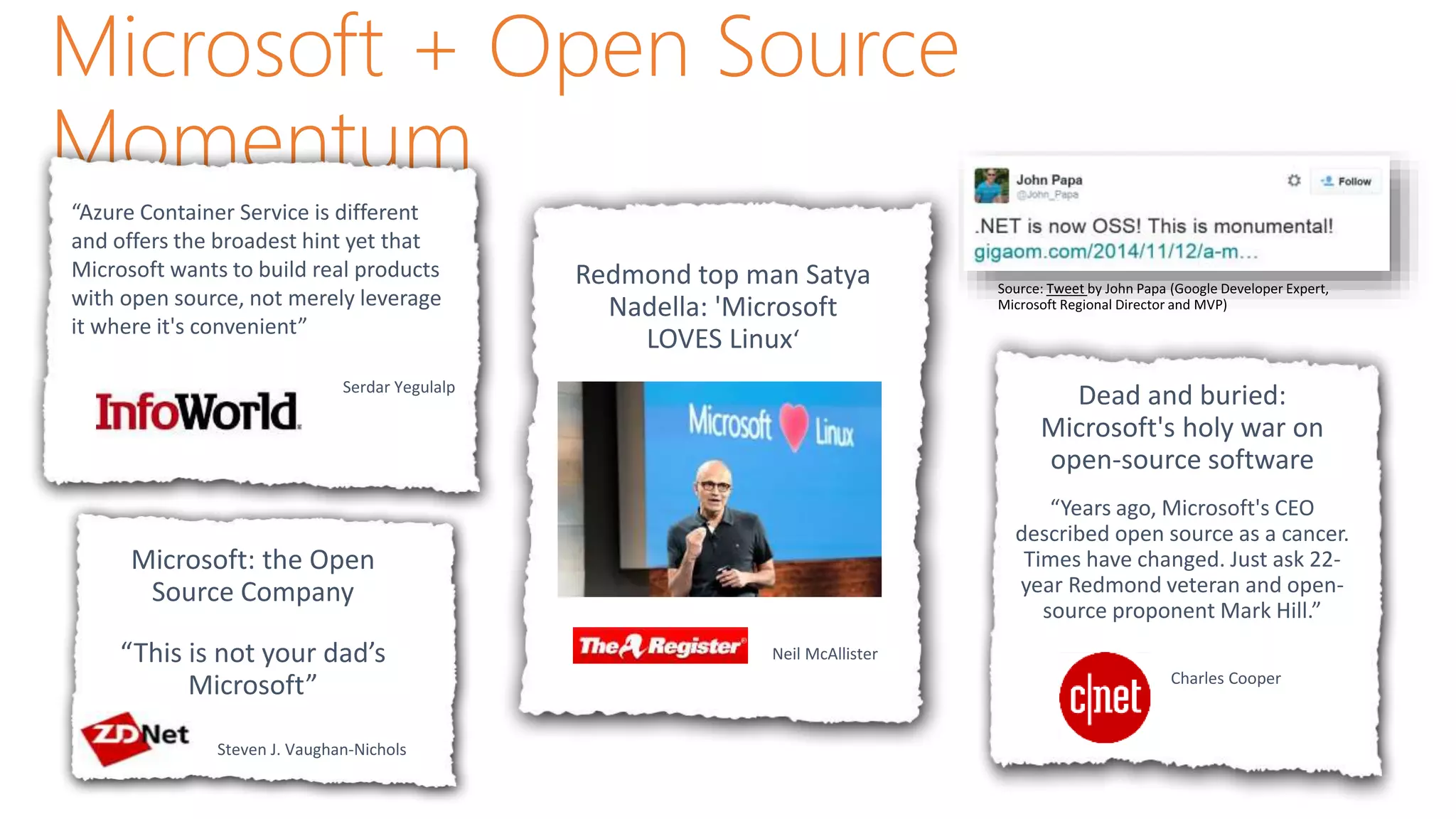
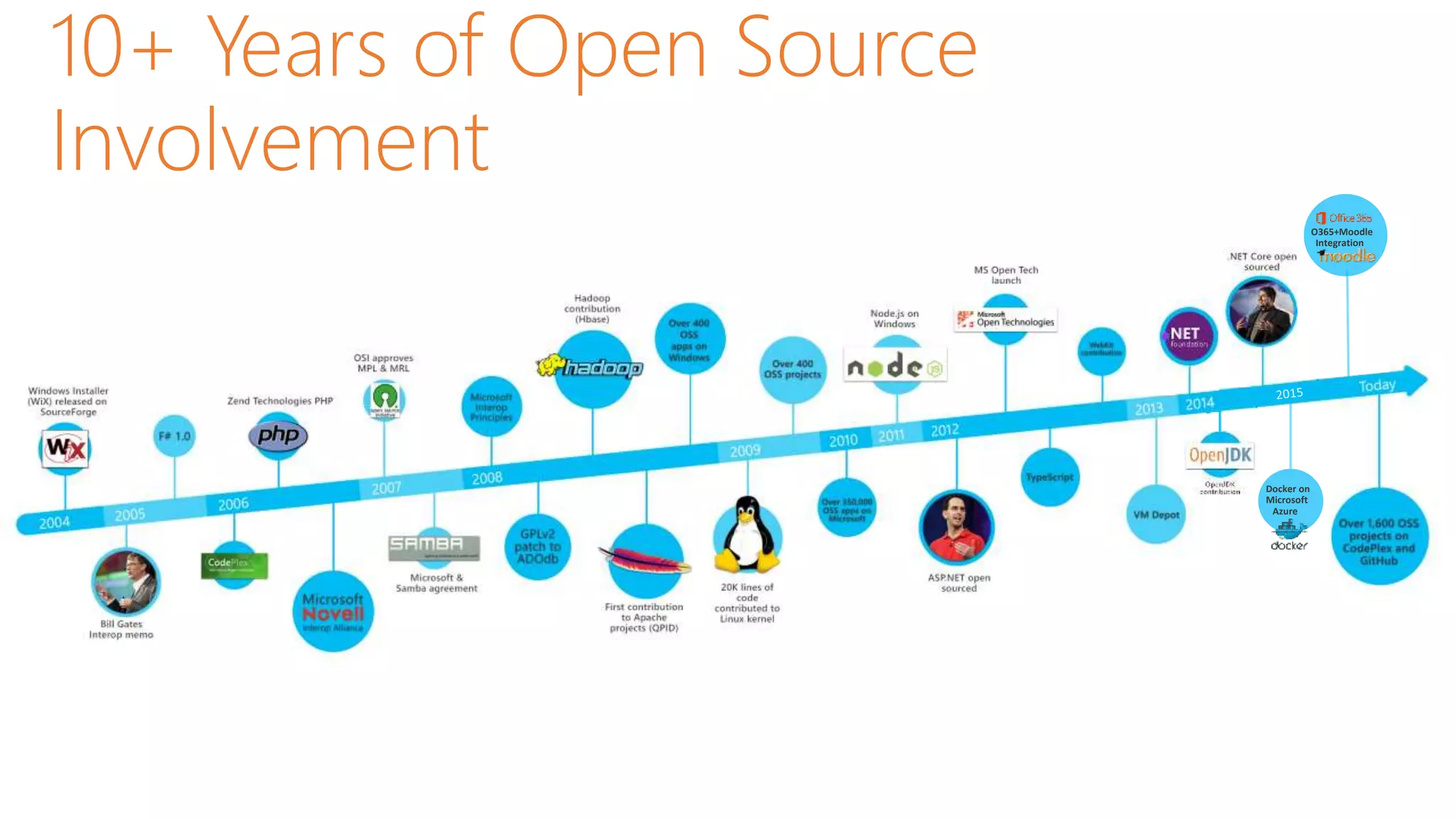
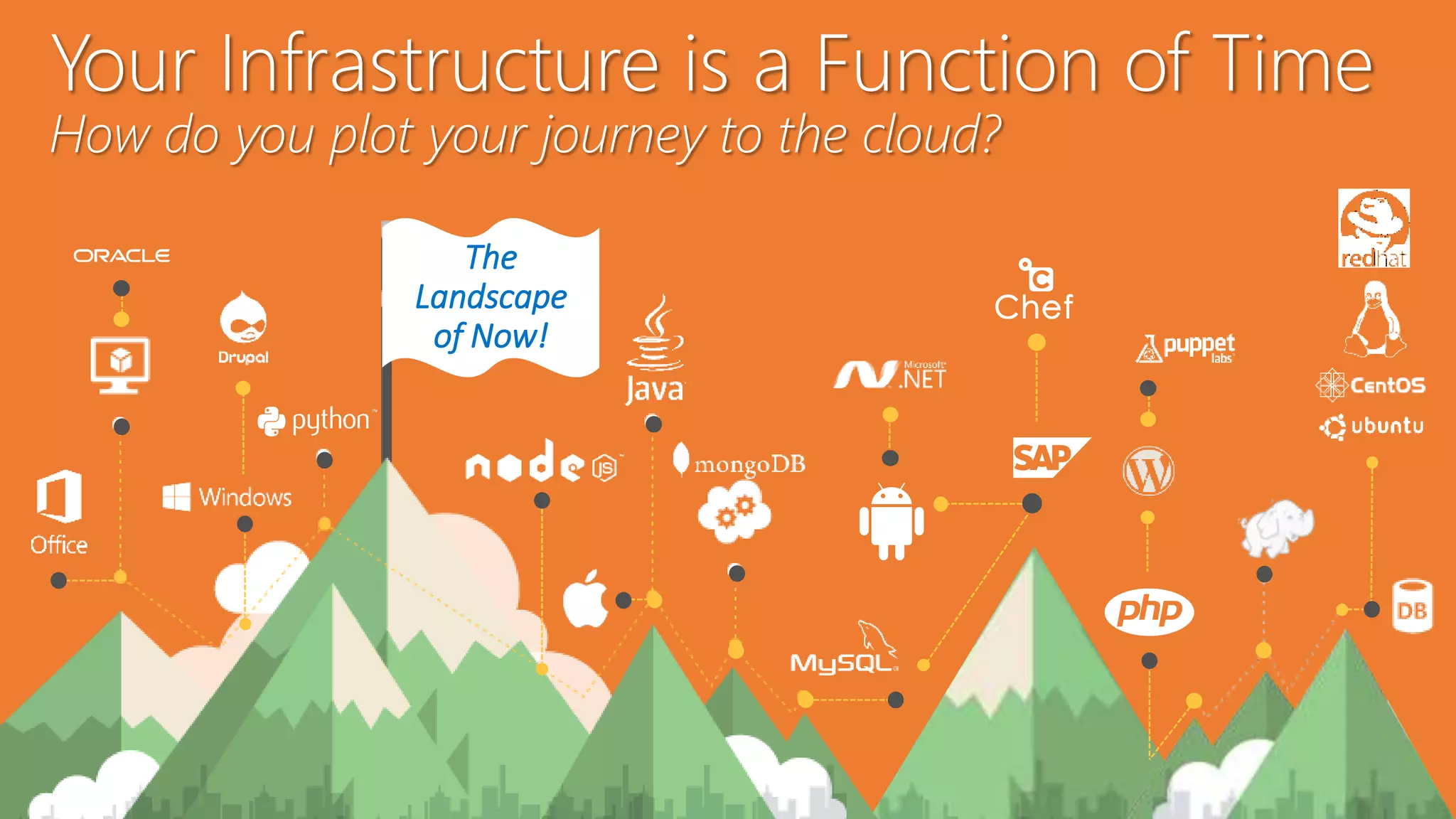
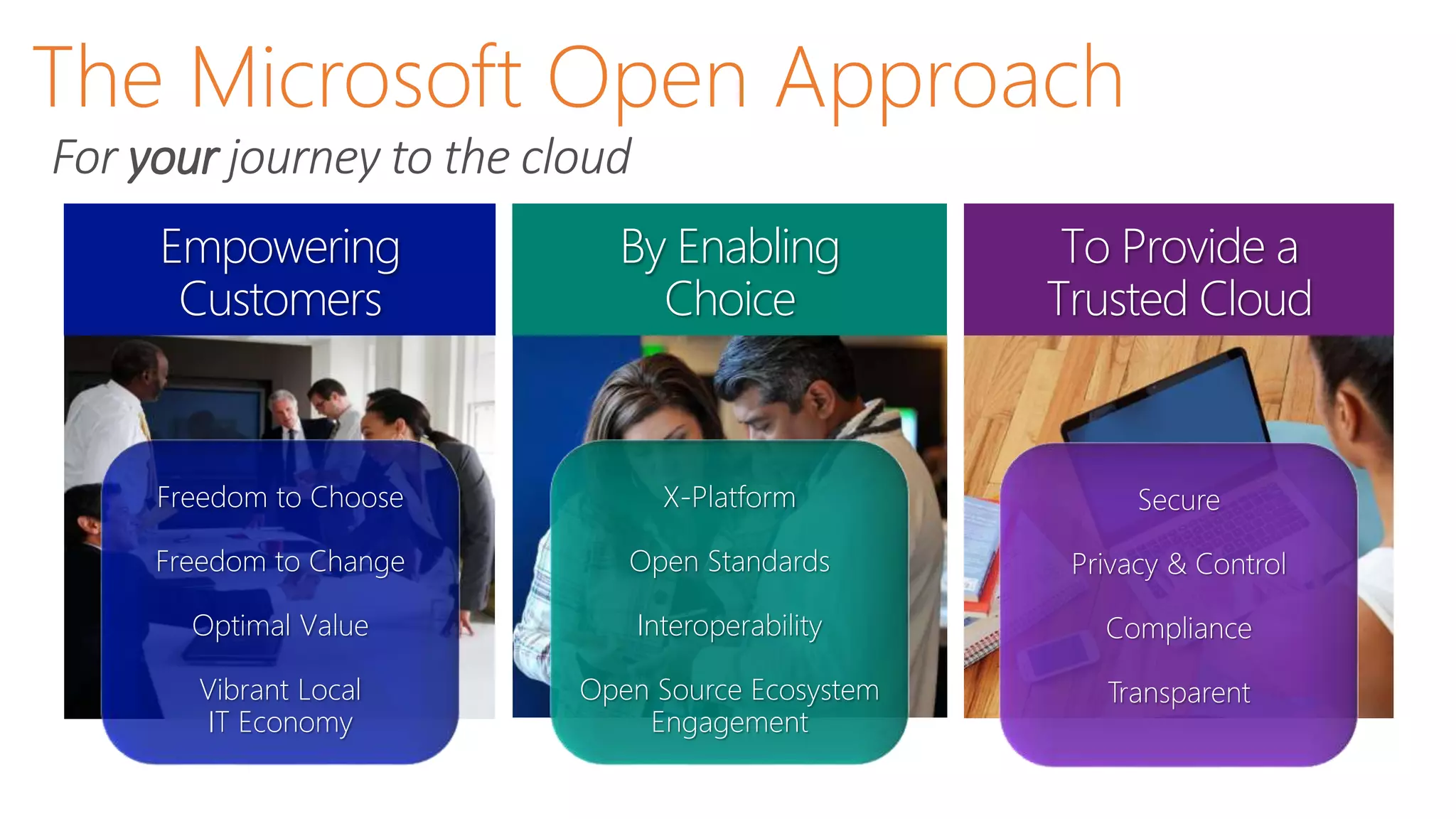
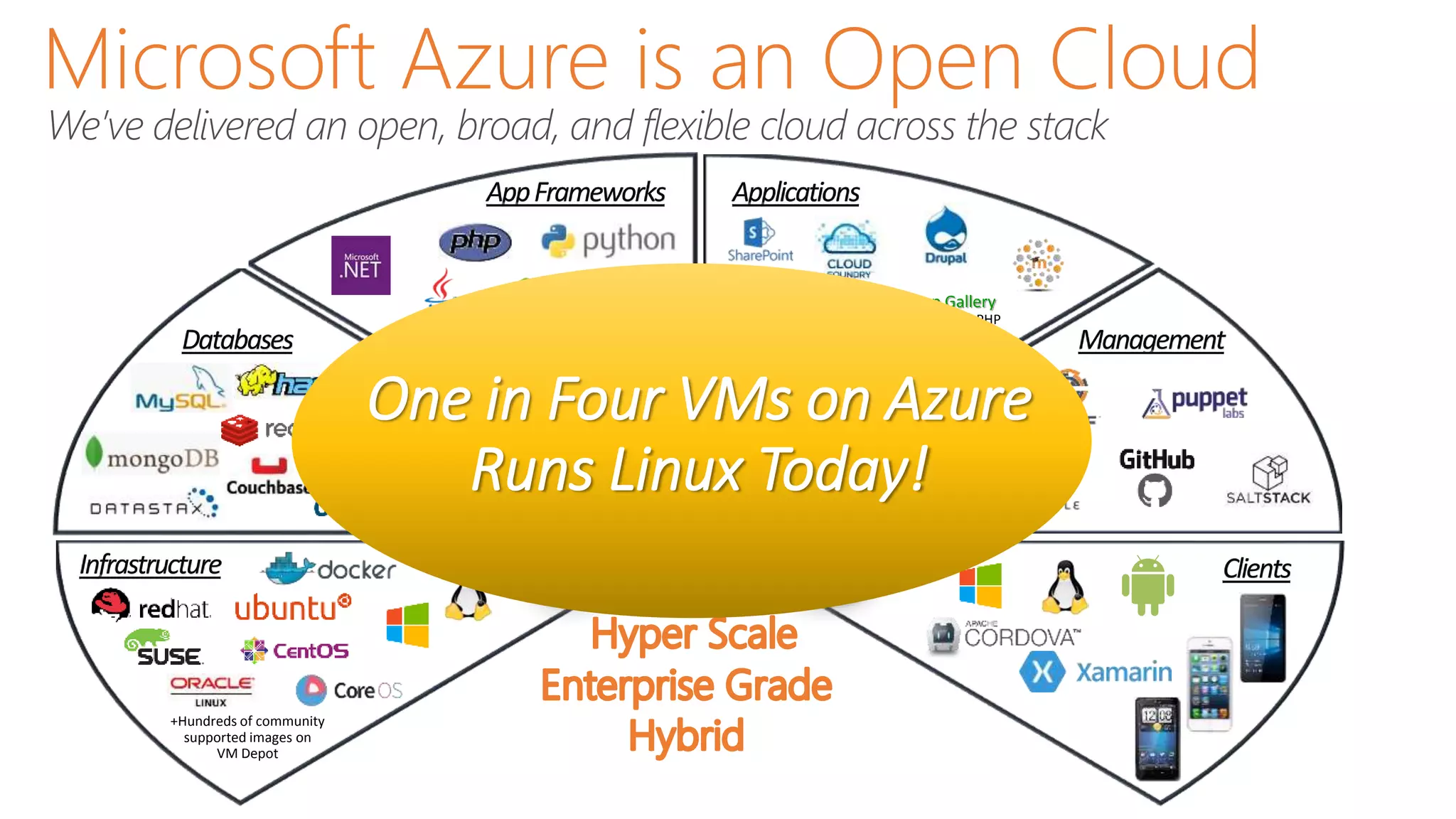
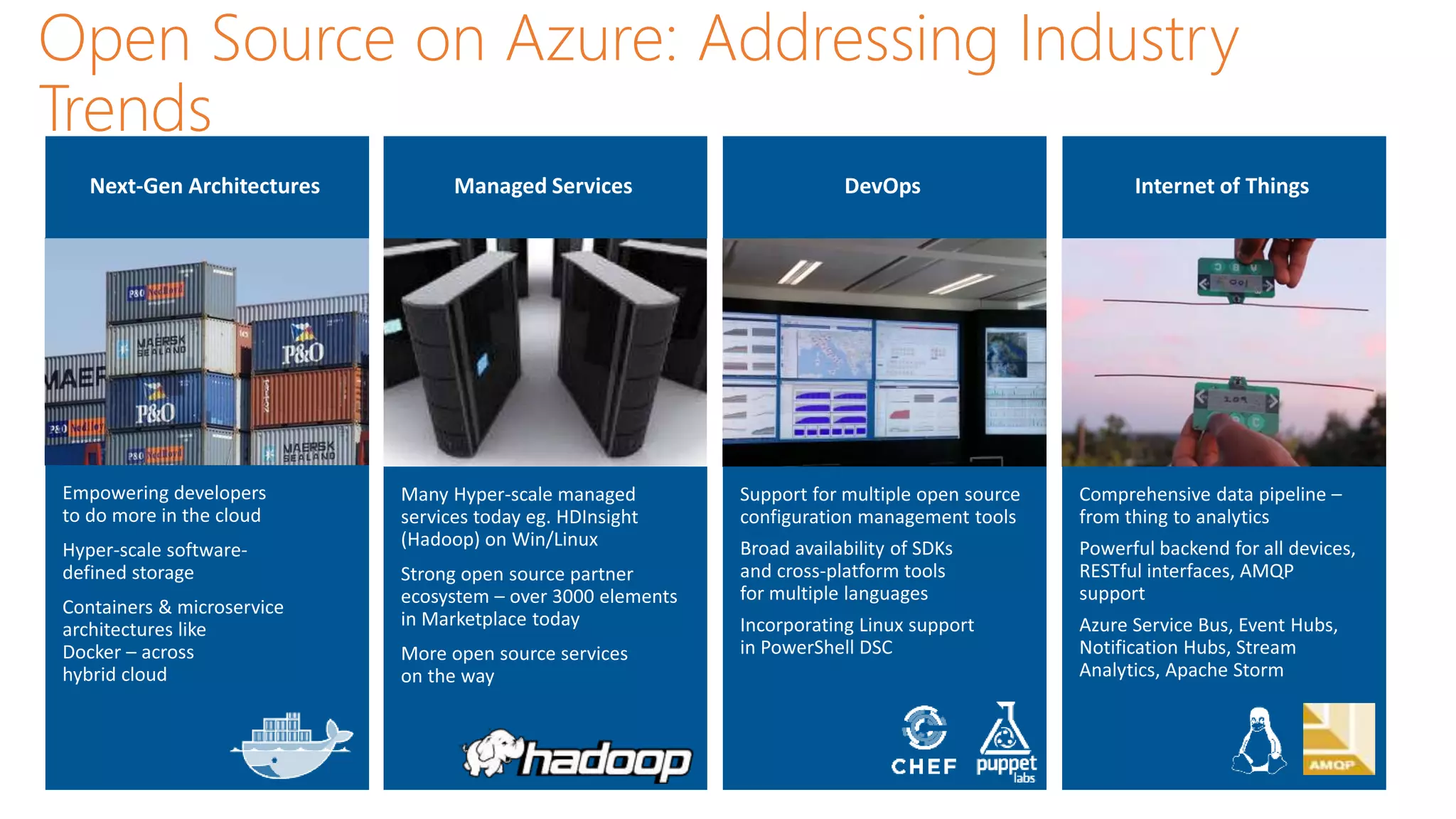
This document discusses Microsoft's shift towards embracing open source software and becoming more open. It notes that Microsoft's CEO now views open source positively rather than as a "cancer" as in the past. It provides examples of Microsoft's involvement in open source, including supporting Linux on Azure and open standards. The document advocates that Microsoft wants to build products with open source rather than just leverage it where convenient. It argues this shift shows Microsoft has become more open and customer-focused under new leadership.