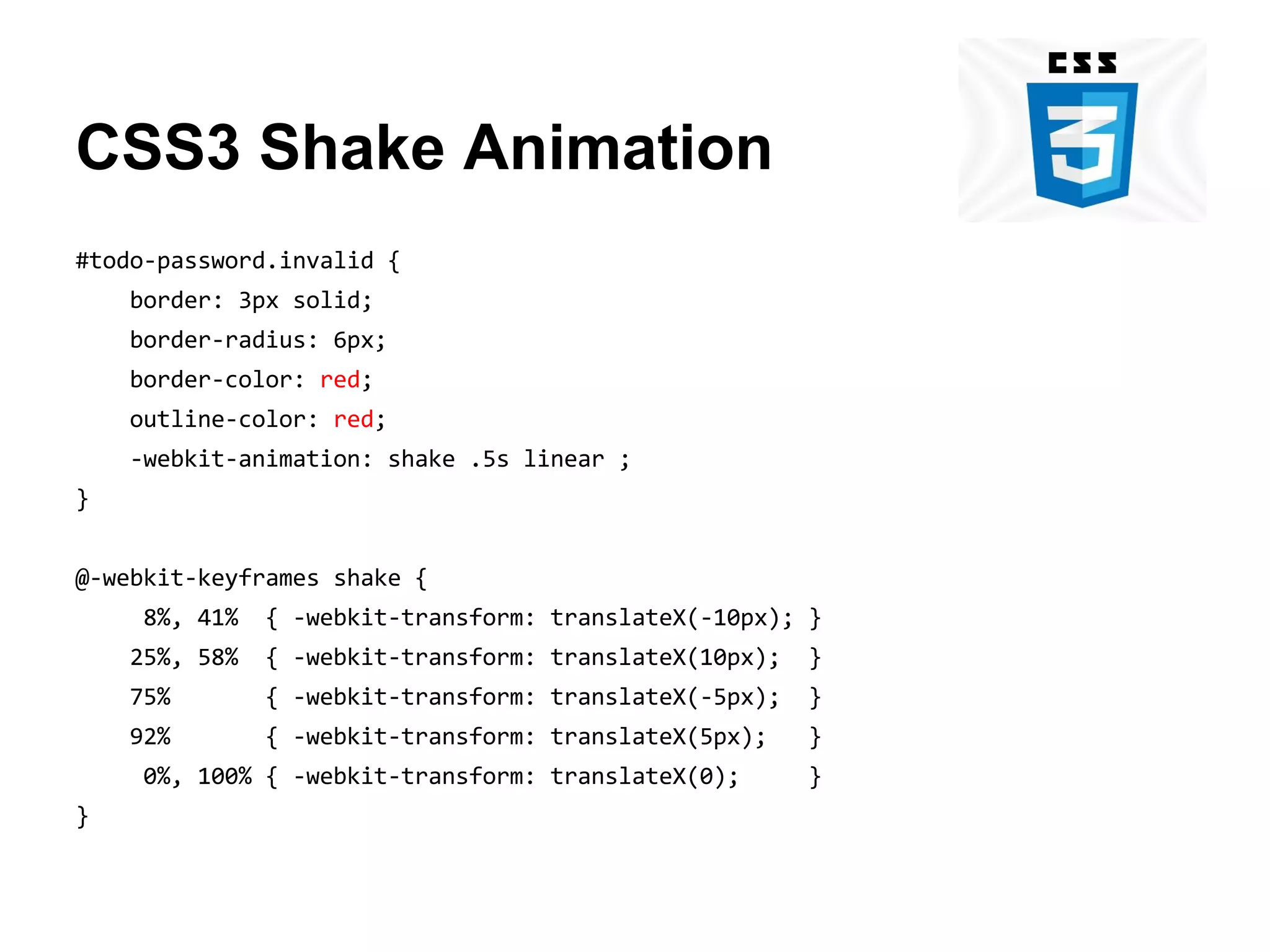
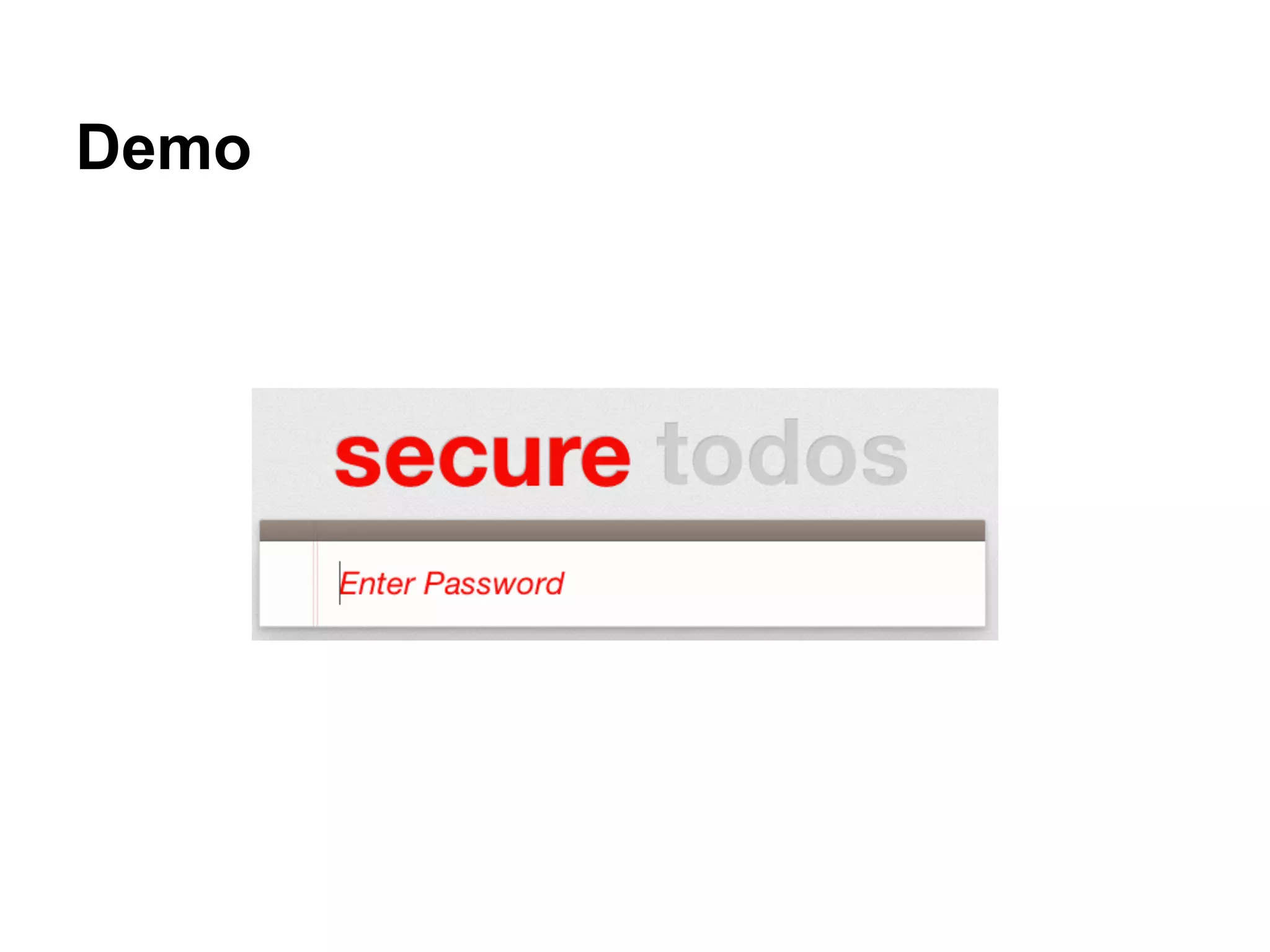
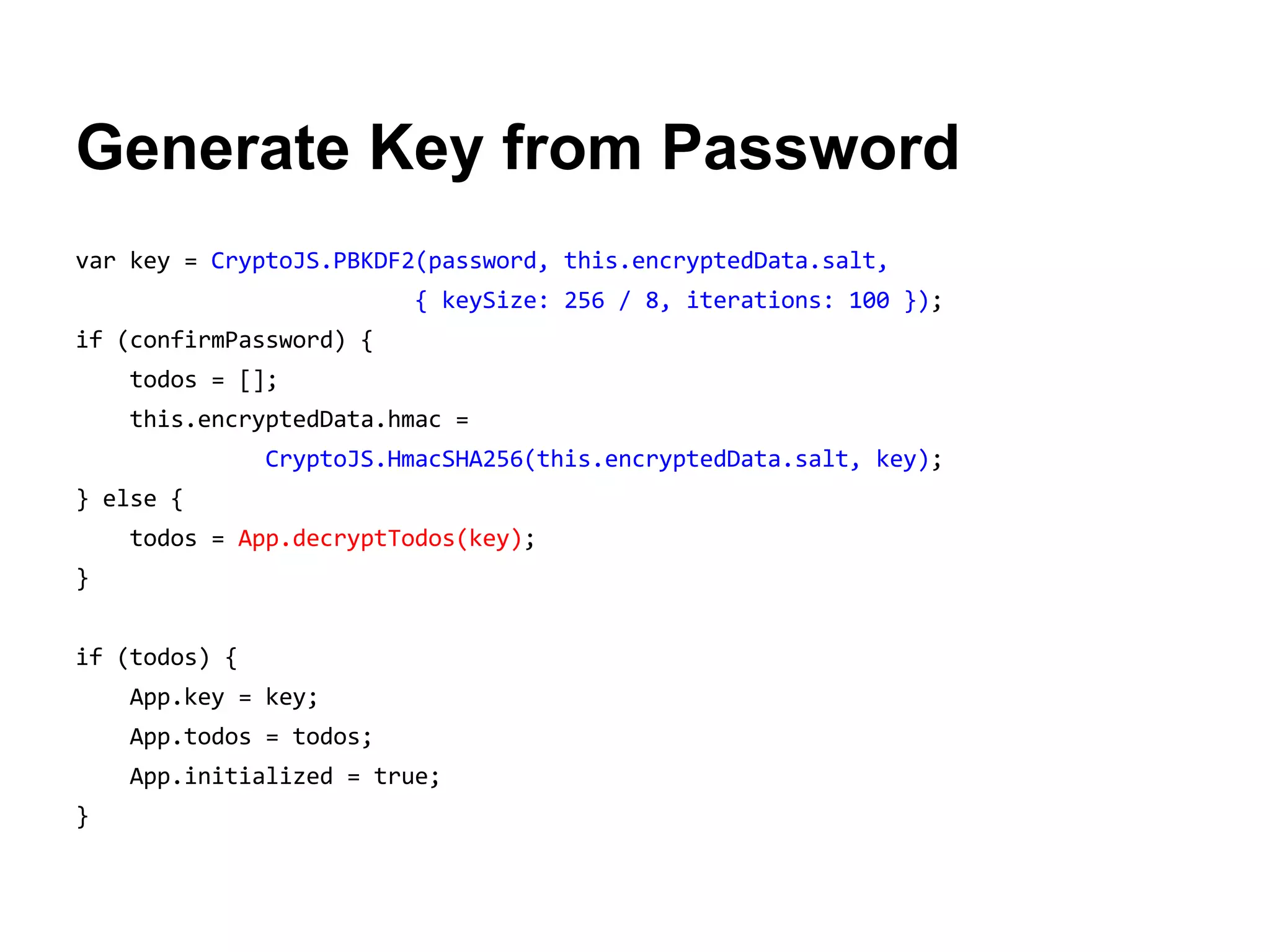
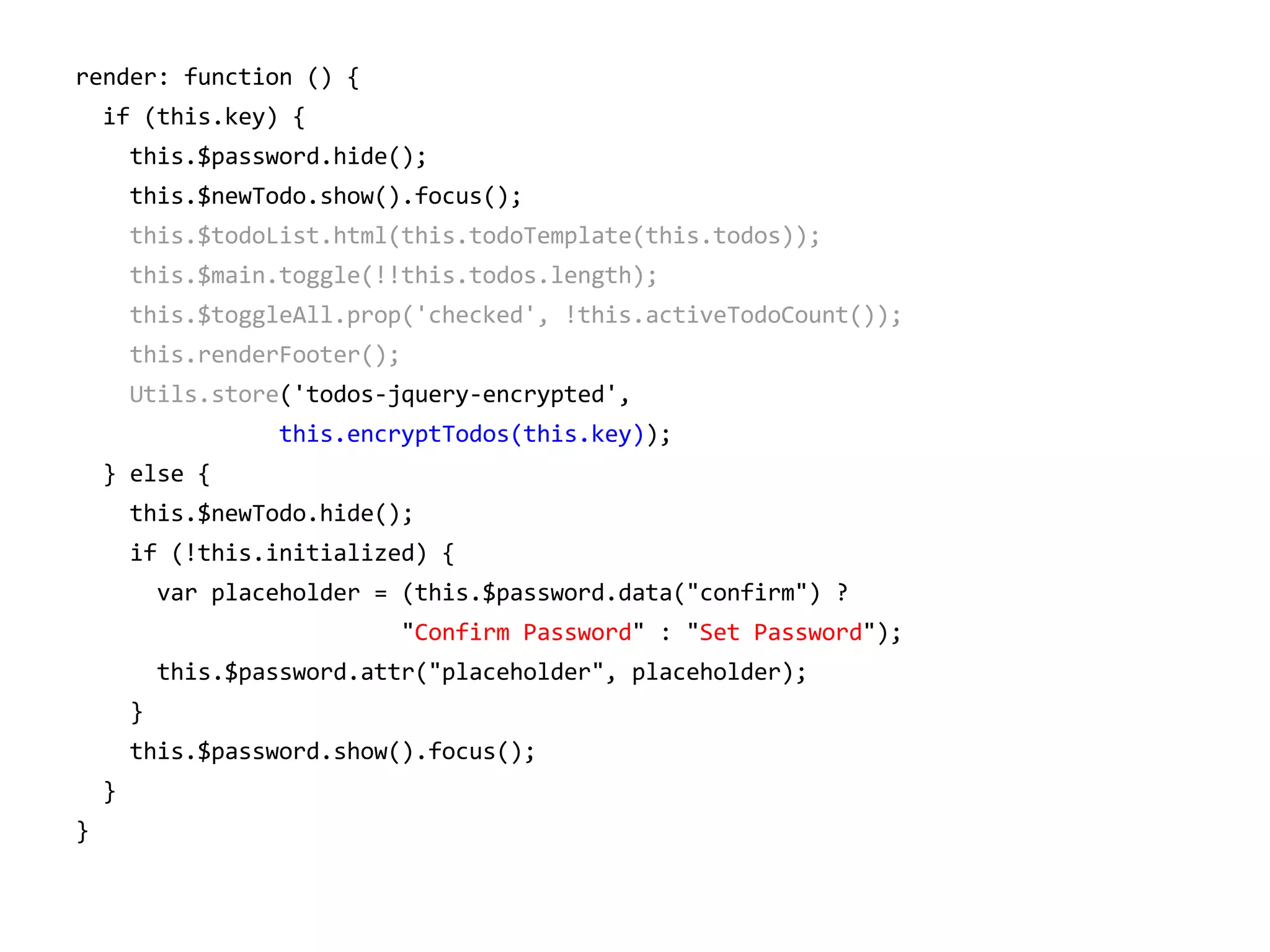
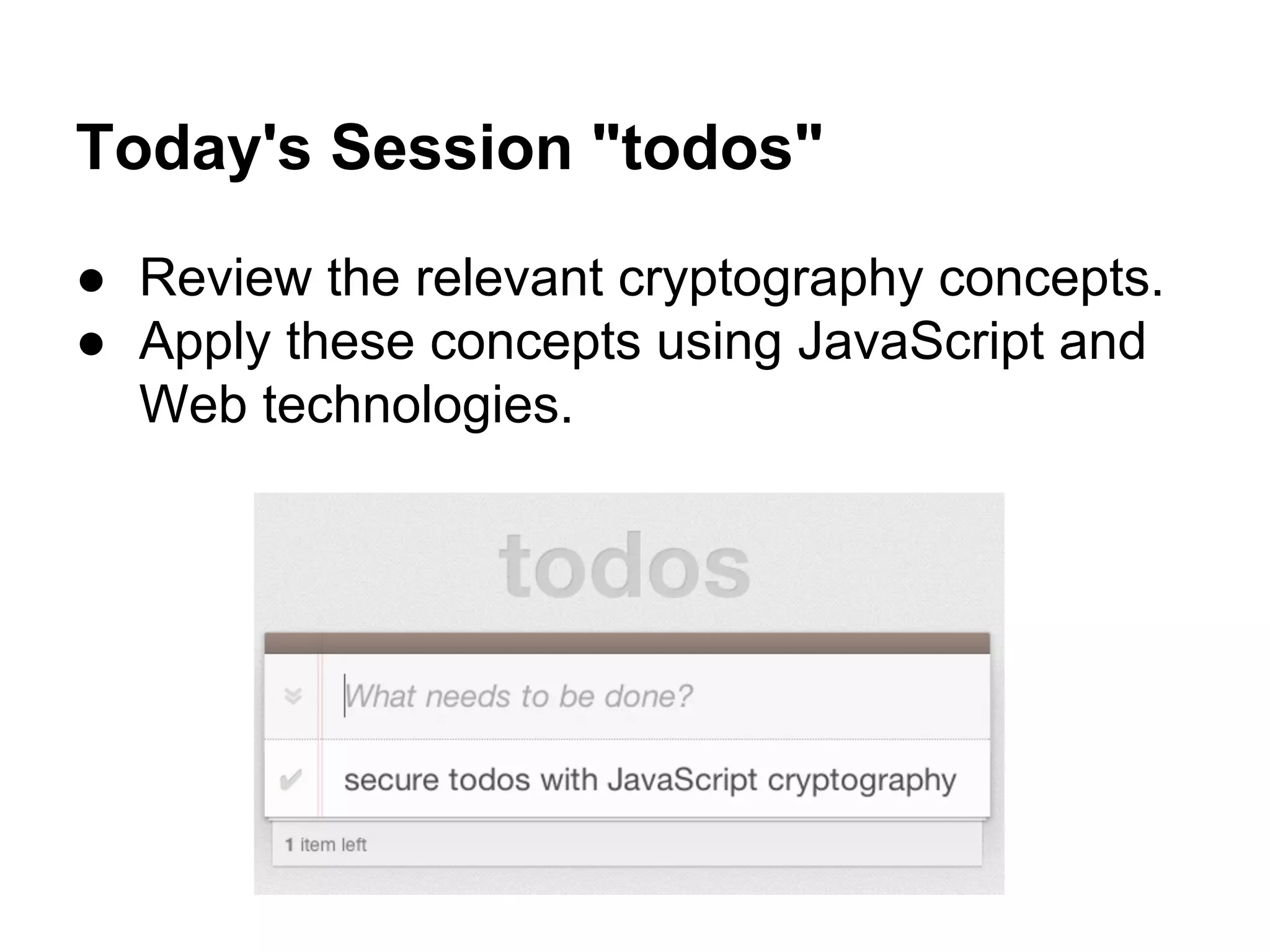
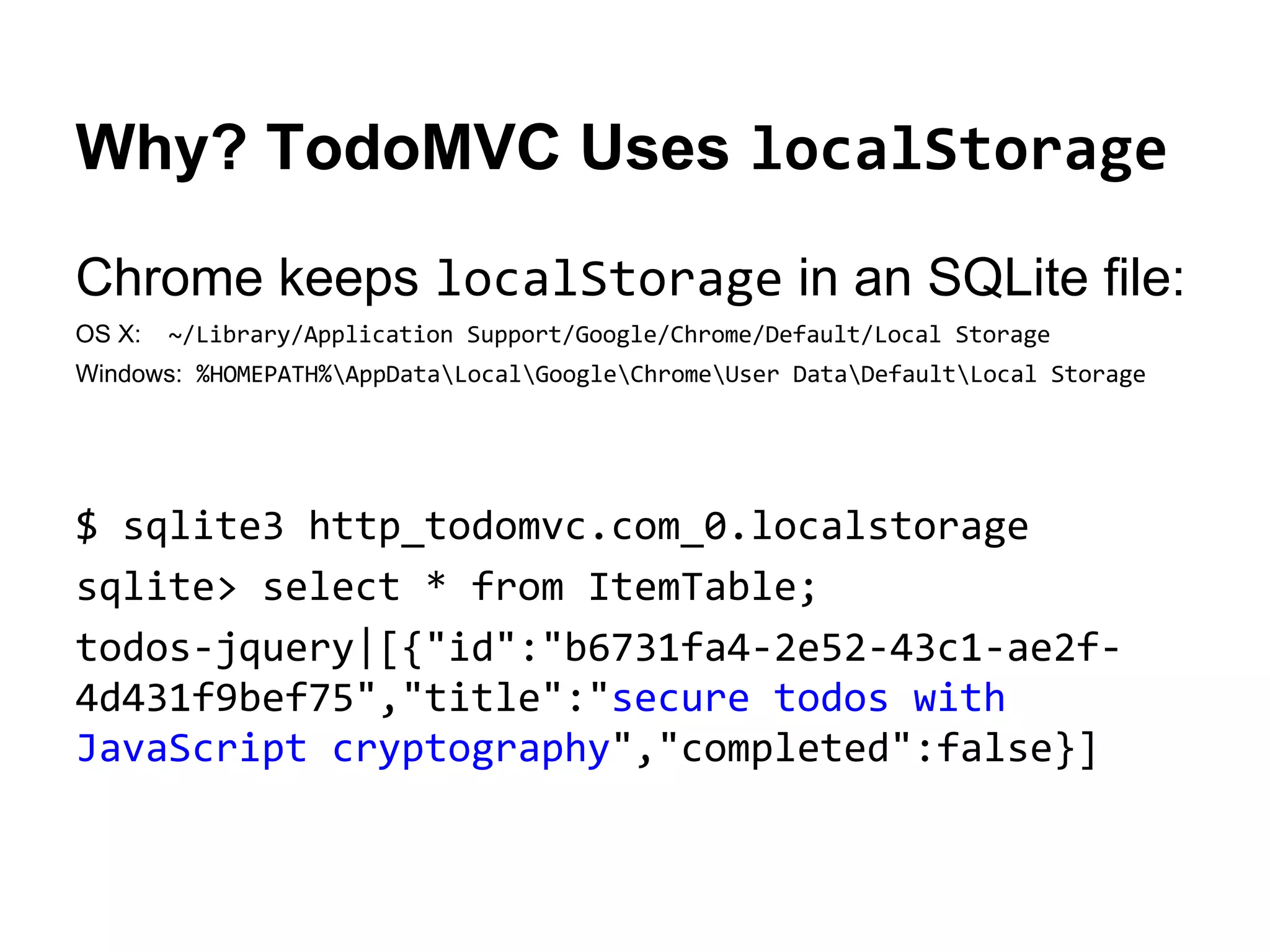
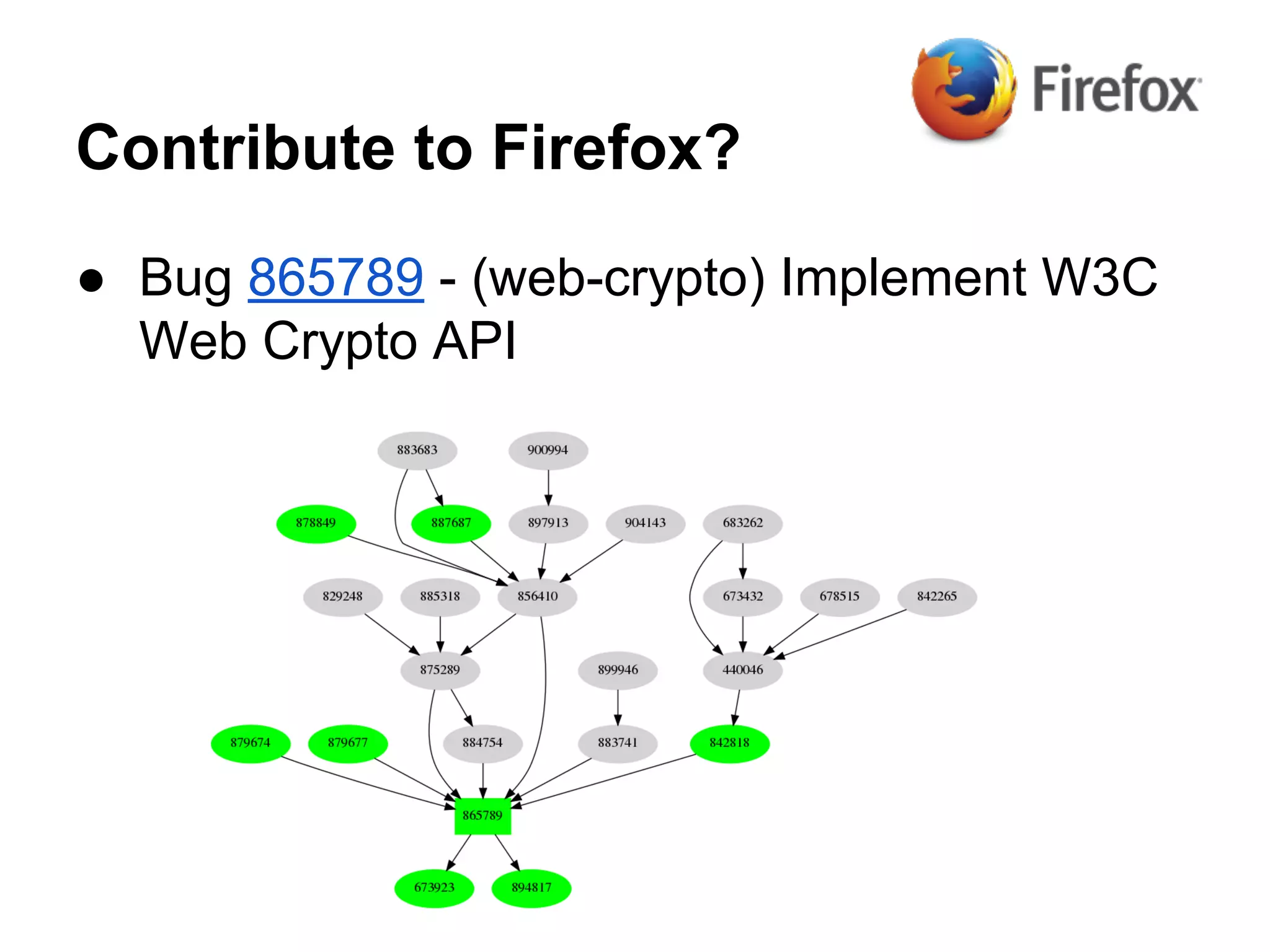
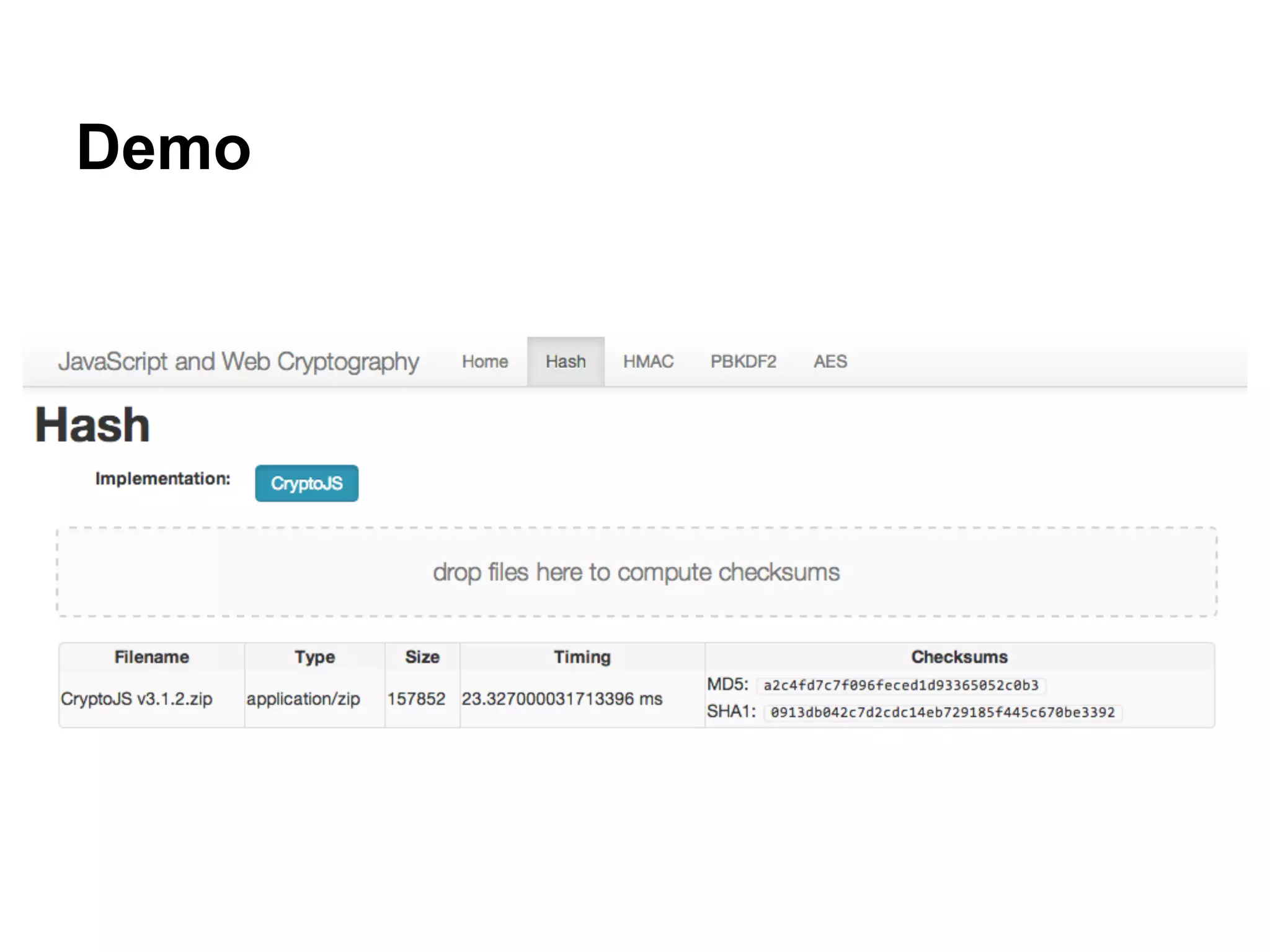
This document provides an overview of a session on JavaScript and web cryptography. It will explore the current state of JavaScript and web cryptography, reviewing basic concepts and definitions. It will discuss the role of TLS/SSL and provide working examples applying cryptography to real-world use cases. It will also preview the upcoming W3C WebCryptoAPI. Code samples will demonstrate CryptoJS in the browser and Node.js Crypto on the server. An extended example will secure the popular TodoMVC project using PBKDF2 for key generation, HMAC for integrity and AES for encryption.



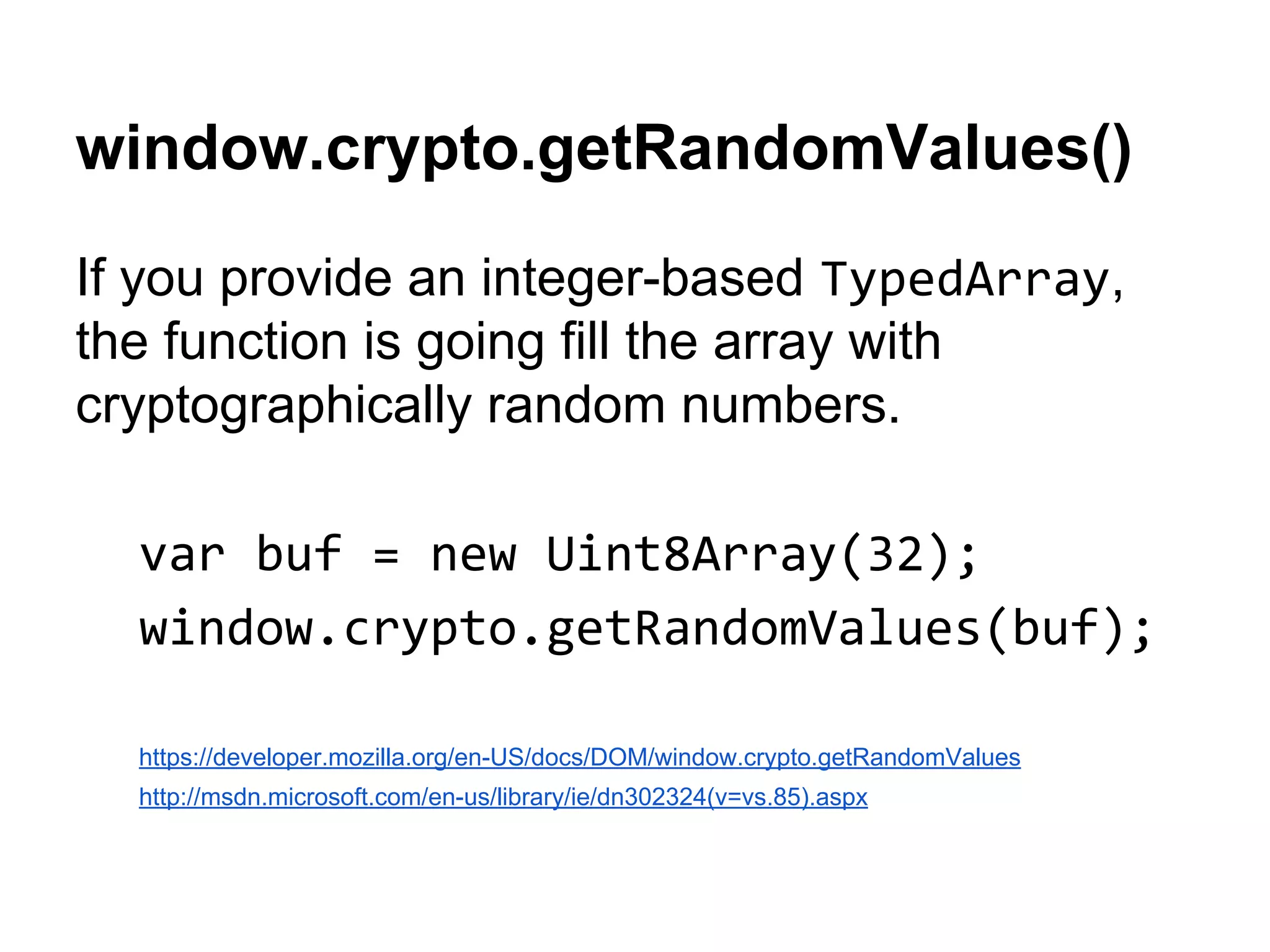
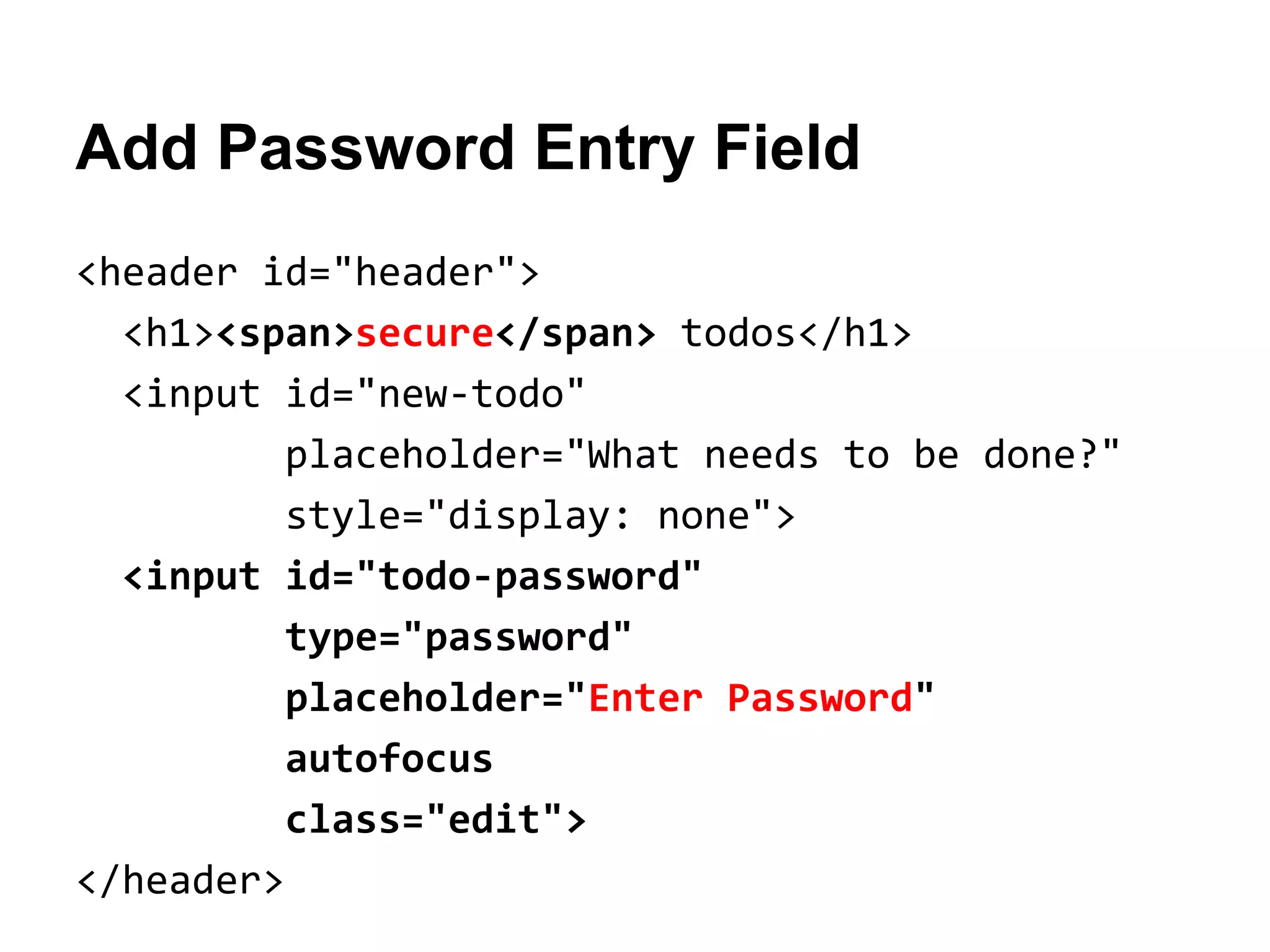
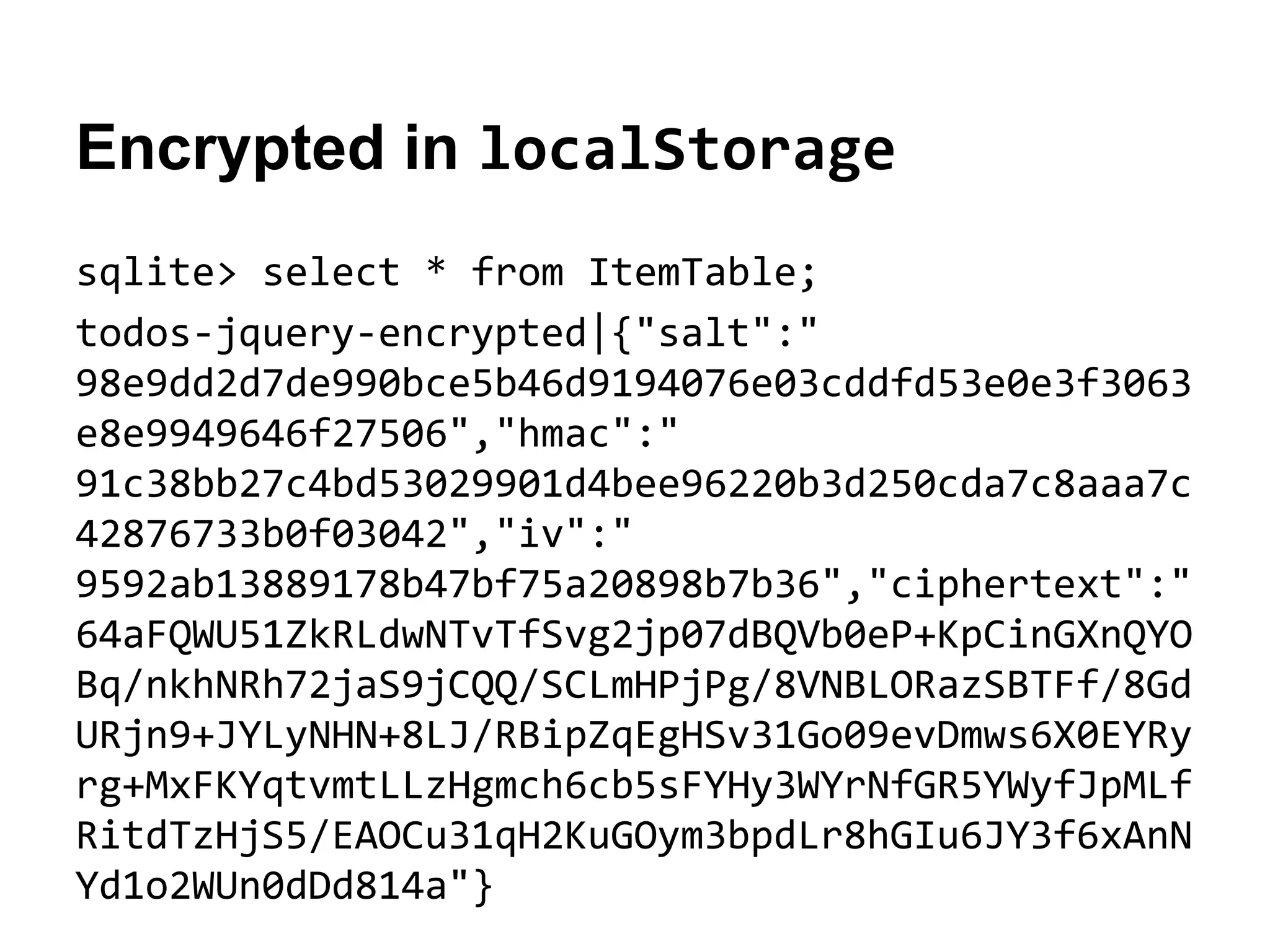
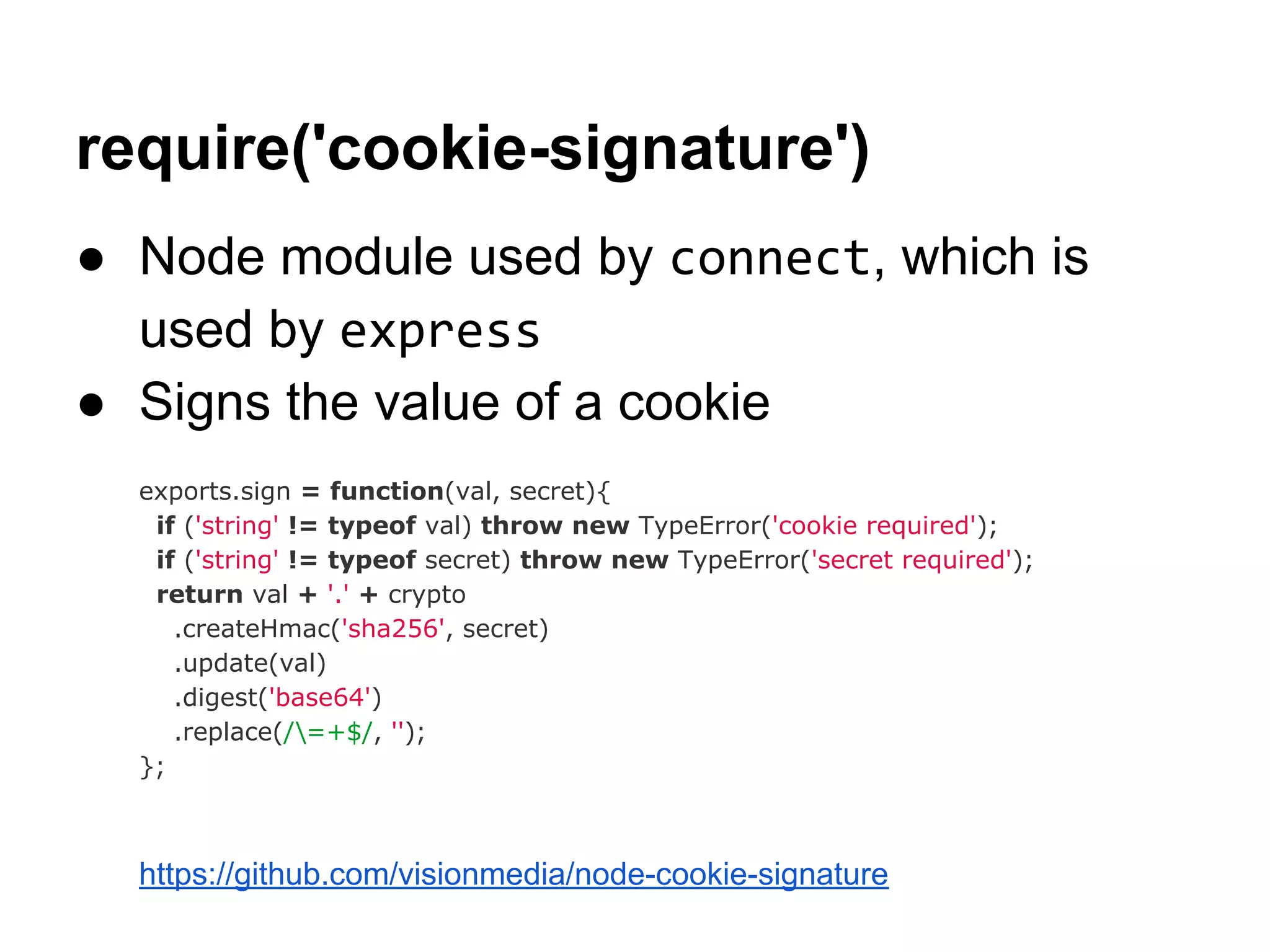
![Javascript Cryptography Considered
Harmful (circa 2010)
● Opinion on browser Javascript cryptography
○ "no reliable way for any piece of Javascript code to
verify its execution environment"
○ "can't outsource random number generation in a
cryptosystem"
○ "practically no value to doing crypto in Javascript
once you add SSL to the mix"
○ "store the key on that server [and] documents there"
http://www.matasano.com/articles/javascript-cryptography/
● Didn't consider the "offline" user experience](https://image.slidesharecdn.com/knynawtltoax36qqjt0n-140701141830-phpapp02/75/Java-script-and-web-cryptography-cf-objective-36-2048.jpg)
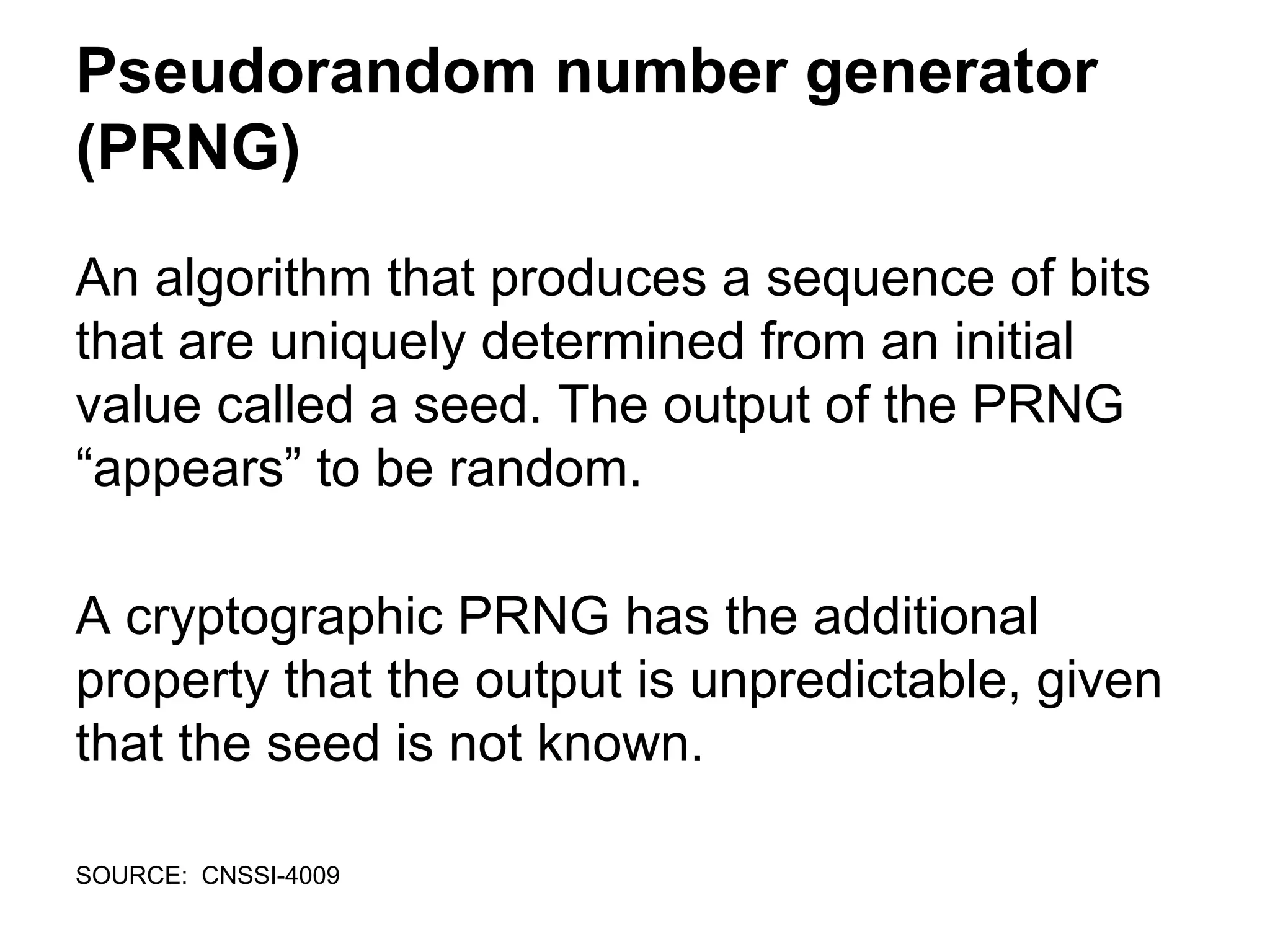
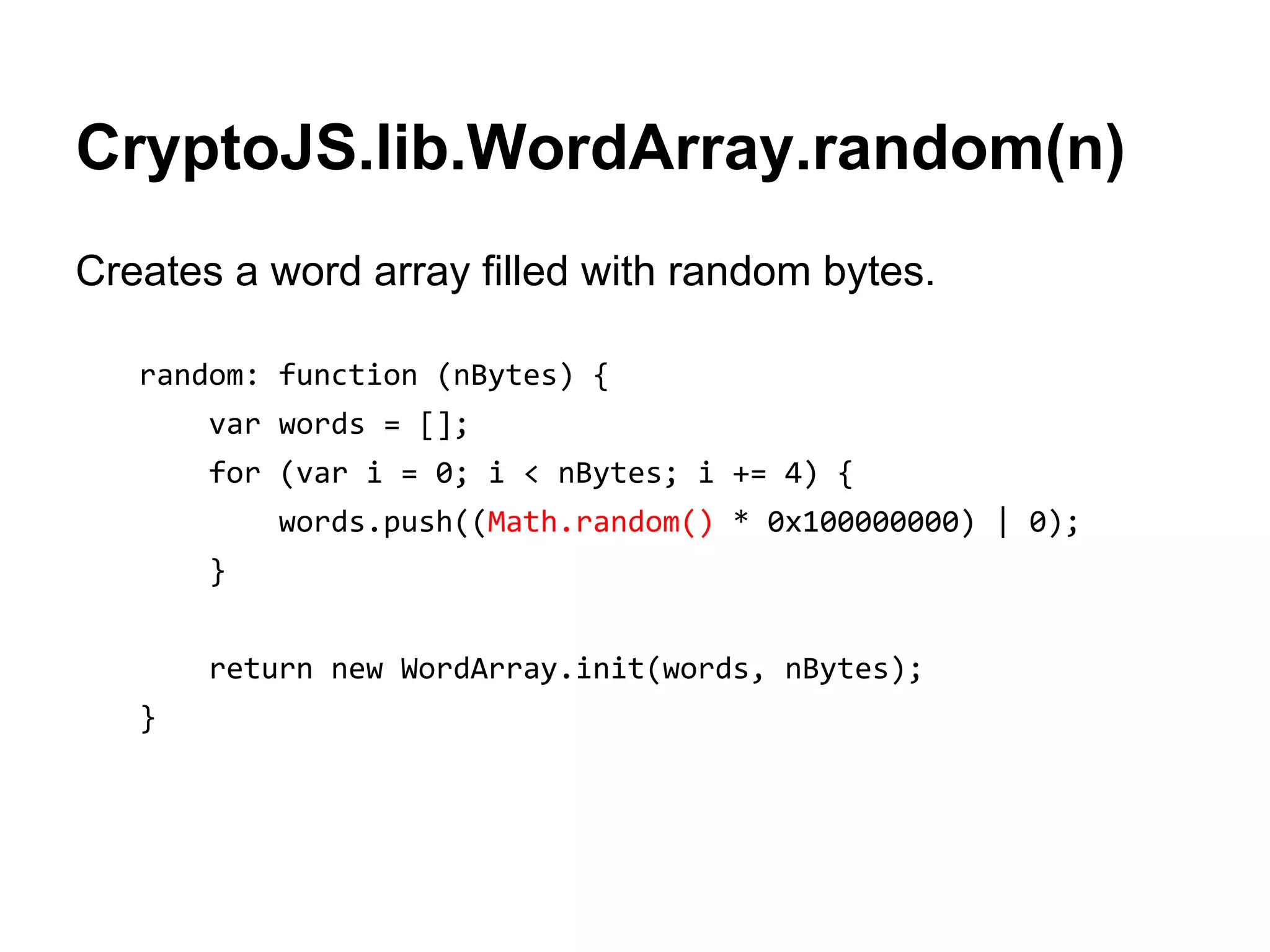
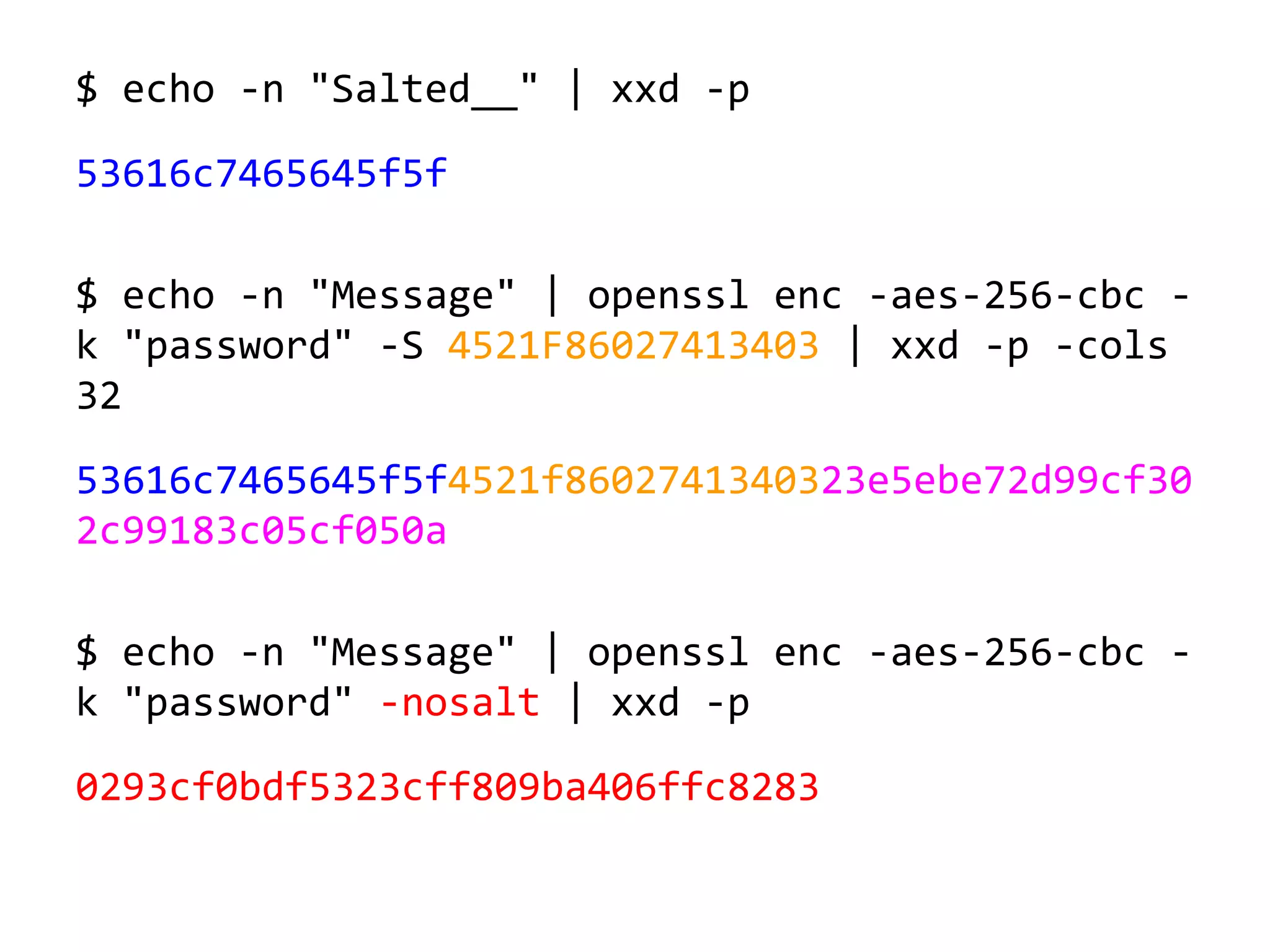
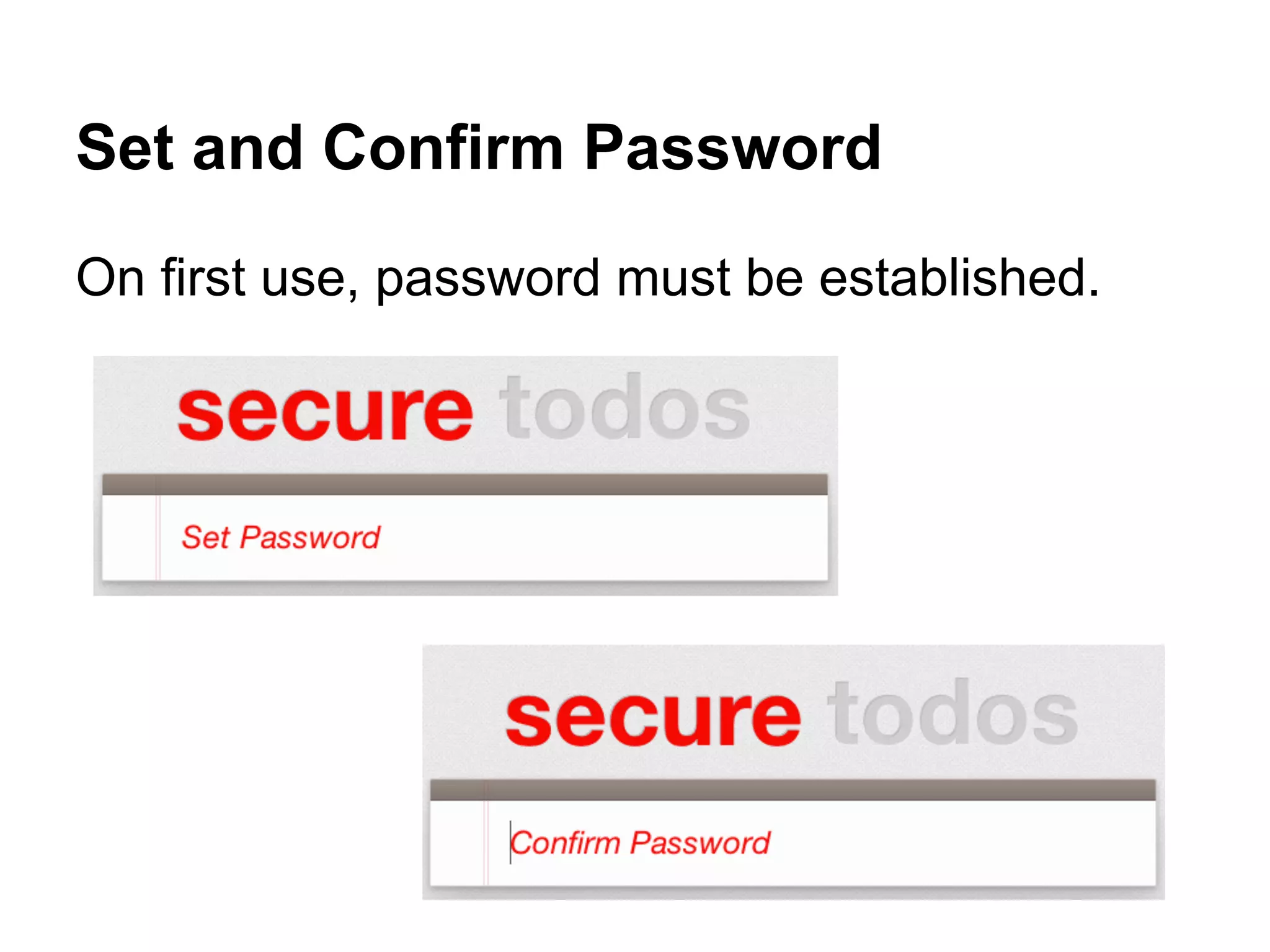
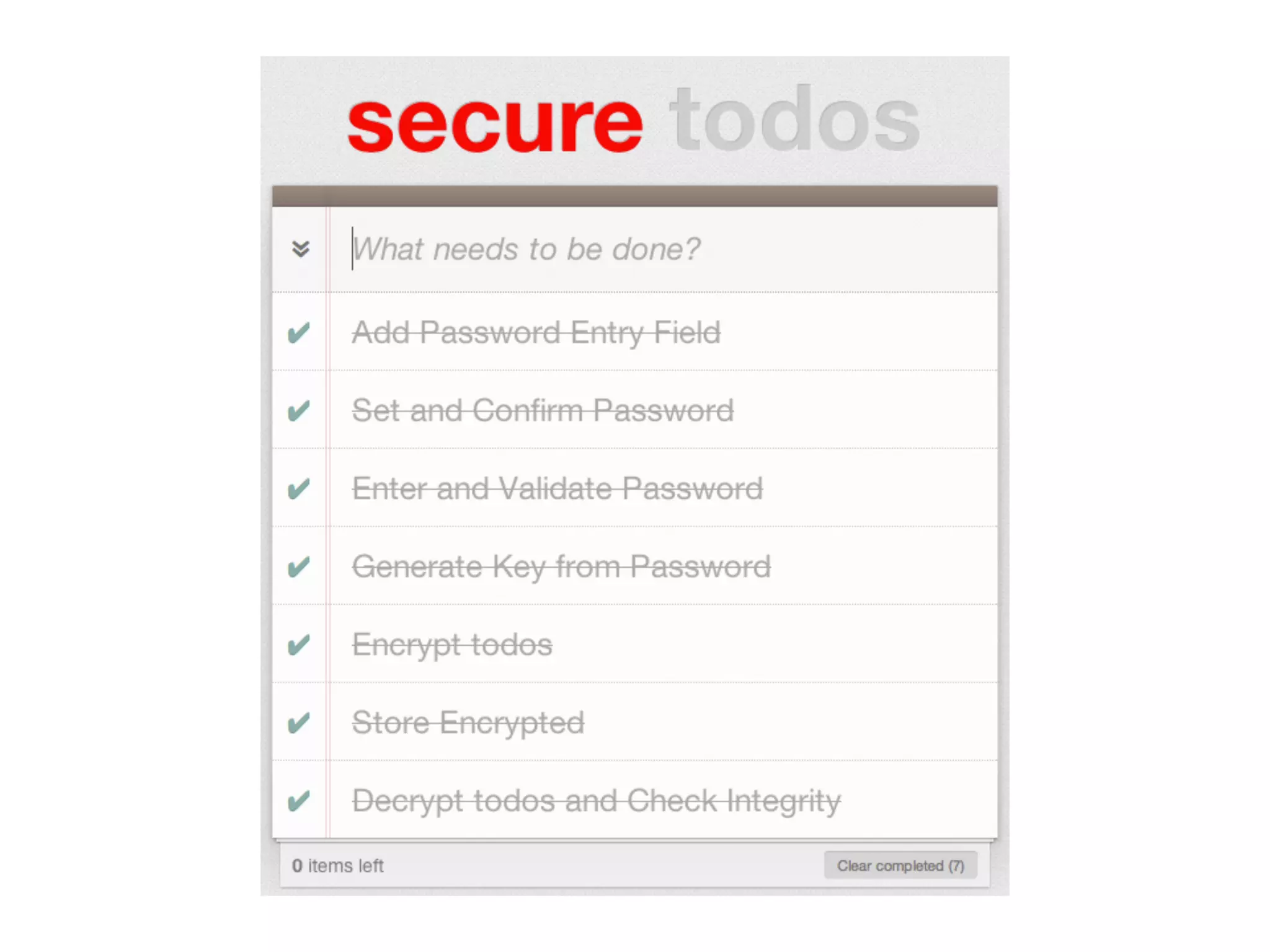
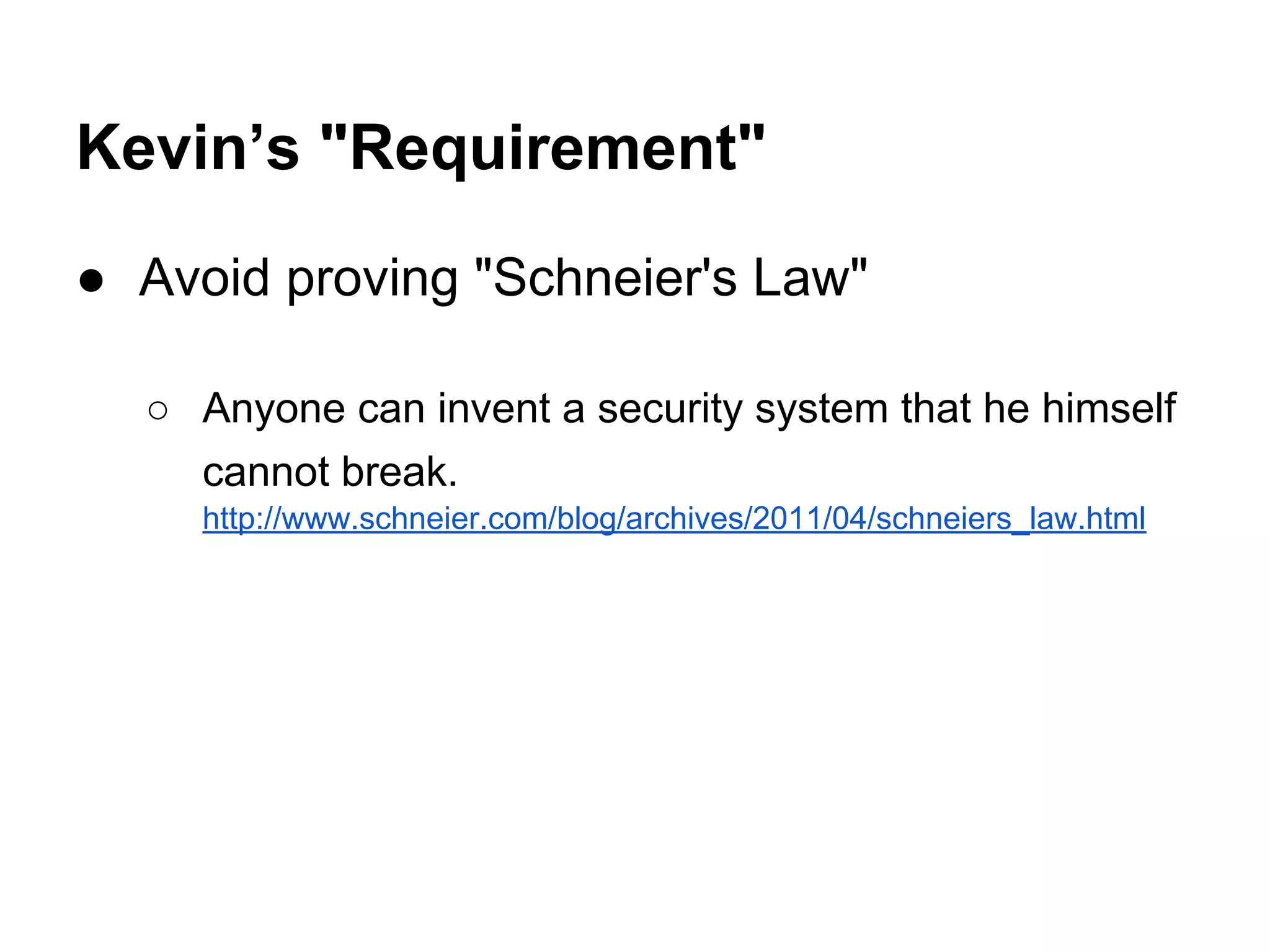
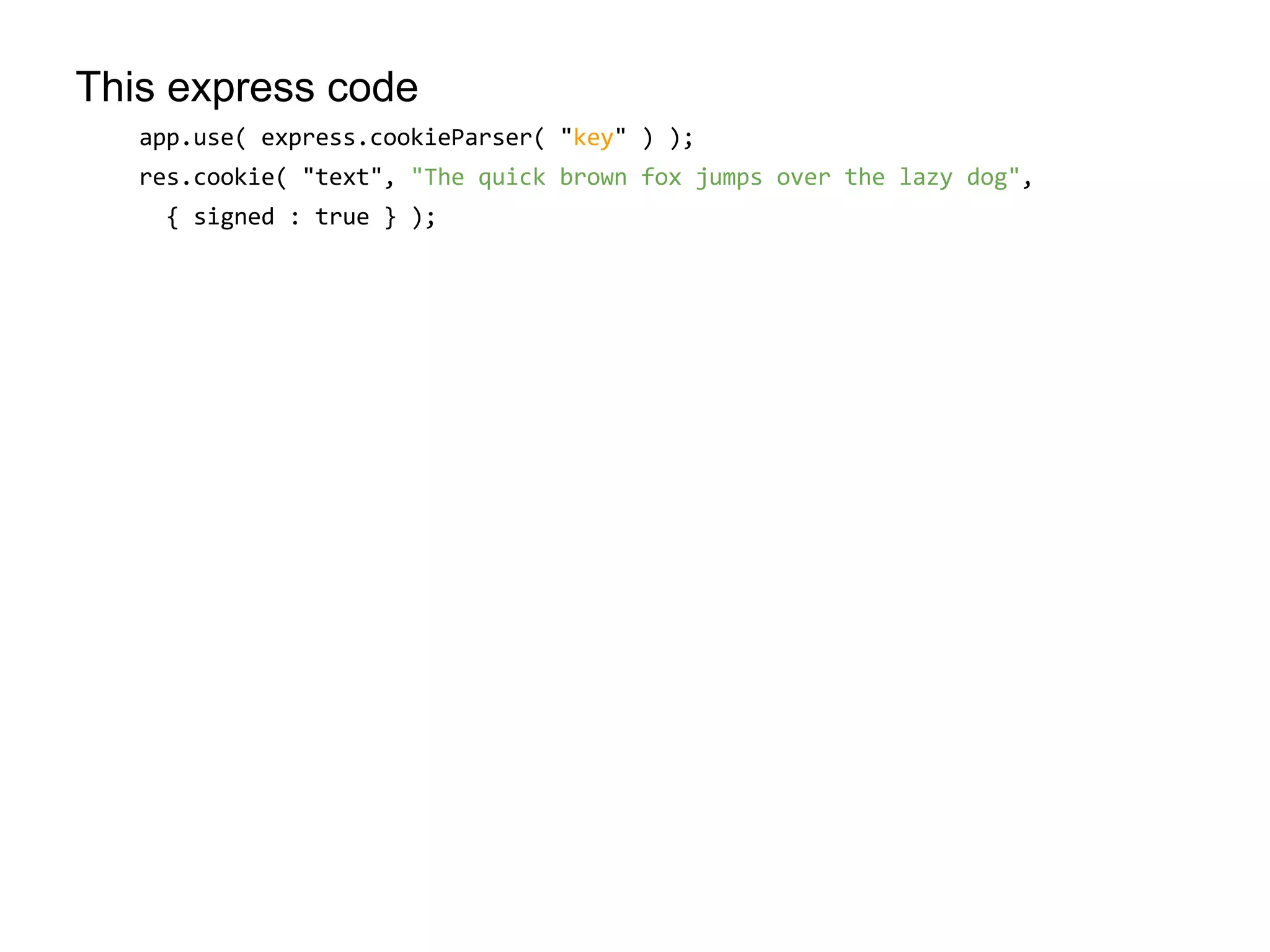
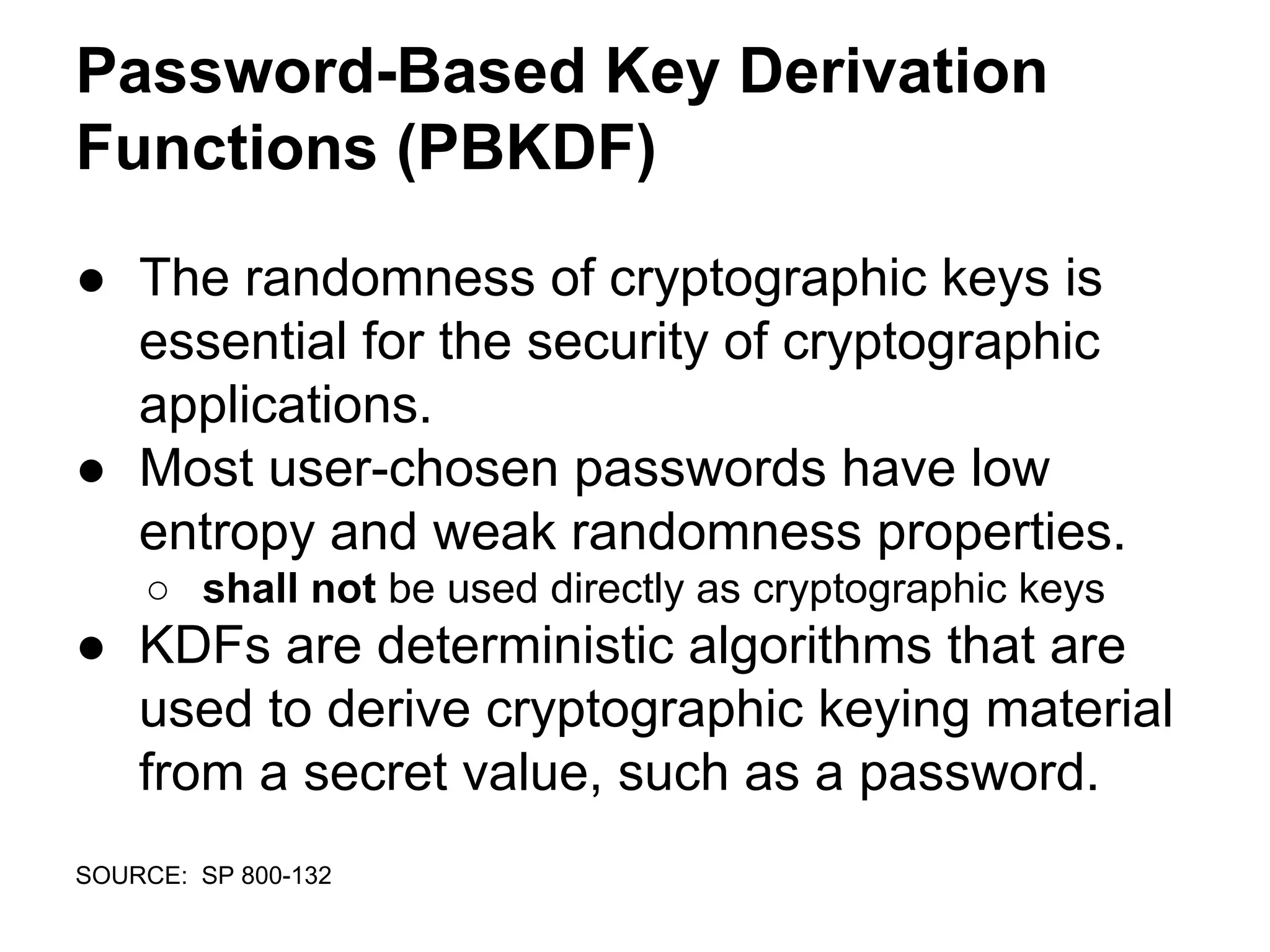
![Web-browser encryption of personal health information [http://www.biomedcentral.com/1472-6947/11/70]
Encryption data flow. A diagram laying out how the encrypted data and the user-supplied passcode are used to decrypt the data.
Morse et al. BMC Medical Informatics and Decision Making 2011 11:70 doi:10.1186/1472-6947-11-70](https://image.slidesharecdn.com/knynawtltoax36qqjt0n-140701141830-phpapp02/75/Java-script-and-web-cryptography-cf-objective-38-2048.jpg)
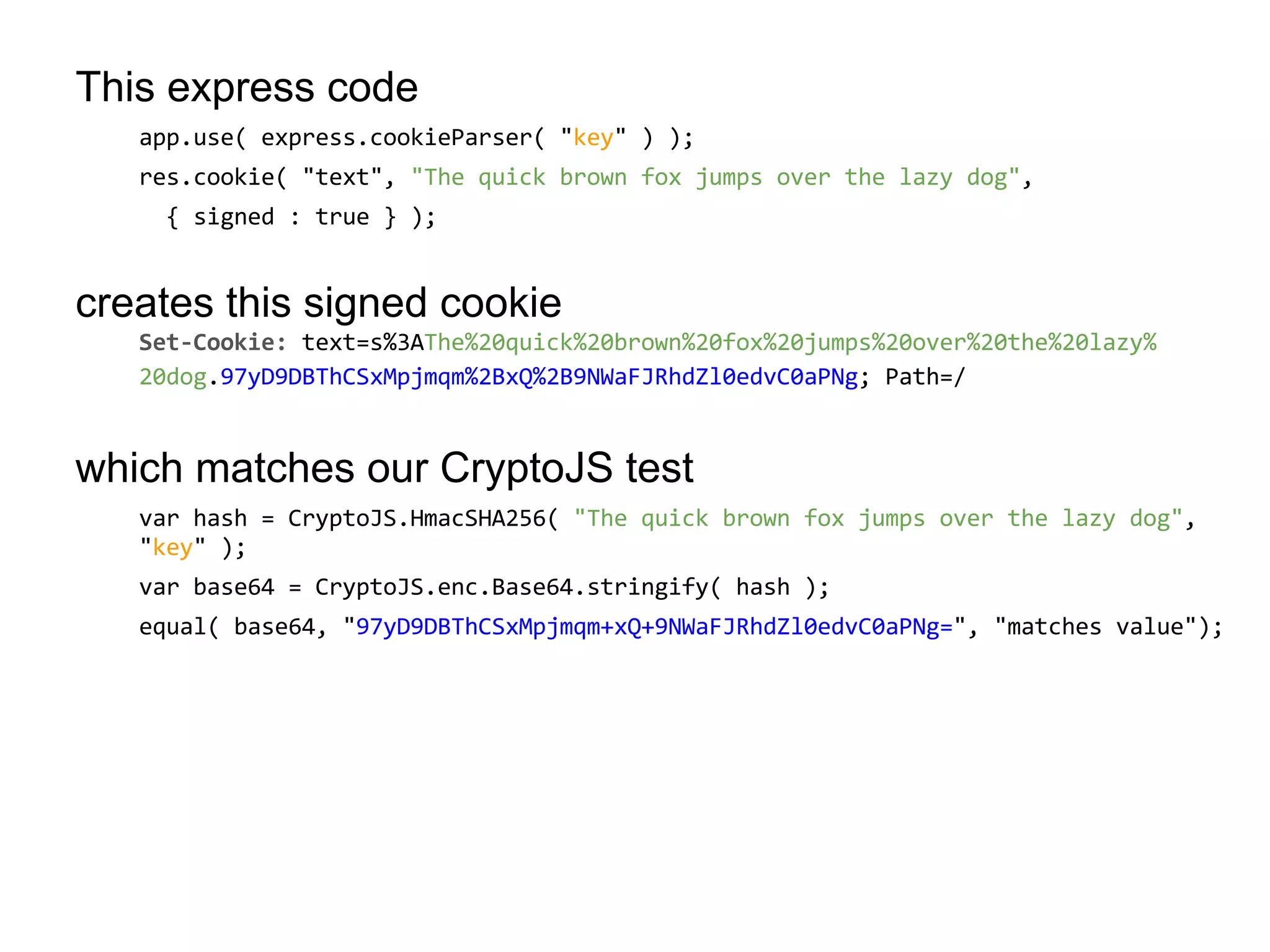
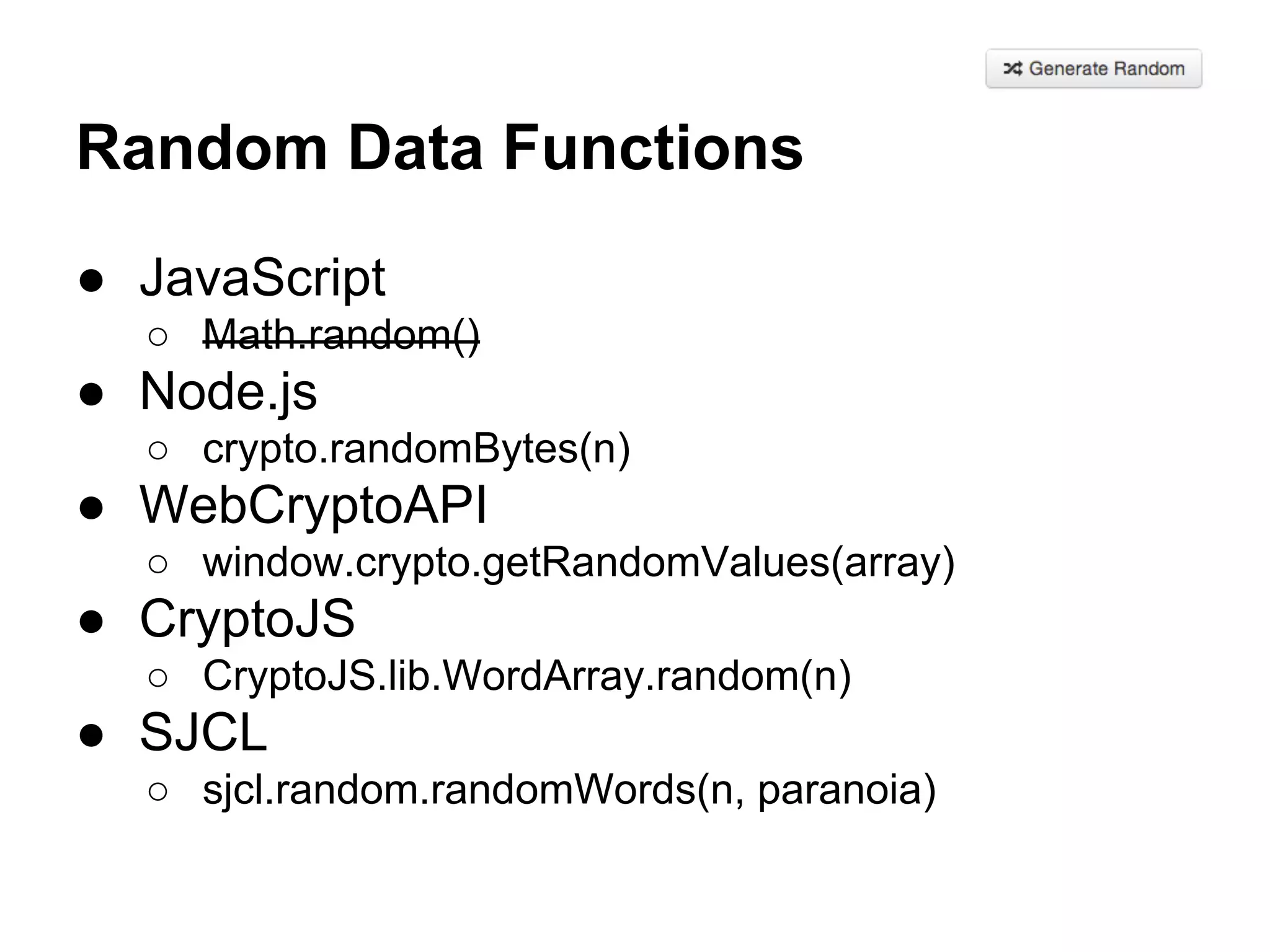
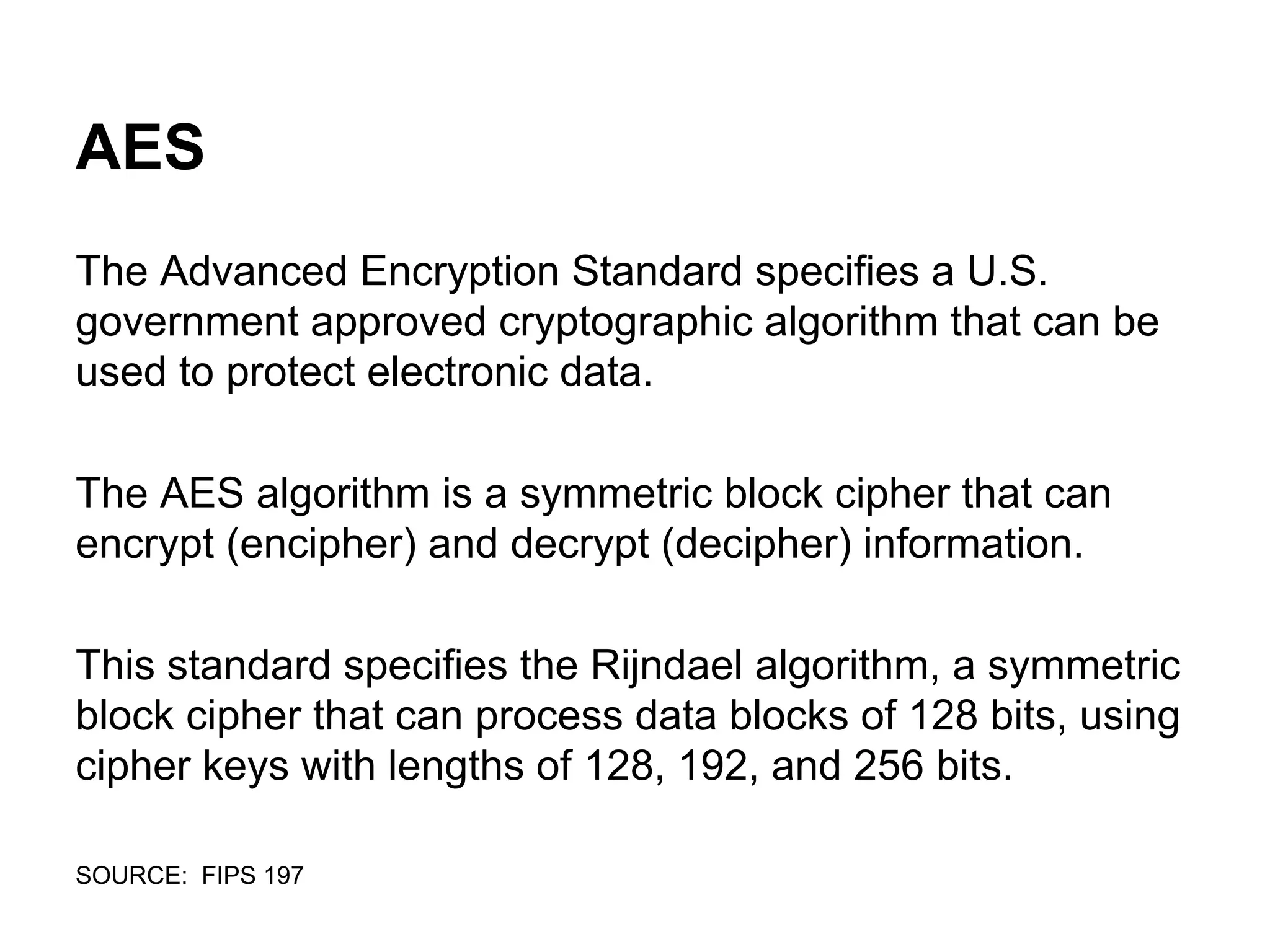
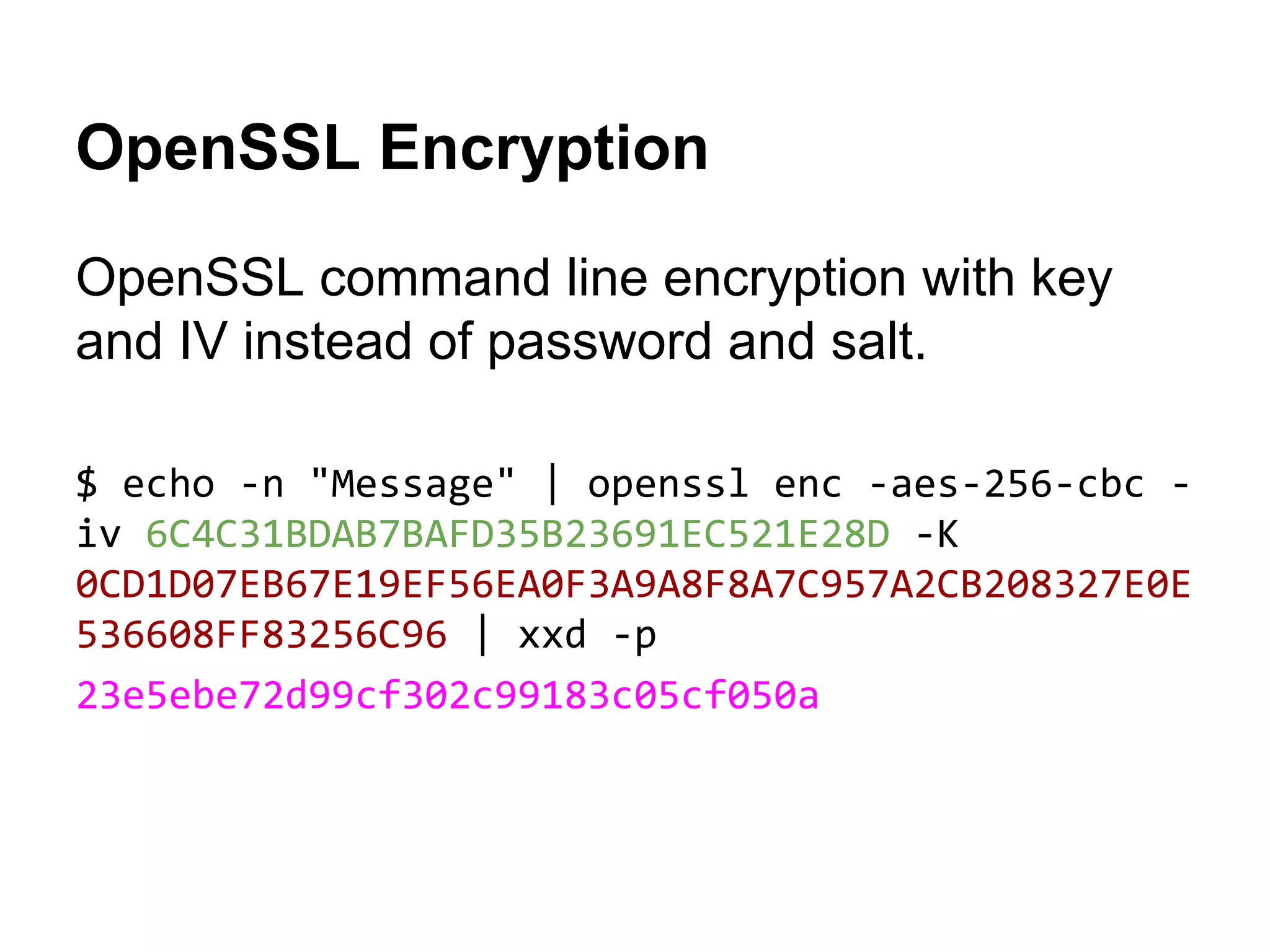
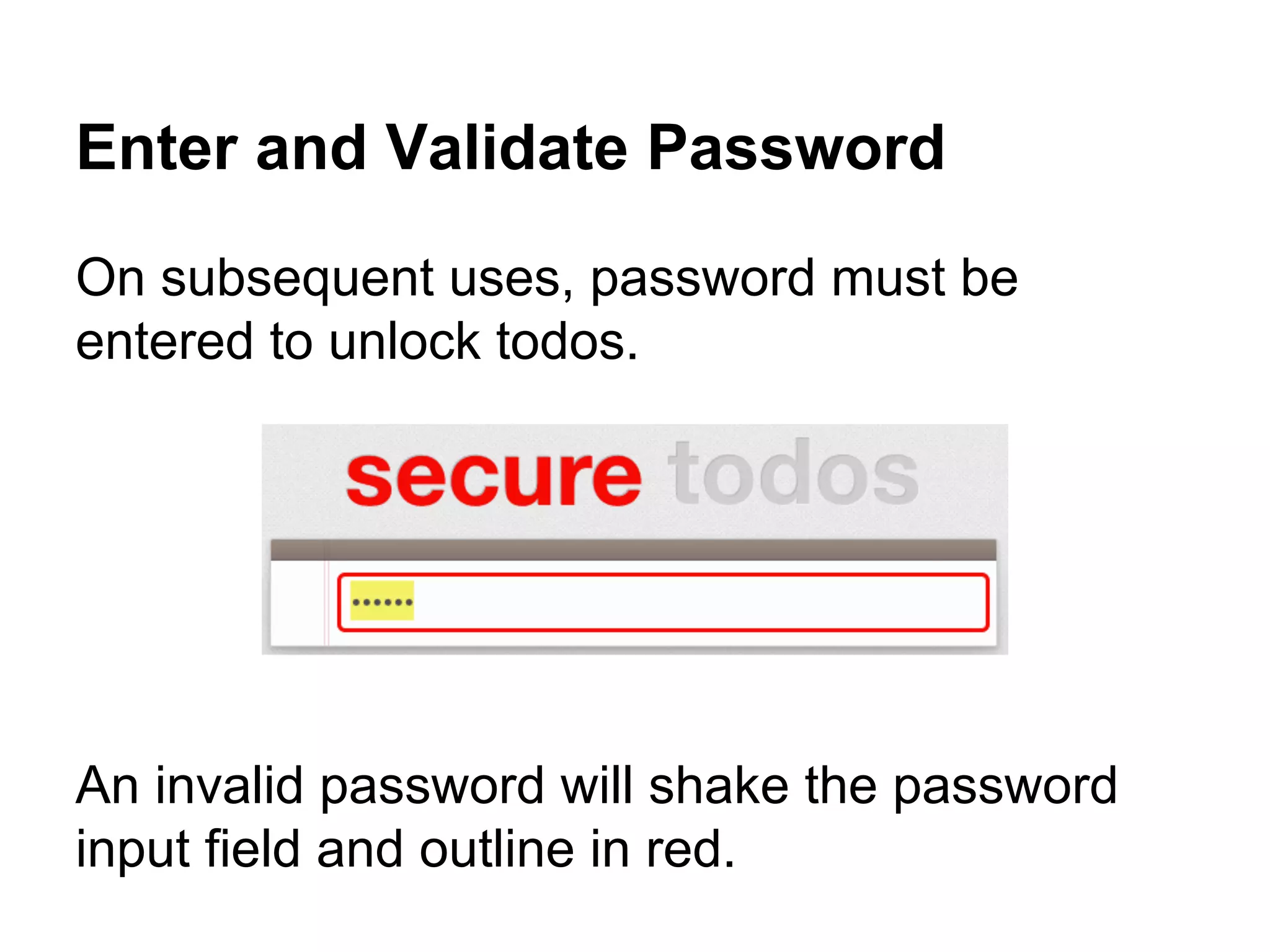
![TypedArray
ECMAScript [ECMA-262] has traditionally been used in
contexts where there is no access to binary data.
Where binary data has needed to be manipulated, it is
often stored as a String and accessed using charCodeAt(),
or stored as an Array with conversion to and from base64
for transmission.
https://www.khronos.org/registry/typedarray/specs/latest/](https://image.slidesharecdn.com/knynawtltoax36qqjt0n-140701141830-phpapp02/75/Java-script-and-web-cryptography-cf-objective-68-2048.jpg)