This document discusses different searching methods like sequential, binary, and hashing. It defines searching as finding an element within a list. Sequential search searches lists sequentially until the element is found or the end is reached, with efficiency of O(n) in worst case. Binary search works on sorted arrays by eliminating half of remaining elements at each step, with efficiency of O(log n). Hashing maps keys to table positions using a hash function, allowing searches, inserts and deletes in O(1) time on average. Good hash functions uniformly distribute keys and generate different hashes for similar keys.

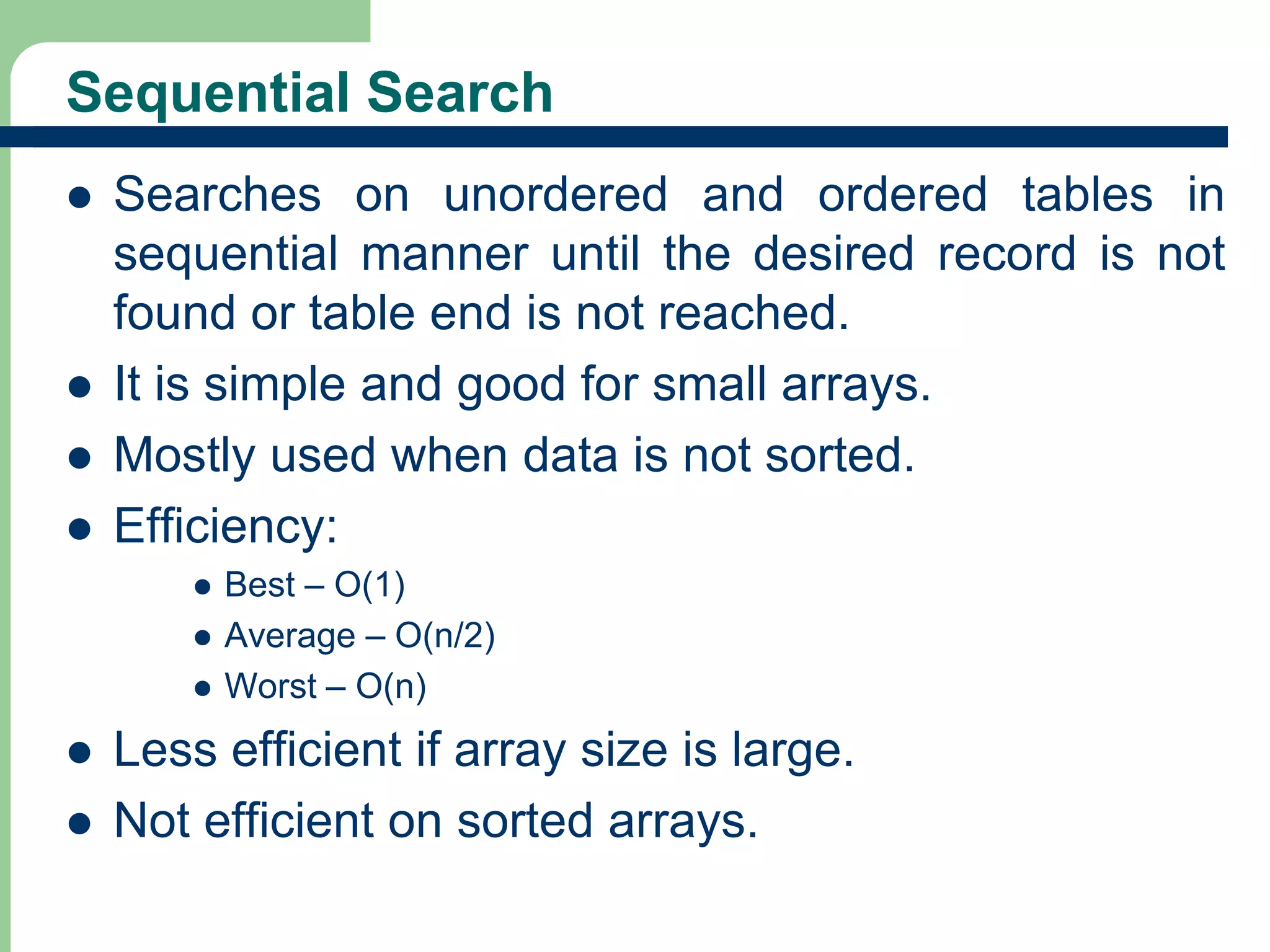

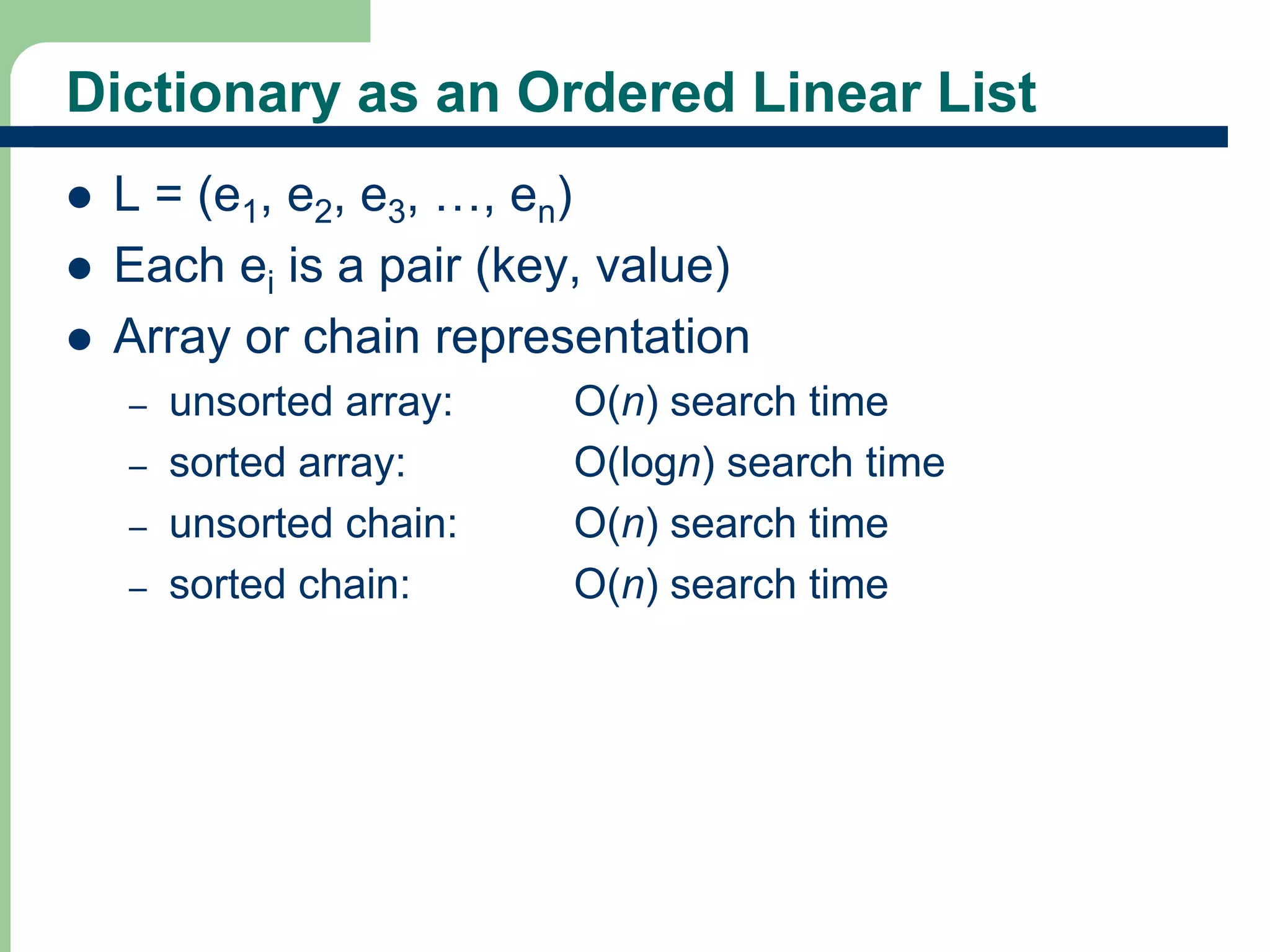
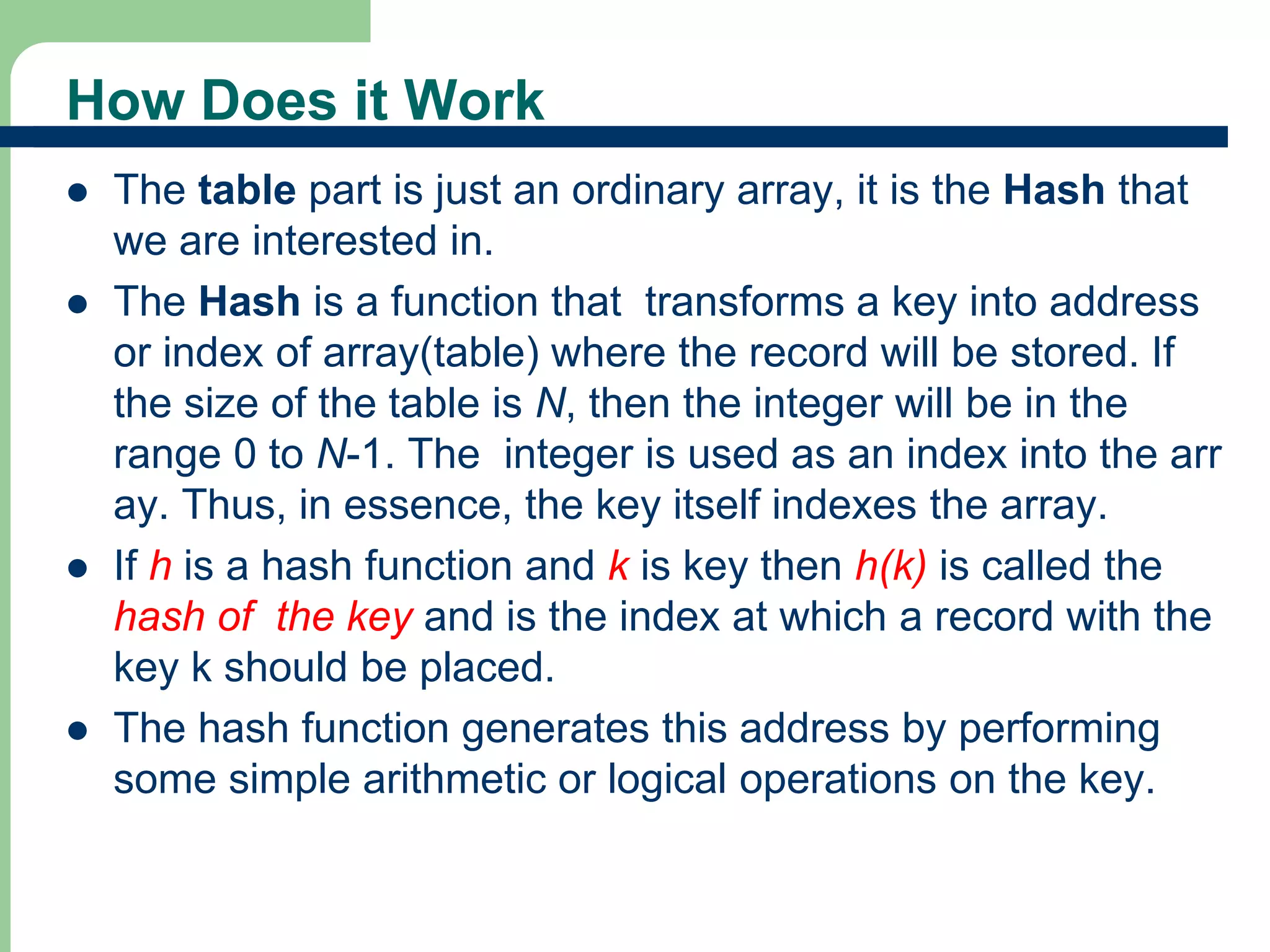
![Ideal Hashing Example
Pairs are: (22,a),(33,c),(3,d),(72,e),(85,f)-
14
-(key, value) pairs
Hash table is ht[0:7], m = 8 (where m is the
number of positions in the hash table)
Hash function h is k % m = k % 8
Where are the pairs stored?
[0] [1] [2] [3] [4] [5] [6] [7]
(72,e) (33,c) (3,d) (85,f) (22,a)
[0] [1] [2] [3] [4] [5] [6] [7]](https://image.slidesharecdn.com/hashingclass-141012005012-conversion-gate01/75/Hashing-Technique-In-Data-Structures-14-2048.jpg)
![Hashing a string key
Table size [0..99]
A..Z ---> 1,2, ...26
0..9 ----> 27,...36
Key: CS1 --->3+19+28 (concat) = 31,928
(31,928)2 = 1,019,397,184 - 10 digits
Extract middle 2 digits (5th and 6th) as table
size is 0..99.
Get 39, so: H(CS1) = 39.
18](https://image.slidesharecdn.com/hashingclass-141012005012-conversion-gate01/75/Hashing-Technique-In-Data-Structures-18-2048.jpg)