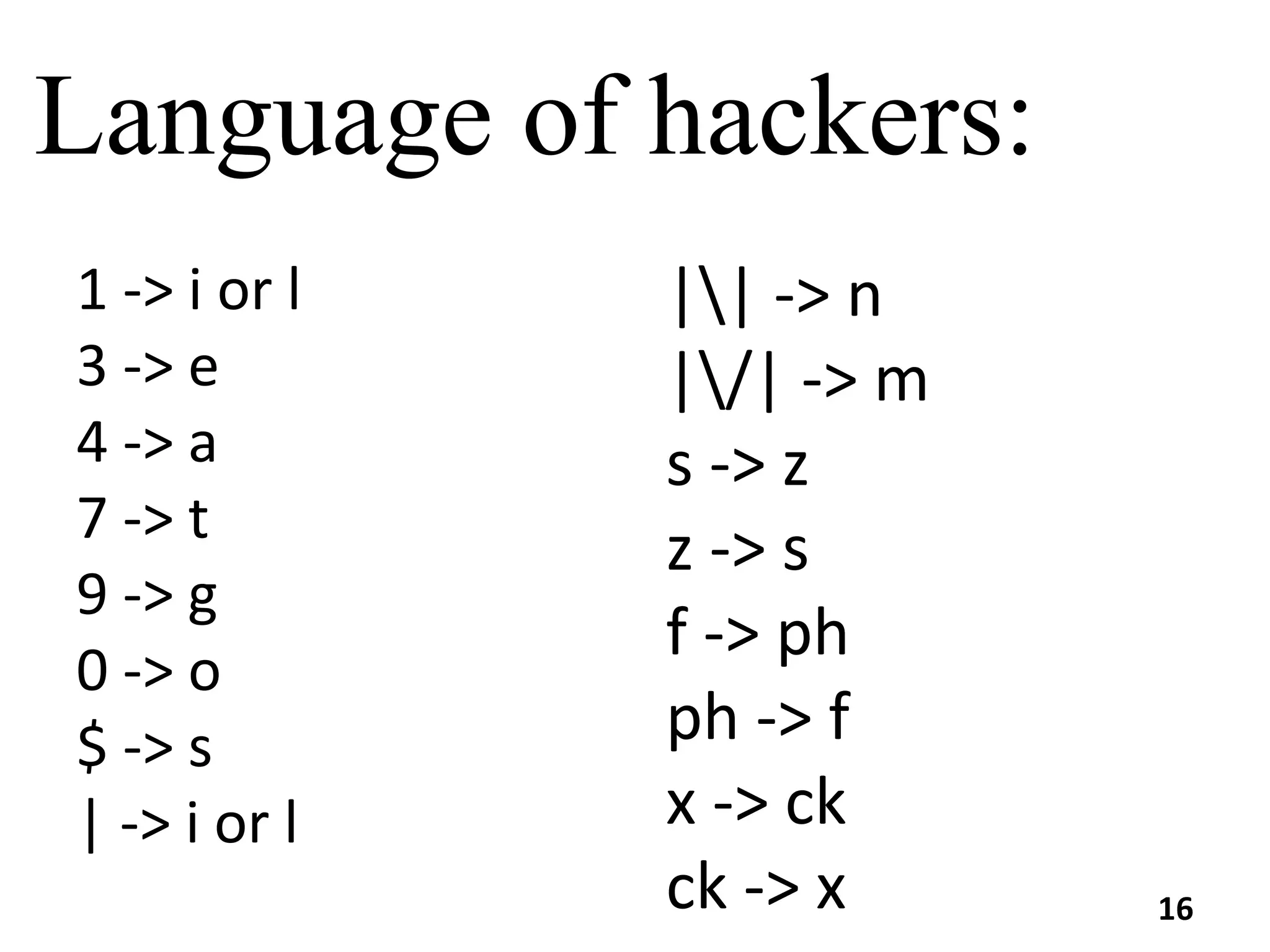
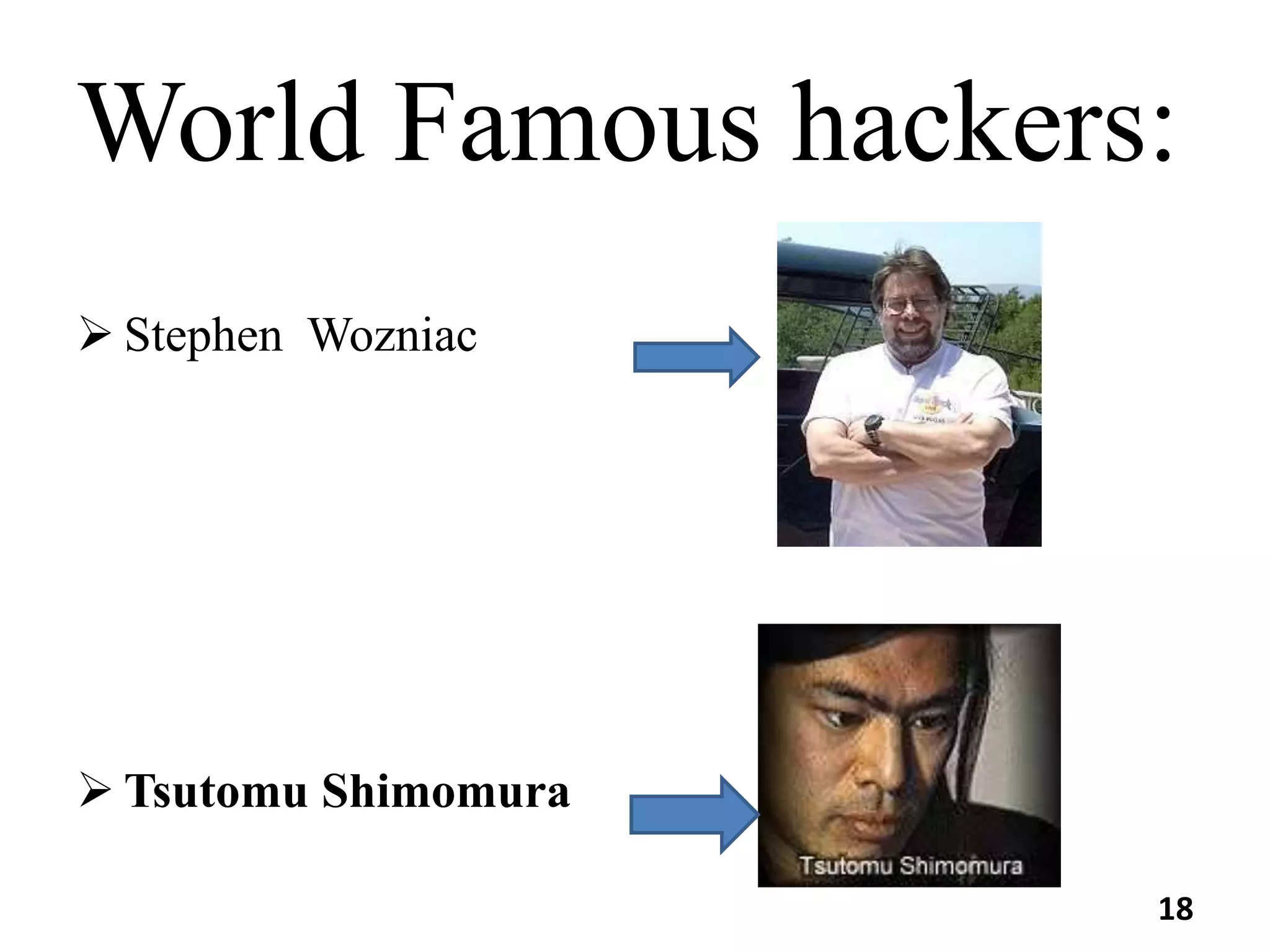
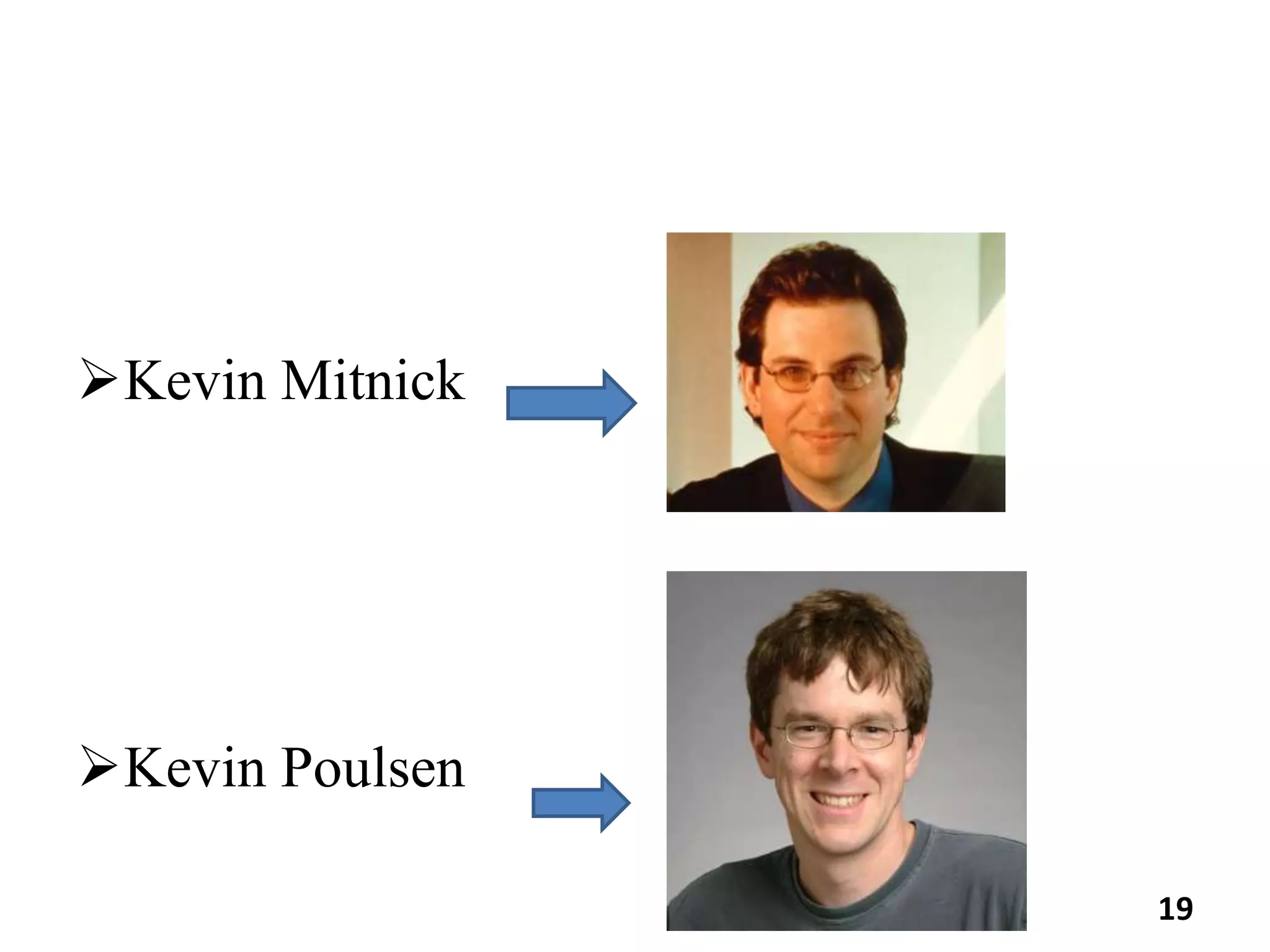
The document discusses hacking, including its meaning, reasons people hack, various types of hacking (such as website, email, network, password, and online banking hacking), and the categories of hackers (white-hat, black-hat, and grey-hat). It also emphasizes preventative measures against hacking and concludes with a call for ethical hacking practices. Additionally, it mentions the age range of typical hackers and lists some famous hackers.