Downloaded 360 times

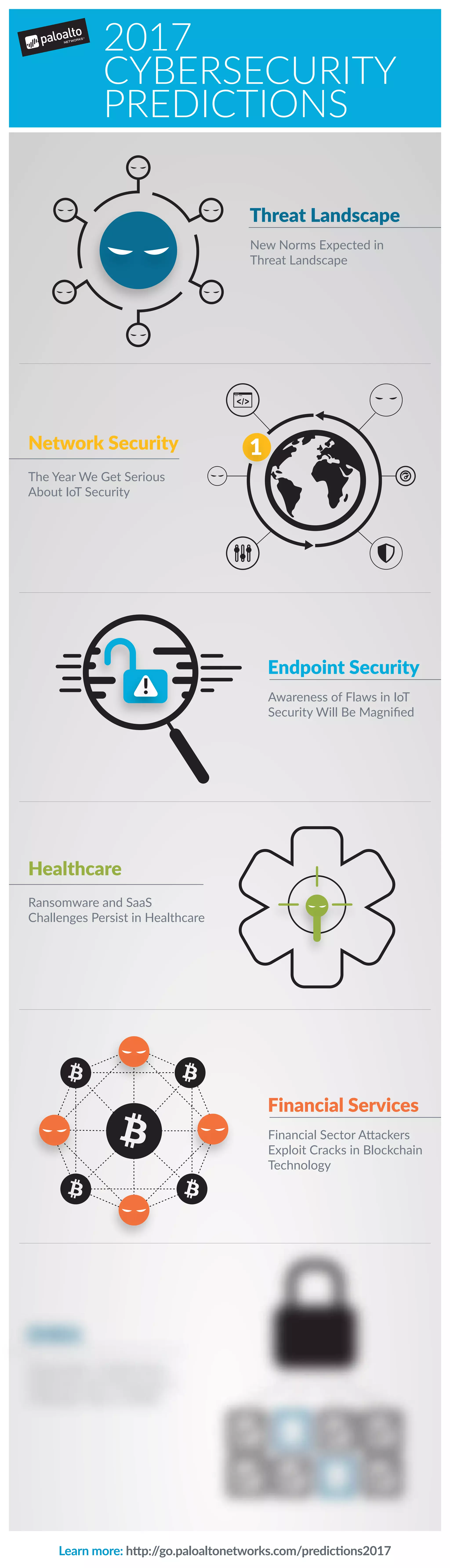
The document discusses the evolving threat landscape in cybersecurity, highlighting the search for diverse cyber talent and the implications of ransomware on critical infrastructure. It addresses concerns regarding Internet of Things (IoT) security, the challenges faced by financial services, and the anticipated growth in cybersecurity measures for 2017 in various regions. Additionally, it emphasizes the importance of threat intelligence sharing and the adoption of automation in addressing these challenges.