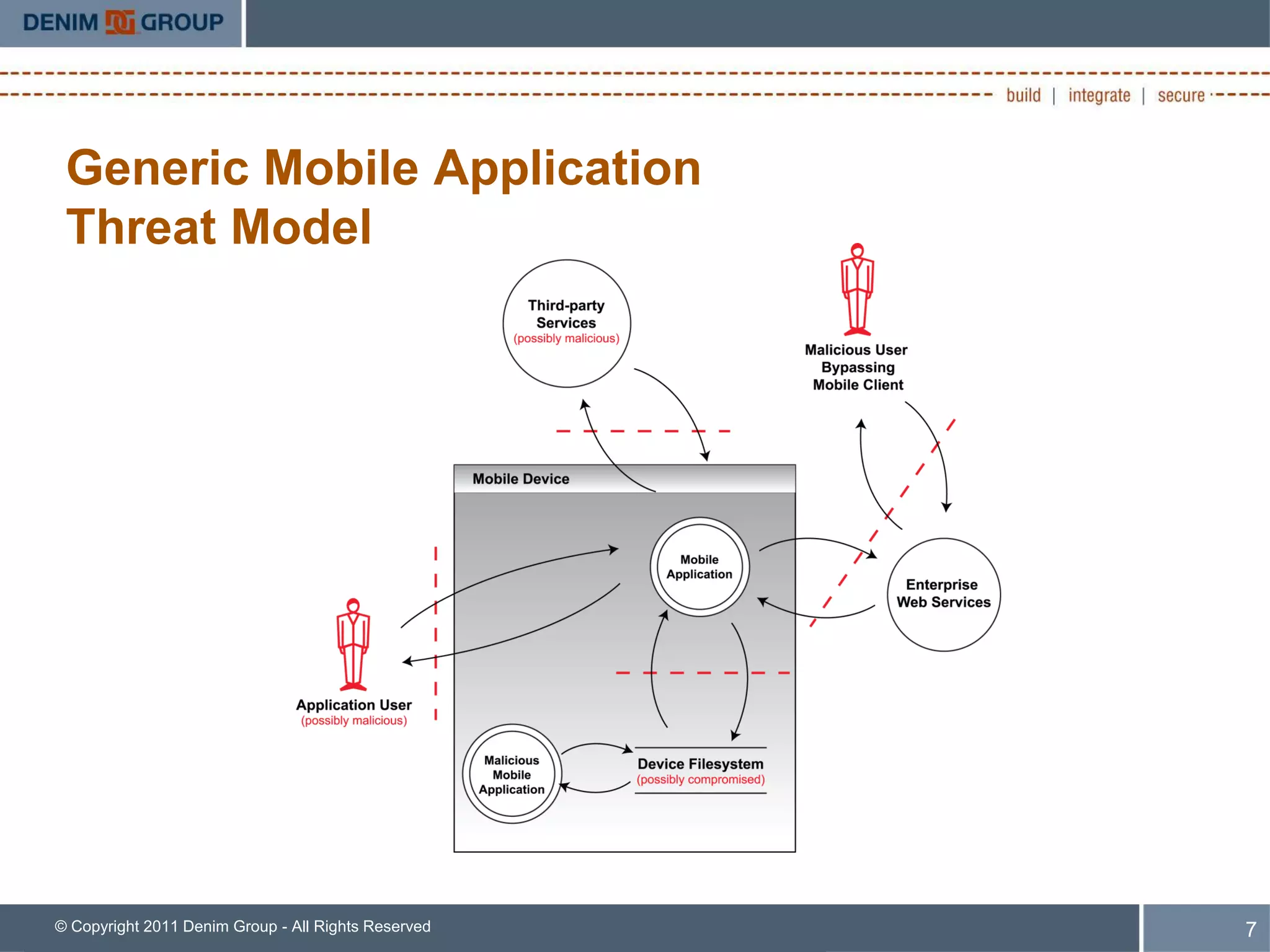
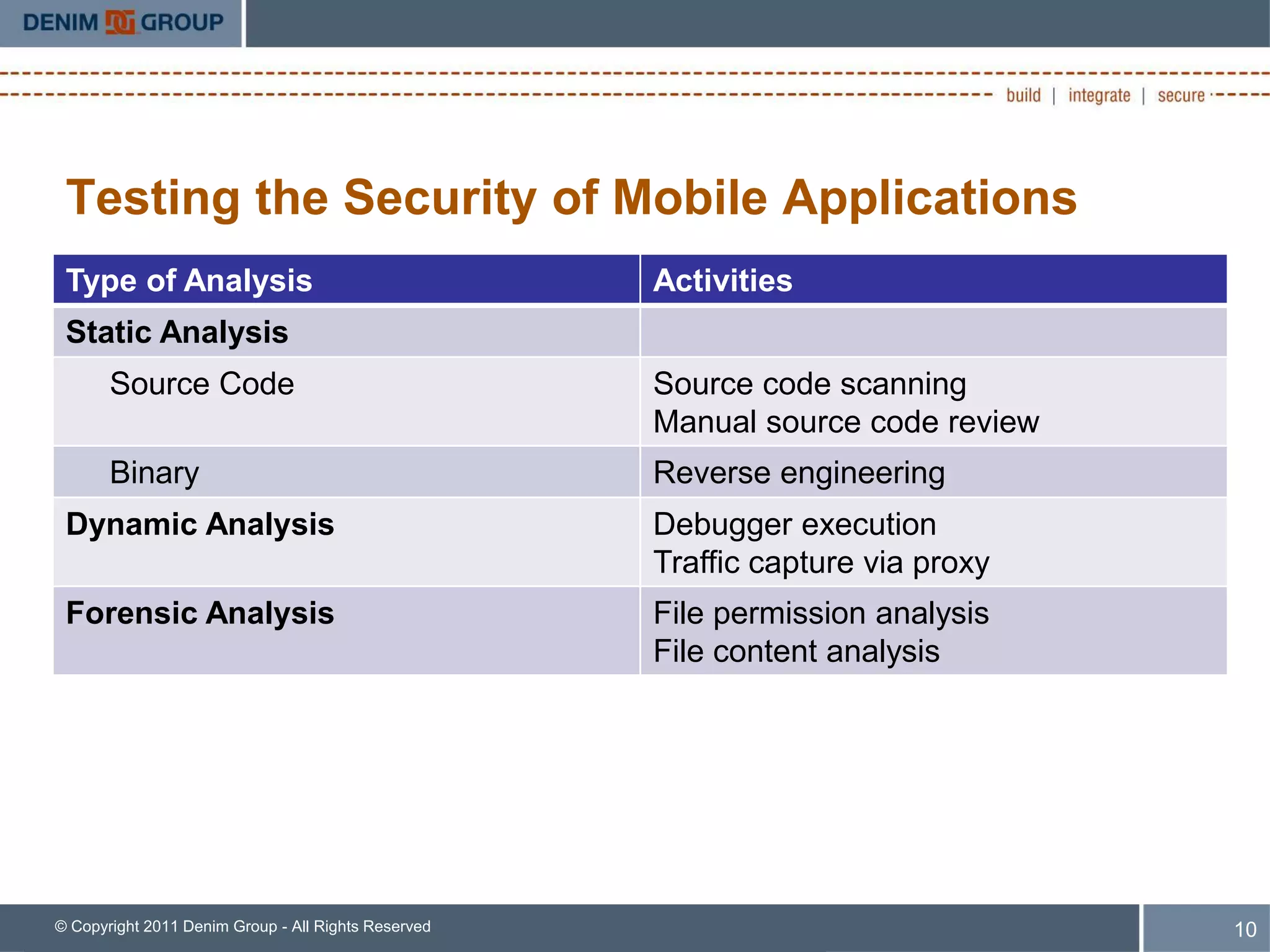
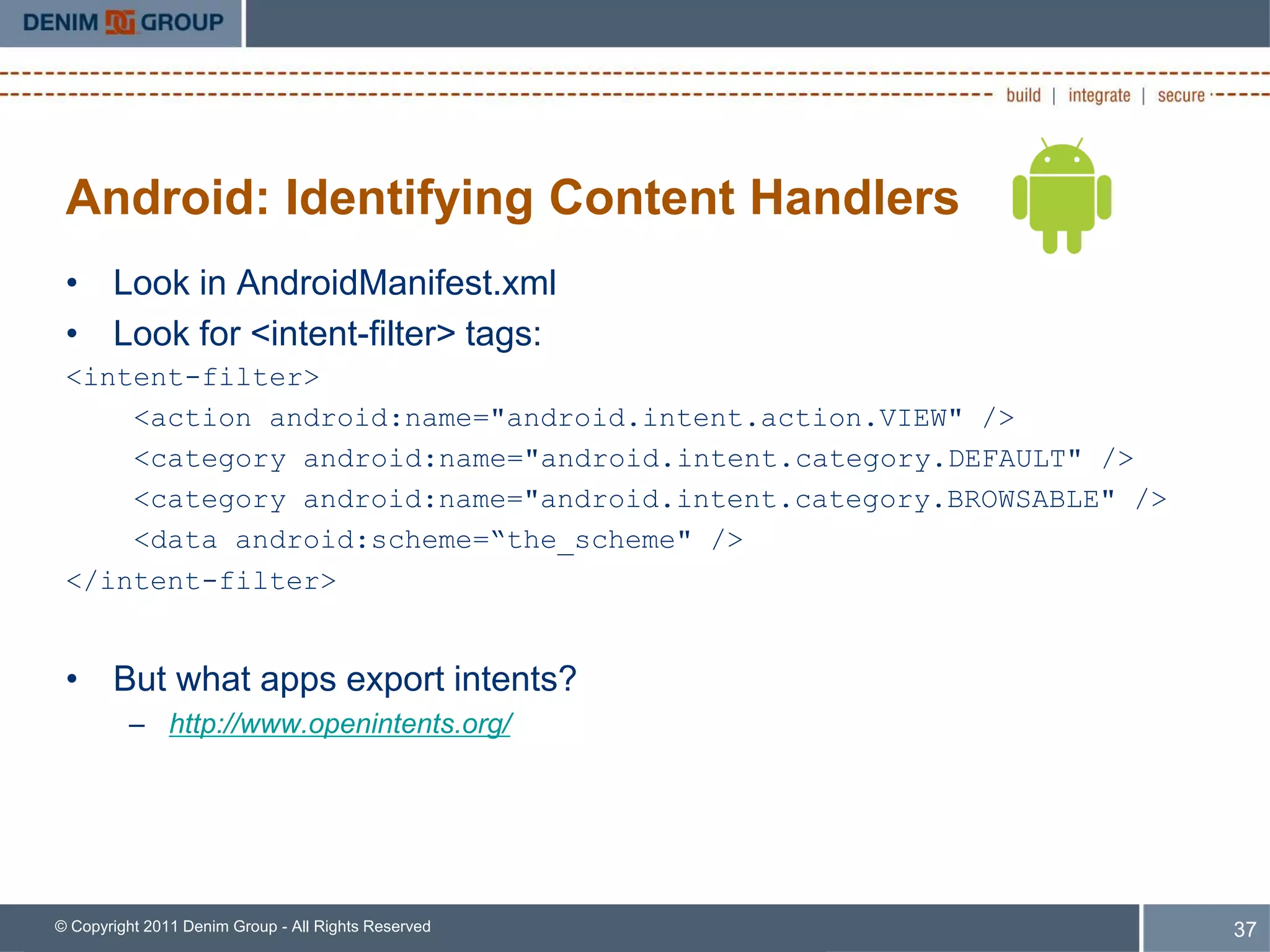
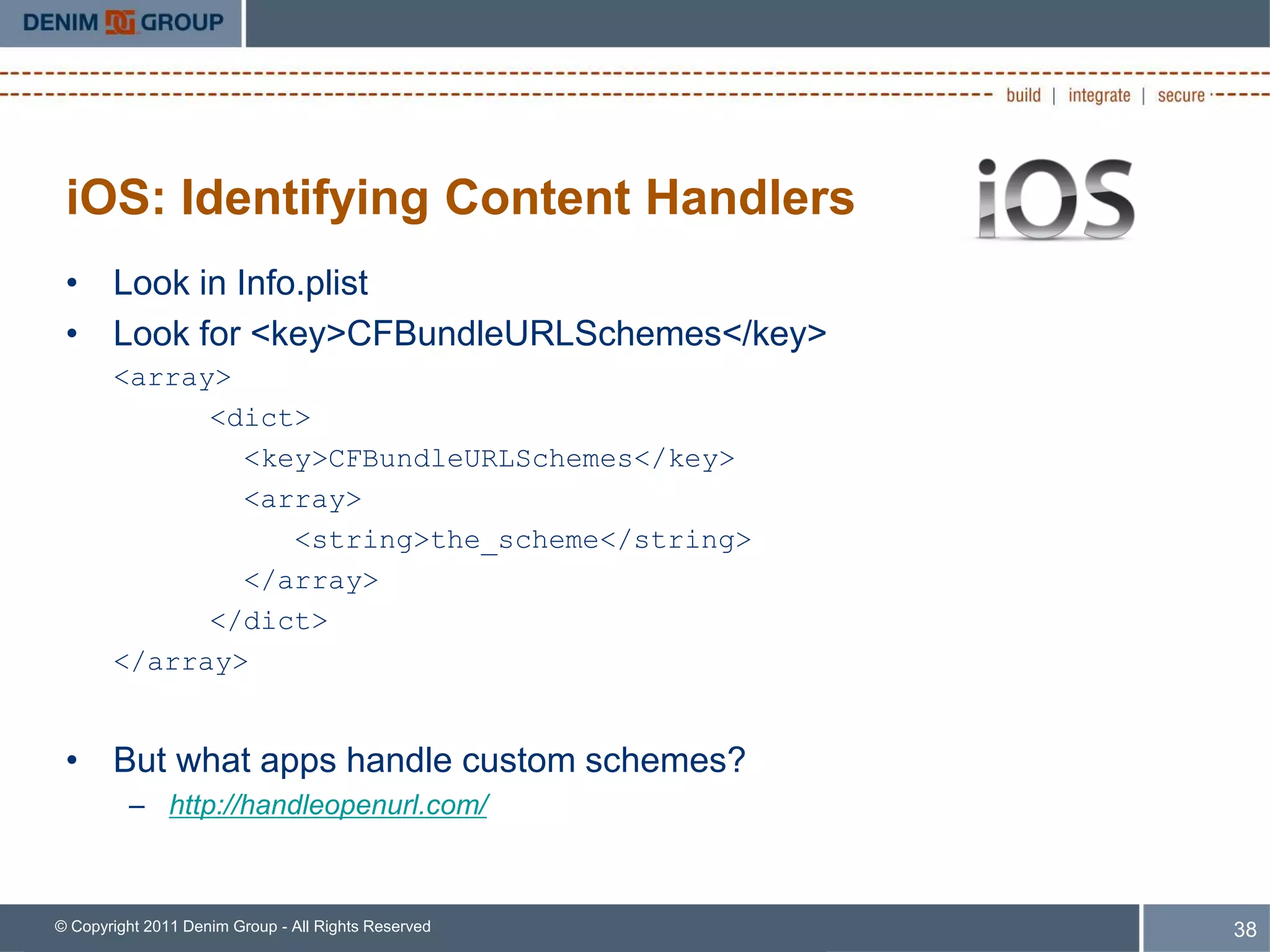
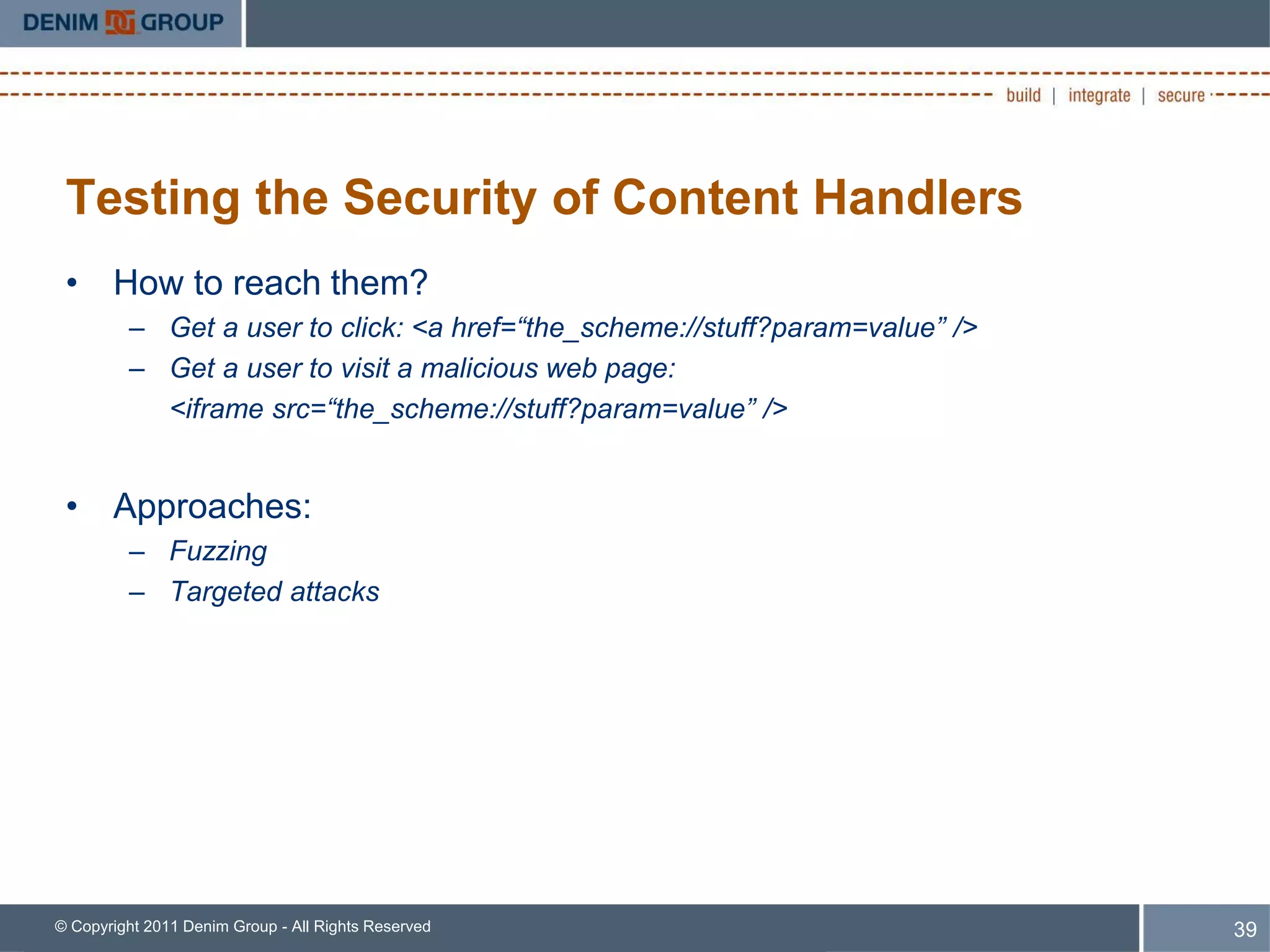
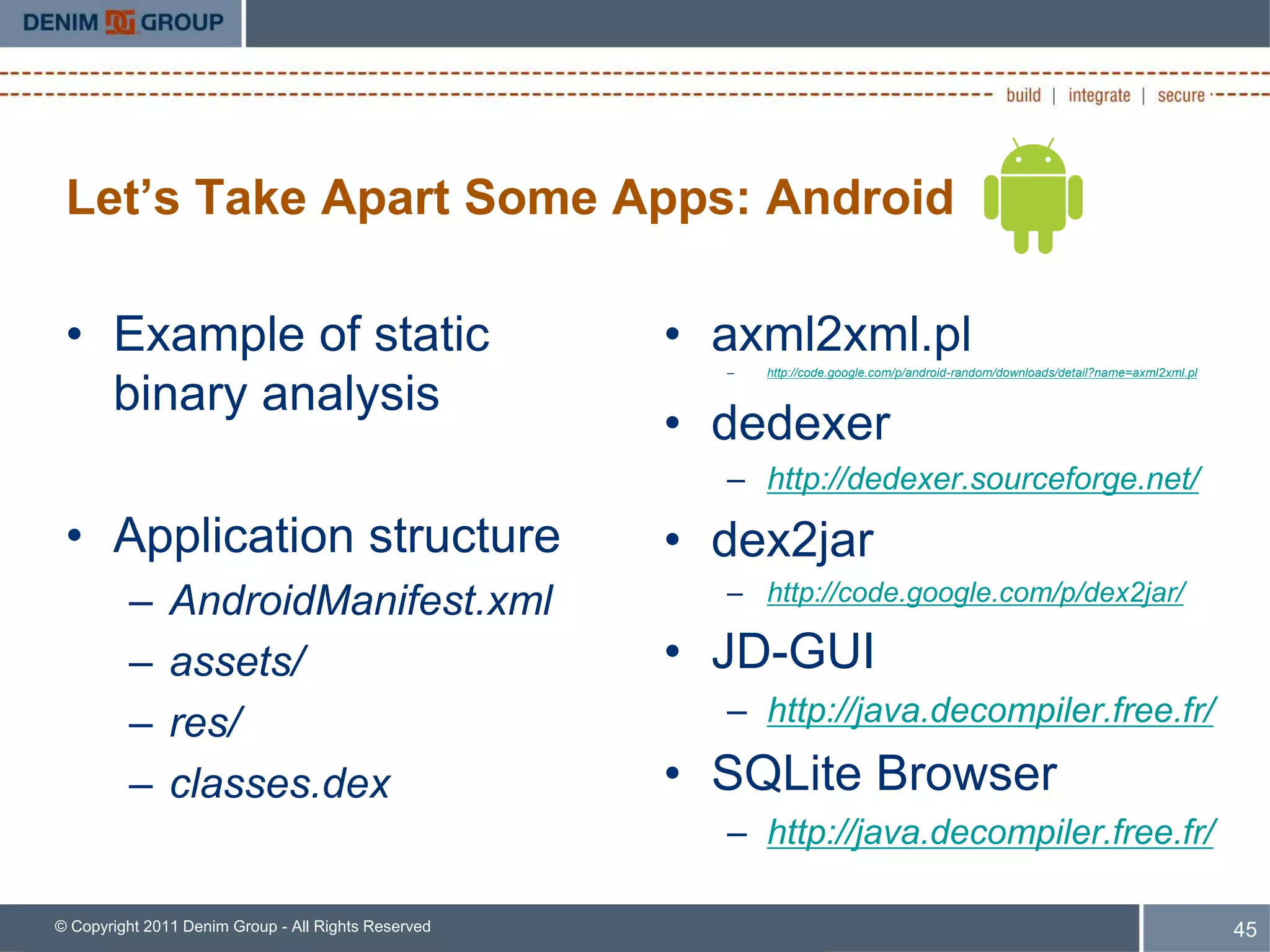
This document provides an overview of a mobile app security code review presentation given at BSides Las Vegas 2011. The presentation focused on identifying security issues in mobile apps related to data storage, third-party services, and untrusted inputs. It also covered platform-specific concerns for Android and iOS apps, such as encryption best practices, network communication standards, and input validation. Static code analysis techniques were discussed for examining how apps store data, access external services, and handle untrusted content.