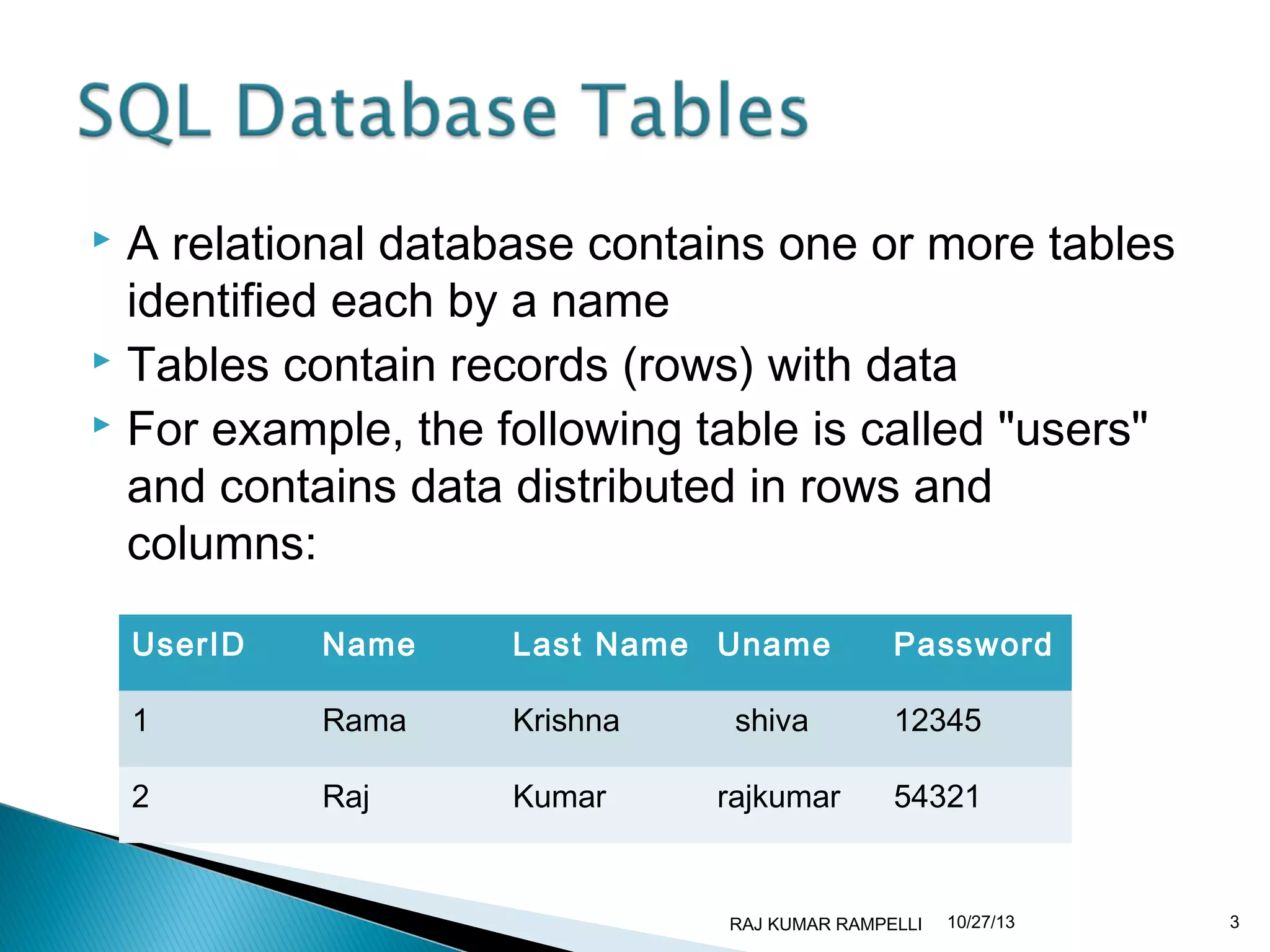
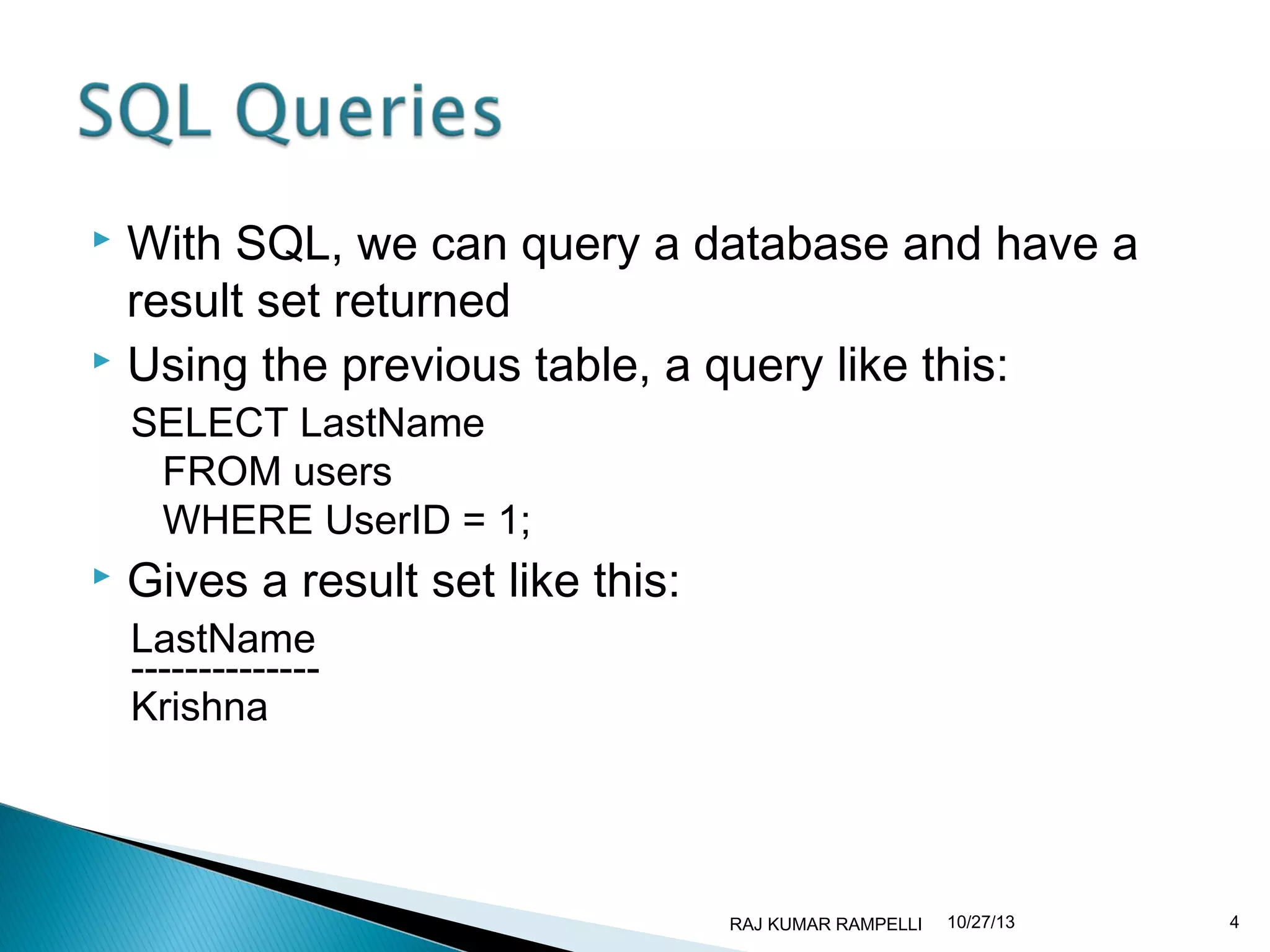
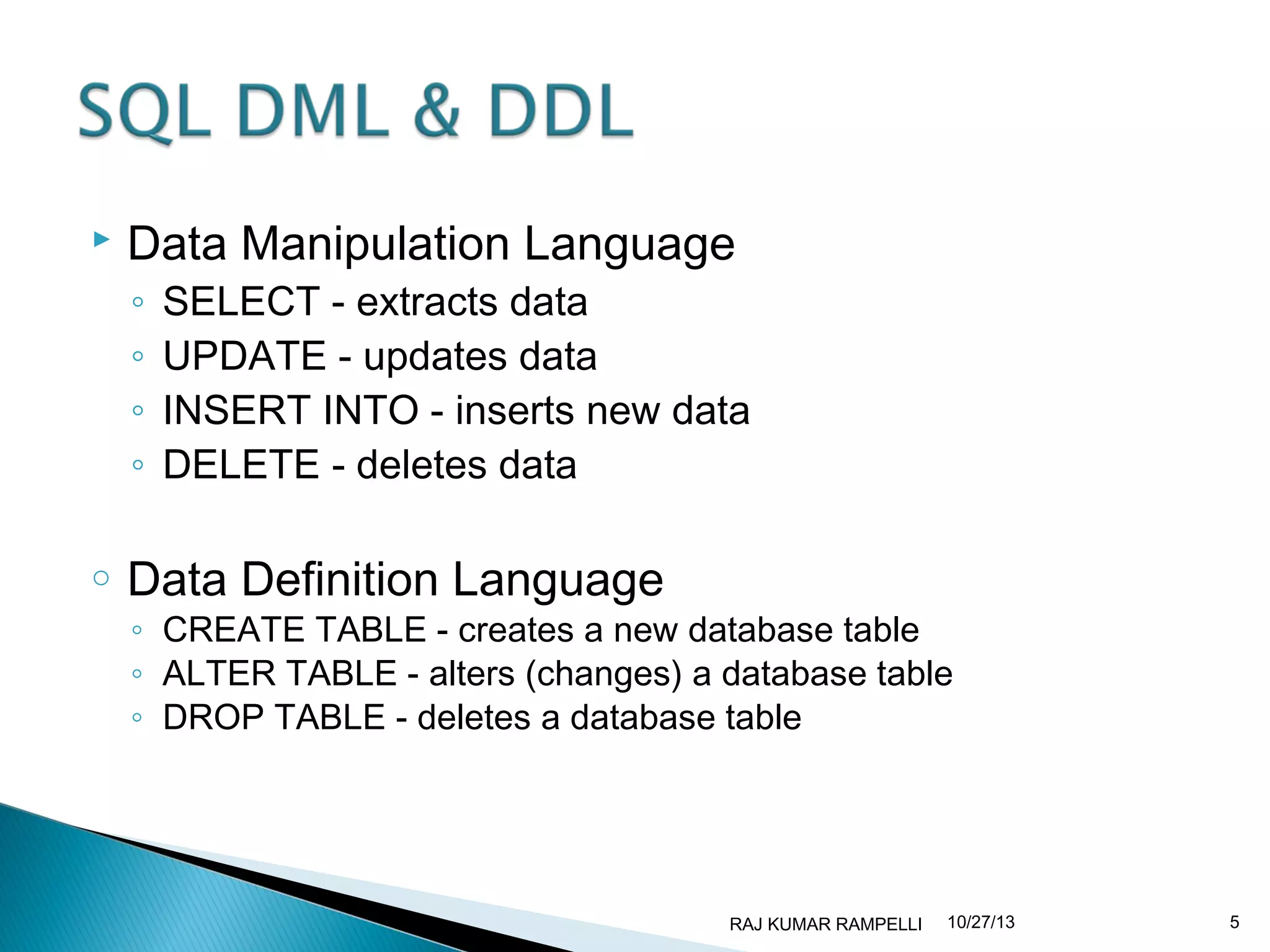
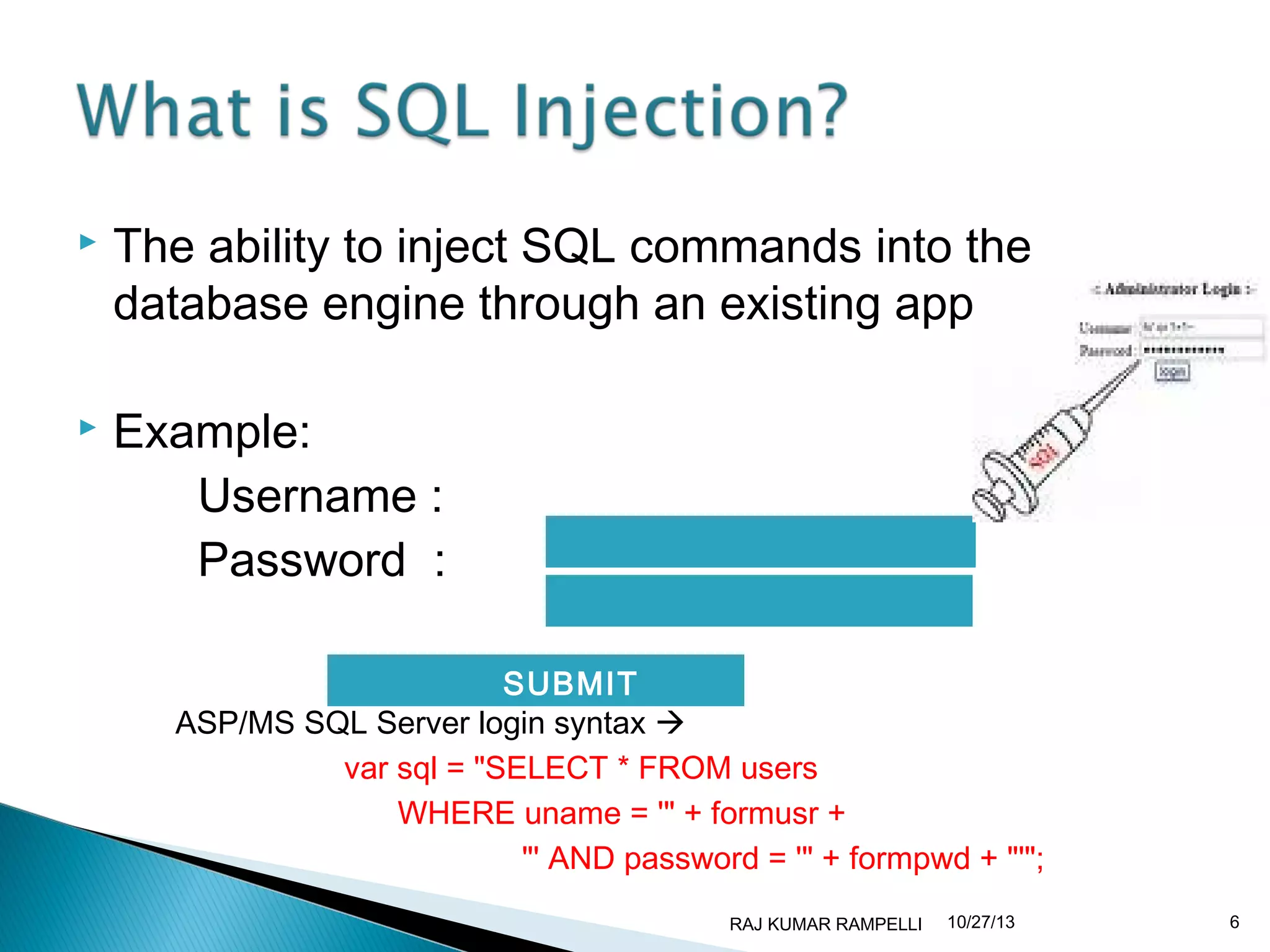
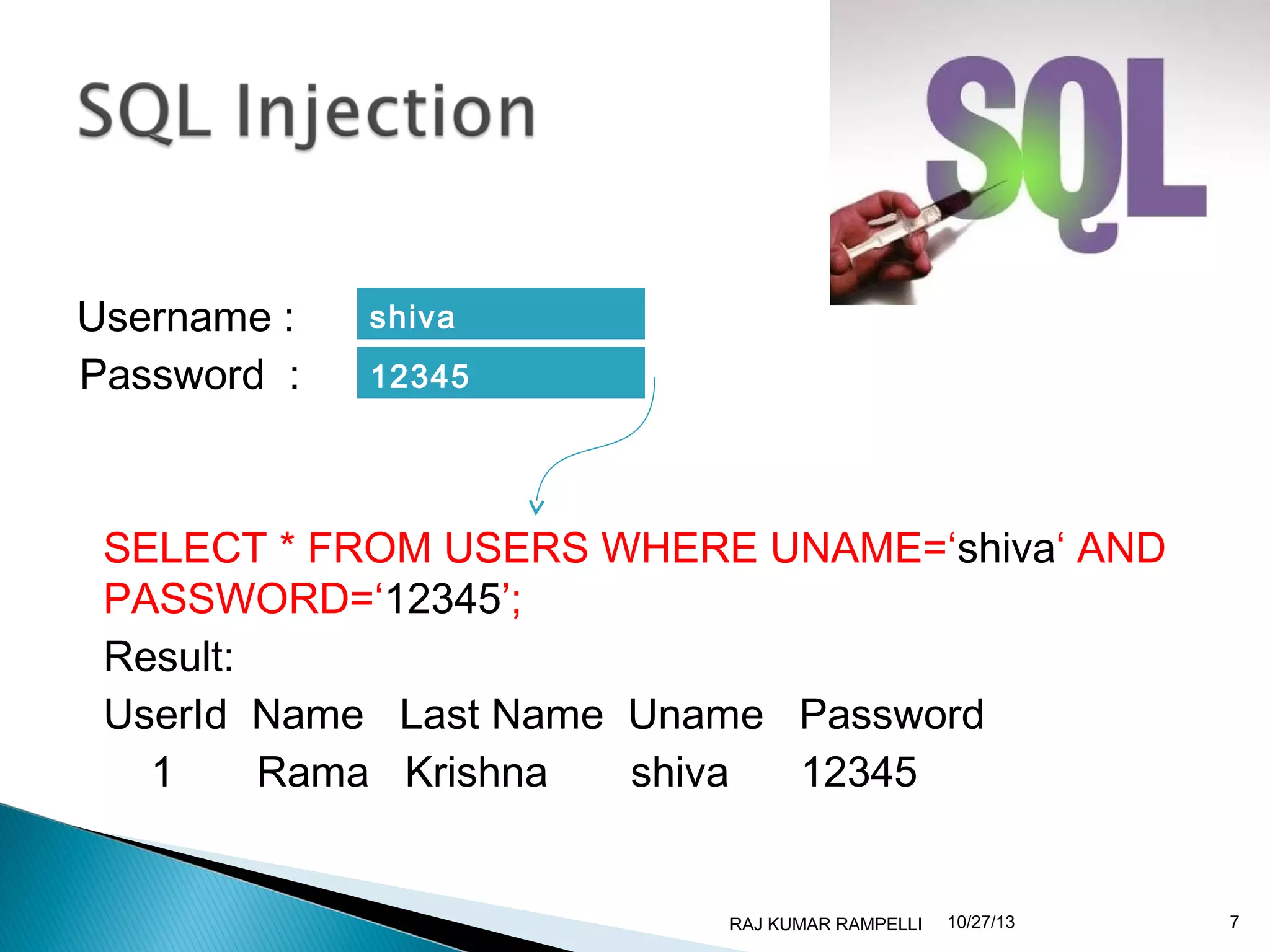
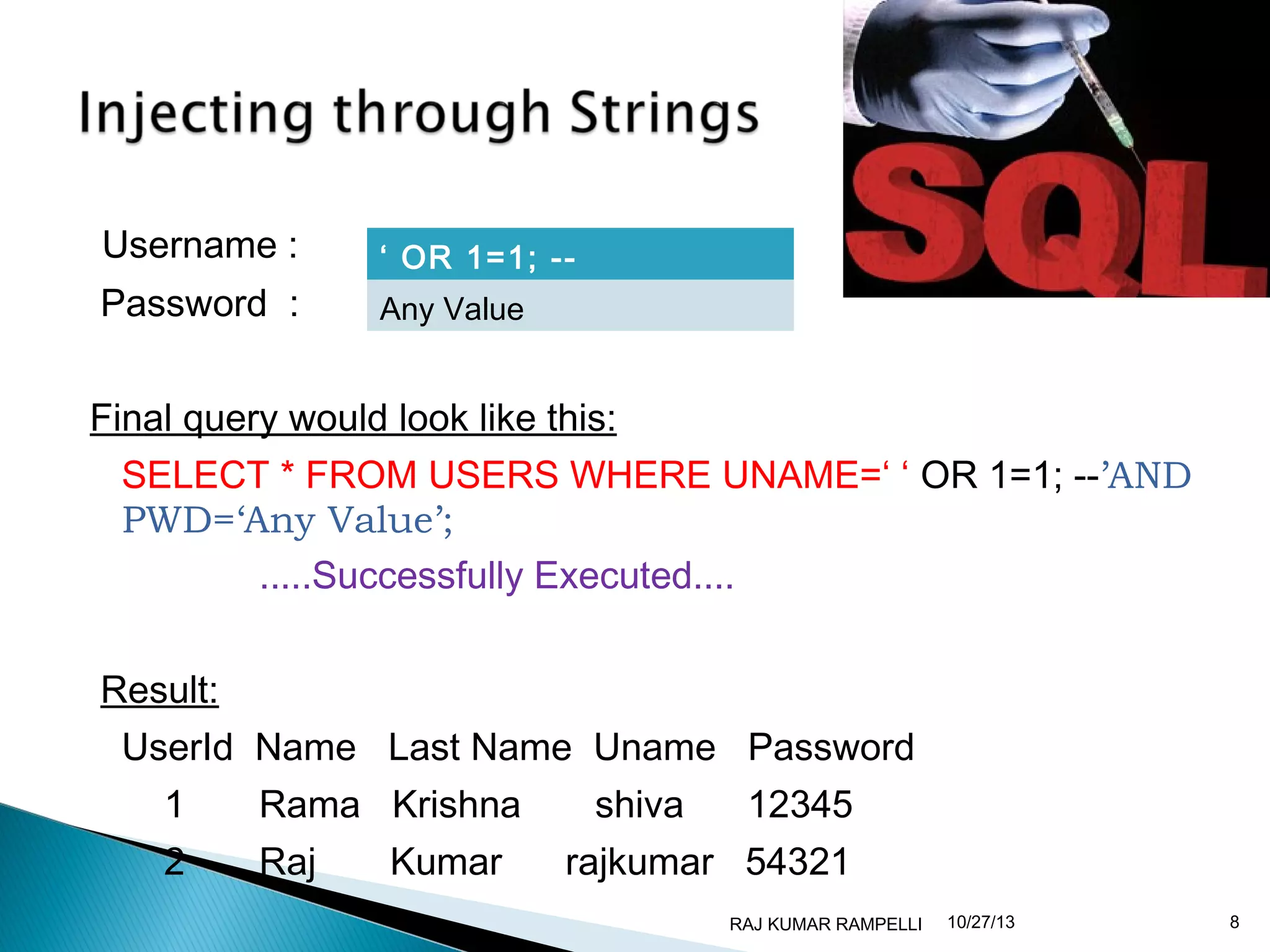
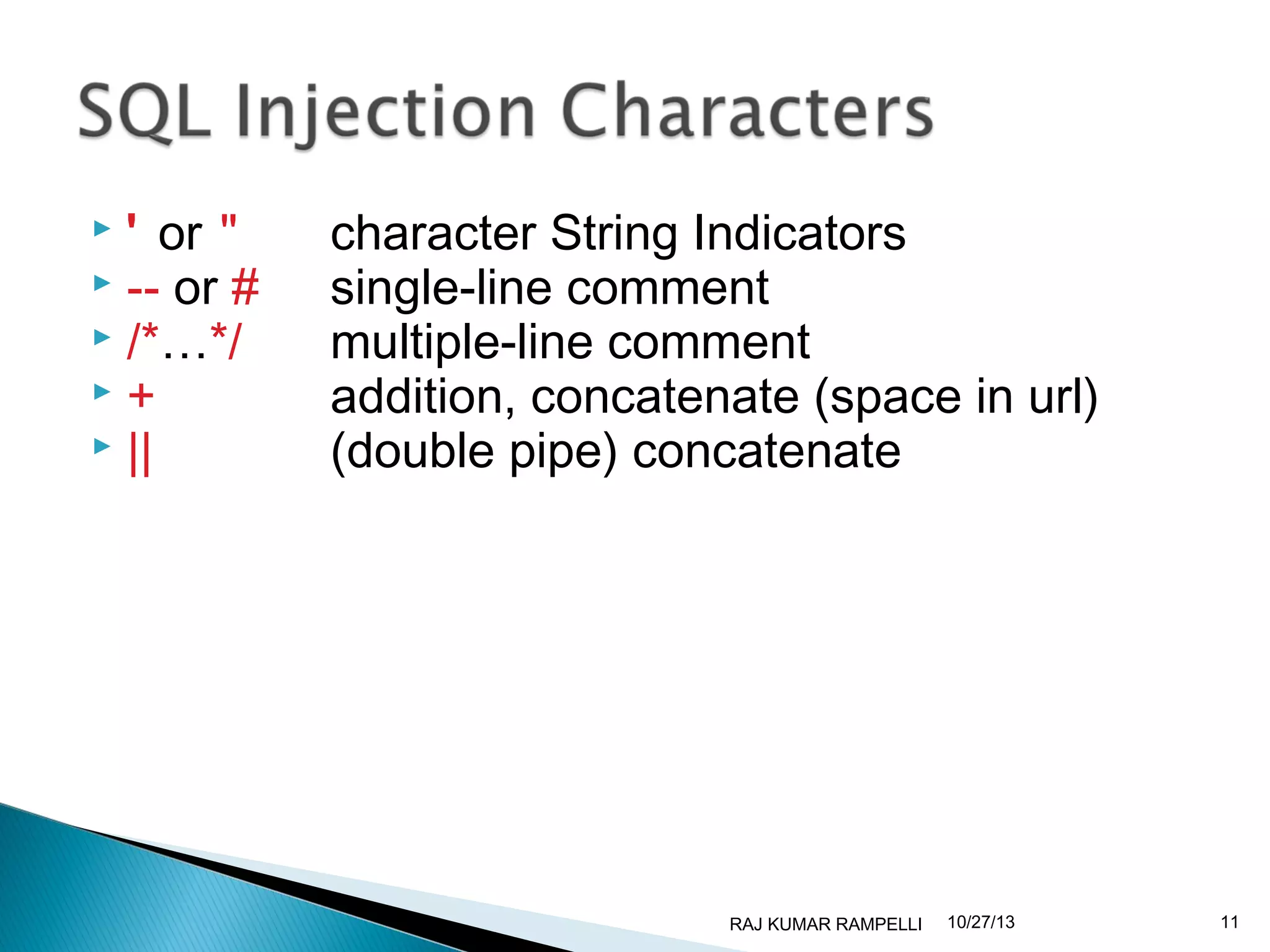
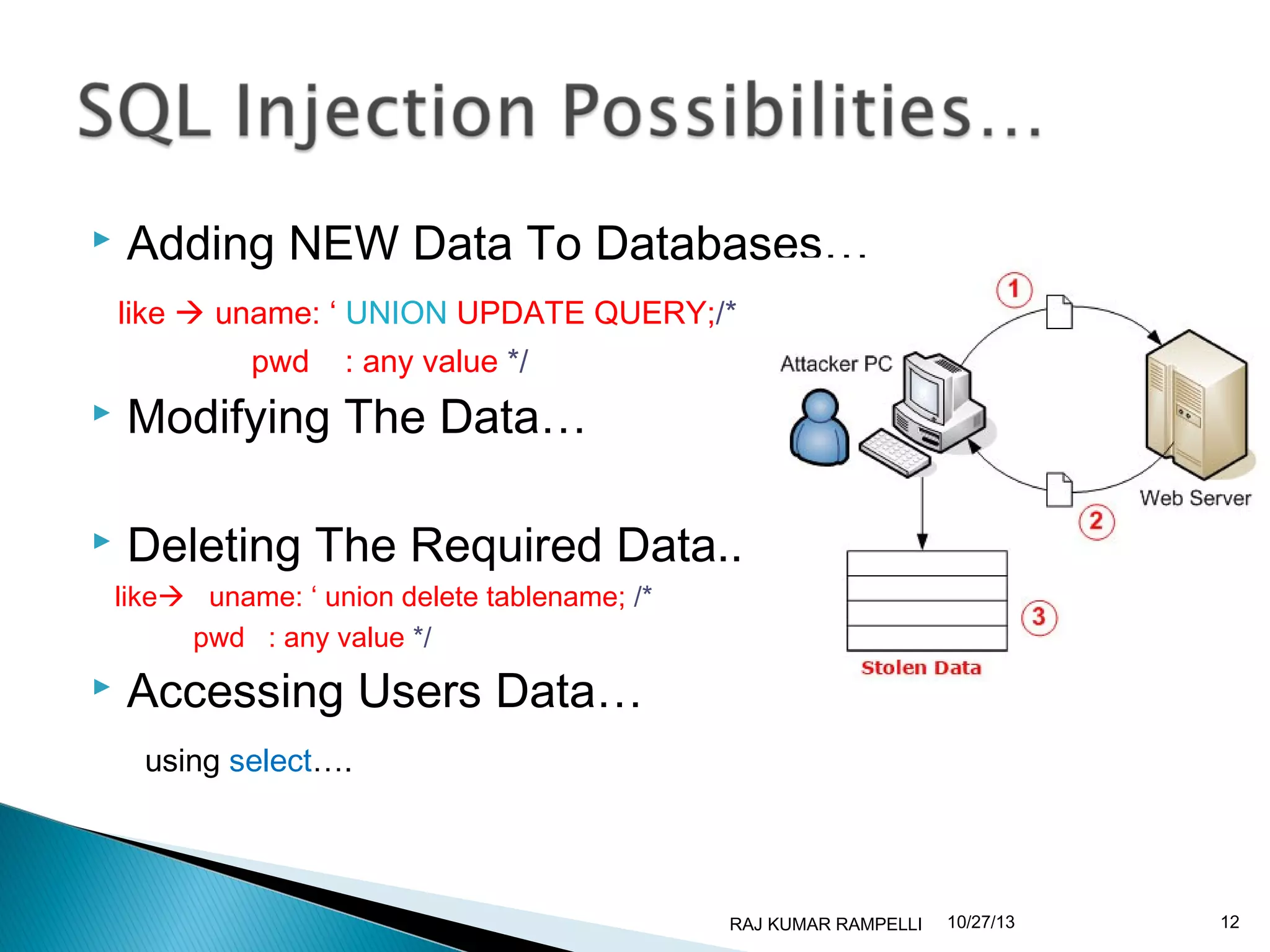
SQL is a language used to access and manipulate databases. It allows users to execute queries, retrieve, insert, update and delete data from databases. SQL injection occurs when malicious code is injected into an SQL query, which can compromise the security of a database. To prevent SQL injection, developers should validate all user input, escape special characters, limit database permissions, and configure databases to not display error information to users.