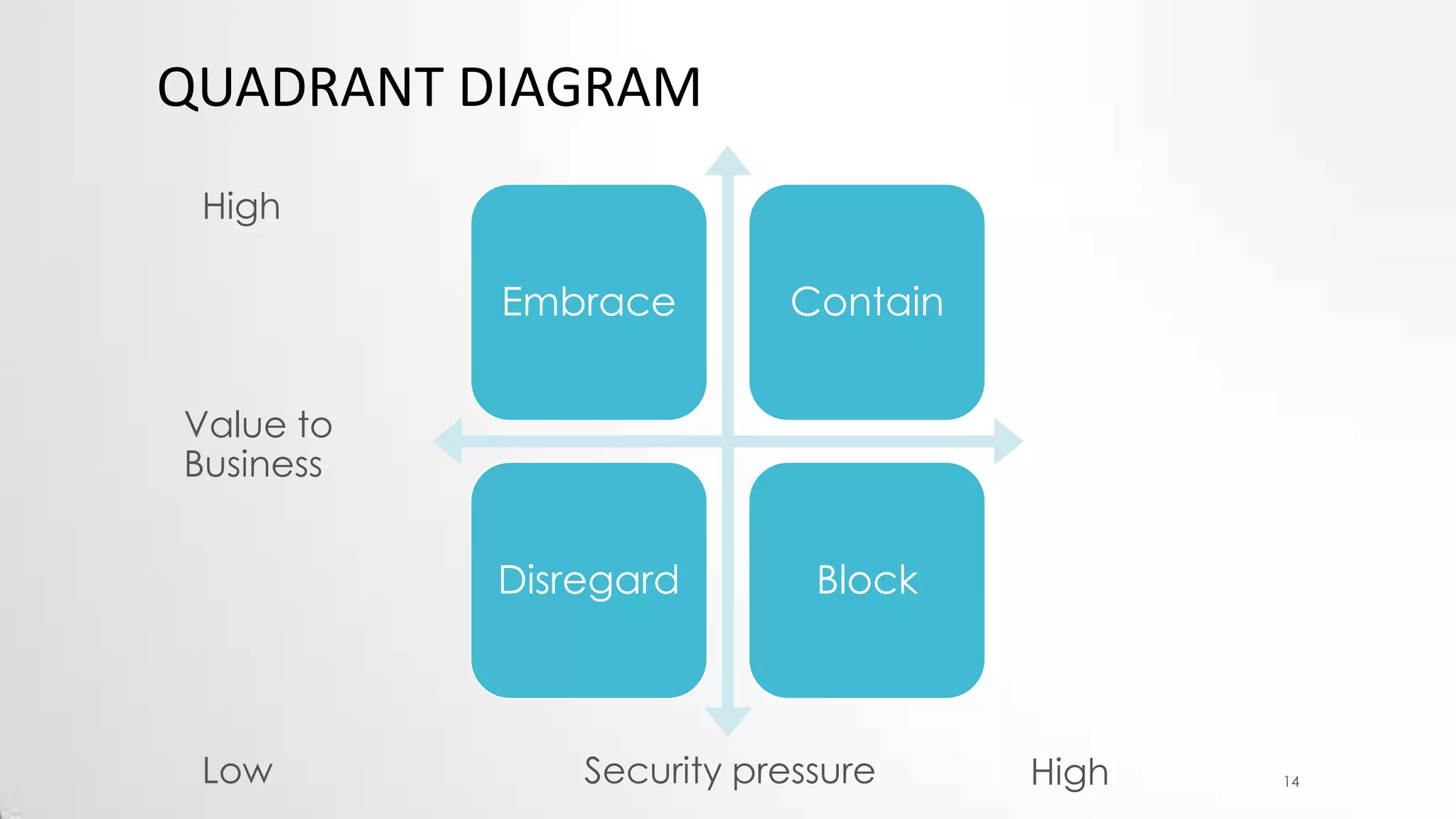
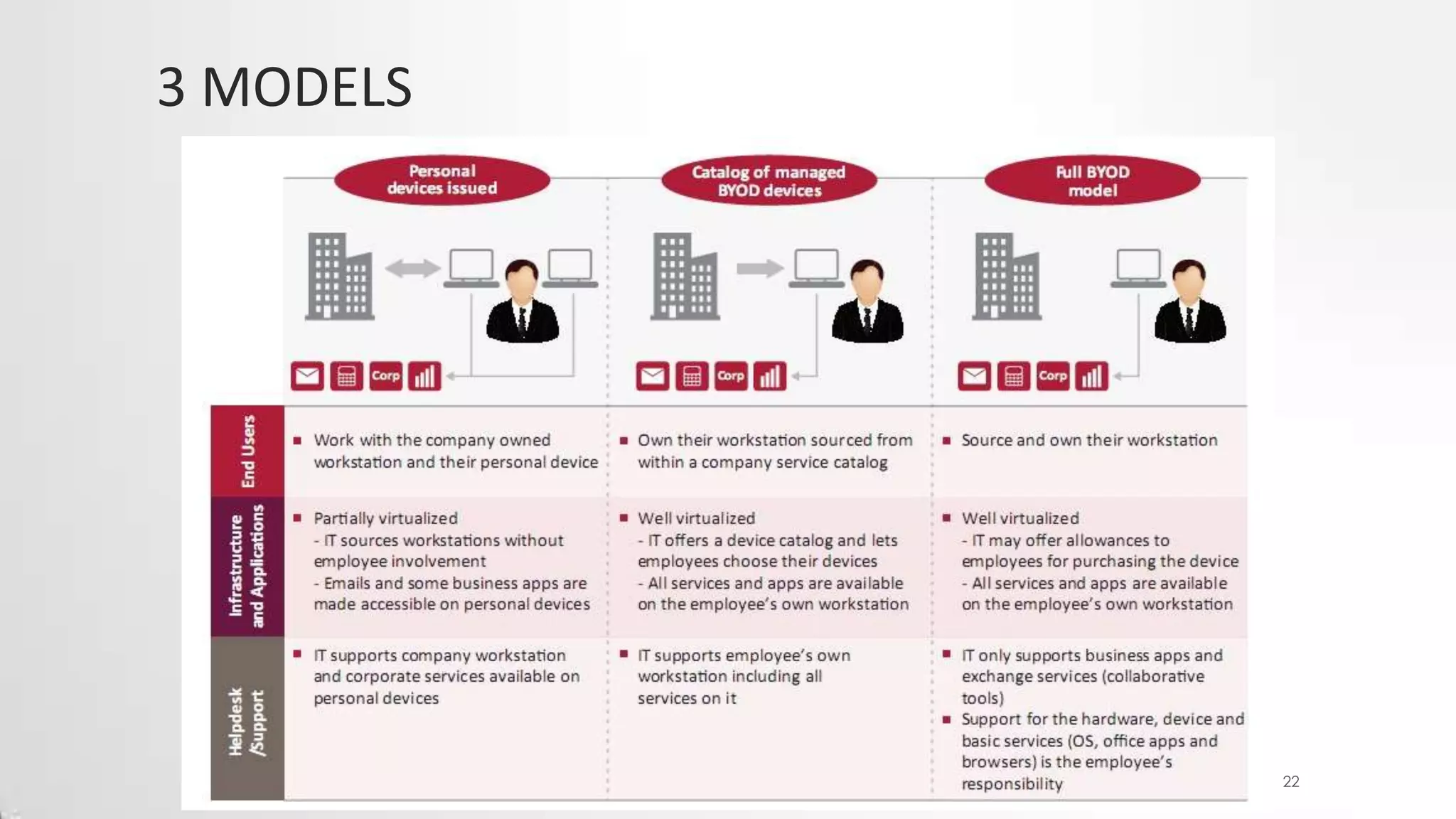
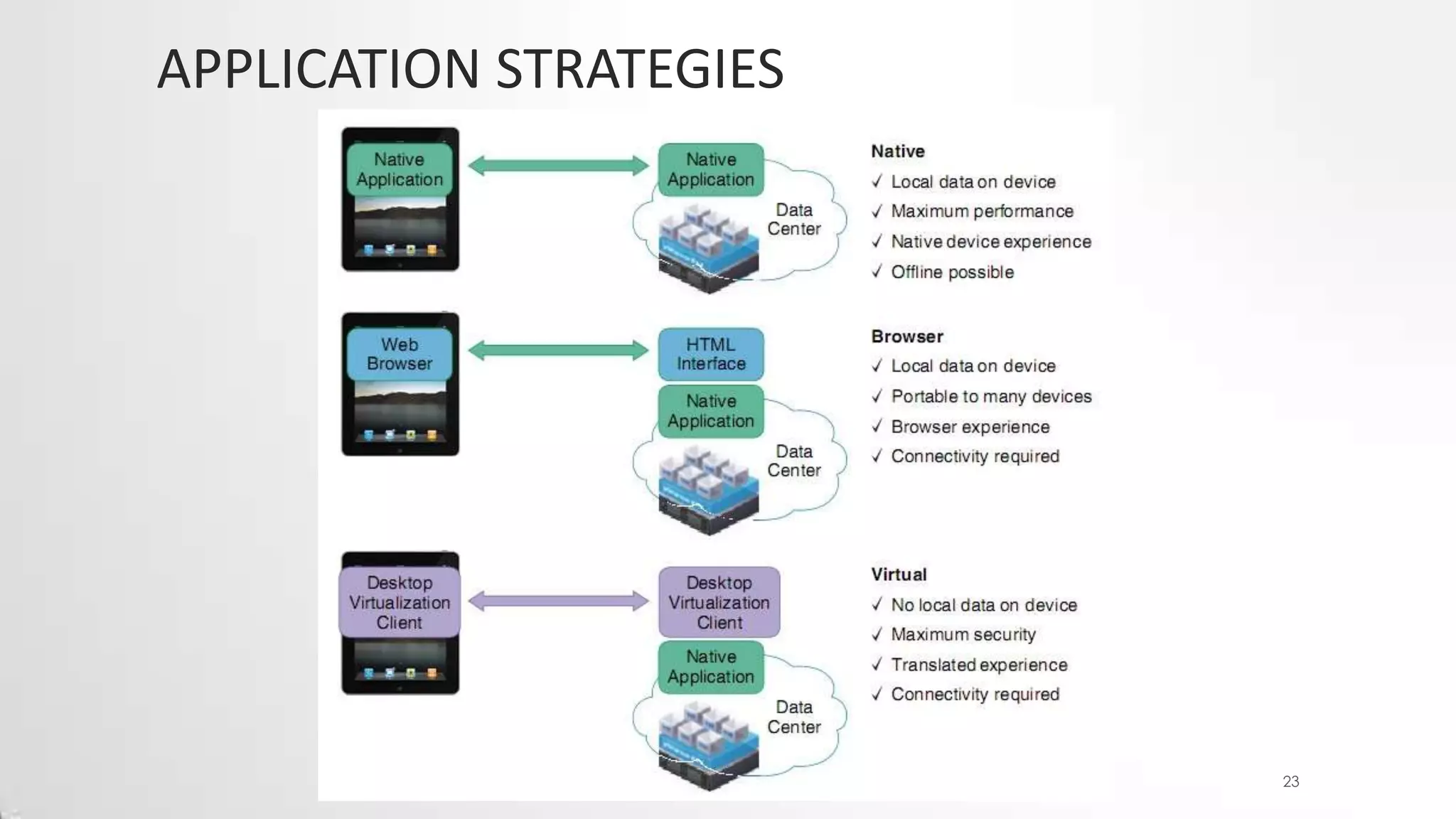
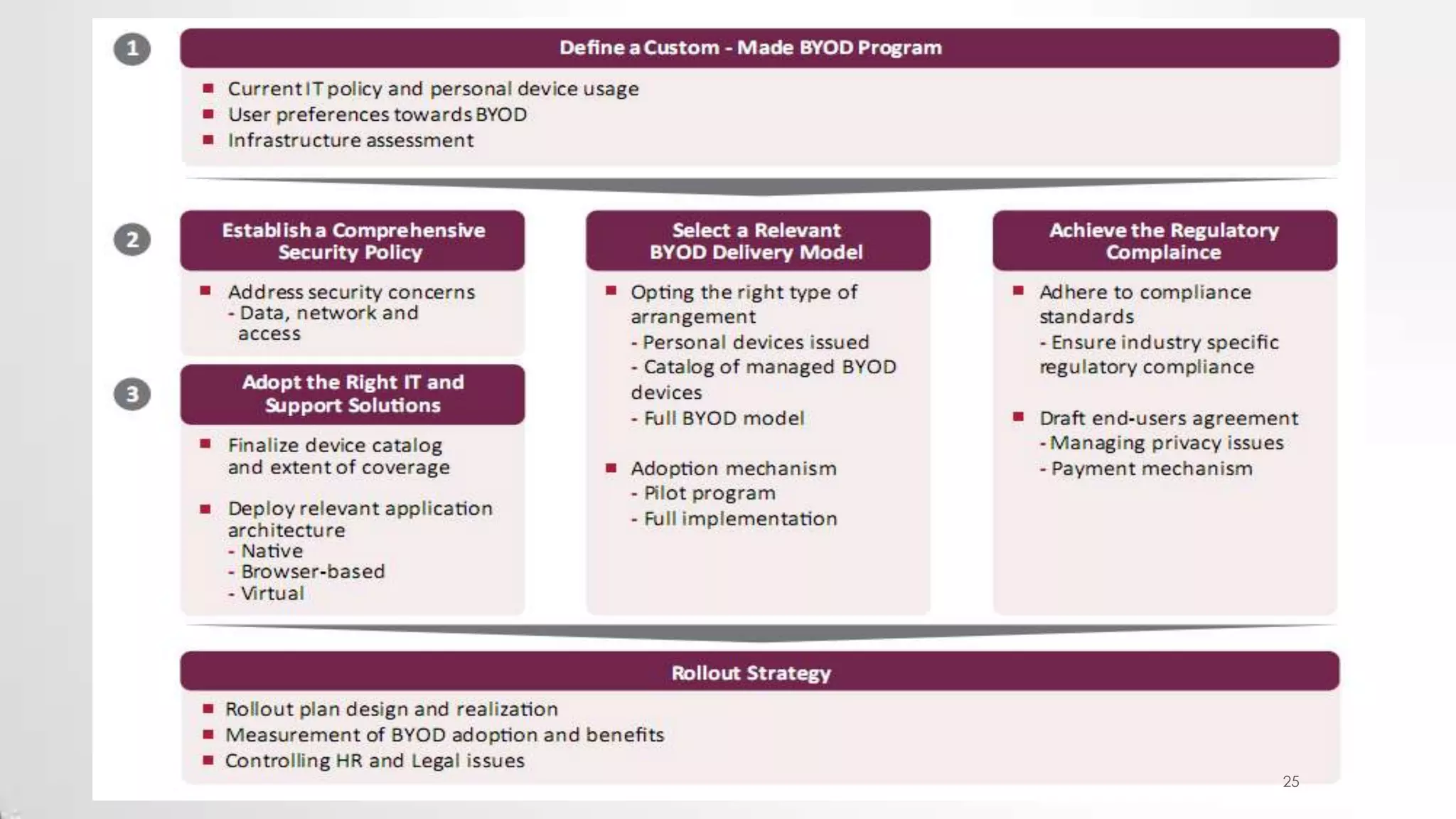
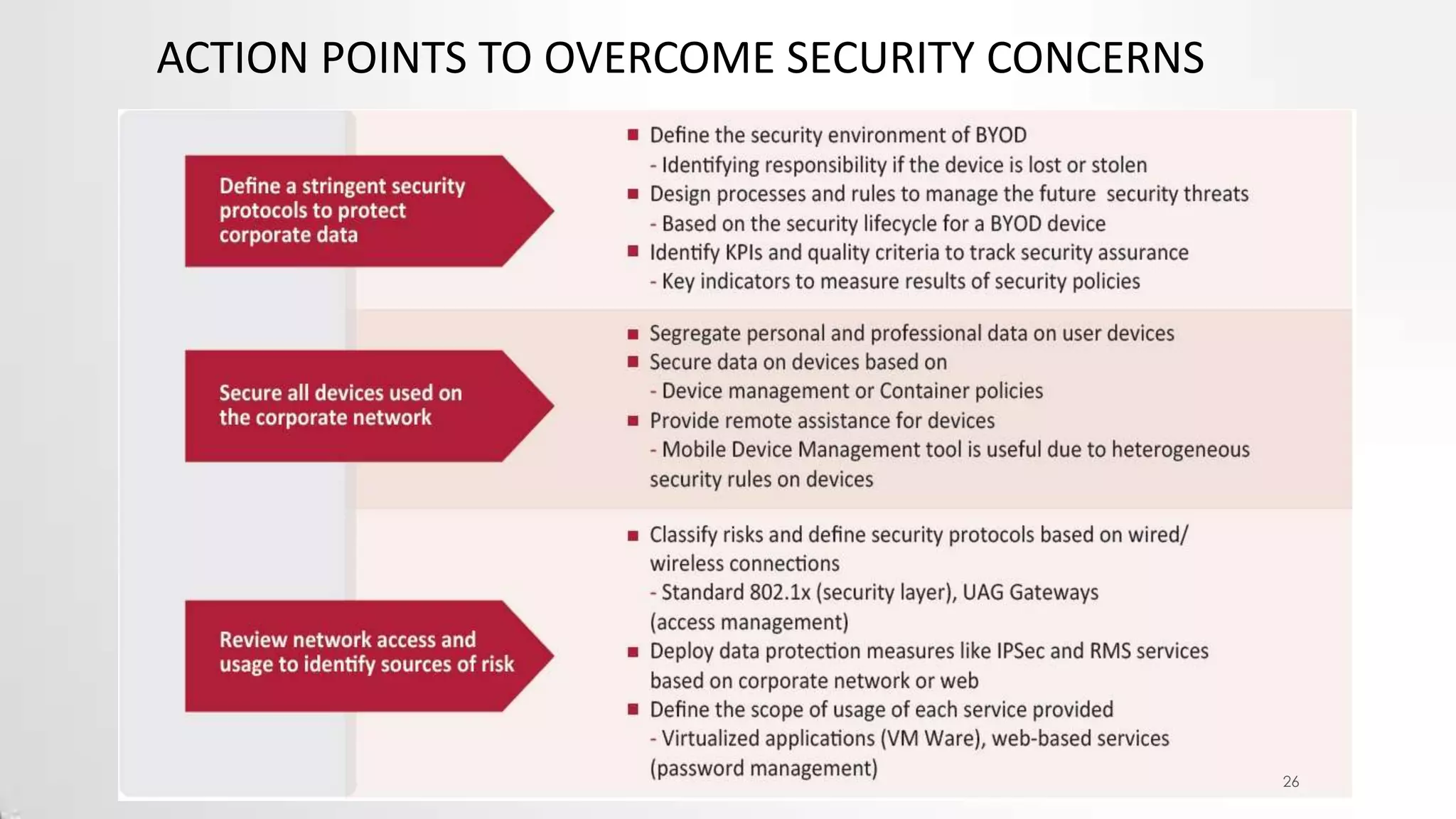
This document discusses Bring Your Own Device (BYOD) trends in IT. It defines BYOD as allowing employees to use personally owned devices for work purposes. The main conflict is that corporate IT aims to restrict devices, updates, and customization, while employees want open access like with personal devices. BYOD can improve productivity and mobility but challenges include security, support costs, and privacy. The document recommends mobile device management software, clear policies, risk analysis, and governance committees to help organizations balance BYOD benefits with risks.