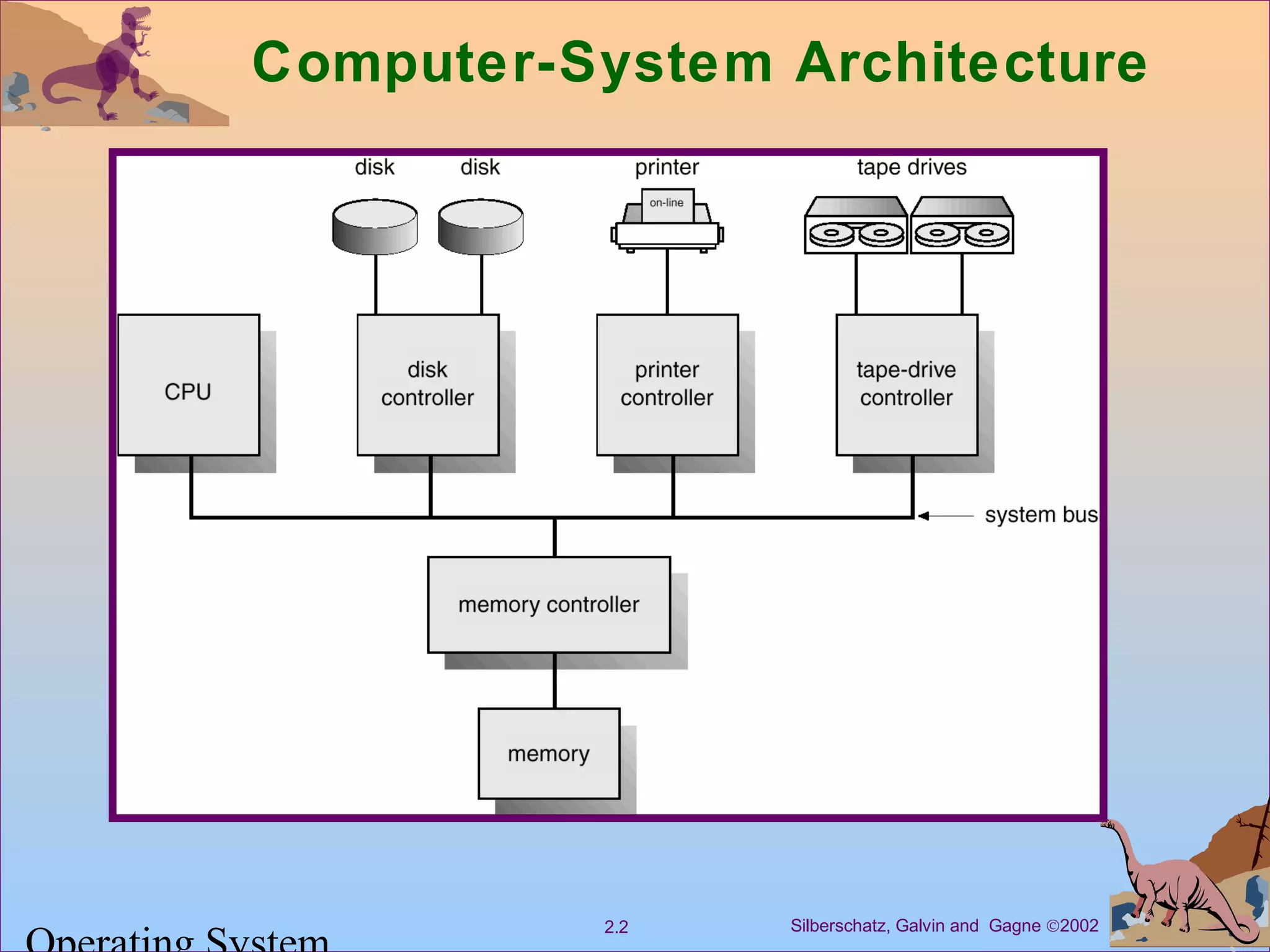
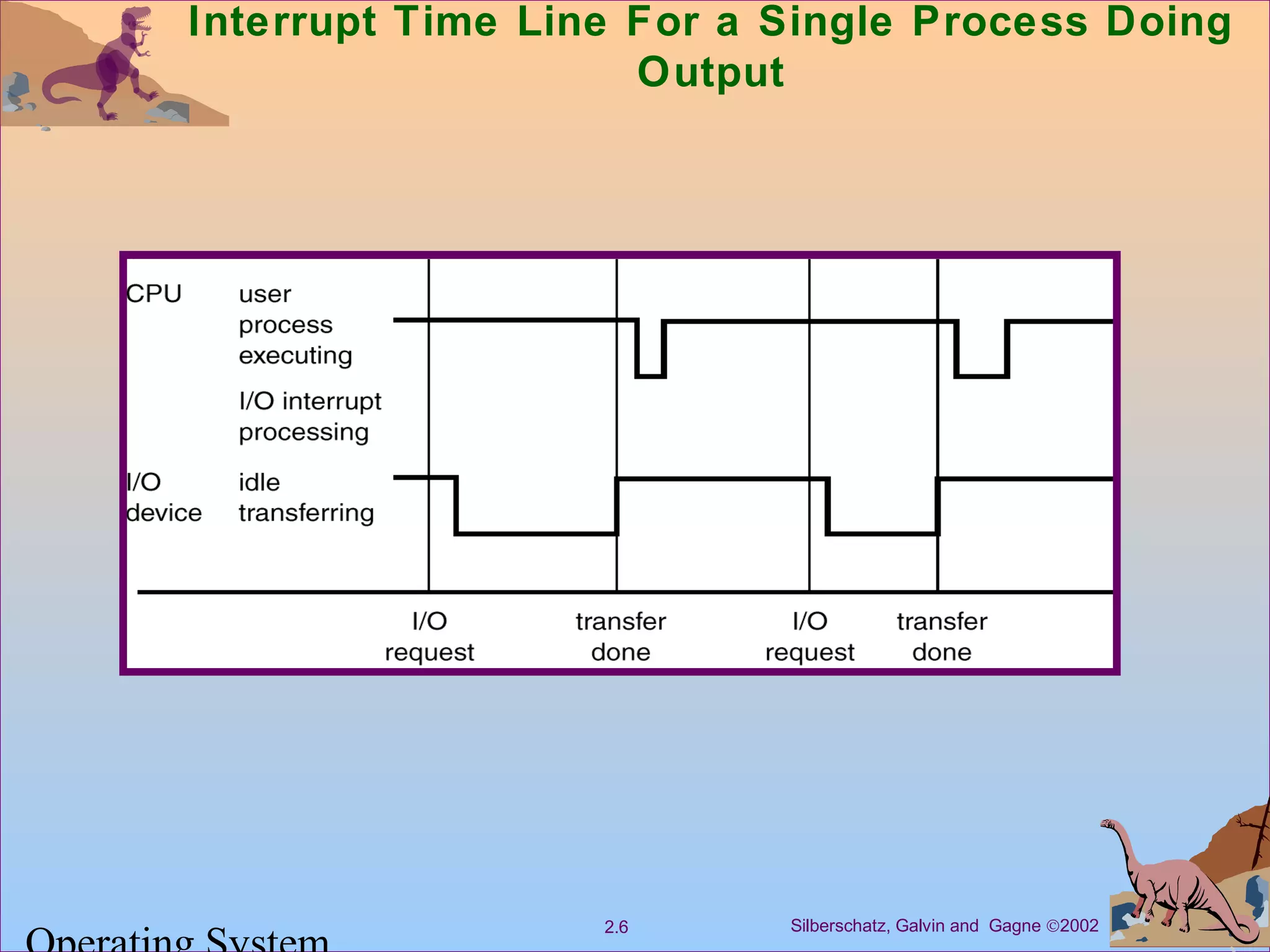
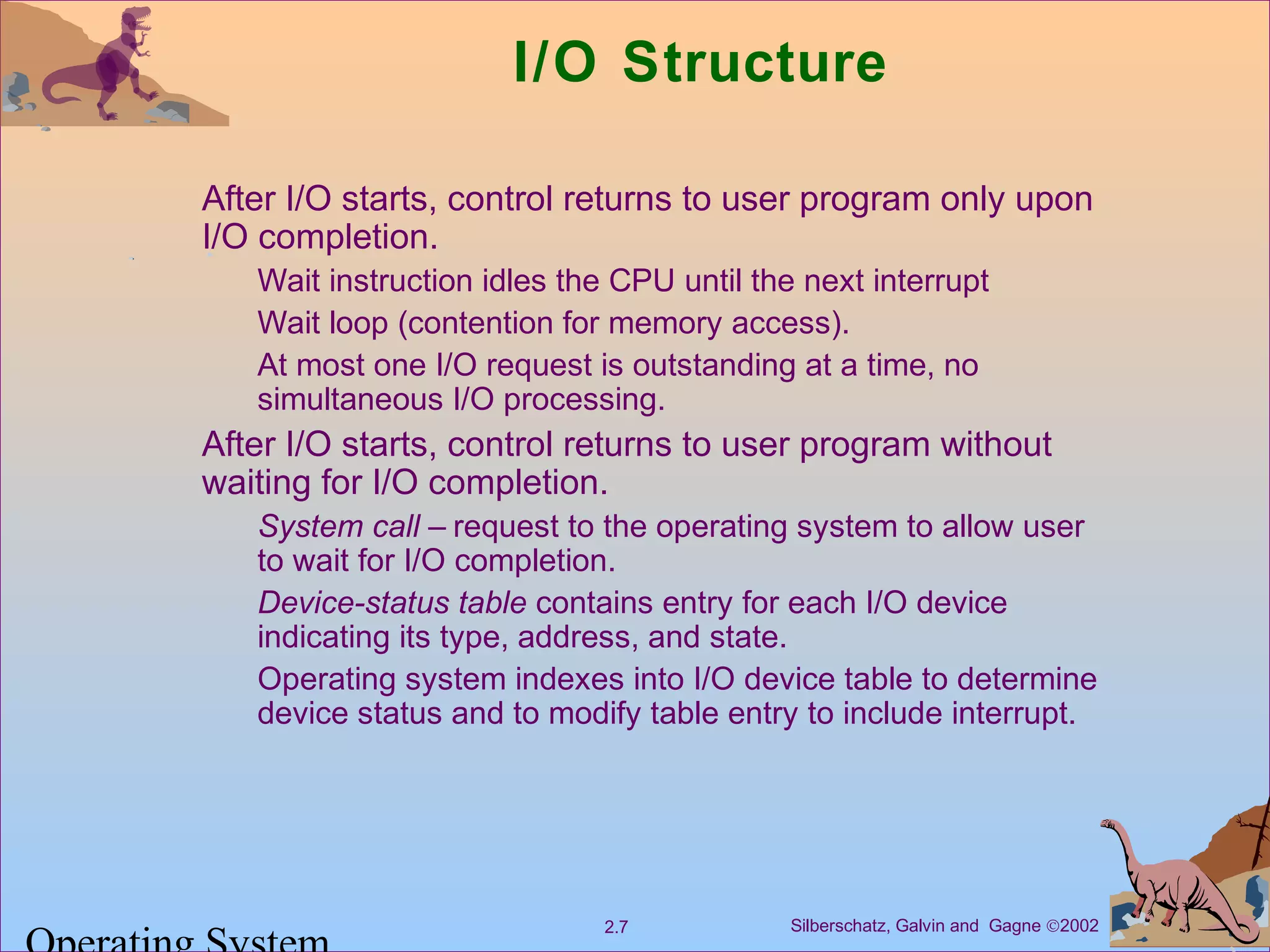
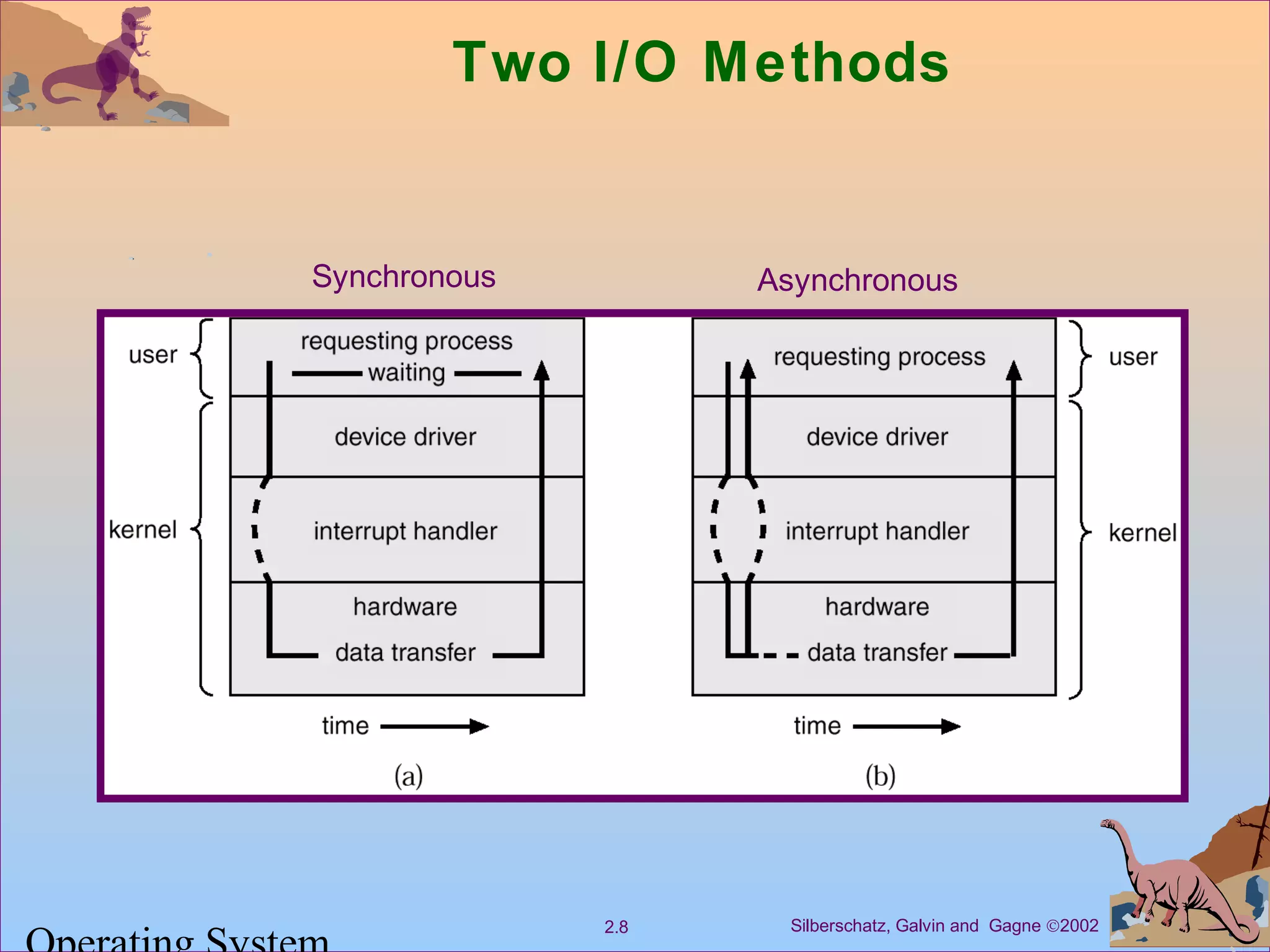
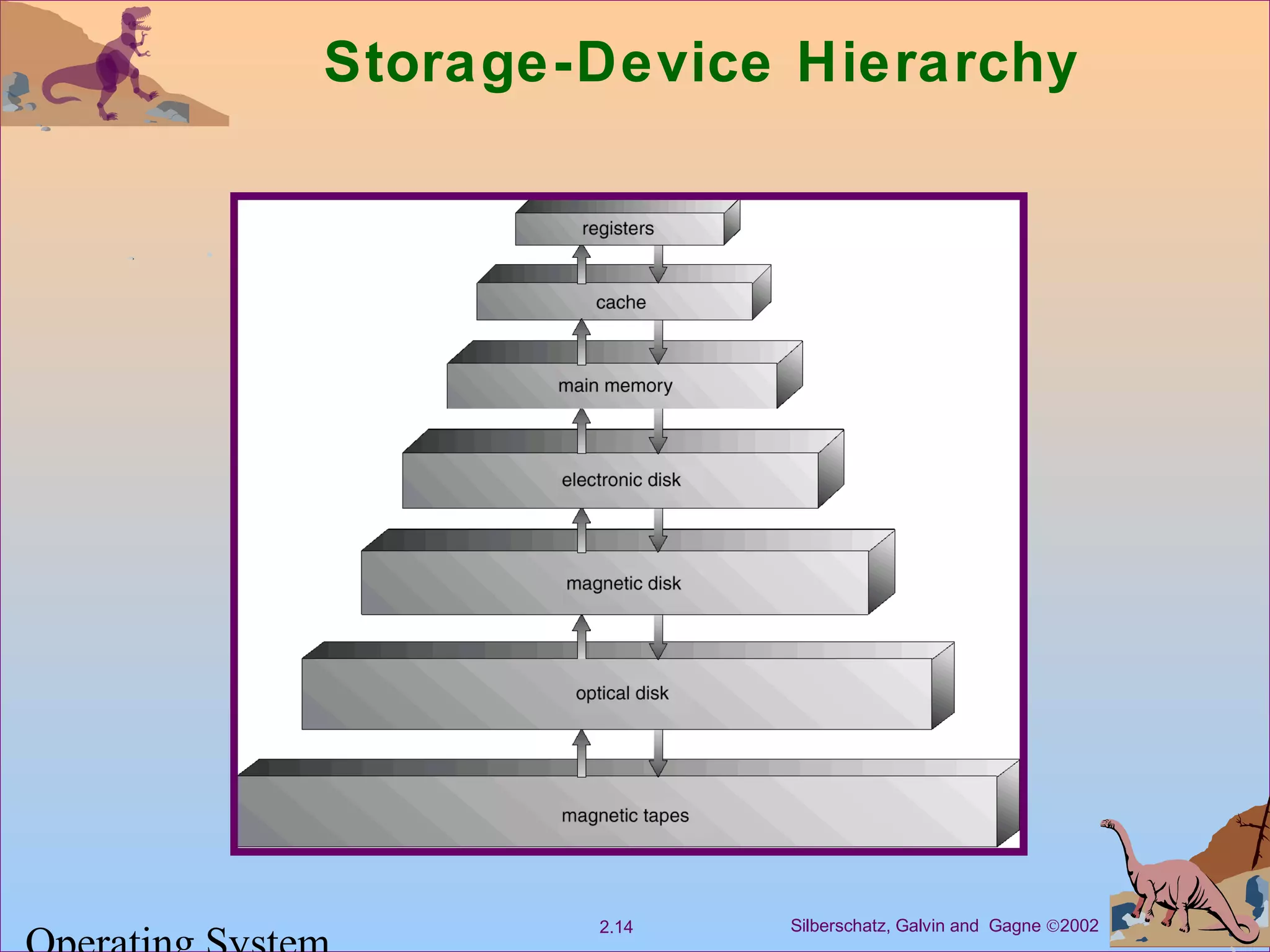
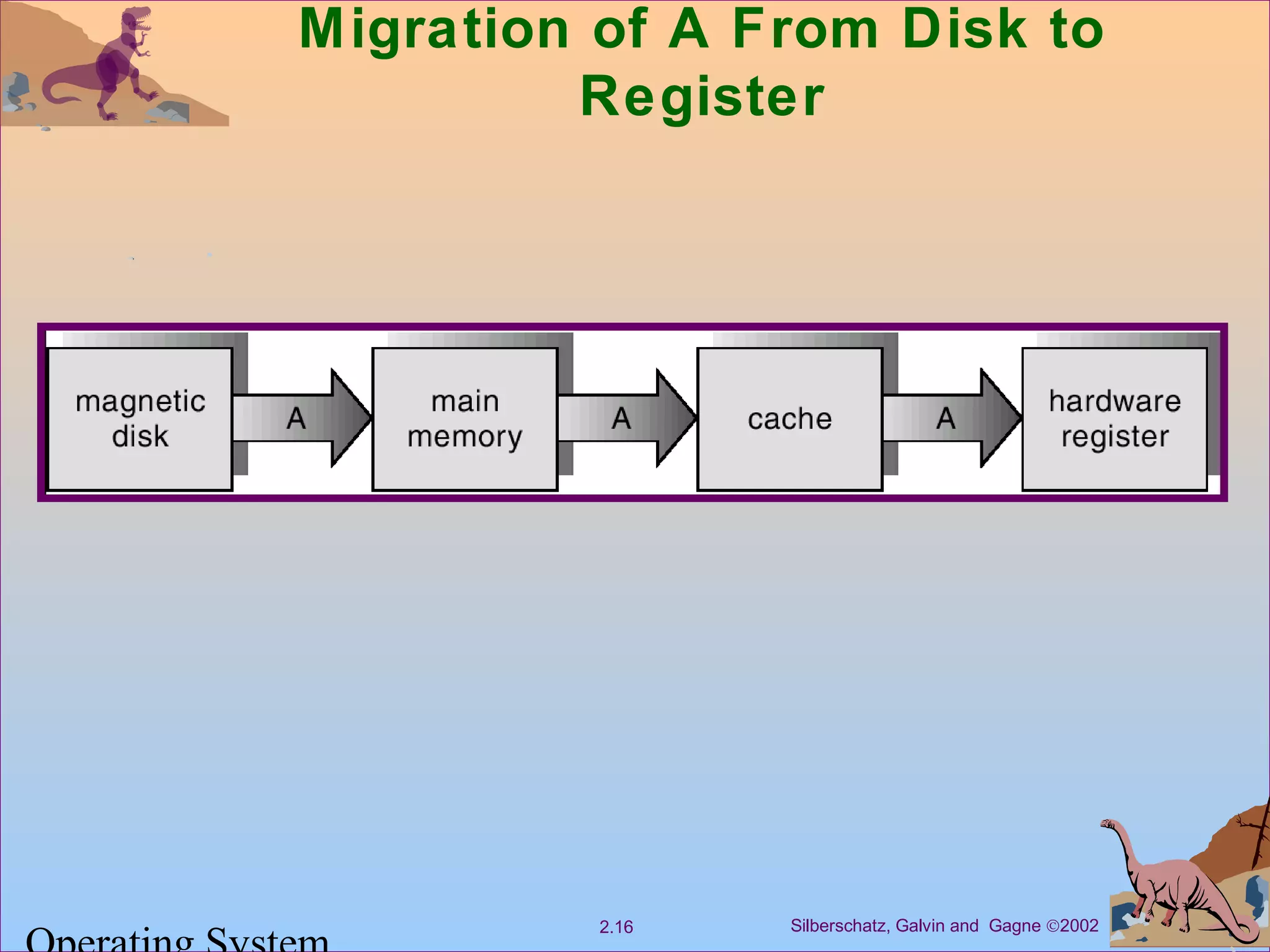
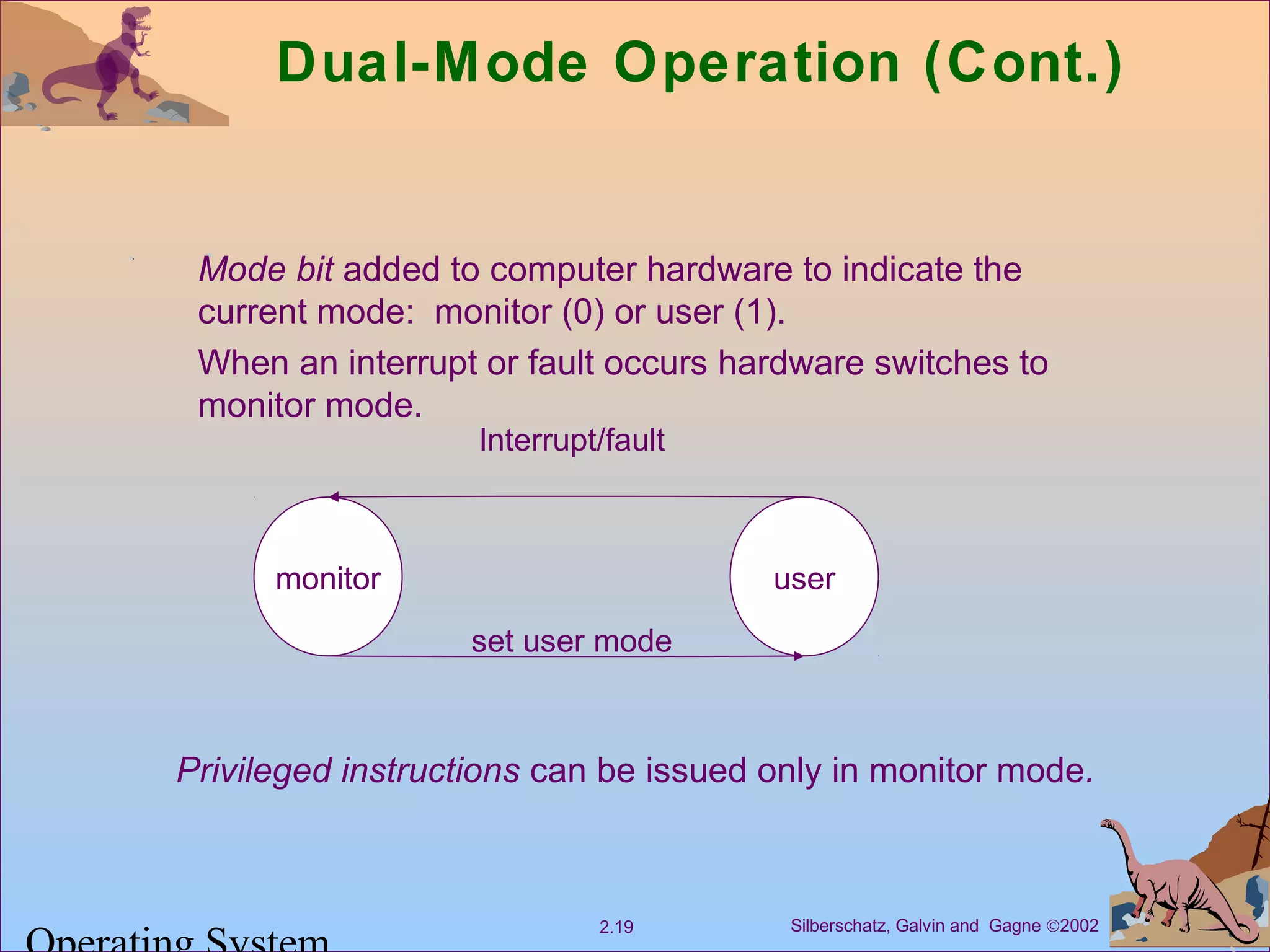
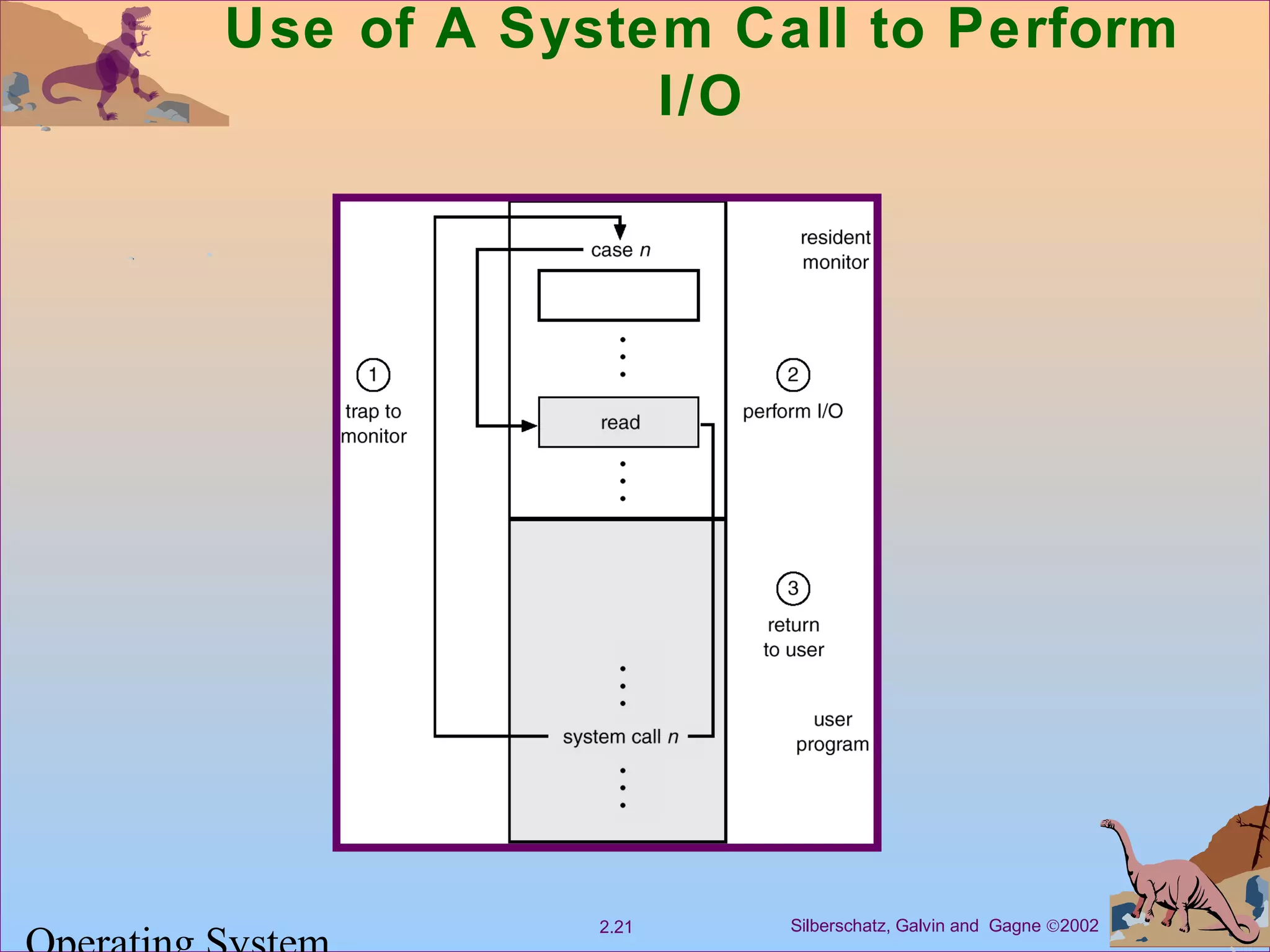
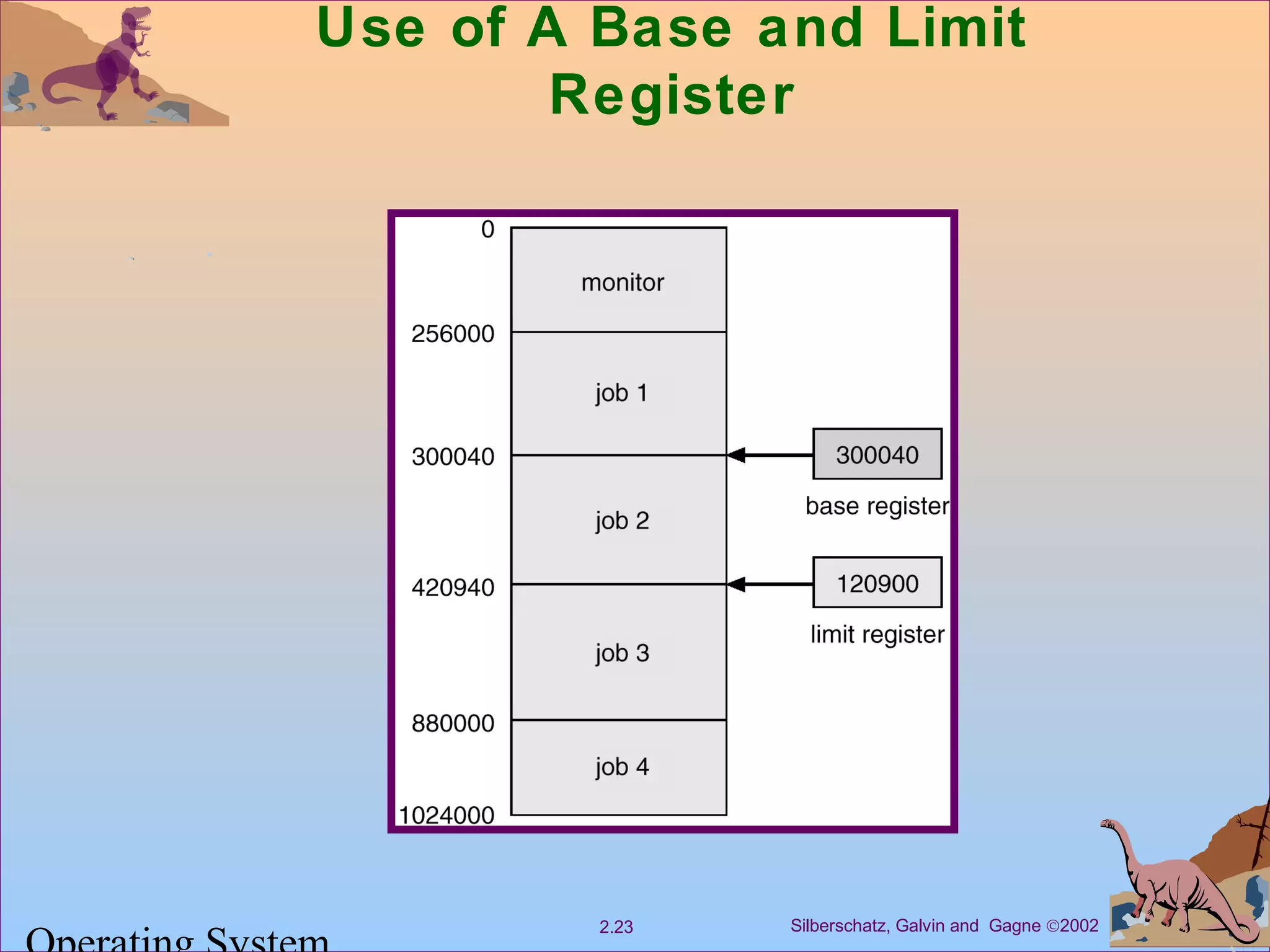
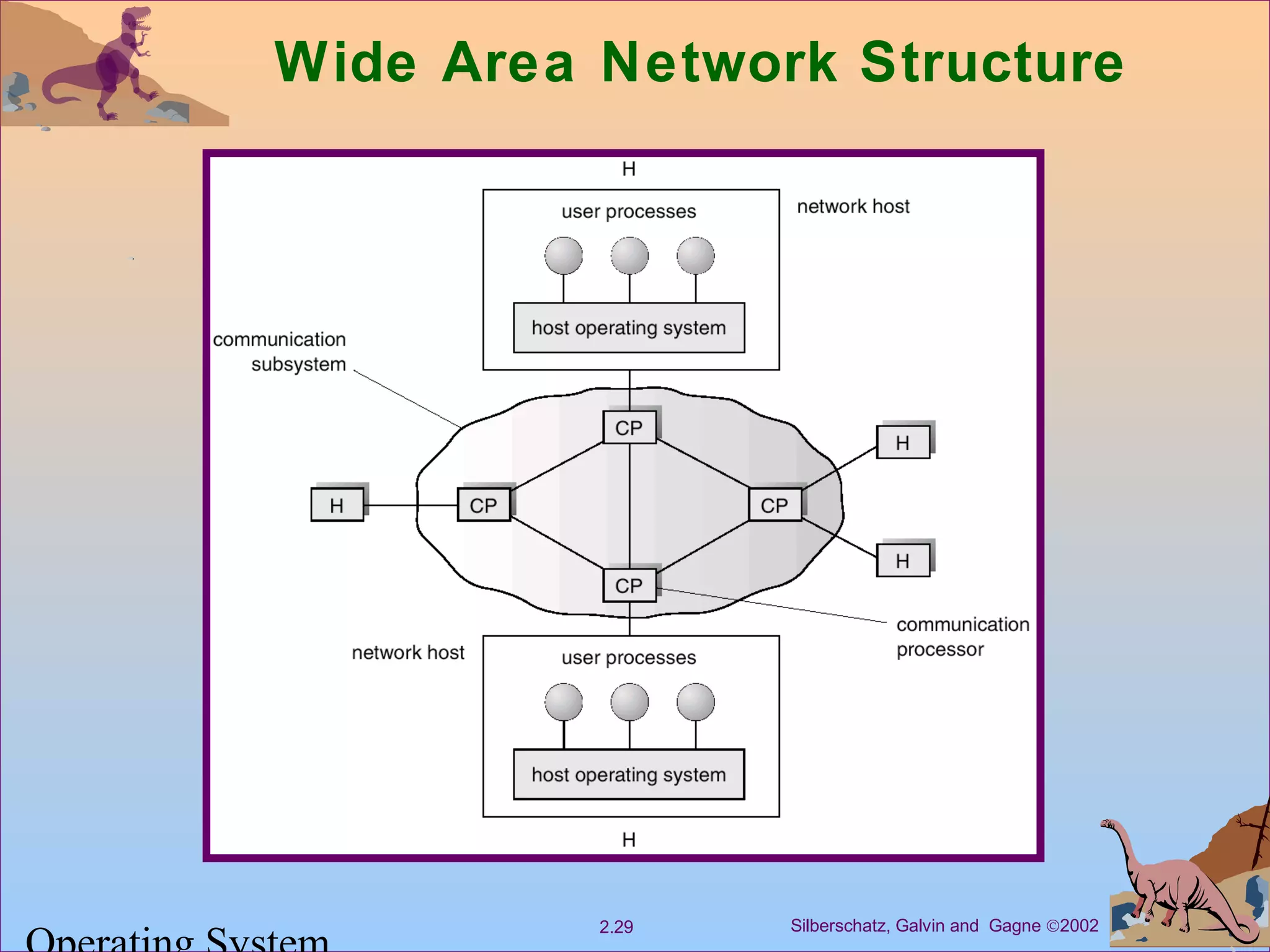
Chapter 2 discusses computer system structures, focusing on computer operation, input/output systems, and hardware protection mechanisms. It explains the roles of device controllers, interrupts, and memory hierarchy, along with methodologies for I/O operations such as synchronous and asynchronous. Additionally, it highlights dual-mode operation for the operating system, ensuring resource protection, and the management of CPU access and memory security.