0% found this document useful (0 votes)
16 views15 pagesQuestion and Answer
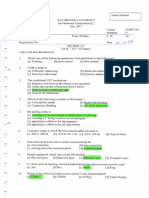
The OSI model is a seven-layer framework that describes how data is transmitted over a network, with each layer performing specific functions. The layers include Physical, Data-Link, Network, Transport, Session, Presentation, and Application, each responsible for different aspects of data communication. The document also briefly compares the OSI model with the TCP/IP model, highlighting their respective layers and functionalities.
Uploaded by
BALAJI DCopyright
© © All Rights Reserved
We take content rights seriously. If you suspect this is your content, claim it here.
Available Formats
Download as DOCX, PDF, TXT or read online on Scribd
0% found this document useful (0 votes)
16 views15 pagesQuestion and Answer
The OSI model is a seven-layer framework that describes how data is transmitted over a network, with each layer performing specific functions. The layers include Physical, Data-Link, Network, Transport, Session, Presentation, and Application, each responsible for different aspects of data communication. The document also briefly compares the OSI model with the TCP/IP model, highlighting their respective layers and functionalities.
Uploaded by
BALAJI DCopyright
© © All Rights Reserved
We take content rights seriously. If you suspect this is your content, claim it here.
Available Formats
Download as DOCX, PDF, TXT or read online on Scribd
/ 15